Since at least 2020, a China‑communicating threat cluster tracked as CL-UNK-1068 has targeted high‑value organizations across South, Southeast and East Asia using web shells, custom and open‑source tools, DLL side‑loading, FRP tunneling and extensive credential theft. The group’s toolkit includes GodZilla, AntSword, Xnote, ScanPortPlus and custom FRP variants and the activity shows a focus on exfiltrating configuration and database data for likely cyberespionage. #CL-UNK-1068 #Xnote
Keypoints
- CL-UNK-1068 is an activity cluster observed since 2020 targeting aviation, energy, government, law enforcement, pharmaceutical, technology and telecommunications organizations across South, Southeast and East Asia.
- Unit 42 attributes the cluster to a Chinese‑communicating threat actor based on tool provenance, linguistic artifacts and victimology, with primary intent assessed as cyberespionage.
- Initial access and lateral movement commonly involve deploying web shells (GodZilla, AntSword) and harvesting web server configuration files (web.config, .aspx, .asmx, .asax, .dll) for credential extraction and reconnaissance.
- The group uses DLL side‑loading of legitimate Python executables to load shellcode in memory and execute payloads (ScanPortPlus, PrintSpoofer, FRP), avoiding disk‑based payload execution.
- Credential theft techniques include Mimikatz, LsaRecorder, memory dumping with DumpIt + Volatility, SSMS sqlstudio.bin extraction (ssms.exe), and harvesting registry artifacts and application credentials via SuperDump and batch scripts.
- Persistent access and tunneling are achieved with custom‑compiled FRP instances (unique tokens and proxy names), and Linux backdoors like Xnote are used for additional capabilities such as DDoS and proxying.
MITRE Techniques
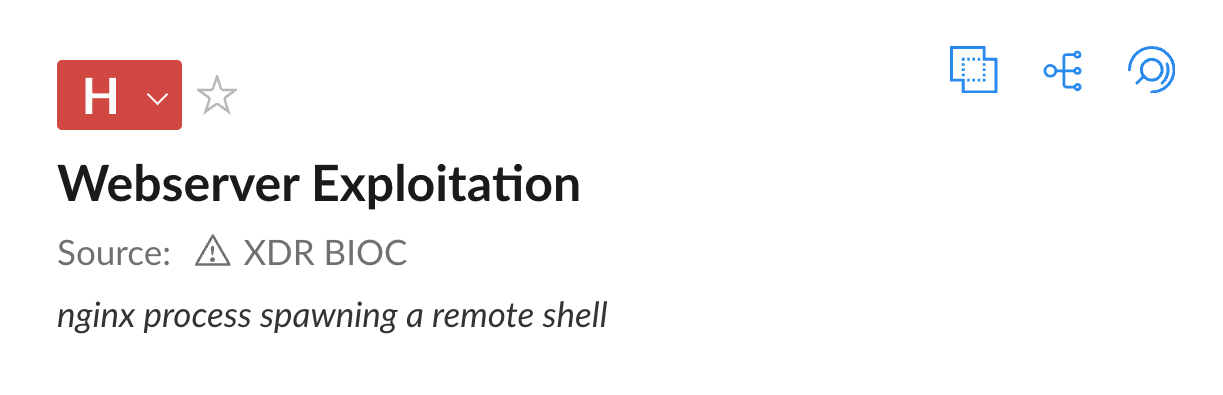
- [T1505 ] Web Shell – Initial access and persistence via web shells: (‘The initial access to environments targeted in CL-UNK-1068 activity is achieved by deploying and utilizing various web shells. We observed the attackers deploying the GodZilla web shell, and a variation of AntSword’)
- [T1574 ] DLL Side‑Loading (Hijack Execution Flow) – Using legitimate Python executables to load malicious DLLs and in‑memory shellcode: (‘use of legitimate Python executables to launch DLL side-loading attacks…python.exe side-loads a malicious loader named python20.dll’)
- [T1090 ] Proxy/Tunneling (FRP) – Establishing persistent access and bypassing firewalls via custom FRP builds with unique tokens and proxy names: (‘deployed FRP, to establish persistent access while bypassing firewalls…authentication token frpforzhangwei’)
- [T1003 ] OS Credential Dumping – Extracting credentials from memory and system stores using Mimikatz and related tools: (‘The attackers used Mimikatz to dump passwords from memory’)
- [T1003.001 ] LSASS Memory – Targeting LSASS and LSA APIs to capture logon credentials using LsaRecorder and LSASS dumps: (‘The LsaRecorder tool captures login passwords by hooking the LsaApLogonUserEx2 callback function.’ )
- [T1046 ] Network Service Discovery – Scanning and mapping networks with a custom scanner (ScanPortPlus) that enumerates IPs, ports and vulnerabilities: (‘ScanPortPlus … command-line options of ScanPortPlus, which include IP address, port and vulnerability scanning.’)
- [T1041 ] Exfiltration Over C2 Channel / Application Layer – Exfiltrating stolen files by Base64‑encoding archives with certutil and printing output via web shells to avoid direct file transfer: (‘Executing the certutil -encode command to Base64-encode the .rar archives…Executing the type command to print the Base64 content to their screen through the web shell.’)
- [T1082 ] System Information Discovery – Host‑level reconnaissance using SuperDump and batch scripts (hp.bat/hpp.bat) to collect user, process, registry and network information: (‘deployed a custom .NET tool that they named SuperDump…later replaced by batch script files called hpp.bat and hp.bat, which also collect host information.’)
- [T1068 ] Exploitation for Privilege Escalation – Leveraging local exploits and tools for escalation such as PwnKit (CVE-2021-4034) and PrintSpoofer/PrintProgram: (‘Attackers deployed PwnKit, a self-contained exploit (CVE-2021-4034) to achieve local privilege escalation on Linux systems.’ and ‘used the open-source PrintSpoofer tool to elevate privileges.’)
Indicators of Compromise
- [SHA256 ] File hashes for tools and payloads – examples include shellcode loader 524734501be19e9ed1bfab304b0622a2263a4f9e3db0971f3fae93f7e7369c20, web shell d8378cf105146217e6ded438187c4ea0edcadb6cf27f5eeddda3fd80cce76d72, and numerous additional hashes for FRP, ScanPortPlus, Xnote, SuperDump, Mimikatz and others.
- [IP addresses ] C2 and infrastructure – examples include 13.250.108[.]65, 43.255.189[.]67, and five other observed IPs used in CL-UNK-1068 activity.
- [Filenames ] Stolen and deployed filenames observed during intrusions – examples include web.config (stolen from c:inetpubwwwroot) and python20.dll (malicious side‑loaded DLL), plus archived files named web.rar, web1.rar, web2.rar.
- [Credentials/Config strings ] Unique configuration identifiers found in tooling – examples include FRP authentication token frpforzhangwei and FRP password f*ckroot123 used across multiple samples.
Read more: https://unit42.paloaltonetworks.com/cl-unk-1068-targets-critical-sectors/