On Feb. 28, 2026, the United States and Israel launched coordinated strikes (Operation Epic Fury / Operation Roaring Lion), triggering a multi-vector Iranian retaliatory campaign and a severe national internet outage that reduced connectivity to 1–4%. Unit 42 observed active SMS/phishing campaigns delivering a malicious RedAlert APK and a widespread surge in hacktivist and state-aligned disruptive activity claimed by groups such as Handala Hack; recommended mitigations include layered defenses, offline backups, patching, phishing training, and contacting Unit 42 for incident response. #OperationEpicFury #HandalaHack
Keypoints
- On Feb. 28, 2026, joint US-Israel kinetic operations triggered Iran’s internet connectivity to drop to 1–4%, degrading leadership and command-and-control capabilities and limiting near-term coordination by Iran-based state actors.
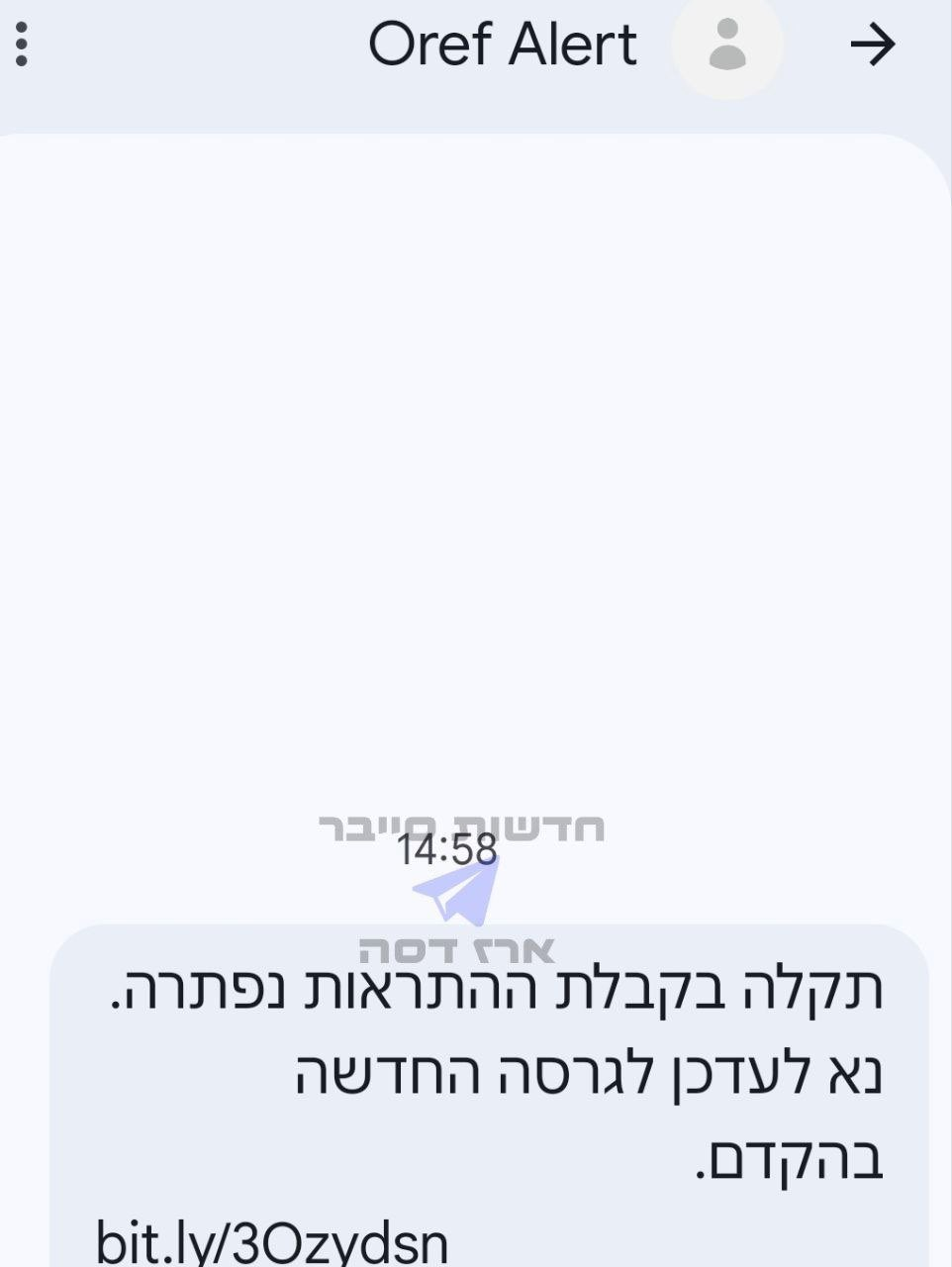
- Unit 42 identified an active SMS/phishing campaign using a malicious replica of the Israeli Home Front Command RedAlert application (APK) to deliver mobile surveillance and data-exfiltrating malware.
- There has been a surge of hacktivist activity—estimated ~60 groups—including Iran-aligned personas (Handala Hack, APT Iran, Cyber Islamic Resistance, FAD Team, Evil Markhors, Sylhet Gang, 313 Team, DieNet) conducting DDoS, hack-and-leak, wiper, and defacement operations.
- State-aligned actors inside Iran may be operationally isolated or acting autonomously due to connectivity and command degradation, while Iran-aligned actors outside the country and opportunistic third parties may continue low-to-medium sophistication disruptive operations.
- Pro-Russian hacktivist groups (Cardinal, NoName057(16), Russian Legion) have claimed disruptive intrusions and access to Israeli systems, including allegations involving IDF documents and Iron Dome components.
- Cybercriminals and RaaS affiliates are exploiting the conflict with social-engineering vishing scams (UAE) and public leak postings (Tarnished Scorpius listing an Israeli company), increasing opportunistic risk to organizations in the region.
- Recommended mitigations include offline backups, out-of-band verification for requests, patching internet-facing assets, phishing/social-engineering training, geographic IP blocking where appropriate, and preparing communications and continuity plans; Unit 42 incident response is available for engagement.
MITRE Techniques
- [T1566 ] Phishing – SMS/phishing lures were used to distribute a malicious RedAlert Android package (‘active phishing campaign using a malicious replica of the Israeli Home Front Command RedAlert application.’)
- [T1566.002 ] Spearphishing Link – Targeted links (including shortened URLs) delivered the malicious APK and credential-harvesting lures (‘SMS phishing message to download malicious RedAlert application.’)
- [T1190 ] Exploit Public-Facing Application – Actors leveraged exploitation of known vulnerabilities to gain access and enable espionage or disruption (‘the exploitation of known vulnerabilities’)
- [T1498 ] Network Denial of Service – Coordinated distributed denial-of-service (DDoS) attacks were used to disrupt Israeli and Western infrastructure (‘distributed-denial-of-service (DDoS) attacks’)
- [T1485 ] Data Destruction – Wiper malware and permanent data destruction were employed against targeted systems, including claims against SCADA/PLC assets (‘wiper attacks’ and ‘data-wiping operations’)
- [T1491 ] Defacement – Website defacements were used as a disruptive and propagandistic tactic in coordinated hacktivist campaigns (‘website defacement’)
- [T1041 ] Exfiltration – Data exfiltration was observed as part of hack-and-leak operations and combined espionage/disruption campaigns (‘blends data exfiltration with cyber operations’)
- [T1195 ] Supply Chain Compromise – State-sponsored campaigns may target victim supply chains, vendors, and providers to amplify impact (‘State-sponsored campaigns might target their victim’s supply-chains, critical infrastructure, vendors or providers.’)
- [T1583 ] Acquire Infrastructure – Use of covert infrastructure and operational infrastructure to support espionage and long-term operations was reported (‘the use of covert infrastructure for espionage’)
- [T1566 ] Phone-based Social Engineering (Vishing) – Social-engineering vishing scams impersonating official entities were used to steal credentials and identity numbers (‘a social engineering vishing scam to steal credentials… impersonating the Ministry of Interior… prompting for the victim’s Emirates Identification Number (EID)’)
Indicators of Compromise
- [URL ] Malicious APK distribution and phishing links – hxxps[:]www[.]shirideitch[.]com/wp-content/uploads/2022/06/RedAlert[.]apk (malicious RedAlert APK distribution), hxxps[:]//bit[.]ly/4tWJhQh (shortened phishing link)
- [API Endpoint ] Analytics/command endpoint used by malicious mobile payload – hxxps[:]//api[.]ra-backup[.]com/analytics/submit.php (reported analytics/submit endpoint associated with the APK)
- [File Name ] Malicious installer – RedAlert.apk (replica of the Israeli Home Front Command RedAlert application used to deliver mobile surveillance and exfiltration)
Read more: https://unit42.paloaltonetworks.com/iranian-cyberattacks-2026/