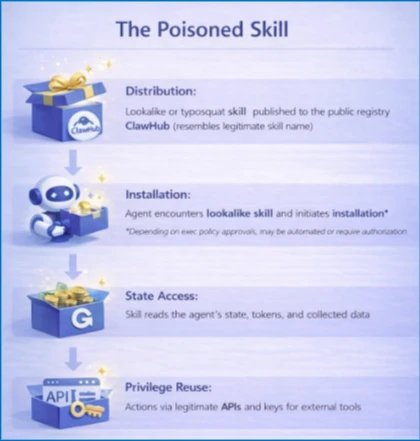
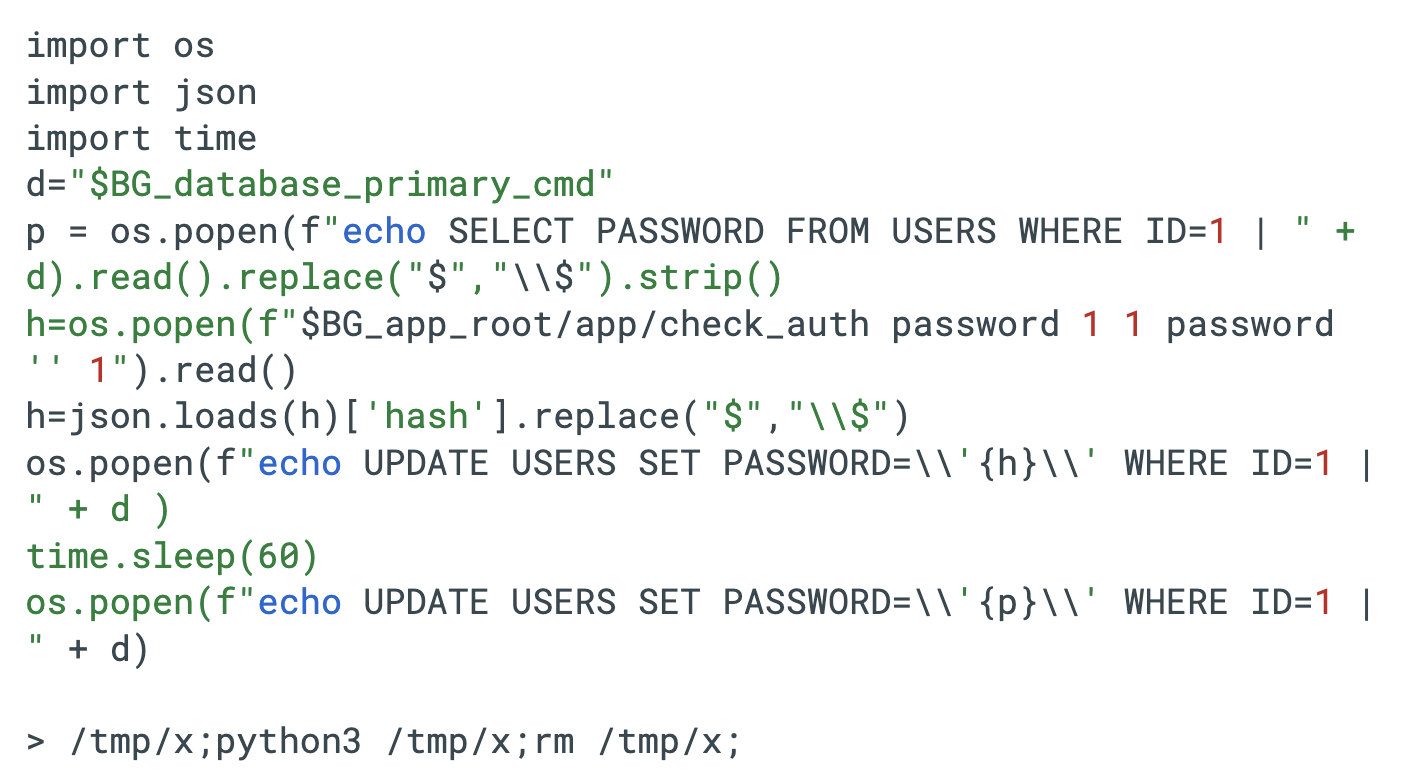
Self-hosted agent runtimes like OpenClaw significantly widen the execution boundary by ingesting untrusted text, downloading and executing external skills, and acting with the credentials of the host, creating risks of credential exposure, persistent memory manipulation, and host compromise. Organizations should treat OpenClaw as untrusted code execution and, if evaluated, run it only in isolated environments with dedicated non-privileged credentials, continuous monitoring, and a rebuild plan. #OpenClaw #Moltbook
Category: Threat Research
CVE-2026-1731 is a critical pre-authentication remote code execution vulnerability in BeyondTrust Remote Support’s thin-scc-wrapper WebSocket handler that Unit 42 has observed being actively exploited to deploy web shells, backdoors (including SparkRAT and VShell), create accounts, move laterally, and exfiltrate data across multiple sectors and countries. CISA added the vulnerability to its…

AhnLab’s January 2026 report summarizes ransomware activity and the number of affected systems using AhnLab diagnostic names and data collected from Dedicated Leak Sites (DLS). The report highlights notable attacks against critical infrastructure sectors (manufacturing, healthcare, finance), continued activity from existing groups and emergence of new groups, and notes a change…

The report analyzes a range of cyber threats against the financial sector, including database leaks, sales of access rights on dark web forums, phishing campaigns, and ransomware incidents affecting major financial organizations. It highlights specific cases involving leaked credentials and datasets (H***, V***, T***), threat actors claiming access (PanchoVilla, Solonik, CLOP),…

Attack Discovery, Workflows, and Agent Builder were combined to automatically detect, confirm, and triage a Chrysalis backdoor campaign delivered via a Notepad++ update supply-chain compromise, collapsing dozens of alerts into a single verified incident and creating a case and Slack channel with on-call responders already added. The automation verified C2, performed VirusTotal checks, ran ES|QL hunts, and executed incident actions (isolation, user suspension, IOC sweeps) in under four minutes instead of hours. #Chrysalis #LotusBlossom

The article describes how a mature underground access economy commoditizes remote credentials, infostealer logs, breach databases, and web shells, letting specialists trade and monetize each part of the attack chain. This industrialized market features products like Fortinet VPN credentials, infostealer families (e.g., Redline), and operators such as DAISY CLOUD that sell…

GrayCharlie, active since mid-2023 and overlapping with SmartApeSG, compromises WordPress sites to inject externally hosted JavaScript that redirects visitors to NetSupport RAT payloads delivered via fake browser update pages or ClickFix lures, often resulting in Stealc and SectopRAT follow-on deployments. Insikt Group mapped extensive infrastructure tied to MivoCloud and HZ Hosting Ltd, identified multiple NetSupport RAT C2 clusters and staging domains, and observed a likely supply‑chain compromise impacting numerous US law firm websites. #GrayCharlie #NetSupportRAT
Researchers uncovered hybrid cryptocurrency investment scams that combine malvertising-driven acquisition with messaging-app-based pig butchering, primarily targeting users in Japan and broader Asia and leveraging more than 23,000 RDGA-generated and lookalike domains. The campaigns use shared website frameworks, lookalike domains (e.g., youtubefind[.]top), and AI/automated chatbots inside legitimate messaging apps to socially engineer victims into sending funds. #RDGA #youtubefind_top

Acronis TRU uncovered a targeted espionage campaign named CRESCENTHARVEST that uses Farsi-language protest lures to trick victims into opening malicious .LNK shortcuts and install a multi-module stealer/RAT. The implant chain relies on DLL sideloading via a signed Google binary, extracts browser app‑bound keys, logs keystrokes and exfiltrates data to a C2 in Riga. #CRESCENTHARVEST #AcronisTRU

Check Point Research demonstrates that AI assistants with web-browsing and URL-fetch capabilities (e.g., Grok and Microsoft Copilot) can be abused as covert command-and-control relays by having the model fetch attacker-controlled URLs and return responses, enabling bidirectional C2 without API keys or accounts. This technique can be combined with WebView2-based implants and prompt-driven workflows to create AI-Driven malware that dynamically decides actions, prioritizes targets and data, and evades traditional detection controls. #Grok #MicrosoftCopilot
Two critical zero-day remote code execution vulnerabilities (CVE-2026-1281 and CVE-2026-1340) in Ivanti Endpoint Manager Mobile (EPMM) are being actively exploited to gain unauthenticated control of enterprise MDM infrastructure. Unit 42 documents automated mass scanning and exploitation leading to reverse shells, web shell installation, malware downloads (including the Nezha monitoring agent), and…

Sinobi is a Ransomware-as-a-Service operation that emerged in mid-2025 and appears to be a rebrand or successor to the Lynx and INC Ransom families based on significant code overlap. The group uses a closed affiliate model and double-extortion tactics—gaining access via compromised credentials and CVE exploits, exfiltrating data with Rclone, and encrypting files with Curve-25519/AES-128-CTR to demand payment. #Sinobi #Lynx
.png)
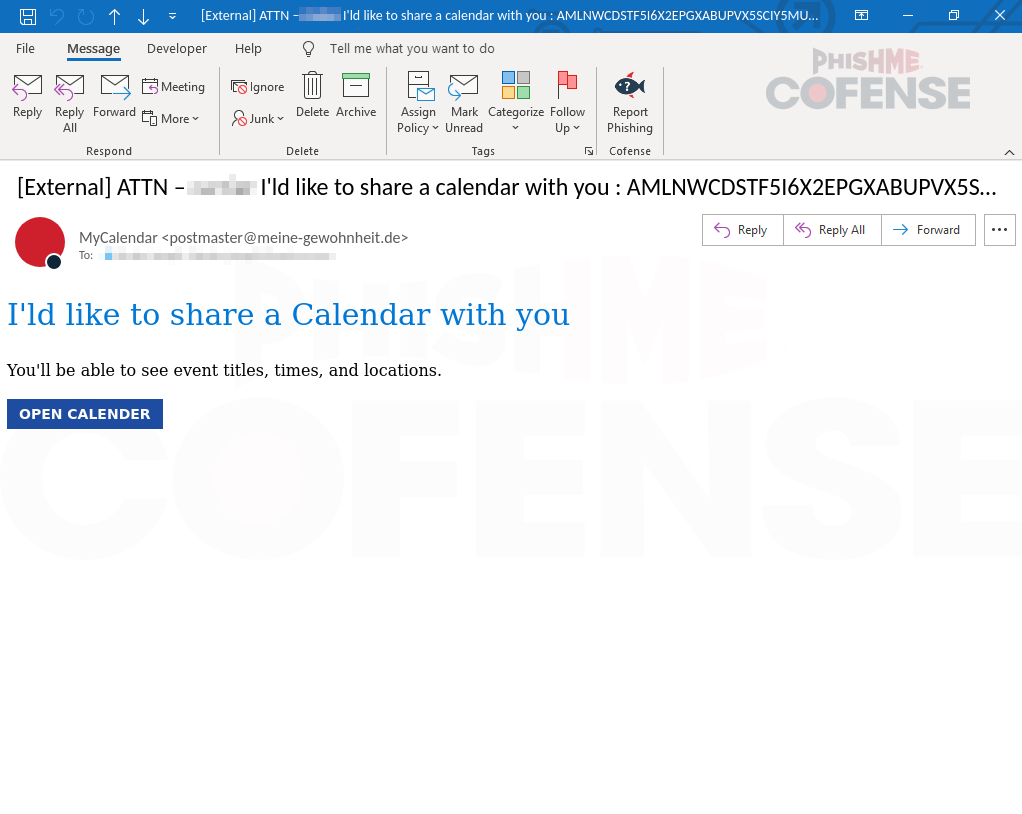
Cofense PDC observed threat actors using spoofed Microsoft and Google Calendar invitations with embedded malicious links that redirect victims to fake login pages to harvest credentials. Users should carefully verify sender addresses and URLs before clicking calendar invites and organizations should deploy real-time defenses to detect and respond to these calendar-based phishing campaigns. #Microsoft #GoogleCalendar

Mandiant and Google Threat Intelligence Group identified exploitation of a critical Dell RecoverPoint for Virtual Machines vulnerability (CVE-2026-22769) by UNC6201 beginning in mid-2024, enabling lateral movement, persistent access, and deployment of SLAYSTYLE, BRICKSTORM, and a new AOT-compiled backdoor called GRIMBOLT. Dell published remediations and the report details Tomcat Manager WAR deployment using hard-coded admin credentials, persistence via convert_hosts.sh modification, VMware pivoting using “Ghost NICs,” and iptables-based Single Packet Authorization techniques. #CVE-2026-22769 #UNC6201 #GRIMBOLT #BRICKSTORM #SLAYSTYLE #DellRecoverPoint
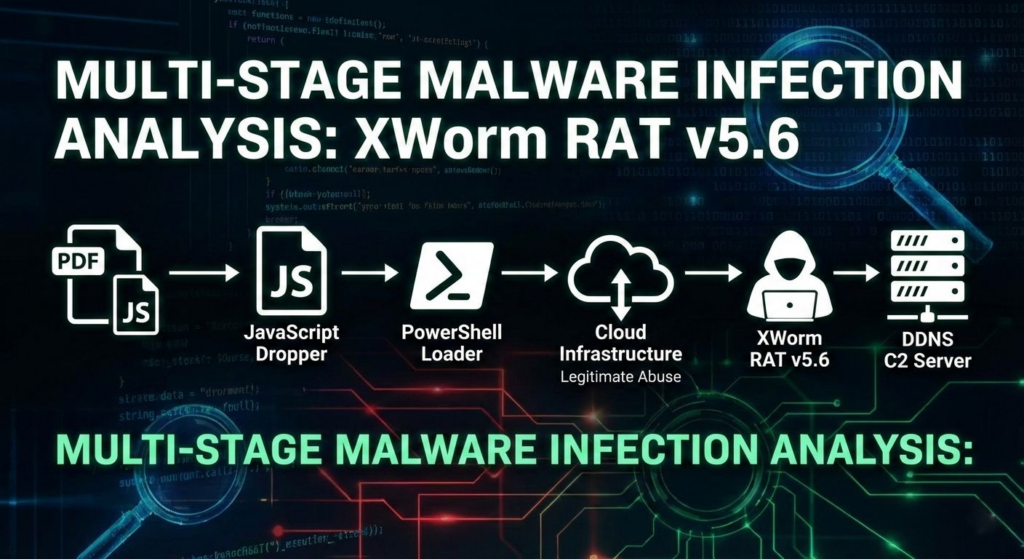
A multi-stage campaign targeting Brazilian users delivers XWorm via a deceptive “banking receipt” WSH dropper that uses obfuscated JavaScript, WMI-spawned PowerShell, Cloudinary-hosted steganography, and in-memory .NET loading to minimize early detection. The infection establishes persistence by registering a Scheduled Task via .NET APIs and injects the XWorm payload into CasPol.exe, enabling…