CVE-2026-1731 is a critical pre-authentication remote code execution vulnerability in BeyondTrust Remote Support’s thin-scc-wrapper WebSocket handler that Unit 42 has observed being actively exploited to deploy web shells, backdoors (including SparkRAT and VShell), create accounts, move laterally, and exfiltrate data across multiple sectors and countries. CISA added the vulnerability to its KEV catalog, Cortex Xpanse found 10,600+ exposed instances, and Palo Alto Networks provided detection queries, mitigation guidance, and product protections to help defenders respond. #CVE-2026-1731 #SparkRAT
Keypoints
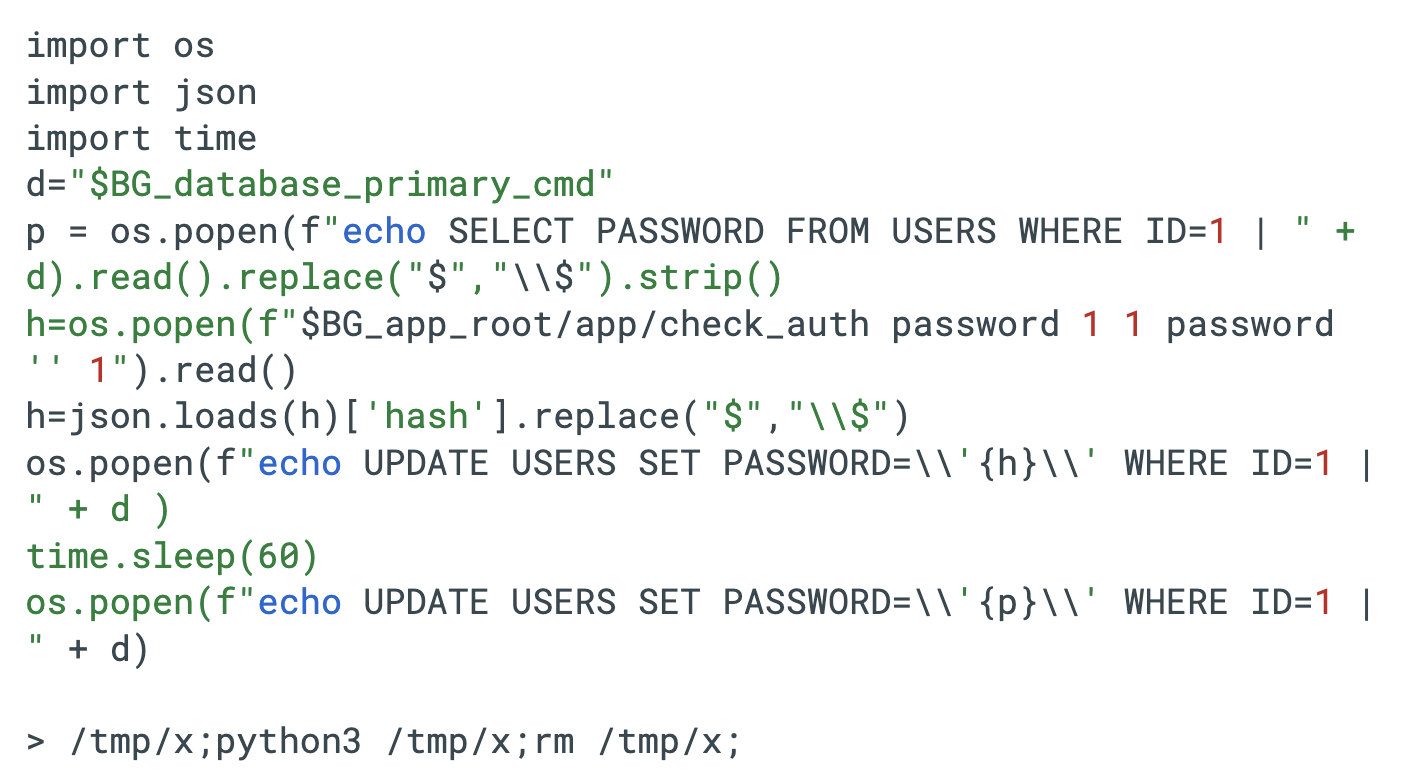
- Unit 42 confirmed active exploitation of CVE-2026-1731, a bash arithmetic-based OS command injection in BeyondTrust’s thin-scc-wrapper WebSocket handling, yielding pre-authenticated RCE (CVSS v4 9.9).
- Observed attacker activities include network reconnaissance, account creation, webshell deployment, C2 traffic, backdoor/RAT deployment (SparkRAT, VShell), lateral movement, and data theft.
- Attacks have impacted organizations across financial services, legal, high tech, higher education, wholesale/retail, and healthcare in the U.S., France, Germany, Australia and Canada.
- CISA added CVE-2026-1731 to the Known Exploited Vulnerabilities Catalog on Feb 13, 2026, mandating urgent remediation for federal agencies and prioritization by the private sector.
- Palo Alto Networks telemetry (Cortex Xpanse) identified 10,600+ exposed vulnerable instances, and Unit 42 published XQL detection queries for Windows and Linux post-exploitation via Bomgar sessions.
- Recommended mitigations include applying vendor patches (specified Remote Support/PRA versions), limiting administrative interfaces via segmentation or zero-trust, and using Palo Alto Networks product protections and Unit 42 incident response services.
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – Attackers exploited a WebSocket handshake vulnerability to achieve pre-authentication RCE by injecting a crafted remoteVersion payload into thin-scc-wrapper during the handshake (‘pre-authentication remote code execution (RCE) issue within BeyondTrust remote support software.’).
Indicators of Compromise
- [IP Address ] attacker C2 and payload hosting – 23.162.40[.]187, 138.197.14[.]95/ws (SparkRAT), and 16 more IPs observed in infrastructure listings.
- [Domain/URL ] OAST/C2 and payload download endpoints – q0r2e5q2dzbykcox9qmkptm12s8mwb.oastify[.]com, hxxps[:]//transfer.weepee[.]io/7nZw7/blue.drx, and other malicious/abused URLs noted in the report.
- [File Hash ] malware and backdoor artifacts – 9f431d5549a03aee92cfd2bdbbe90f1c91e965c99e90a0c9ad5a001f4e80c350 (SparkRAT), 98a7b0900a9072bb40af579ec372da7b27af12b15868394df51fefe290ab176b (VShell), and 7 more hashes.
- [File Name ] web shells and droppers used for persistence and C2 – aws.php, file_save.php, blue.drx, and additional backdoor/dropper filenames recovered.
Read more: https://unit42.paloaltonetworks.com/beyondtrust-cve-2026-1731/