Cofense PDC observed a Bitpanda-themed phishing campaign that used a deceptive, similarly named domain and highly convincing replica pages to harvest login credentials and multiple pieces of PII (name, phone, address, date of birth). The attack used scare tactics and a multi-step “verification” flow before redirecting victims to the real Bitpanda site, and it slipped past a secure email gateway but was remediated by Cofense Managed Phishing Remediation. #Bitpanda #Cofense
Keypoints
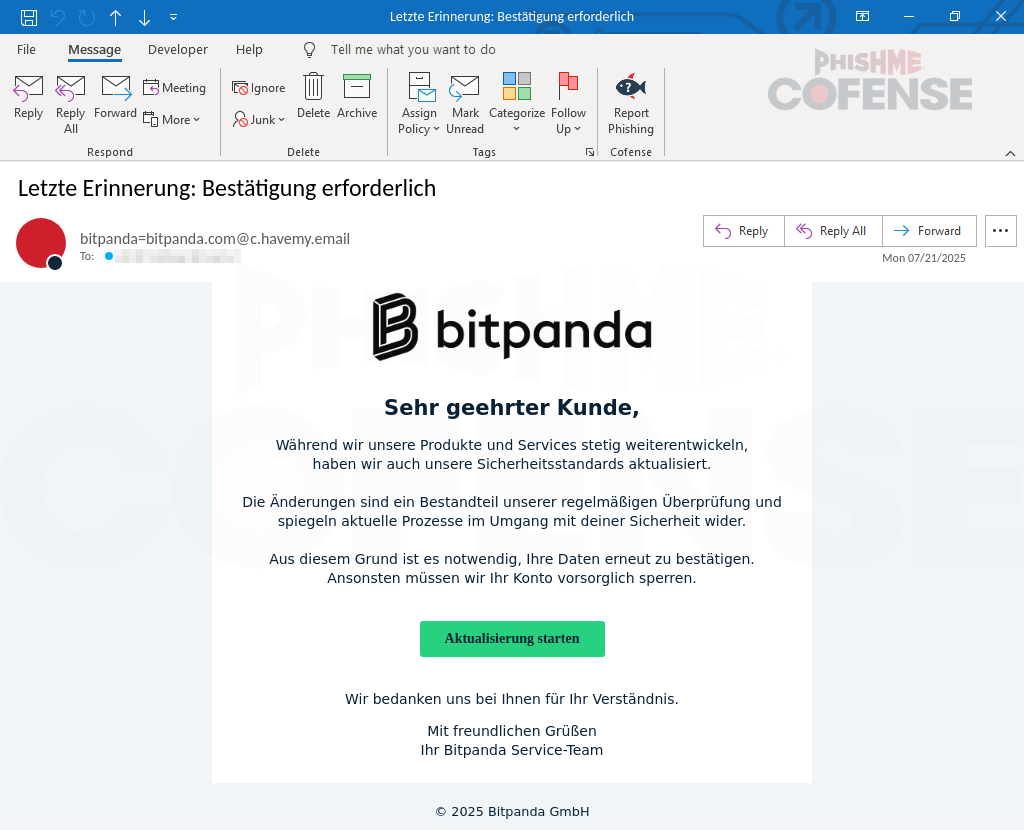
- Attackers impersonated the cryptocurrency brokerage Bitpanda with a nearly identical phishing email and landing pages to trick users into providing credentials and PII.
- The phishing email used a scare tactic threatening to “block your account” and included a “Start Update” button that pointed to a non-Bitpanda URL.
- The malicious domain account-bitpanda[.]com was registered shortly before the campaign and closely mimicked the legitimate account.bitpanda[.]com domain to increase believability.
- The multi-step phishing site harvested username/passwords and sequentially requested first/last name, phone number, address, and date of birth under the guise of multi-factor verification.
- The fake pages included a QR code linking to the official Bitpanda app to further legitimize the site and lead victims to trust the process.
- The campaign bypassed a secure email gateway (SEG) but was detected and remediated by Cofense Managed Phishing Remediation and PDC analysts.
MITRE Techniques
- [T1566.002 ] Spearphishing Link – The actor delivered a phishing email containing a link to a credential- and PII-harvesting website. (‘The button immediately below the “blocking statement” translates to “Start Update,” prompting the user to click’)
- [T1036 ] Masquerading – The threat actor registered and used a deceptive domain and near-identical web pages to impersonate Bitpanda and deceive users. (‘The domain “account-bitpanda[.]com” is fake and was only created a few days prior… The real Bitpanda domain, “account.bitpanda[.]com” is the real one.’)
- [T1204.002 ] User Execution: Malicious Link – Social-engineering and a scare message coerced users into following the link and entering sensitive information. (‘Otherwise, we will have to block your account as a precautionary measure.’)
Indicators of Compromise
- [Domain ] phishing landing and legitimate domain – account-bitpanda[.]com (malicious spoof domain used for credential/PII harvesting), account.bitpanda[.]com (legitimate Bitpanda domain)
- [Email address ] suspicious sender – email “from” address described as not originating from the company domain (no specific sender address provided in the article)
Read more: https://cofense.com/blog/pii-pillage-how-attackers-use-bitpanda-to-plunder-credentials
.png?language=en)