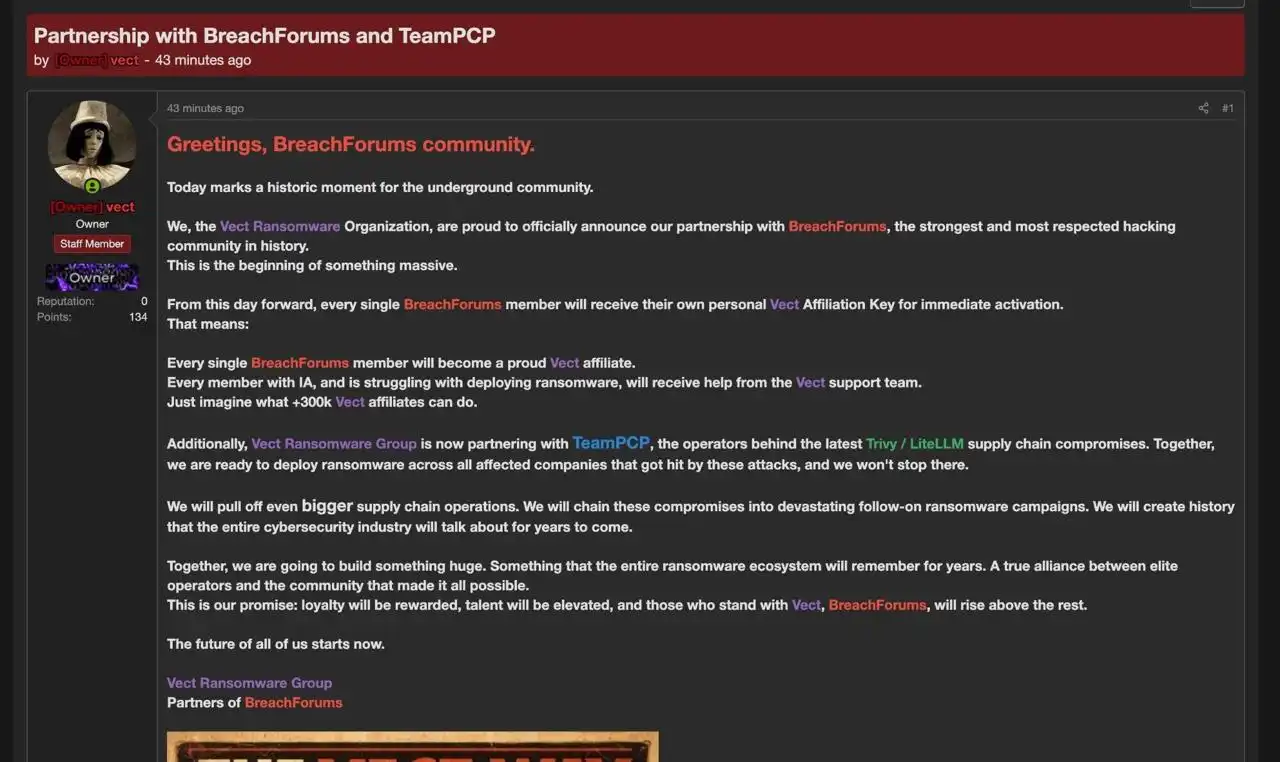
Between late February and March 2026, TeamPCP executed multi-wave supply chain compromises that poisoned widely trusted open-source security and developer tooling — including Aqua Security Trivy, Checkmarx KICS, BerriAI LiteLLM and the Telnyx Python SDK — to plant infostealer payloads into GitHub Actions and PyPI packages. The operation exfiltrated cloud access tokens, SSH keys and Kubernetes secrets at scale (reported >300 GB and ~500,000 credentials), deployed the CanisterWorm decentralized ICP canister C2 and added targeted wiper components for destructive operations. #TeamPCP #CanisterWorm
Keypoints
- TeamPCP (aka PCPcat, ShellForce, DeadCatx3) conducted coordinated supply chain attacks from late February through March 2026 targeting CI/CD and package registries.
- Primary victims included Aqua Security Trivy, Checkmarx KICS, BerriAI LiteLLM and the official Telnyx Python SDK, with malicious code inserted into GitHub Actions workflows and PyPI packages.
- Malicious payloads (TeamPCP cloud stealer / CanisterWorm) harvested cloud access tokens, SSH keys, Kubernetes secrets and high-density LLM API keys, then exfiltrated data to typosquatted domains and ICP canisters.
- Attackers used credential harvesting, npm/PyPI publishing token abuse, SDK-squatting, and pre/post-install script injection to propagate across developer and CI/CD environments.
- CanisterWorm introduced a decentralized ICP-based C2 and included self-replication and wiper components capable of deploying privileged DaemonSets and bricking clusters.
- Reported impact: over 300 GB of exfiltrated data, approximately 500,000 credentials, infection of dozens of additional packages (47 npm packages and 48 additional packages), and public leaks naming at least 16 organizations.
- Defensive recommendations emphasize SBOM visibility, pinning package versions, hardening CI/CD policies, rotating compromised tokens and leveraging Cortex/Unit 42 services for assessment and incident response.
MITRE Techniques
- [T1059 ] Command and Scripting Interpreter – Used to execute multi-stage and embedded scripts (bash and Python loaders) that run before legitimate tooling; quoted content: (‘import base64; exec(base64.b64decode(‘)
- [T1074 ] Data Staged – Malware created and wrote staged artifacts and encrypted payloads for exfiltration and persistence; quoted content: (‘action_file_name in (“session.key”, “payload.enc”, “session.key.enc”, “tpcp.tar.gz”, “sysmon.service”, “pglog”, “.pg_state”)’)
- [T1021.007 ] Remote Services: Kubernetes API – Actors enumerated and accessed Kubernetes APIs and metadata services to harvest secrets and move laterally; quoted content: (‘/api/v1/namespaces/.+/secrets|/api/v1/secrets|/latest/meta-data/iam/security-credentials/|/latest/api/token’)
Indicators of Compromise
- [IP Addresses ] C2 and infrastructure – 23.142.184[.]129, 45.148.10[.]212, and 6 other IPs
- [Domains ] Exfiltration and typosquat C2 domains – scan.aquasecurtiy[.]org, models.litellm[.]cloud, checkmarx[.]zone, and 1 more domain
- [Tunneling URLs ] Cloudflare tunnels used for staging/redirects – championships-peoples-point-cassette.trycloudflare[.]com, create-sensitivity-grad-sequence.trycloudflare[.]com, and other trycloudflare URLs
- [Filenames ] Malicious file and script names observed in payloads – kamikaze[.]sh, kube[.]py, and additional filenames like prop[.]py, proxy_server[.]py, tpcp.tar[.]gz
- [Certificate SHA256s ] Self-signed certificates used by malware – 30015DD1E2CF4DBD49FFF9DDEF2AD4622DA2E60E5C0B6228595325532E948F14, 41C4F2F37C0B257D1E20FE167F2098DA9D2E0A939B09ED3F63BC4FE010F8365C, and 1 more hash
- [Malicious file SHA256s ] Hashes for payloads and binaries – 0880819ef821cff918960a39c1c1aada55a5593c61c608ea9215da858a86e349, 0c0d206d5e68c0cf64d57ffa8bc5b1dad54f2dda52f24e96e02e237498cb9c3a, and dozens of additional hashes
Read more: https://unit42.paloaltonetworks.com/teampcp-supply-chain-attacks/