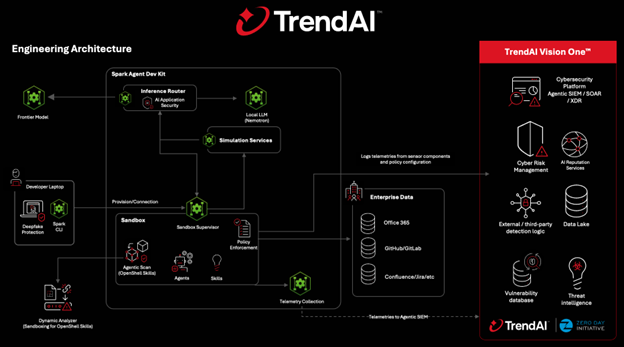
The article explains how NVIDIA OpenShell and TrendAI integrate to provide governance, runtime enforcement, and visibility for deploying autonomous agentic AI safely at enterprise scale. It outlines layered defenses—pre-execution policy distribution, Agentic Scan for skill/tool risk, dynamic behavioral analysis, inline runtime enforcement, AI-specific threat inspection, and continuous monitoring—enabling secure, auditable agent lifecycles. #NVIDIAOpenShell #TrendAI
Keypoints
- Agentic AI introduces persistent, self-evolving agents that change the security model by adding memory, tool invocation, code execution, and long-lived identities.
- NVIDIA OpenShell provides a runtime with sandboxed execution, local memory and file system isolation, tool/skill invocation boundaries, and model routing to support safer agent deployment.
- TrendAI integrates governance and enforcement into OpenShell by distributing centrally defined policies into the runtime via TrendAI Vision One™, shifting policy into enforceable controls.
- Agentic Scan continuously inventories and analyzes agent skills, MCP integrations, and tool definitions to detect deceptive or non-compliant capabilities before they run.
- TrendAI applies dynamic behavioral analysis in isolated environments to detect hidden malicious actions, unauthorized system access, and anomalous network or file activity.
- Inline runtime policy enforcement, AI-specific threat inspection (e.g., prompt injection and data leakage), continuous telemetry, and threat intelligence enable real-time risk decisions and auditability.
MITRE Techniques
- [None ] The article does not reference specific MITRE ATT&CK technique identifiers (Txxxx); it describes attack classes such as prompt injection (‘…Prompt injection…’), indirect prompt manipulation (‘…Indirect prompt manipulation…’), sensitive data leakage (‘…Sensitive data leakage…’), code execution (‘…Execute code to enable new capabilities…’), and unauthorized system access (‘…Unauthorized system access…’).
Indicators of Compromise
- [None ] The article does not provide concrete IOCs (no IP addresses, domains, file hashes, or filenames); it refers to telemetry and monitoring artifacts such as agent execution logs, tool usage records, and sandbox environment telemetry as sources for detection and forensics.