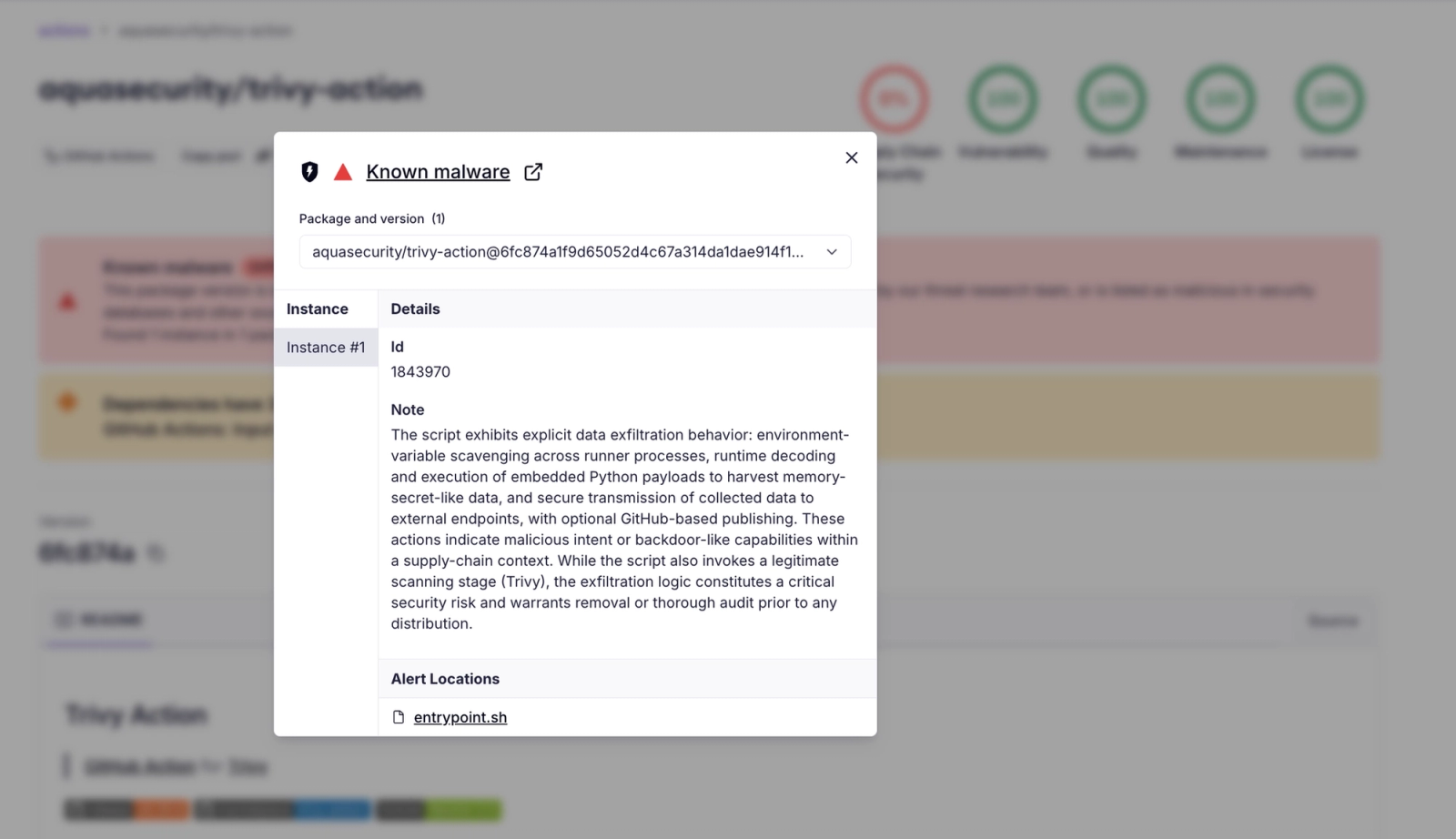
A supply chain attack compromised the aquasecurity/trivy-action GitHub Action by force-updating 75 version tags to point to malicious commits that replaced the action entrypoint with an infostealer, putting over 10,000 workflows at risk. The payload collects secrets (including SSH keys, cloud credentials, and runner memory dumps), encrypts them, and exfiltrates to a typosquatted domain or to victim-created GitHub repositories; attribution points to TeamPCP. #TeamPCP #trivy-action
Keypoints
- The aquasecurity/trivy-action GitHub Action was compromised when an attacker force-pushed 75 version tags to point to new commits that swapped in a malicious entrypoint, affecting widely used version-tag references.
- The malicious entrypoint executes an infostealer before the legitimate Trivy scan, harvesting runner environment variables, SSH keys, cloud credentials, Kubernetes tokens, and optionally dumping GitHub Actions Runner.Worker memory to extract secrets.
- Exfiltration occurs primarily via HTTPS POST to a typosquatted domain (scan[.]aquasecurtiy[.]org) with a resilient fallback that creates a public repo (tpcp-docs) in the victim’s GitHub account and uploads stolen data as a release asset.
- Socket detected the campaign in real time at ~19:15 UTC on March 19, 2026, generating numerous threat feed entries and classifying the activity as Backdoor/Infostealer/Reconnaissance; Trivy maintainers confirmed attacker access was via a compromised credential with write rights.
- The attacker spoofed commit metadata for each rewritten tag to mimic original commits, making the malicious commits appear legitimate in git logs; telltale signs include missing GPG web-flow signatures and impossible parent/date relationships.
- Immediate remediation: stop using trivy-action by version tag, pin to commit SHA 57a97c7e7821a5776cebc9bb87c984fa69cba8f1 or use tag 0.35.0 only; treat any pipeline that ran a poisoned tag as fully compromised and rotate all exposed secrets.
MITRE Techniques
Indicators of Compromise
- [Domain ] exfiltration endpoint (typosquat of Aqua Security) – scan[.]aquasecurtiy[.]org
- [File Hash ] malicious entrypoint script SHA256 – 18a24f83e807479438dcab7a1804c51a00dafc1d526698a66e0640d1e5dd671a (entrypoint.sh)
- [GitHub Action Tags ] compromised aquasecurity/trivy-action version tags used to distribute payload – examples: @0.33.0, @0.34.2, and 73 other poisoned tags
- [Repository/Action ] compromised action repository – aquasecurity/trivy-action (official Trivy GitHub Action) referenced by workflows
- [GitHub Artifact/Repo Name ] fallback exfiltration artifact/repository name – tpcp-docs (public repos/releases created in victim accounts)
- [Commit SHA ] safe pin / remediation target – 57a97c7e7821a5776cebc9bb87c984fa69cba8f1 (pin to this commit) and tag 0.35.0 (only unaffected tag)
Read more: https://socket.dev/blog/trivy-under-attack-again-github-actions-compromise