Cato CTRL researcher Vitaly Simonovich disclosed CVE-2026-25611, a high-severity vulnerability in MongoDB’s OP_COMPRESSED wire-protocol handling that allows unauthenticated actors to force large memory allocations and crash servers. The flaw affects MongoDB versions with compression enabled (3.4+; enabled by default since 3.6, including Atlas when exposed) and was patched in coordination with MongoDB; mitigations include applying patches, restricting network exposure, and disabling compression if not needed. #CVE-2026-25611 #MongoDB
Keypoints
- Vulnerability CVE-2026-25611 exists in MongoDB’s OP_COMPRESSED handling where the server allocates memory based on the attacker-controlled uncompressedSize before verifying decompression.
- Pre-authentication exploit: no credentials required because the issue occurs during wire-protocol parsing before auth checks.
- High amplification: ~47KB of compressed data can force a 48MB allocation per connection (≈1027:1 amplification), enabling fast OOM crashes.
- Low bandwidth, few connections required: a 512MB instance can be crashed with ~10 connections; a 64GB server falls with ~1,350 connections.
- Default exposure risk: compression enabled by default since MongoDB 3.6; attacker access is most likely when instances are internet-exposed (e.g., 0.0.0.0/0 entries).
- Mitigations: update to patched versions (>= 8.2.4 / 8.0.18 / 7.0.29), restrict network access, implement connection limits, monitor memory, or disable compression.
MITRE Techniques
- [None ] No MITRE ATT&CK techniques explicitly mentioned – ‘No MITRE ATT&CK techniques were referenced in the article.’
Indicators of Compromise
- [Port ] Network exposure to default MongoDB port – 27017 (default MongoDB listener), and other configured database ports.
- [Wire protocol / Opcode ] Malformed OP_COMPRESSED messages and suspicious opcode values – opCode 2012 (OP_COMPRESSED); uncompressedSize fields set to large values like 48000000 bytes.
- [Packet characteristics ] Compressed packets with large claimed uncompressed size but small packet length – ~47KB compressed payloads claiming ~48,000,000 bytes uncompressed; OP_COMPRESSED packets 10MB.
- [Connection patterns ] High volume of concurrent TCP connections from a single source or rapid connection bursts – e.g., 10 concurrent connections causing OOM on 512MB instances, 198 connections for 8GB instances.
- [System / Process ] Host-level symptoms and logs indicating memory exhaustion – mongod exit code 137 (SIGKILL), OOM killer events in syslog, and rapid MongoDB process memory spikes.
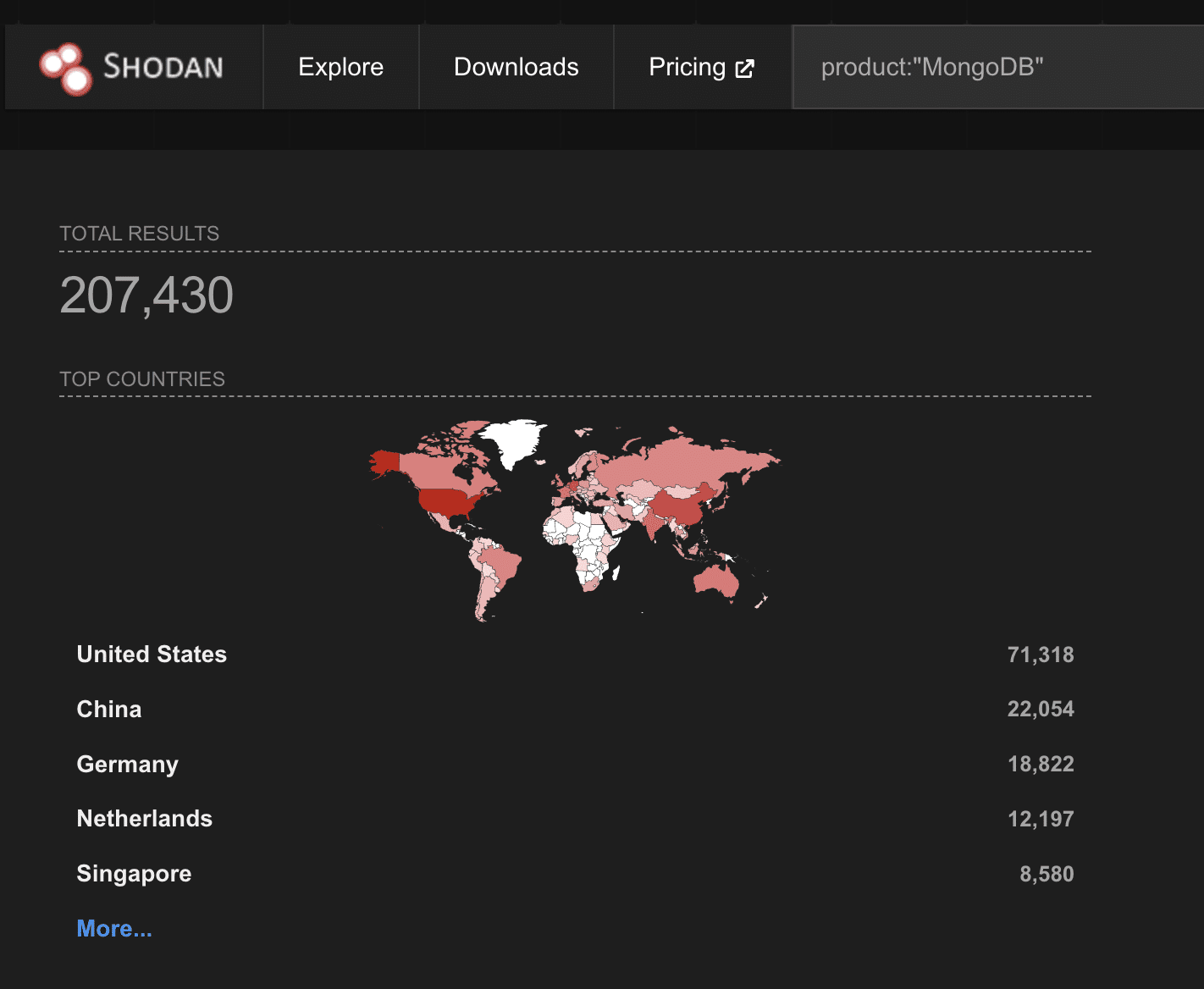
- [Discovery ] Public exposure metrics – Shodan-scanned count of 207,000+ internet-exposed MongoDB instances.
Read more: https://www.catonetworks.com/blog/cato-ctrl-new-mongodb-vulnerability-cve-2026-25611/