Proofpoint researchers disclosed “CursorJack”, a proof‑of‑concept showing how Cursor IDE’s cursor:// MCP deeplinks can be abused via social engineering to install malicious MCP servers or execute arbitrary commands. In tests a single user click plus acceptance of the install prompt could fetch and run staged scripts that retrieve a Metasploit/Meterpreter payload or install remote MCP servers, #Cursor #Meterpreter
Keypoints
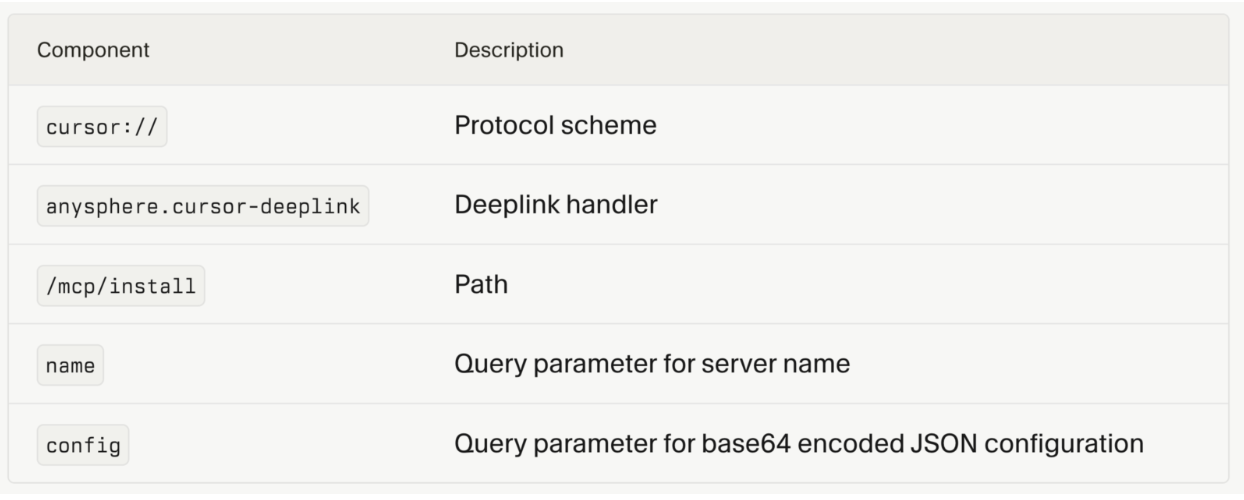
- Cursor’s cursor:// protocol handler accepts deeplinks that embed base64 MCP configurations, allowing deeplinks to add entries to ~/.cursor/mcp.json.
- A single user click plus approval of the installation dialog can result in arbitrary command execution under the user’s privileges.
- Two exploitation paths exist: the command parameter enabling immediate local code execution, and the url parameter enabling installation of a remote (malicious) MCP server.
- The CursorJack proof‑of‑concept staged a Meterpreter reverse shell by downloading run.bat and a Metasploit payload (p.exe) via curl from attacker infrastructure.
- The installation dialog shows identical warnings for legitimate and malicious deeplinks and previously reported issues could hide dangerous arguments from the preview.
- Developers’ workstations are high‑value targets because MCP servers run with user privileges and may expose SSH keys, API tokens, source code, and cloud credentials; enterprise controls (EDR, allow‑listing, OS policies) can mitigate risk depending on configuration.
- Recommended mitigations include granular permission models or containerization for MCP execution, signing/verified publishers for MCP servers, and treating deeplinks from untrusted sources like untrusted executables.
MITRE Techniques
- [T1566 ] Phishing – The attack used email/links to lure victims to a landing page that redirects to a malicious deeplink (‘A phishing email directs the victim to a malicious landing page that triggers an MCP deeplink.’)
- [T1204 ] User Execution – The exploit requires user interaction (click + acceptance) to execute the payload (‘a single click followed by user acceptance of an install prompt could result in arbitrary command execution.’)
- [T1059 ] Command and Scripting Interpreter – The attacker used batch scripts and command interpreters (curl, run.bat) to stage and execute the payload (‘run.bat is a staging script that uses curl to download and execute the Metasploit payload (p.exe)’)
- [T1105 ] Ingress Tool Transfer – Tools and payloads were retrieved from attacker‑controlled infrastructure via network fetches (‘Cursor executes the curl command to fetch run.bat from the attacker’s server.’)
- [T1547 ] Boot or Logon Autostart Execution – The malicious install command persists and executes each time the IDE is launched, providing persistence (‘the install command executing each time Cursor is launched.’)
- [T1071 ] Application Layer Protocol – The Meterpreter reverse shell established a network connection to the attacker’s listener as the C2 channel (‘Reverse shell connects and Meterpreter establishes connection to attacker’s listener.’)
Indicators of Compromise
- [URL / deeplink ] Deeplink schema used to deliver MCP config – cursor://anysphere.cursor-deeplink/mcp/install?name=&config=
- [File name ] Staging and payload filenames observed – run.bat, p.exe
- [Config file ] MCP configuration and path written by Cursor – mcp.json (e.g., ~/.cursor/mcp.json)
- [Payload / tool ] Remote tools and frameworks used in POC – Metasploit, Meterpreter (p.exe)
- [Vulnerability identifiers ] Related disclosed issues referenced in report – CVE-2025-54136, CVE-2025-54133