This report describes a multi-stage phishing campaign that delivered a ZIP containing a .url shortcut which triggered a WebDAV download and a chain of loaders (.wsh → .js → .bat) that established persistence, decrypted a payload and injected it into explorer.exe. Analysis revealed dynamic retrieval of C2 configuration from Pastebin and indicators linking the infrastructure to activity associated with the XWorm botnet, though attribution is not definitive. #ANBSC #XWorm
Keypoints
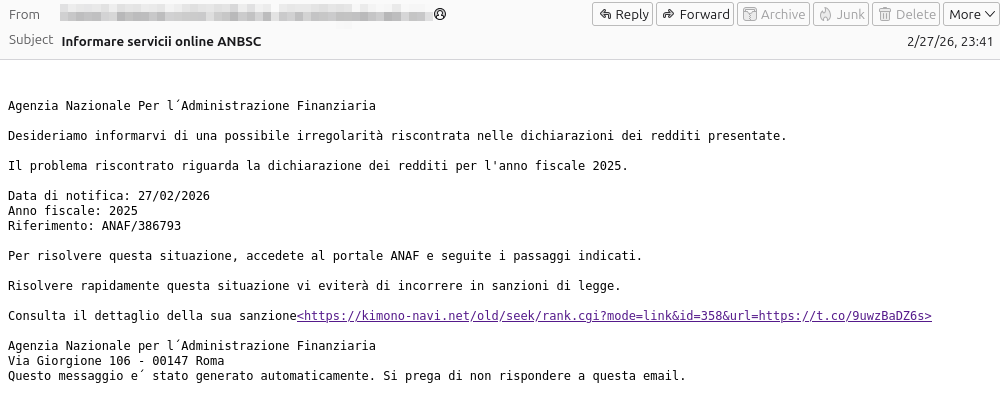
- The initial vector was a phishing email impersonating an Italian agency (ANBSC) with a link that led to a ZIP containing a Windows .url shortcut.
- The .url shortcut initiated a WebDAV over TLS download that retrieved a .wsh loader (elcqjyp.wsh), which then fetched a JavaScript stage (uweepyj.js) and a batch orchestrator (qidctgy.bat).
- The JavaScript used Windows Script Host COM objects (FileSystemObject, WScript.Shell) to download and execute the main batch file, which launched a legitimate PDF as a decoy and re-executed itself hidden via PowerShell.
- Persistence was achieved by creating %LOCALAPPDATA%mrbqm, installing an embedded Python runtime (python.exe 3.14.0) if absent, and placing a startup batch in the user’s Startup folder.
- The payload new.bin was decrypted by sb.py using three XOR keys stored in a.txt in three sequential passes, producing a final payload that was memory-injected into explorer.exe via CreateProcessA → VirtualAllocEx → WriteProcessMemory → QueueUserAPC → ResumeThread.
- C2 configuration was fetched dynamically from Pastebin entries (multiple pastes observed referencing ports 6000/7000/8000); community submissions linked the C2 to XWorm activity, but no definitive XWorm assembly was recovered.
MITRE Techniques
- [T1566] Phishing – Initial access via a phishing email impersonating an institutional actor (‘a phishing email with subject “Informare servicii online ANBSC”‘)
- [T1204.002] User Execution: Malicious Link/File – Victim clicks link and opens ZIP containing a .url shortcut that triggers remote retrieval (‘the ZIP containing a file with extension .url (Windows internet shortcut)’)
- [T1105] Ingress Tool Transfer – Multiple stages and files downloaded via WebDAV/TLS from a remote server (‘.url … indicates remote access via WebDAV on TLS’ and ‘the URL points to a .wsh script hosted on a domain exposed via Cloudflare Tunnel’)
- [T1059.004] Command and Scripting Interpreter: Windows Script Host – .wsh loader and JS using WSH COM objects to interact with file system and shell (‘the .wsh … calls a second-stage JavaScript .js’ and ‘the script JS uses Windows COM objects (Scripting.FileSystemObject and WScript.Shell)’)
- [T1059.003] Command and Scripting Interpreter: Windows Command Shell – Batch orchestrator qidctgy.bat executed via cmd /c to prepare environment and launch stages (‘downloads the main batch qidctgy.bat … and starts its execution with cmd /c’)
- [T1059.001] Command and Scripting Interpreter: PowerShell – Use of PowerShell to relaunch the dropper in hidden mode (‘relaunches itself in hidden mode via PowerShell with the option -WindowStyle Hidden’)
- [T1547.001] Boot or Logon Autostart Execution: Startup Folder – Persistence via a batch placed in the user’s Startup folder to execute at login (‘guarantees persistence by downloading an additional batch into the user’s Startup folder’)
- [T1055] Process Injection – Final payload injected into a legitimate process (explorer.exe) using CreateProcessA → VirtualAllocEx → WriteProcessMemory → QueueUserAPC → ResumeThread (‘at the end of the three XOR layers the final payload is injected in memory into explorer.exe through the sequence: CreateProcessA → VirtualAllocEx → WriteProcessMemory → QueueUserAPC → ResumeThread’)
- [T1102] Web Service – C2 configuration and endpoints retrieved dynamically from Pastebin entries used to configure communications (‘the IP address and port of the C2 are not hardcoded in the binary: they are retrieved dynamically from a URL hosted on Pastebin’)
- [T1090] Proxy/Tunneling – Use of Cloudflare Tunnel to expose the hosting domain used in the delivery chain (‘.wsh hosted on a domain exposed via Cloudflare Tunnel’)
Indicators of Compromise
- [File names] Delivery and loader artifacts – Fac_2026_1612320608.url, elcqjyp.wsh, uweepyj.js, qidctgy.bat
- [Payload files] Decryption and runtime files – sb.py, new.bin, a.txt (used for XOR decryption), and an embedded python.exe (Python 3.14.0)
- [File paths] Persistence locations – %LOCALAPPDATA%mrbqm (working directory and runtime extraction), Startup folder (startup batch)
- [Processes] Execution and injection targets – python.exe (launcher/runtime), explorer.exe (process into which payload was injected)
- [Network / C2] Remote configuration and C2 endpoints – Pastebin-hosted URL(s) used to retrieve C2 (multiple pastes observed referencing ports 6000, 7000, 8000) and C2 IP/port (identified during dynamic analysis, exact IP/port not published)
- [Infrastructure] Delivery hosting and exposure – domain exposed via Cloudflare Tunnel and a sender domain tied to a Spanish university email account (used to send the phishing message)