Moonrise is a previously undetected Go-based remote access trojan that establishes WebSocket C2 and full interactive control of an endpoint before static detections trigger. Detection requires behavior-based analysis and faster SOC workflows to catch credential theft, remote command execution, persistence, and user-monitoring activity early. #Moonrise #ANY.RUN
Keypoints
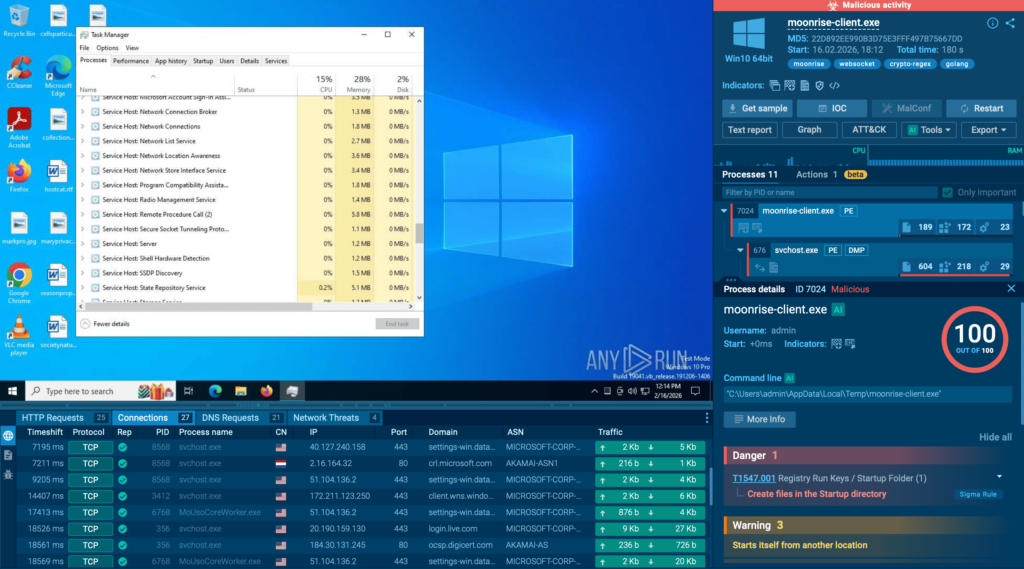
- Moonrise is a Go-based RAT that evaded static detection at the time of analysis and established active C2 before vendor alerts appeared.
- The malware provides a broad command set including credential theft, clipboard and keylogging, screen/webcam/microphone capture, file upload/download/execute, and remote command/process control.
- Initial C2 uses a WebSocket-like session with client_hello, connected, and ping/pong messages to maintain persistent operator connectivity.
- Operator-visible behaviors include process_list, file_list, screenshot attempts, process_kill, file_upload/file_run, and explorer_restart, enabling escalation from reconnaissance to full control.
- Privilege and persistence capabilities (uac_bypass, rootkit_enable/disable, watchdog and protection configs) increase dwell time and complicate removal.
- ANY.RUN recommends a 3-step detection loop—monitoring for new infrastructure, rapid enrichment plus sandbox execution for behavioral confirmation, and threat hunting from confirmed indicators—to reduce exposure.
MITRE Techniques
- [T1071 ] Application Layer Protocol – Moonrise maintains C2 over WebSocket-like messaging (‘client_hello connected ping/pong’).
- [T1059 ] Command and Scripting Interpreter – The RAT executes remote commands and spawns shells (e.g., ‘svchost.exe spawning cmd.exe to execute system commands’).
- [T1105 ] Ingress Tool Transfer – Operator-driven file_upload and file_download allow additional payloads to be transferred to the host (‘file_upload file_download’).
- [T1057 ] Process Discovery – The malware enumerates running processes using ‘process_list’ to survey the environment (‘process_list’).
- [T1083 ] File and Directory Discovery – Moonrise inspects file structures with ‘file_list’ to find accessible data (‘file_list’).
- [T1056 ] Input Capture – Keylogging and clipboard monitoring are used to capture credentials and sensitive data (‘keylogger_start keylogger_logs clipboard_history’).
- [T1113 ] Screen Capture – The RAT attempts screenshots and can stream screen content for operator surveillance (‘screenshot screen_stream_start screen_stream_stop’).
- [T1123 ] Audio Capture – Microphone recording capability enables audio capture of user activity (‘microphone_record’).
- [T1041 ] Exfiltration Over C2 Channel – Collected data (files, keylogger logs, clipboard contents) can be transferred via the established C2 channel (‘file_download keylogger_logs clipboard_history’).
- [T1547 ] Boot or Logon Autostart Execution – Presence of persistence-related commands suggests support for maintaining execution across reboots (‘persistence and privilege-related functions increase dwell time’).
- [T1548 ] Abuse Elevation Control Mechanism – The sample includes uac_bypass and other privilege-manipulation commands indicating UAC or elevation abuse capabilities (‘uac_bypass rootkit_enable rootkit_disable’).
- [T1497 ] Defacement or Disruption (User Interface) – User-facing commands (fun_message, fun_wallpaper, fun_bsod, fun_restart, fun_shutdown) allow visible disruption or coercion of user experience (‘fun_message fun_wallpaper fun_bsod’).
Indicators of Compromise
- [IP Address ] C2 infrastructure observed – 193[.]23[.]199[.]88
- [File Hashes ] Malware sample hashes observed – c7fd265b23b2255729eed688a211f8c3bd2192834c00e4959d1f17a0b697cd5e, 8a422b8c4c6f9a183848f8d3d95ace69abb870549b593c080946eaed9e5457ad, and 5 other hashes
- [File Names ] Process/file names observed in behavior – svchost.exe (spawned), cmd.exe (spawned)
Read more: https://any.run/cybersecurity-blog/cybersecurity-blog/moonrise-rat-detected/