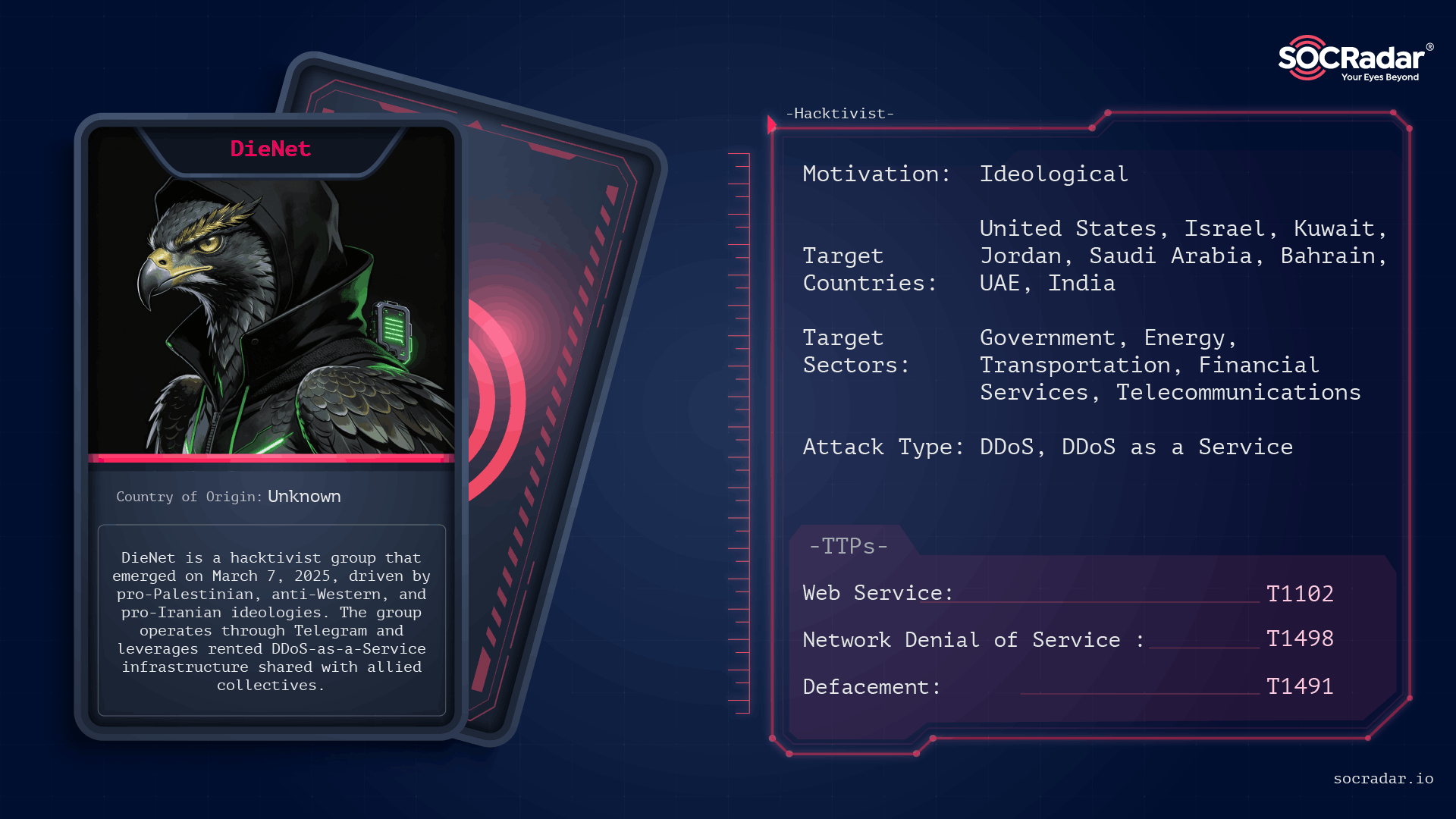
DieNet emerged in March 2025 as a fast‑growing pro‑Iranian hacktivist franchise that leverages rented DDoS‑as‑a‑Service infrastructure to claim large volumes of disruption, including 59 distinct attack claims across March 2–3, 2026, and a major share of 149 hacktivist DDoS claims against 110 organizations. The group targets governments, critical infrastructure, and high‑visibility Western firms, has made unverified claims of ransomware and OT/ICS access (Locknet, VeroPoint), and operates inside a broader “Electronic Operations Room” of aligned actors. #DieNet #Locknet
Keypoints
- DieNet announced itself on Telegram in March 2025 and rapidly scaled to become the most prolific pro‑Iranian DDoS actor during the Feb–Mar 2026 escalation, claiming 59 attacks in two days (March 2–3, 2026).
- The group relies on rented DDoS‑as‑a‑Service (DaaS) infrastructure and a franchise‑like structure—core brand managers plus a wider ring of operators—enabling high‑volume campaigns without building proprietary botnets.
- Primary targets include government portals, financial institutions, telecoms, transportation, and healthcare across the U.S., Gulf states, Israel, and other countries; notable victim claims include Amazon Pay, NASDAQ, Port of Los Angeles, and NSO Group.
- DieNet claims additional capabilities (Locknet ransomware, OT/ICS access, a TOIPOI intelligence platform) but many such claims are unverified or consist of repurposed open‑source data used for psychological effect.
- The group shares infrastructure with DaaS providers like OverFlame and DenBots Proof and acted as a high‑volume DDoS engine within the pro‑Iran “Electronic Operations Room” during the 2026 conflict.
- Defenders are advised to use layered mitigations—upstream filtering, cloud scrubbing/CDNs, WAFs, OT segmentation, phishing‑resistant MFA, and monitoring of DieNet Telegram channels for early warning.
MITRE Techniques
- [T1592 ] Gather Victim Host Information – Reconnaissance on target hosts and services to inform DDoS and targeted operations (‘Gather Victim Host Information’)
- [T1590 ] Gather Victim Network Information – Mapping network topologies and open resolvers used to enable amplification techniques (‘Gather Victim Network Information’)
- [T1583.005 ] Acquire Infrastructure: Botnet – Use or acquisition of botnet/DaaS infrastructure to generate attack traffic (‘Acquire Infrastructure: Botnet’)
- [T1584.005 ] Compromise Infrastructure: Botnet – Leveraging third‑party DDoS services or shared botnet resources (OverFlame, DenBots Proof) to execute campaigns (‘Compromise Infrastructure: Botnet’)
- [T1190 ] Exploit Public‑Facing Application – Defacements and admin panel takeovers claimed against web portals as part of symbolic targeting (‘Exploit Public‑Facing Application (defacements, admin panel takeover)’)
- [T1071.001 ] Application Layer Protocol: Web Protocols – Use of web protocols for command, control, or application‑layer flooding against dashboards and APIs (‘Application Layer Protocol: Web Protocols’)
- [T1090 ] Proxy – Use of proxies and infrastructure to hide attack origins and control DDoS resources (‘Proxy (hiding origin, controlling DDoS infrastructure)’)
- [T1498 ] Network Denial of Service – Primary confirmed impact type, executed via volumetric and application‑layer floods (‘DieNet’s primary confirmed TTP is Network Denial of Service (T1498).’)
- [T1498.001 ] Network DoS: Direct Network Flood – Direct SYN/RST/TCP floods used to exhaust server resources and connections (‘Network DoS: Direct Network Flood’)
- [T1498.002 ] Network DoS: Reflection Amplification – Use of DNS and NTP amplification to magnify attack traffic against victims (‘Network DoS: Reflection Amplification’)
- [T1499 ] Endpoint Denial of Service – Targeted disruption of specific endpoints and services to render them unresponsive (‘Endpoint Denial of Service’)
- [T1491.001 ] Defacement: External Defacement – Public defacements and staged leak claims used for propaganda and spectacle (‘Defacement: External Defacement’)
- [T1565 ] Data Manipulation – Staged leak and data manipulation claims (e.g., inflated NIC exfiltration) used for psychological impact (‘Data Manipulation (staged “leaks”)’)
Indicators of Compromise
- [Telegram channels ] Coordination and public claims – DieNet Main, DieNet Media, and 2 more channels
- [Malware name ] Claimed extortion tools (unverified) – Locknet (claimed against UTLX)
- [Victim organizations ] High‑profile targets cited in claims – Amazon Pay, NASDAQ, and many government portals across Kuwait, Bahrain, Israel, UAE
- [OT/ICS systems ] Alleged industrial access screenshots – VeroPoint systems, PLC interfaces
- [DaaS/Infrastructure providers ] Shared DDoS infrastructure used in campaigns – OverFlame, DenBots Proof
Read more: https://socradar.io/blog/dark-web-profile-dienet/