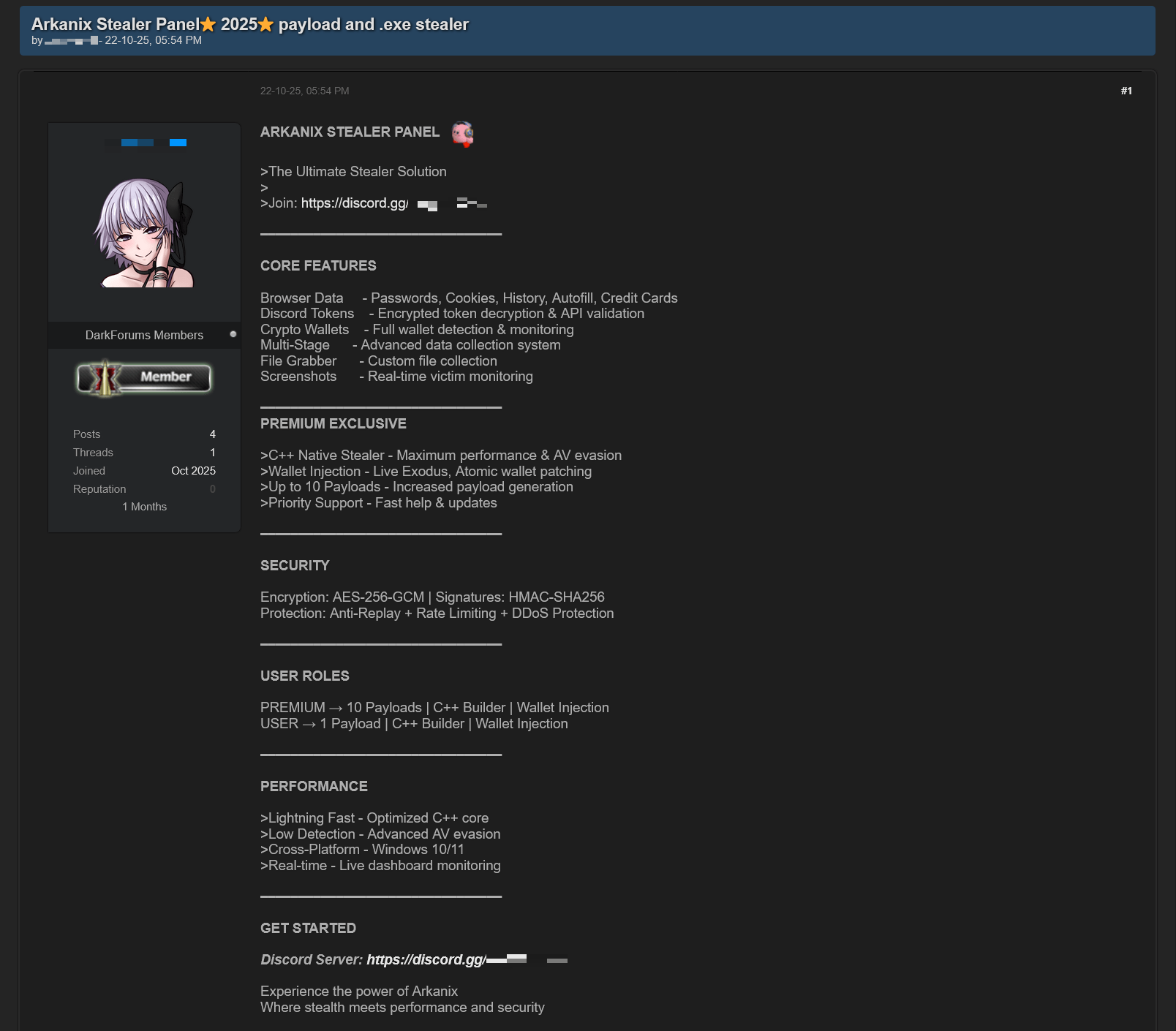
In October 2025 researchers discovered forum posts advertising a previously unknown MaaS called “Arkanix Stealer” offering both native C++ and Python implants, a configurable control panel, and payload generation. The malware harvested browser credentials, cryptocurrency wallets (using an embedded ChromElevator injector), system and application data, communicated with C2 endpoints on arkanix[.]pw, and the affiliate program and panel were subsequently taken down. #ArkanixStealer #ChromElevator
Keypoints
- Arkanix Stealer was advertised on dark web forums and operated under a MaaS model with a control panel and referral program.
- Two main implementations were observed: a native C++ build (ArkanixStealer.exe) and a Python-based stealer (stealer.py) with dynamic, panel-controlled features.
- The native C++ sample embeds the public ChromElevator browser post-exploitation tool and uses process injection via direct Nt syscalls to exfiltrate browser data.
- Python loaders often install dependencies via pip, register victims to the panel (hxxps://arkanix[.]pw/api/session/create), download stealer payloads, and execute them; some loaders were bundled with PyInstaller or Nuitka.
- Data collection capabilities include system info, saved browser credentials (including OAuth2), cookies, Telegram tdata, Discord credentials and self-spreading, VPN credentials, gaming platform credentials, file harvesting, and screenshots (native build).
- Additional modules (chrome grabber, wallet patcher, extra collector, HVNC) were delivered from C2, encrypted with AES-GCM and PBKDF2, decrypted and stored temporarily before execution.
- The campaign infrastructure included arkanix[.]pw (real IP observed) and arkanix[.]ru (Cloudflare), but the panel and Discord server were taken down by December 2025.
MITRE Techniques
- [T1566 ] Phishing – The initial infection vector is believed to be phishing based on loader filenames. (‘the initial infection vector involved phishing’)
- [T1059.006 ] Command and Scripting Interpreter: Python – Python loaders and the stealer execute Python scripts, install packages via pip, and use subprocess/threading. (‘the loader first installs the required packages — namely, requests, pycryptodome, and psutil — via the pip package manager, utilizing the subprocess module.’)
- [T1105 ] Ingress Tool Transfer – The loader downloads payloads from the attacker-controlled domain and executes them (stealer.py and dropper). (‘makes a GET request to hxxps://arkanix[.]pw/stealer.py and executes the downloaded payload.’)
- [T1055 ] Process Injection – The embedded ChromElevator injector spawns a suspended browser process and injects code using Nt syscalls. (‘injects the decrypted code into it via Nt syscalls.’)
- [T1555.001 ] Credentials from Web Browsers – The stealer extracts saved passwords, cookies, autofill and OAuth2 tokens from Chromium and other browsers and decrypts them via DPAPI or AES. (‘the stealer supports the extraction of … Saved passwords … In case of Chromium-based browsers, 0Auth2 data is also extracted’)
- [T1113 ] Screen Capture – The native implementation captures screenshots for each monitor using a WinAPI call. (‘capCreateCaptureWindowA WinAPI’)
- [T1071.001 ] Application Layer Protocol: Web Protocols – C2 and panel communication use HTTPS endpoints on arkanix[.]pw for session registration, feature retrieval, and payload download. (‘makes a POST request to hxxps://arkanix[.]pw/api/session/create’)
- [T1497 ] Virtualization/Sandbox Evasion – The native sample performs checks to detect sandbox or debugger environments and patches AmsiScanBuffer and EtwEventWrite to avoid detection. (‘implements a series of analysis countermeasures to verify that the application is not being executed within a sandboxed environment or run under a debugger. … patches AmsiScanBuffer and EtwEventWrite’)
- [T1070.004 ] File Deletion – After operations complete, the stealer deletes itself and its artifact folder from disk. (‘the stealer removes itself from the drive, along with the artifacts folder (Arkanix_lol in this case).’)
Indicators of Compromise
- [Domain ] C2 and panel hosting – arkanix[.]pw, arkanix[.]ru
- [IP address ] Infrastructure hosts – 195.246.231[.]60 (arkanix[.]pw real IP), 172.67.186[.]193 (Cloudflare IP observed)
- [File hash ] Sample MD5s observed – 208fa7e01f72a50334f3d7607f6b82bf (Python loader), af8fd03c1ec81811acf16d4182f3b5e1 (Python stealer), and many other hashes reported in the dataset
- [File name ] Known filenames linked to loaders/implants – discord_nitro_code_validator_right_aligned.py, ArkanixStealer.exe
- [URLs / Endpoints ] Observed C2/payload endpoints – hxxps://arkanix[.]pw/api/session/create, hxxps://arkanix[.]pw/stealer.py, hxxps://arkanix[.]pw/upload_dropper.py (and other /api/* endpoints)
- [HTTP Header ] User-Agent used by native sample – ArkanixStealer/1.0