NetSPI’s Detective Controls Testing (DCT) Team integrated Azure capabilities into their DCT product and demonstrated multiple methods to achieve code execution on Azure Virtual Machines (VMs) and Virtual Machine Scale Sets (VMSSs) using Entra ID credentials. The post details Invoke-RunCommand, Run-Command objects, Custom Script Extension, Desired State Configuration, VMSS variants, REST/CLI/PowerShell examples, cleanup considerations, and platform-level detection guidance via Azure Activity Log. #NetSPI #AzureVM
Keypoints
- NetSPI integrated multiple Azure execution vectors into the DCT platform to validate detective controls for Azure VMs and VMSSs.
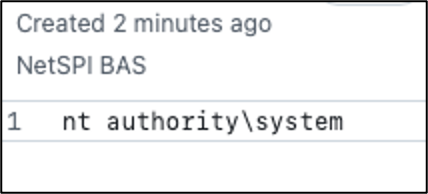
- Execution methods demonstrated: Invoke Run-Command, create Run-Command objects, Custom Script Extension, and Desired State Configuration (DSC) for Windows.
- Examples provided for Azure CLI, Azure PowerShell, and direct REST API calls (including authentication via Entra ID tokens).
- Custom Script Extension and DSC require hosting payloads externally (Azure Storage or pre-signed URLs) and may persist on hosts if not removed.
- VMSS invocations require an instance ID and Custom Script Extensions applied to a scale set execute across all instances; output retrieval varies by method.
- Platform-level detection opportunities focus on Azure Activity Log events (RunCommand actions/writes, Extensions/Write, and VMSS write events) with recommended detection concepts and caveats.
MITRE Techniques
- [T1059.001 ] PowerShell – Used to execute commands and scripts on VMs via RunCommand and extensions; example commands include ‘RunPowerShellScript’ and ‘powershell -ExecutionPolicy Unrestricted -file ScriptExtension.ps1’ (‘RunPowerShellScript’; ‘powershell -ExecutionPolicy Unrestricted -file ScriptExtension.ps1’).
- [T1078 ] Valid Accounts – Use of legitimate Entra ID credentials to authenticate and invoke management APIs/CLI for code execution (‘can be used to achieve code execution on Azure VMs using Entra ID credentials’).
Indicators of Compromise
- [URL / Domain ] management and payload endpoints – https://management.azure.com (API endpoint), https://api.github.com/gists (exfiltration/payload POST), and https://.core.windows.net/… (storage blob URLs for script payloads).
- [File names ] script and extension artifacts observed – ScriptExtension.ps1, ScriptExtensionGist.ps1, BASDSC.ps1.zip (DSC payload), and other extension names like CustomScriptExtension, DSC.
- [Azure resource names / IDs ] example resource and subscription identifiers used in PoCs – VM/VMSS names: BAS-Windows, BAS-WindowsVMSS, run-command name BASExample; subscription GUID example: 12345678-1234-1234-1234-123456789abc.