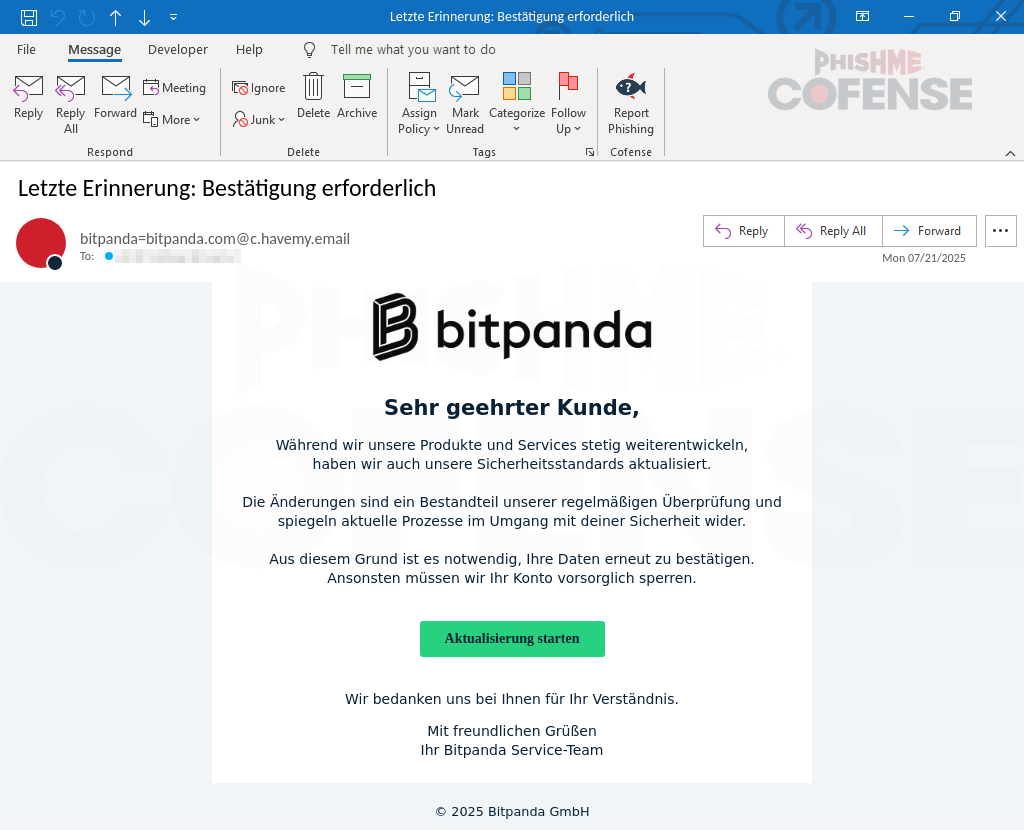
Cofense PDC observed a Bitpanda-themed phishing campaign that used a deceptive, similarly named domain and highly convincing replica pages to harvest login credentials and multiple pieces of PII (name, phone, address, date of birth). The attack used scare tactics and a multi-step “verification” flow before redirecting victims to the real Bitpanda site, and it slipped past a secure email gateway but was remediated by Cofense Managed Phishing Remediation. #Bitpanda #Cofense
Category: Threat Research
State-sponsored APT activity originating in the Middle East focuses on long-term infiltration and intelligence collection using spear-phishing, malicious documents, and abuse of legitimate RMM tools. Defensive emphasis is placed on endpoint behavior-based EDR to detect post-execution activity and persistent misuse of legitimate administration platforms. #MuddyWater #Atera
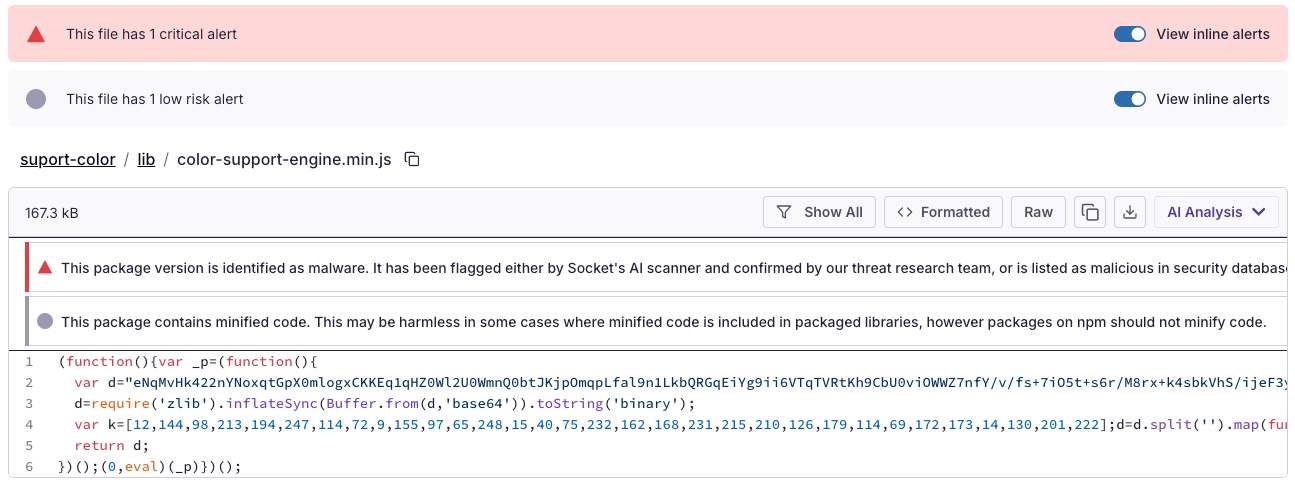
Socket’s Threat Research Team discovered a Shai-Hulud-like supply chain worm campaign tracked as SANDWORM_MODE that spread through at least 19 typosquatting npm packages and a malicious GitHub Action, harvesting developer and CI secrets, exfiltrating via HTTPS/GitHub API/DNS, and persisting via git hooks and MCP server injection targeting AI coding assistants. npm, GitHub, and Cloudflare removed related infrastructure, but defenders must treat the identified packages and injected workflows as active compromise risks and rotate/revoke affected tokens, audit global git templates, and inspect AI assistant configs for rogue MCP servers. #SANDWORM_MODE #suport-color
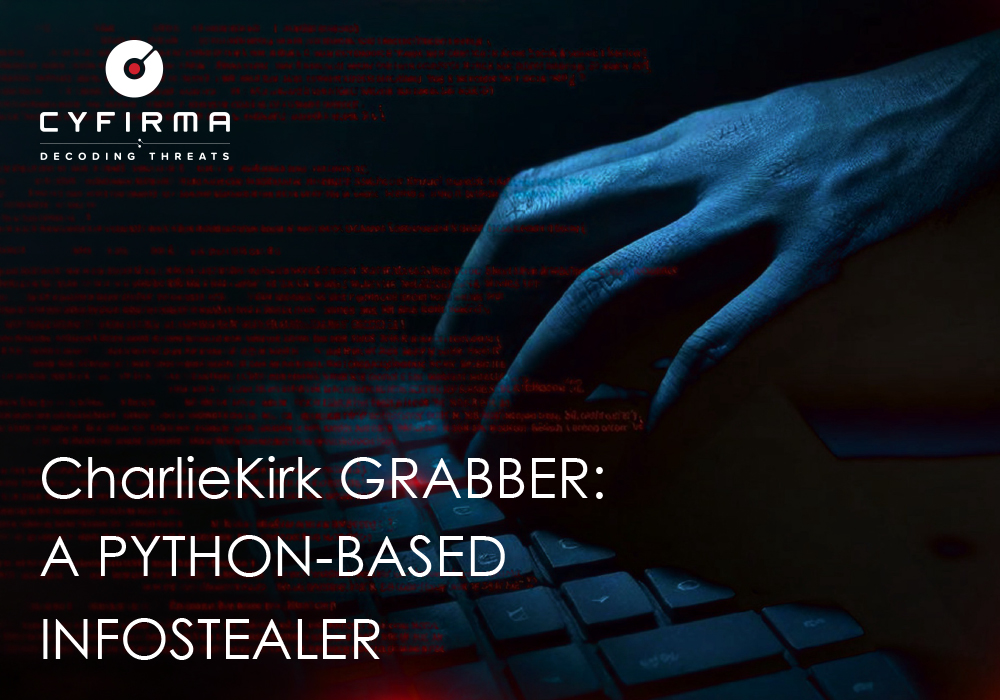
CharlieKirk Grabber is a Python-based Windows infostealer that performs rapid “smash-and-grab” credential harvesting, system reconnaissance, and immediate exfiltration using legitimate Windows utilities and multithreading to minimize runtime. It stages browser credentials, Discord tokens, Wi‑Fi and game session artifacts, compresses them, uploads the archive to GoFile, and sends the download link via Discord or Telegram for attacker retrieval. #CharlieKirk #GoFile

FortiGuard Labs observed a phishing campaign delivering a new XWorm RAT variant via malicious Excel attachments that exploit CVE-2018-0802 to execute an HTA which runs JScript/PowerShell, loads a fileless .NET module, and deploys XWorm into Msbuild.exe via process hollowing. XWorm v7.2 communicates with AES-encrypted C2 servers (example: berlin101.com:6000), supports a modular plugin architecture and extensive control commands enabling full remote control, data exfiltration, DDoS, and ransomware capabilities. #XWorm #MicrosoftWindows

Elastic Security Labs discovered a multi-stage ClickFix campaign that compromises legitimate websites to deliver a five-stage chain culminating in a custom native RAT called MIMICRAT. The attack uses an obfuscated PowerShell downloader with ETW and AMSI bypass, a Lua-based in-memory loader and Meterpreter-like shellcode, and a C++ implant with token impersonation and SOCKS5 tunneling. #MIMICRAT #ClickFix
Attackers ran paid Facebook ads that mimicked official Microsoft Windows 11 update promotions and redirected victims to near-perfect counterfeit download pages that delivered a malicious 75 MB installer (ms-update32.exe) hosted on GitHub which installs an Electron-based LunarApplication to harvest saved passwords, browser sessions, and cryptocurrency wallet data. The campaign used geofencing…
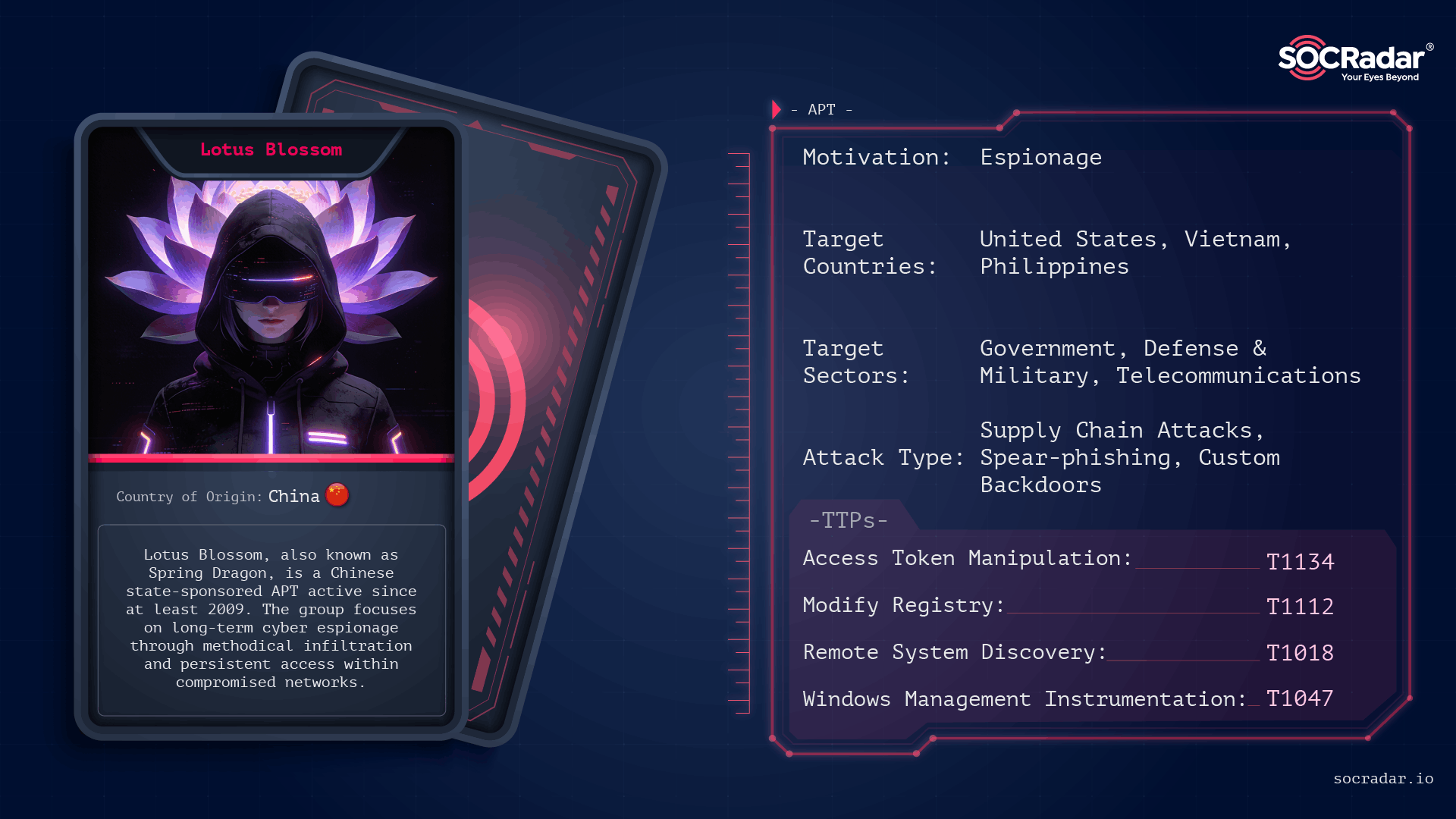
Lotus Blossom is a long-running, China-attributed APT that evolved from spear-phishing and watering-hole campaigns into sophisticated supply-chain compromises and targeted espionage using custom implants like Elise, Sagerunex, Hannotog, and Chrysalis. The group’s Notepad++ update-channel compromise and prior attacks against diplomatic, military, and maritime infrastructure demonstrate a “low-and-slow” intelligence collection approach emphasizing DLL sideloading, living-off-the-land techniques, and clandestine persistence. #LotusBlossom #Chrysalis
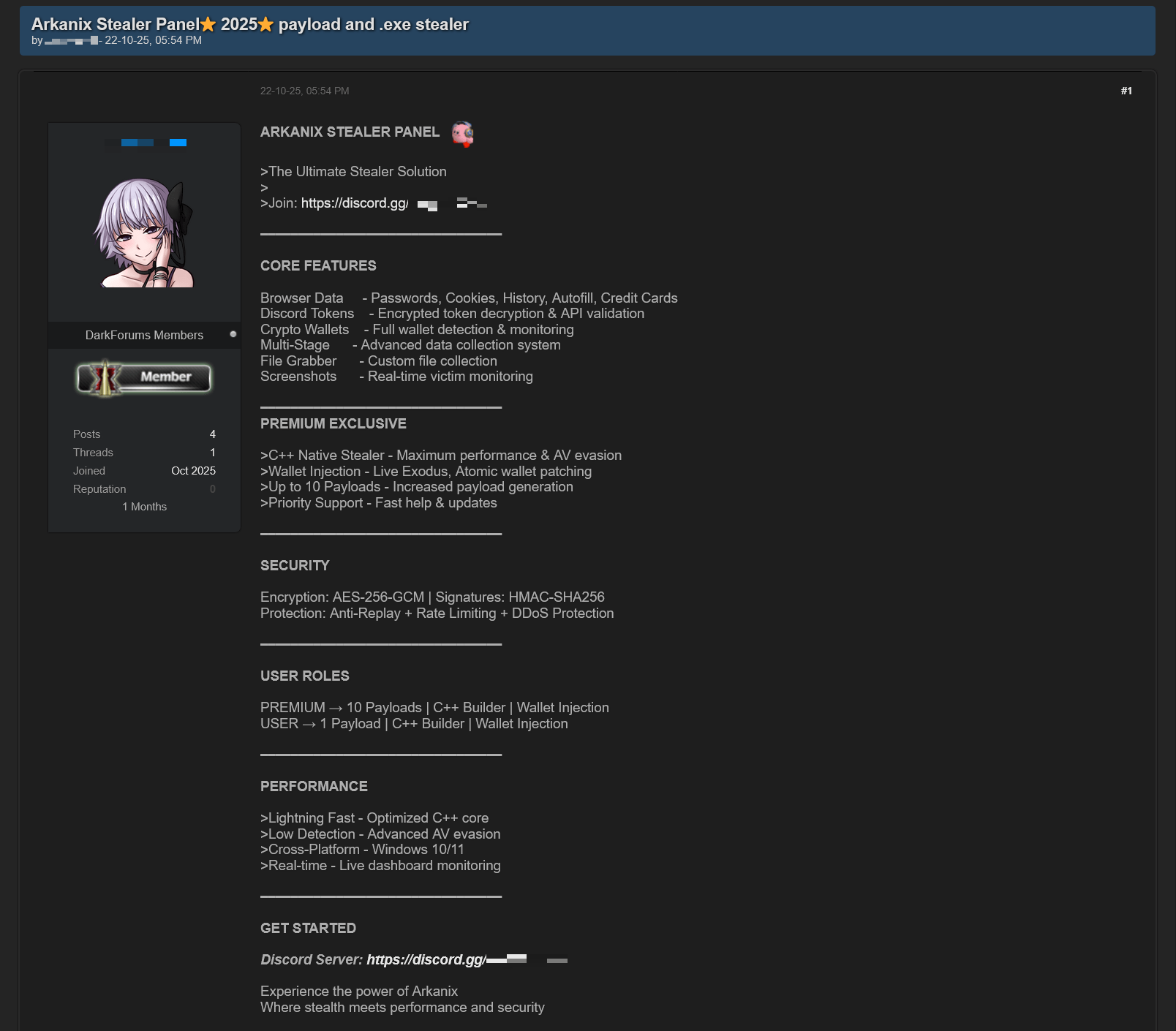
In October 2025 researchers discovered forum posts advertising a previously unknown MaaS called “Arkanix Stealer” offering both native C++ and Python implants, a configurable control panel, and payload generation. The malware harvested browser credentials, cryptocurrency wallets (using an embedded ChromElevator injector), system and application data, communicated with C2 endpoints on arkanix[.]pw, and the affiliate program and panel were subsequently taken down. #ArkanixStealer #ChromElevator
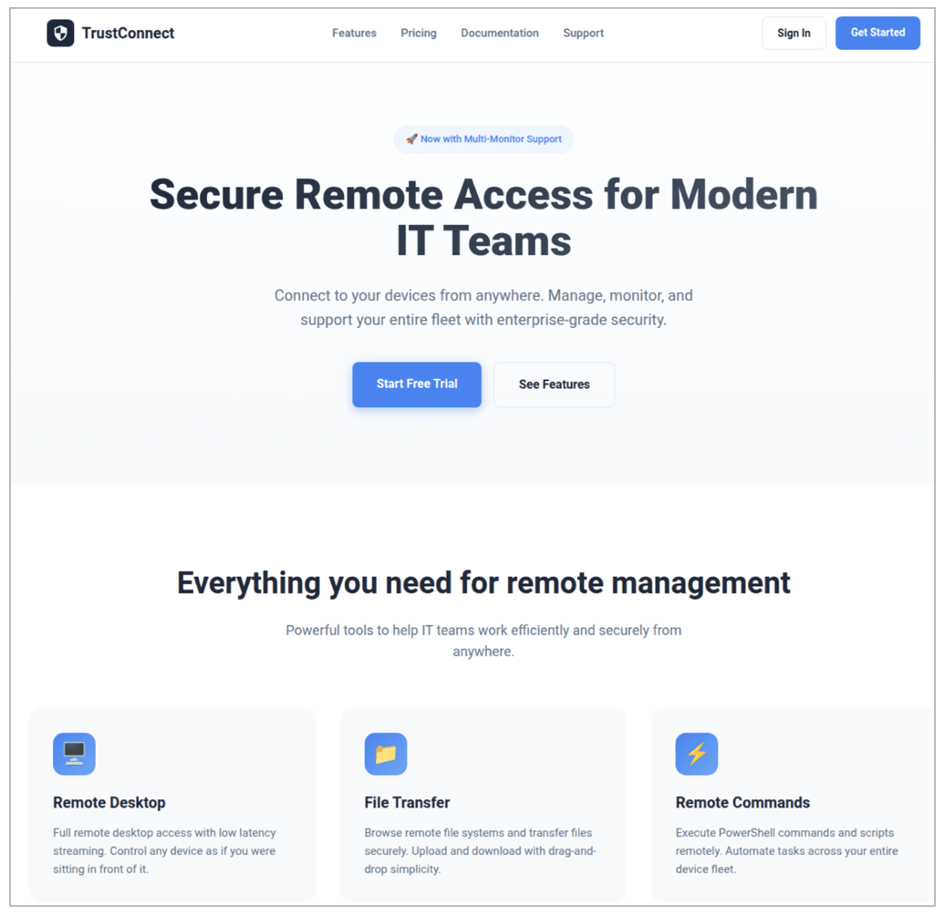
Proofpoint identified a new malware-as-a-service (MaaS) called TrustConnect that masqueraded as a legitimate remote monitoring and management (RMM) tool, used an EV code signing certificate to sign branded installers, and provided a web-based C2/dashboard with automated payload generation and a $300/month subscription model. Proofpoint disrupted the TrustConnect infrastructure (C2 domain trustconnectsoftware[.]com…
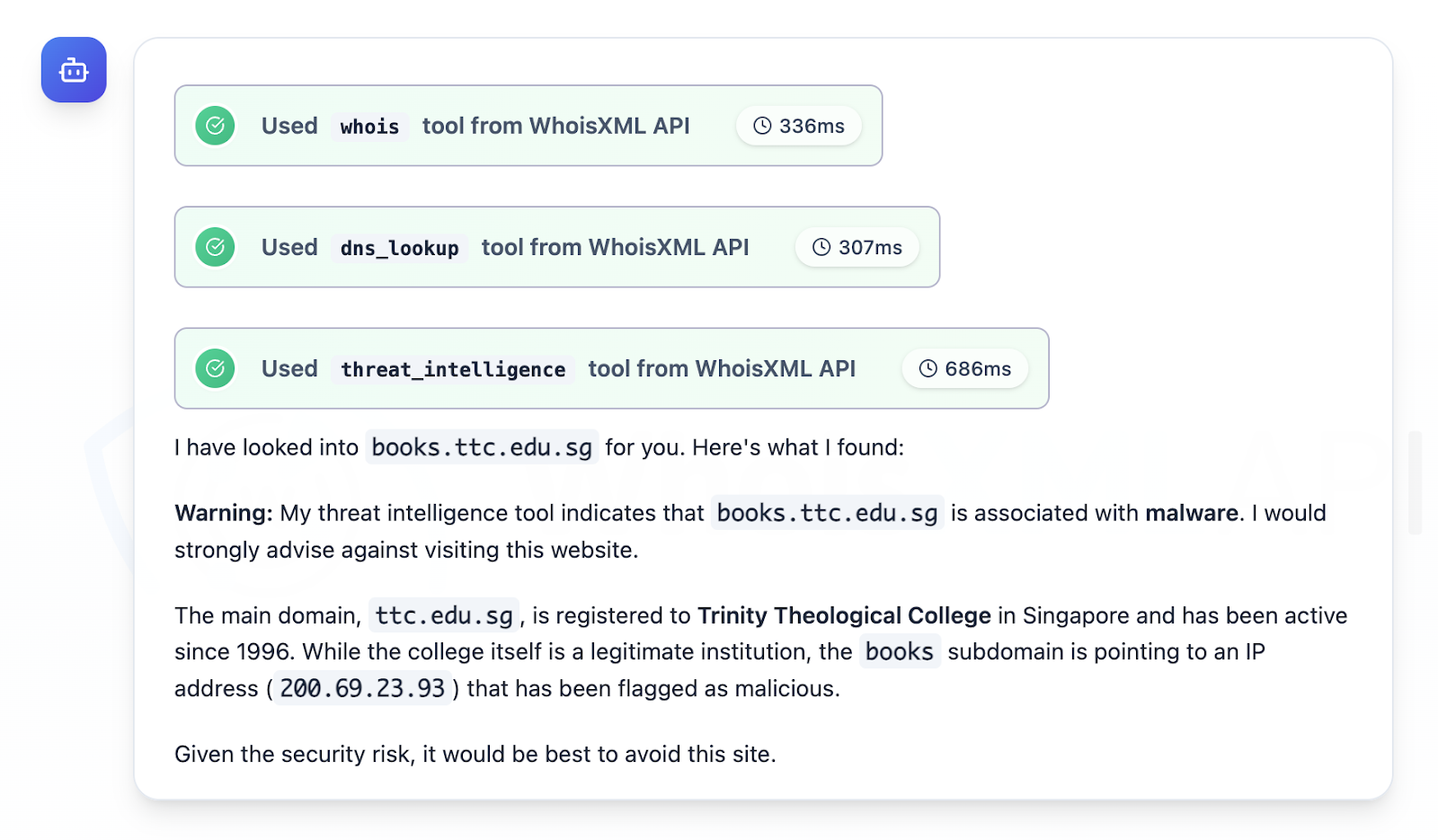
CloudSEK and follow-up research focused on QakBot as a top access trojan/loader that is commonly distributed via phishing, harvests credentials, maintains C2 access, delivers payloads, and moves laterally to enable targeted attacks and ransomware against email-reliant enterprises. The investigation analyzed Trellix IoCs (extracted 929 domains, filtered to 492, studied 125), 19 subdomains, multiple client and infrastructure IPs, and thousands of email-connected domains, identifying specific malicious artifacts (e.g., books[.]ttc[.]edu[.]sg -> 200[.]69[.]23[.]93) and providing a downloadable dataset for further hunting. #QakBot #Trellix

AhnLab’s January 2026 report summarizes automated collection and analysis of Infostealer samples distributed via SEO-poisoned crack/keygen pages, forum and corporate site posts, and highlights differences in Windows and macOS distribution and obfuscation techniques. Notable findings include ACRStealer’s shift to ECDH + ChaCha20-Poly1305 for C2 encryption and rapid macOS sample churn with…

Security researchers uncovered a mass-distributed macOS loader delivered via cracked music plugin DMGs that deploys multistage payloads including Odyssey and MacSyncStealer and an additional Mach-O loader. The campaign leverages social engineering (including ClickFix-style browser prompts), obfuscated shell scripts, and PPI/affiliate tracking to retrieve and execute secondary payloads from domains such as mac[.]fleebottom-33[.]xyz and robincompany[.]xyz. #MacSyncStealer #Odyssey

Researchers demonstrate a new False File Immutability (FFI) exploit, Redux, that leverages the Windows Cloud Files driver (cldflt.sys) and FltWriteFileEx to modify in-use executables and achieve kernel-level code execution without requiring SMB/network redirectors. The technique bypasses prior mitigations (and remains effective on some patched Windows versions), and proof-of-concept exploits and mitigations (including an Elastic Defend rule and a filesystem minifilter) were released. #FalseFileImmutability #PPLFault

Kubernetes has announced that Ingress NGINX will be retired after March 2026, meaning no further releases, bug fixes, or security patches will be provided and organizations must migrate away. The post highlights past critical flaws including the CVE-2025-1974 “IngressNightmare” RCE and urges immediate checks and migration planning to Gateway API–conformant controllers. #IngressNGINX #Kubernetes
.png?language=en)