Microsoft Defender researchers observed phishing campaigns that abuse OAuth’s built-in redirection and silent authentication behavior (e.g., prompt=none and invalid scope) to redirect government and public-sector users to attacker-controlled landing pages without stealing tokens. Microsoft flagged malicious activity across email, identity, and endpoint signals, Microsoft Entra disabled the observed OAuth applications, but related OAuth redirect activity and malicious redirects (including use of EvilProxy and malware delivery) persist and require ongoing monitoring. #MicrosoftEntraID #EvilProxy
Keypoints
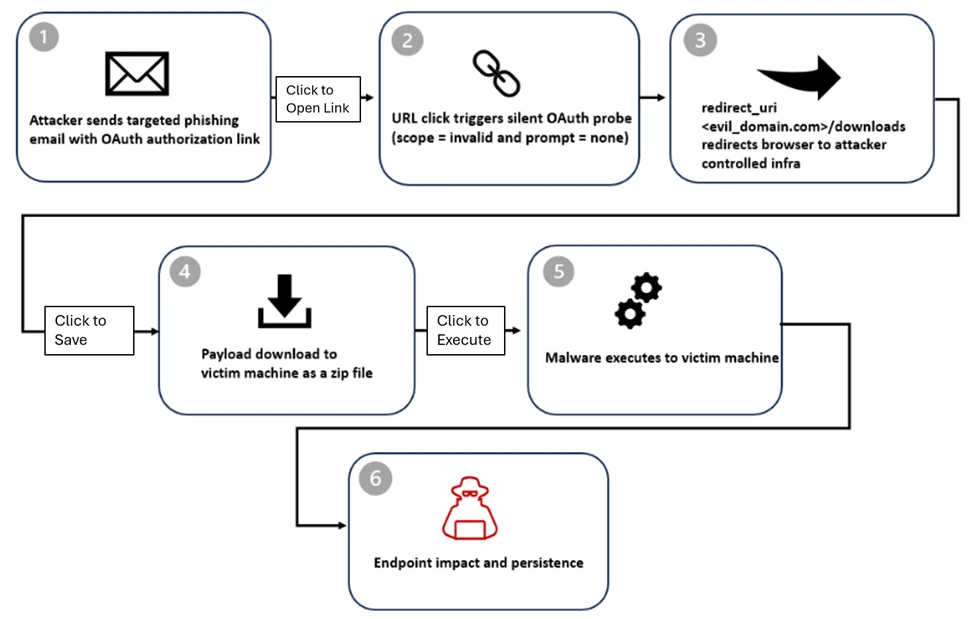
- Researchers detected phishing campaigns that deliberately abuse OAuth authorization error-handling (prompt=none, invalid scope, etc.) to force silent redirects from trusted identity providers to attacker-controlled landing pages.
- Attackers register malicious OAuth applications (attacker-controlled tenant and redirect URIs) and embed crafted OAuth URLs in phishing lures to increase credibility and bypass typical phishing defenses.
- Delivery methods include email links, PDF attachments with embedded URLs, and fake calendar (.ics) invites; social engineering themes included document sharing, payroll/SSN, Teams meeting invites, and password resets.
- Actors repurposed the OAuth state parameter to pass target email addresses (plaintext, hex, Base64, or custom encoding) so phishing pages auto-populate victim data and appear more legitimate.
- Redirects commonly led to phishing frameworks such as EvilProxy or to /download/ paths that delivered ZIP archives with LNK shortcuts and HTML smuggling loaders, transitioning the attack from identity reconnaissance to endpoint compromise.
- Endpoint activity included PowerShell execution, tar extraction of steam_monitor.exe, DLL side-loading of crashhandler.dll (which decrypted and executed crashlog.dat), and outbound C2 connections; Defender detections and hunting queries were provided to locate related activity.
- Mitigations recommended: govern OAuth apps and user consent, apply Conditional Access and identity protection, enable cross-domain detection across email/identity/endpoint, block known IOCs, and monitor for auth URLs with prompt=none and encoded state parameters.
MITRE Techniques
- [T1566.001 ] Phishing: Spearphishing Link – Attackers embedded crafted OAuth authorization URLs into emails and PDFs to trick users into clicking; ‘Several threat actors distributed phishing campaigns containing OAuth redirect URLs.’
- [T1189 ] Drive-by Compromise – Redirects to attacker-controlled pages that automatically delivered ZIP archives and malicious loaders; ‘After redirection, victims were sent to a /download/XXXX path, where a ZIP file was automatically downloaded to the target device.’
- [T1574 ] Hijack Execution Flow – DLL side-loading used to execute final payload in memory via a legitimate binary; ‘PowerShell then launched the legitimate steam_monitor.exe, which was leveraged to side-load the malicious crashhandler.dll.’
- [T1071.001 ] Application Layer Protocol: Web Protocols – Outbound C2 connections over web protocols after payload execution; ‘ultimately establishing an outbound connection to an external C2 endpoint.’
- [T1078 ] Valid Accounts (application abuse) – Abuse of legitimate OAuth flows and registered applications to leverage trust and redirect users without stealing tokens; ‘The attack begins with the creation of a malicious application in an actor-controlled tenant, configured with a redirect URI pointing to a malicious domain.’
Indicators of Compromise
- [OAuth Client IDs ] Malicious OAuth application client IDs observed – 9a36eaa2-cf9d-4e50-ad3e-58c9b5c04255, 89430f84-6c29-43f8-9b23-62871a31441, and 20+ other client IDs.
- [Initial redirection URLs / Domains ] Attacker-controlled redirect landing pages used after OAuth error redirects – https[:]//dynamic-entry[.]powerappsportals[.]com/dynamics/, https[:]//calltask[.]im/cpcounting/via-secureplatform/quick/, and additional domains like westsecure.powerappsportals[.]com, memointernals.powerappsportals[.]com.
- [File names / Payload components ] Downloaded and executed payload filenames observed – steam_monitor.exe, crashhandler.dll, crashlog.dat (delivered inside ZIPs and LNKs).
- [Malware / Detections ] Defender detection names for components of this campaign – Trojan:Win32/Malgent, Trojan:Win32/Korplug, and others such as Trojan:Win32/Znyonm and Trojan:Win32/GreedyRobin.B!dha.
- [Email attachments / Delivery artifacts ] Phishing and delivery artifacts used in campaigns – .ics calendar invite files, ZIP archives containing .LNK shortcut files and HTML smuggling loaders.
- [Suspicious OAuth URL parameters ] OAuth authorization request patterns used to trigger error redirects – examples include ‘prompt=none’ with ‘scope=‘ in Entra ID and Google URLs (e.g., login.microsoftonline.com … ?prompt=none&scope=, accounts.google.com … ?prompt=none … &state= &redirect_uri=).