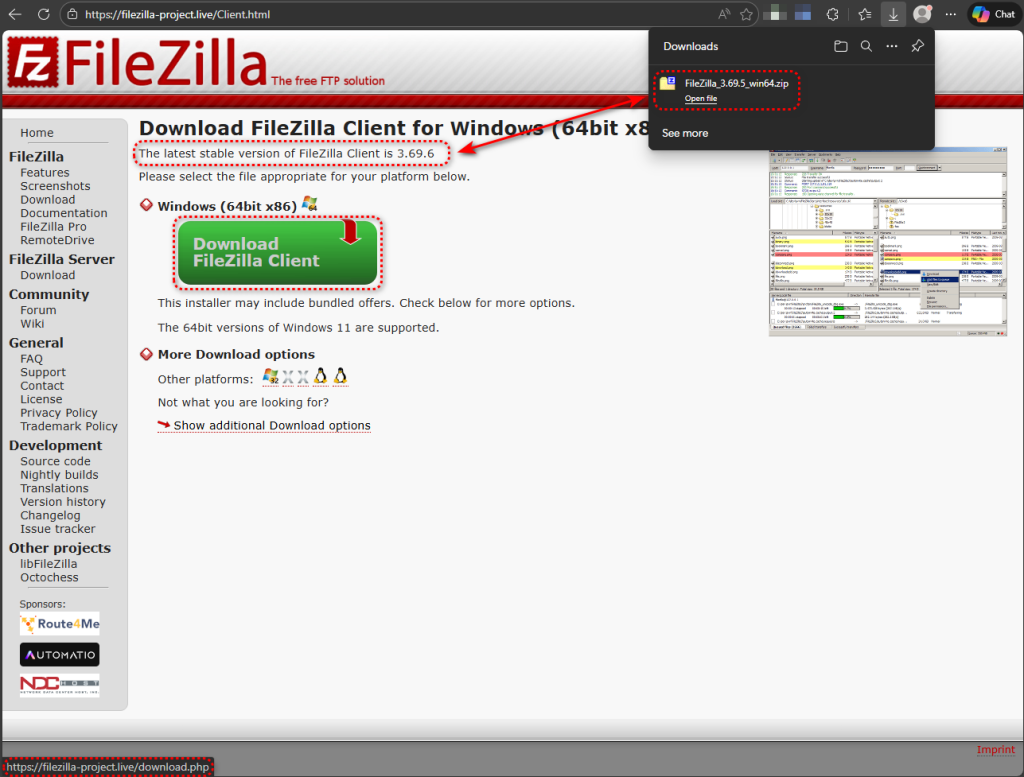
A trojanized portable build of FileZilla 3.69.5 is circulating on a lookalike site and contains a malicious version.dll that is loaded via DLL search-order hijacking, allowing the malware to run inside filezilla.exe and steal saved FTP credentials. The loader uses sandbox-evasion checks and DNS-over-HTTPS to contact its C2 infrastructure (welcome.supp0v3[.]com and 95.216.51.236:31415), with observable IOCs including two SHA-256 hashes and the fake domain filezilla-project[.]live; #FileZilla #version.dll
Keypoints
- A trojanized FileZilla 3.69.5 portable archive contains a single malicious DLL (version.dll) that triggers DLL search-order hijacking when filezilla.exe is launched.
- The malicious DLL runs inside filezilla.exe, can access saved FTP credentials, and calls back to C2 infrastructure via DNS-over-HTTPS and a direct TCP connection to 95.216.51.236:31415.
- Distribution relies on deception (lookalike domain filezilla-project[.]live and poisoned search results) rather than exploiting a FileZilla vulnerability.
- Behavioral analysis shows sandbox and VM detection, DLL proxying behavior, process manipulation, registry autorun modifications, runtime .NET compilation, and file-encryption API calls.
- Key forensic clues include the unexpected version.dll inside the portable folder and a single-file timestamp anomaly different from the rest of the archive.
- Recommended actions: verify downloads from the official site, check for version.dll in FileZilla directories, monitor DoH traffic from non-browser processes, and block the listed domains/IPs.
MITRE Techniques
- [T1038 ] DLL Search Order Hijacking – used to load the malicious library from the application folder before System32 (‘DLL search order hijacking, where an application loads a library from its own directory before checking the Windows system folder’).
- [T1574.001 ] DLL Side‑Loading / Proxying – the malicious DLL attempts to forward calls to a renamed original (‘the malicious DLL searches for version_original.dll in the same directory…telltale sign of DLL proxying’).
- [T1055 ] Process Injection – the campaign exhibits behaviors of creating suspended processes and writing to other processes’ memory (‘Creating suspended processes and writing to other processes’ memory’).
- [T1555 ] Credentials from Password Stores – the sideloaded DLL harvests saved FTP credentials from the client (‘the malware can access saved FTP credentials’).
- [T1497 ] Virtualization/Sandbox Evasion – the loader performs VM and sandbox checks before executing payloads (‘BIOS version checks, system manufacturer queries, VirtualBox registry key probing…’).
- [T1071.001 ] Application Layer Protocol: Web Protocols (HTTPS/DoH) – C2 resolution uses DNS-over-HTTPS via Cloudflare (‘https://1.1.1.1/dns-query?name=welcome.supp0v3[.]com&type=A’).
- [T1547.001 ] Registry Run Keys / Startup Folder – registry changes consistent with autorun persistence were observed (‘Registry modifications consistent with autorun persistence’).
- [T1486 ] Data Encrypted for Impact – behavioral detections flagged multiple file encryption API calls (‘Multiple file encryption API calls’).
- [T1204.002 ] User Execution: Malicious File – infection requires a user to download and run a tampered archive from an unofficial site (‘depends on someone downloading the modified copy from an unofficial website and running it’).
- [T1059 ] Command and Scripting Interpreter – the loader or droppers perform runtime .NET compilation via csc.exe (‘Runtime .NET compilation via csc.exe’).
Indicators of Compromise
- [File hash ] trojanized artifacts – 665cca285680df321b63ad5106b167db9169afe30c17d349d80682837edcc755 (trojanized FileZilla archive FileZilla_3.69.5_win64.zip), e4c6f8ee8c946c6bd7873274e6ed9e41dec97e05890fa99c73f4309b60fd3da4 (trojanized version.dll)
- [Domain ] distribution and C2 – filezilla-project[.]live (fake download site), welcome.supp0v3[.]com (C2 callback/staging)
- [Network address ] C2 server – 95.216.51[.]236:31415 (persistent TCP callback attempts observed)
- [File name ] malicious binaries/artifacts – version.dll (malicious DLL placed in FileZilla folder), FileZilla_3.69.5_win64.zip (trojanized archive filename)