Cryptographic analysis confirms a legitimate RSA private key matching the wildcard TLS certificate for *.myclaw[.]360[.]cn was exposed in distributed installer material, enabling potential namespace-wide impersonation and interception if used in production. The certificate (issued by WoTrus RSA DV SSL CA 2) appears to have been rotated on 16 March 2026 after discovery, and the namespace is attributed to Qihoo 360. #SecurityClaw #Qihoo360
Keypoints
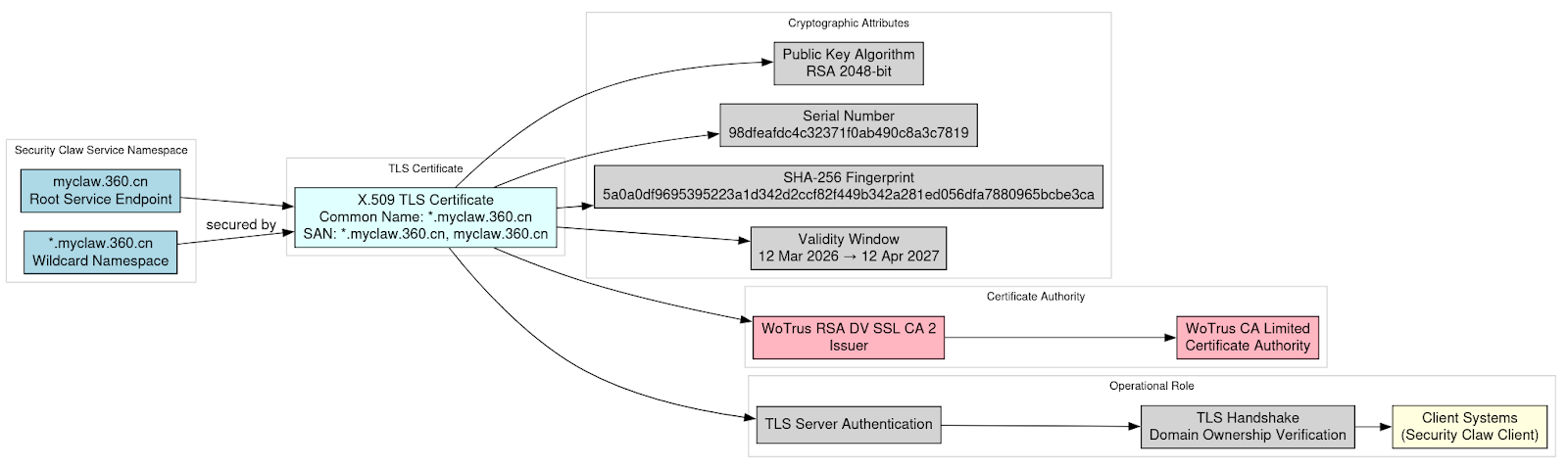
- Cryptographic validation shows the provided private key matches the public key in the X.509 wildcard certificate for *.myclaw[.]360[.]cn, proving the leak was of an operational key pair.
- The certificate is a wildcard TLS server certificate (CN and SAN include *.myclaw[.]360[.]cn and myclaw[.]360[.]cn) issued by WoTrus RSA DV SSL CA 2 with validity 2026-03-12 to 2027-04-12.
- CT-log analysis indicates the certificate was replaced with a new RSA key pair on 16 March 2026, consistent with emergency key rotation following discovery of the exposure.
- Passive DNS and registration data tie the myclaw.360.cn namespace to Beijing Qihoo Technology Co., Ltd. (360[.]cn), supporting attribution of the infrastructure to Qihoo 360.
- Primary risks include server impersonation, man-in-the-middle decryption, credential/token theft, malicious update delivery, and manipulation of AI inference responses for the Security Claw platform.
- Root cause likely stems from improper build/package controls (CI/CD pipeline included certificate and private key in the installer), reflecting inadequate secrets management during release packaging.
- Impact depends on whether the leaked key was deployed in production and whether any adversary accessed it prior to rotation; further CT logs and passive telemetry are recommended to clarify exposure scope.
MITRE Techniques
- No MITRE ATT&CK techniques were explicitly mentioned in the article.
Indicators of Compromise
- [Domain ] Platform namespace and service endpoints – myclaw[.]360[.]cn, *.myclaw[.]360[.]cn
- [URL / Endpoint ] reported backend service endpoint (non-standard port) – https://myclaw[.]360[.]cn:19798
- [Certificate Serial Number ] unique certificate identifier – 98dfeafdc4c32371f0ab490c8a3c7819
- [Certificate SHA-256 Fingerprint ] certificate fingerprint for identification – 5a0a0df9695395223a1d342d2ccf82f449b342a281ed056dfa7880965bcbe3ca
- [Issuer / CA ] issuing authority associated with the certificate – WoTrus RSA DV SSL CA 2 (WoTrus CA Limited)
- [Artifact / PEM content ] exposed artifacts in distributed installer – full X.509 certificate (PEM) provided in appendix and corresponding private key present in the supplied dataset