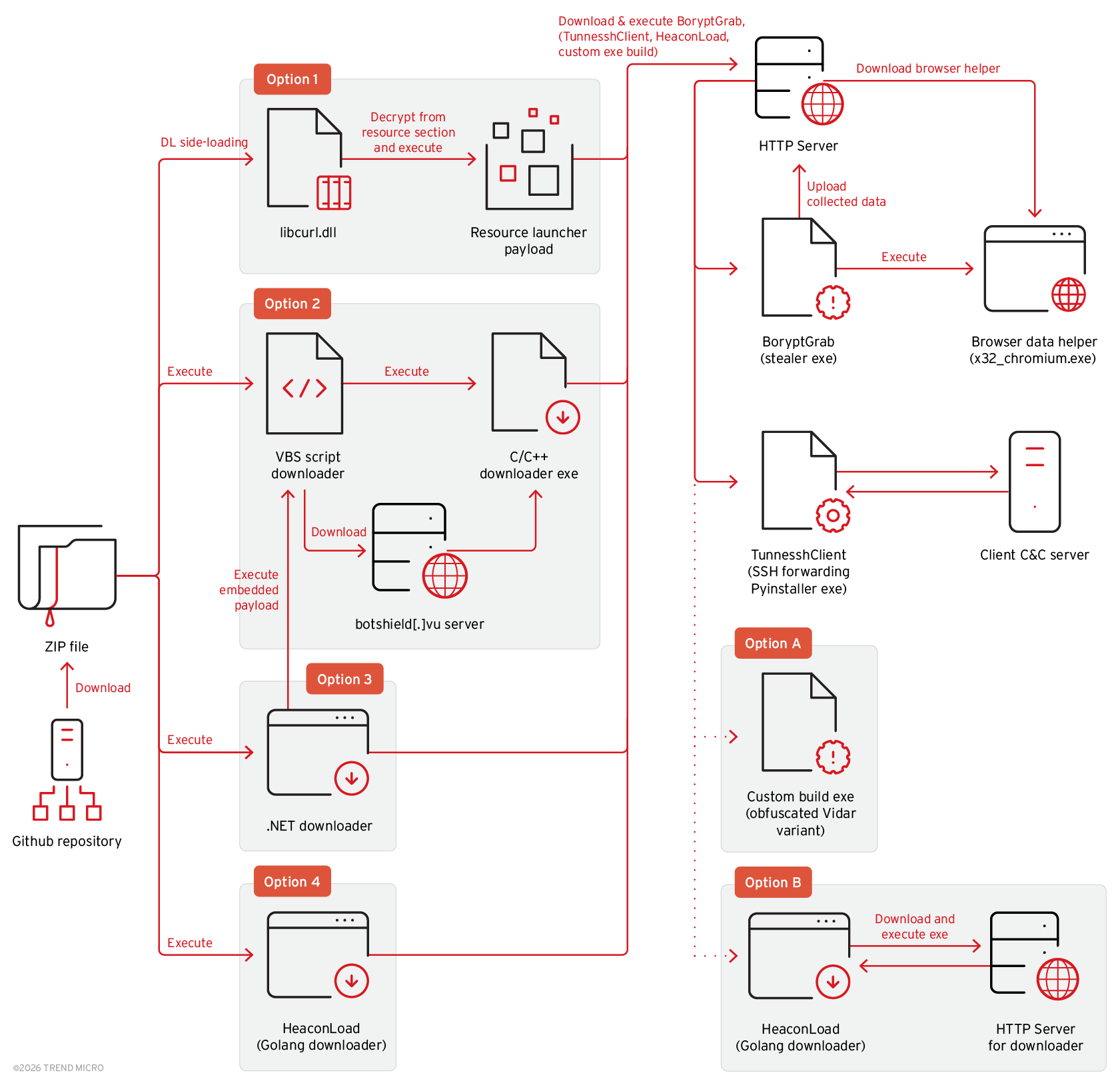
BoryptGrab is a newly identified data‑stealing stealer delivered via SEO‑optimized fake GitHub repositories and deceptive download pages that harvests browser data, cryptocurrency wallet information, system data, screenshots, Telegram/Discord tokens, and other files. The campaign uses multiple staged download routes (DLL side‑loading, VBS and .NET downloaders, Golang loaders) and delivers additional payloads including TunnesshClient (a PyInstaller reverse SSH backdoor) and Vidar variants. #BoryptGrab #TunnesshClient
Keypoints
- BoryptGrab is a C/C++ stealer that collects browser credentials (including Chrome App Bound Encryption bypass), cryptocurrency wallet data, system information, screenshots, Telegram files, and Discord tokens.
- The campaign distributes malware through hundreds of public GitHub repositories and fake GitHub download pages using SEO keywords and staged redirects that ultimately generate malicious ZIP archives.
- Multiple delivery chains are used: DLL side‑loading loaders, VBS and Base64‑embedded downloaders, .NET wrappers, a Golang downloader (HeaconLoad), and direct ZIP payloads; many artifacts contain Russian comments/logging.
- TunnesshClient is a PyInstaller backdoor that retrieves SSH credentials from a C2, establishes a reverse SSH tunnel, supports SOCKS5 proxying, executes attacker commands, and can forward local SSH connections.
- Many components implement persistence (registry Run key, scheduled tasks), anti‑analysis (VM checks, process name checks), and obfuscation (XOR/AES/Base64, opaque predicates); some loaders further stage Vidar stealer variants.
- Attack infrastructure includes multiple IPs, domains, and hardcoded build names used to select payloads; variants and build tags (e.g., Shrek, CryptoByte, yaropolk) indicate an active, evolving operation.
- Indicators provided include sample hashes, malicious domains, GitHub repository names, ZIP filenames, and C2 IP addresses useful for hunting and detection.
MITRE Techniques
- [T1204.002] User Execution: Malicious File – used to trick victims into downloading ZIP archives from fake GitHub download pages (‘the infection chain is initiated when ZIP file is downloaded from a fake GitHub download page’).
- [T1574.001] Hijack Execution Flow: DLL Side‑Loading – loaders side‑load a malicious libcurl.dll which loads/decrypts launcher payloads (‘distributed ZIP file variants can contain an executable that side‑loads a libcurl.dll file’).
- [T1105] Ingress Tool Transfer – multiple components download additional payloads (BoryptGrab, TunnesshClient, Vidar variants, helper binaries) from attacker servers (‘downloads the BoryptGrab stealer’, ‘/api/client’, ‘/api/custom_exe?build={BUILD_NAME}’).
- [T1547.001] Boot or Logon Autostart Execution: Registry Run Keys/Startup Folder – HeaconLoad achieves persistence by adding a registry Run key (‘achieves persistence by adding a registry entry under the Run key’).
- [T1053.005] Scheduled Task/Job: Scheduled Task – launchers create scheduled tasks to execute downloaded TunnesshClient and other binaries (‘schedules tasks that use .xml files at %TEMP%client_task_system.xml and %TEMP%client_task_user.xml to execute the downloaded TunnesshClient’).
- [T1027] Obfuscated Files or Information – use of XOR/AES/Base64, opaque predicates, and junk code to hide strings and control flow (‘uses XOR-encrypted strings and contains opaque predicates with redundant code for obfuscation’).
- [T1555.003] Credentials from Web Browsers – BoryptGrab harvests browser passwords and uses Chrome App Bound Encryption bypass code to extract browser credentials (‘collects browser data…collects browser passwords’ and uses Chrome App Bound Encryption bypass code).
- [T1113] Screen Capture – the stealer captures screenshots of the victim system (‘then captures a screenshot and collects system information’).
- [T1005] Data from Local System – “File Grabber” functionality collects files with specified extensions from common directories (‘File Grabber ability, where it collects files with specified extensions under common directories’).
- [T1090.004] Proxy: SOCKS – TunnesshClient can act as a SOCKS5 proxy to forward attacker traffic (‘Act as SOCKS5 proxy’).
- [T1021.004] Remote Services: SSH – TunnesshClient establishes a reverse SSH tunnel and retrieves SSH credentials from the C2 (‘establishes a reverse Secure Shell (SSH) tunnel’ and ‘retrieves SSH credentials…’).
- [T1041] Exfiltration Over C2 Channel – collected data is archived and uploaded to attacker servers (‘archives and uploads its collected data to the attacker’s server’).
- [T1055] Process Injection – Vidar variants observed in the campaign can perform code injection or APC injection (‘can also perform code injection or APC injection’).
- [T1059.003] Command and Scripting Interpreter: Windows Command Shell – TunnesshClient supports executing shell commands sent by the attacker (‘Operation type 83: Execute shell command’).
Indicators of Compromise
- [File Hash ] malware/sample identifiers – fa767391b99865f8533efc1fe6dfa6175215718679fb00ca85fc13c3bd4ae4b7 (libcurl.dll), 576692df4bf1c7d8927d3a183f5219a81c3bff3dd22971691f8af6889f80c5a0 (TunnesshClient), and other hashes referenced in the report.
- [IP Address ] C2 and download hosts – 193.143.1[.]104 (TunnesshClient C2), 45.93.20[.]61 (:5466 download API), and additional campaign IPs such as 45.93.20[.]195.
- [Domain / URL ] redirect and download infrastructure – voicemod-pro-download-tool.github[.]io (fake download page), best-tinted[.]com/github-download.html (ZIP generator), botshield[.]vu (download host), and other attacker-controlled domains (kiamatka[.]com, etc.).
- [GitHub Repository ] SEO‑optimized malicious repos – https://github[.]com/Voicemod-Pro-Download-Tool, https://github[.]com/PassFab-4WinKey-Windows-Password-Reset (examples of repos used to host redirect source and fake .github pages).
- [File Names ] malicious distributables and helpers – “valorant performance boost fps booster 5.4.9.zip”, “vmware-download-github-io-4.83.4.zip” (examples of ZIP names used to lure victims; many similar filenames listed).
- [File Path ] dropped helper binaries and scheduled task files – %TEMP%x32_chromium.exe (Chromium helper), %TEMP%client_task_system.xml and %TEMP%client_task_user.xml (scheduled task definitions).