Pawn Storm (APT28) deployed a modular malware suite called PRISMEX to target the Ukrainian defense supply chain and allied logistics, combining steganography, COM hijacking, and abuse of legitimate cloud services for resilient fileless execution and C2. The campaign weaponized newly disclosed vulnerabilities (CVE-2026-21509 and CVE-2026-21513), used spear-phishing lures tied to hydrometeorological and military topics, and leveraged Filen.io subdomains for command-and-control. #PawnStorm #PRISMEX
Keypoints
- TrendAI Research attributes a coordinated Pawn Storm campaign (since Sept 2025, escalated Jan 2026) targeting Ukraine’s defense supply chain and NATO logistics using a malware family called PRISMEX.
- PRISMEX is modular: PrismexSheet (Excel dropper with VBA steganography), PrismexDrop (native dropper with COM hijacking persistence), PrismexLoader (proxy DLL extracting payloads from PNG via “Bit Plane Round Robin”), and PrismexStager (Covenant Grunt abusing Filen.io for C2).
- The actor exploited CVE-2026-21509 (Office OLE Shell.Explorer.1 allowlist bypass) to retrieve malicious .lnk files from WebDAV and likely exploited CVE-2026-21513 (MSHTML LNK/IE frame bypass) as a zero-day; domain registrations and a VirusTotal sample indicate infrastructure pre-positioning and zero-day use.
- The campaign employs advanced evasion: fileless CLR bootstrapping, in-memory .NET assembly loading inside explorer.exe, custom steganography scattering payload bits across images, and trusted cloud-service C2 to blend traffic.
- Observed actions include both espionage (data collection, lateral movement via Covenant) and destructive potential (wiper commands observed in prior activity), raising risk of sabotage against logistics, weather services, and humanitarian corridors.
- Immediate mitigations: patch CVE-2026-21509/CVE-2026-21513, restrict non-business cloud storage, disable Shell.Explorer.1 if needed, enforce macro restrictions, audit user-registered CLSIDs and unusual CLR loads, and block/monitor Filen.io-related domains.
MITRE Techniques
- [T1566.001 ] Spearphishing Attachment – Delivered malicious RTF attachments to targets: (‘Spear-phishing emails are sent to targeted individuals with subject lines related to “Hydro-meteorological Warnings,” “Invitation to Military Training Program,” or “Weapon Smuggling Alerts.”‘)
- [T1059.001 ] PowerShell – Listed as an execution technique in mapping (reported usage pattern): (‘T1059.001 – PowerShell’)
- [T1059.005 ] Visual Basic – VBA macros in malicious Excel droppers used to extract and deploy payloads: (‘PrismexSheet: A malicious Excel dropper with VBA macros that extracts payloads embedded within the file itself using steganography techniques.’)
- [T1204.001 ] User Execution: Malicious Link – Malicious .lnk shortcuts retrieved and executed via WebDAV after RTF OLE instantiation: (‘this vulnerability forces the host application to automatically initiate an outbound connection… to retrieve and execute a remote .lnk (shortcut) file’)
- [T1546.015 ] Component Object Model Hijackin – Persistence via user-registered COM InProcServer32 pointing to dropped DLLs: (‘PrismexSheet establishes persistence by hijacking a COM object… By rewriting the InProcServer32 value to point to the dropped malicious DLL (adwapi64.dll)’)
- [T1053.005 ] Scheduled Task – Scheduled task used as a trigger to restart explorer.exe and load hijacked COM: (‘A hidden scheduled task (“OneDriveHealth”) runs once, one minute after infection, executing a command sequence that terminates and restarts explorer.exe.’)
- [T1574.002 ] DLL Side-Loading – Proxy DLL technique forwards legitimate exports while executing malicious code to avoid crashes: (‘This component masquerades as the legitimate Windows DLL like EhStorShell.dll. It functions as a Proxy DLL, forwarding legitimate function exports to the real system DLL’)
- [T1027.003 ] Steganography – Payloads embedded and scattered across images using a “Bit Plane Round Robin” extraction algorithm: (‘The loader cycles through the entire image buffer extracting the LSB of every byte before moving to the next bit plane.’)
- [T1562.001 ] Disable or Modify Tools – Bypass of platform defenses and Protected View to circumvent security features: (‘effectively bypassing Protected View and standard OLE security prompts.’)
- [T1055 ] Process Injection – In-memory CLR hosting and execution of .NET assemblies inside explorer.exe to avoid filesystem artifacts: (‘the malicious code executes within explorer.exe (a highly trusted system process), and the payload never touches the filesystem’)
- [T1553.005 ] Mark-of-the-Web Bypass – Exploits used to bypass Mark-of-the-Web and IE Enhanced Security: (‘likely exploits CVE-2026-21513 … to bypass Mark of the Web and IE Enhanced Security Configuration.’)
- [T1114.001 ] Local Email Collection – Collection technique listed in mapping relating to email-based targeting and follow-on collection: (‘T1114.001 – Local Email Collection’)
- [T1071.001 ] Web Protocols – Use of WebDAV and web protocols to retrieve .lnk payloads from attacker-controlled servers: (‘the attacker forces the host application to automatically initiate an outbound connection… to retrieve and execute a remote .lnk (shortcut) file’)
- [T1102 ] Web Service – Abuse of Filen.io cloud service for command-and-control and data transfer: (‘The malware abuses the legitimate end-to-end encrypted cloud storage service Filen.io for C&C communications.’)
- [T1048.003 ] Exfiltration Over Alternative Protocol – Use of ingest/egest Filen.io endpoints to exfiltrate data and retrieve payloads: (‘Ingress domains: ingest.filen.io (for data exfiltration)’)
Indicators of Compromise
- [Domain ] C2 and exploit infrastructure – wellnesscaremed[.]com (shared C2 between CVE-2026-21509 and CVE-2026-21513 analyses), gateway.filen.io (Filen.io gateway used for C2).
- [File hash ] Exploit/sample identification – SHA256 aefd15e3c395edd16ede7685c6e97ca0350a702ee7c8585274b457166e86b1fa (VirusTotal submission for CVE-2026-21513 exploit sample).
- [File name ] Dropped/persistent artifacts – adwapi64.dll (dropped malicious DLL registered via COM hijack), EhStoreShell.dll (malicious proxy DLL target path), SplashScreen.png / background.png (steganography carriers used to hide payloads).
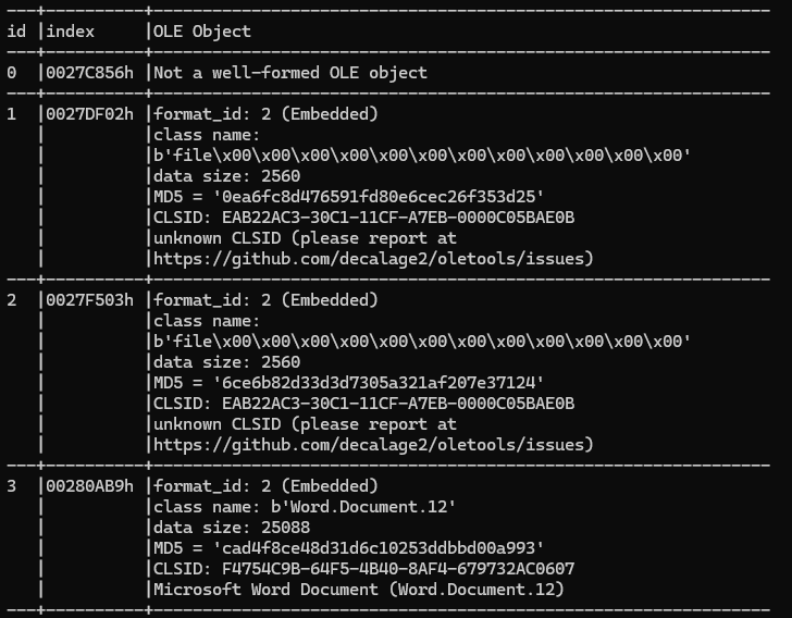
- [CLSID / GUID ] COM and OLE targets – Shell.Explorer.1 CLSID EAB22AC3-30C1-11CF-A7EB-0000C05BAE0B (exploited via CVE-2026-21509), user-registered hijack CLSID {68DDBB56-9D1D-4FD9-89C5-C0DA2A625392} (InProcServer32 hijack target).
- [Scheduled Task ] Persistence trigger – OneDriveHealth (hidden scheduled task that restarts explorer.exe to load hijacked COM and execute payloads).
- [Cloud service subdomains ] Filen.io C2/exfiltration endpoints – gateway.filen.io, ingest.filen.io, egest.filen.io (used for C2, payload download, and data exfiltration).
Read more: https://www.trendmicro.com/en_us/research/26/c/pawn-storm-targets-govt-infra.html