Proofpoint observed China-aligned TA416 resume systematic targeting of European government and diplomatic entities from mid-2025 through early 2026 and expand operations into Middle Eastern diplomatic and government organizations following the outbreak of conflict in Iran. The actor employed waves of web-bug reconnaissance and evolving malware delivery chains—fake Cloudflare Turnstile pages, Microsoft Entra OAuth redirects, ZIP smuggling with LNK files, and MSBuild/CSPROJ downloaders—ultimately loading a heavily obfuscated custom PlugX backdoor via DLL sideloading. #TA416 #PlugX
Keypoints
- TA416 resumed focused targeting of European government and diplomatic mailboxes from mid-2025, often targeting NATO and EU delegations immediately after the 25th EU–China summit.
- In March 2026 TA416 expanded targeting to Middle Eastern diplomatic and government entities following the outbreak of war in Iran, using region-specific lures such as energy infrastructure reports.
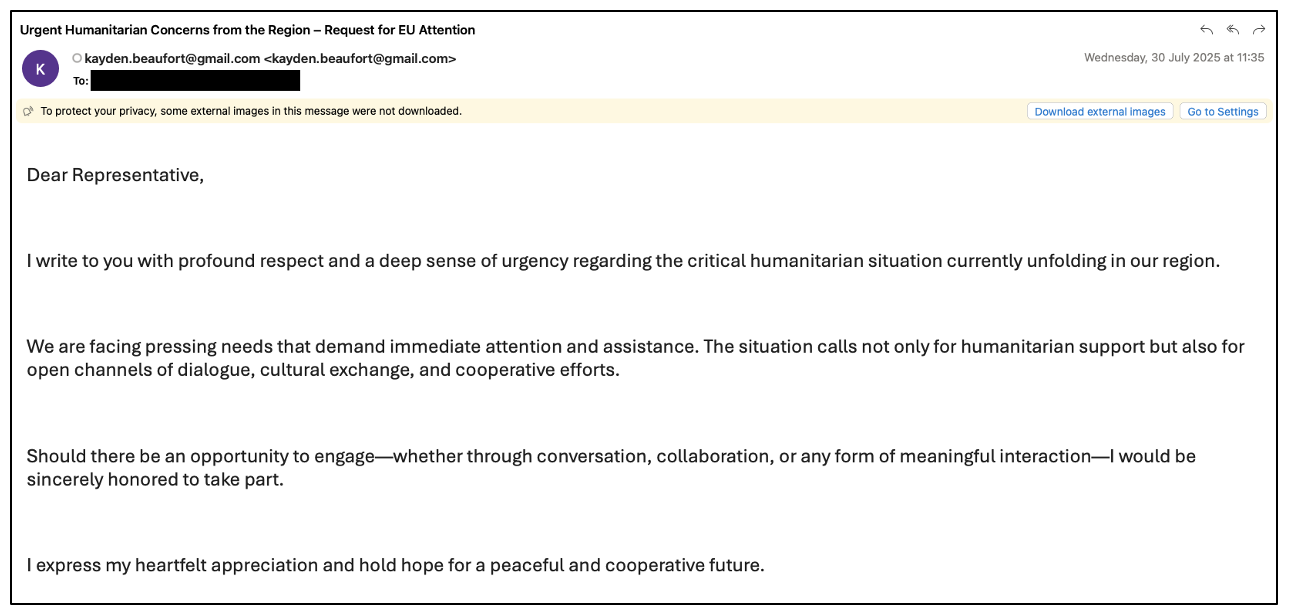
- The group ran large web-bug reconnaissance campaigns using freemail sender accounts and unique tracking URLs to assess delivery and engagement before follow-on malware delivery.
- Malware delivery used attacker-controlled freemail and compromised government/diplomatic accounts pointing to payloads hosted on Azure Blob Storage, Google Drive, compromised SharePoint, and actor domains.
- Initial access and delivery methods evolved frequently—fake Cloudflare Turnstile pages, Microsoft Entra OAuth silent redirects, ZIP smuggling with LNK-based PowerShell, and MSBuild + CSPROJ downloaders—while keeping DLL sideloading triads to load PlugX.
- PlugX variants showed increased obfuscation and hardened configuration encryption (RC4 outer layer + per-field rolling XOR), custom C2 protocol over HTTP with RC4, API hashing, and persistence via Run registry keys.
MITRE Techniques
- [T1566.002 ] Spearphishing Link – TA416 used web-bug and link-based phishing to perform reconnaissance and deliver payloads (‘web bug (or tracking pixel) … triggers an HTTP request to a remote server when opened, revealing the recipient’s IP address, user agent, and time of access’).
- [T1566.001 ] Spearphishing Attachment – ZIP smuggling with embedded LNK files that execute PowerShell and carve/extract payloads from within archives (‘The ZIP files contain a single Microsoft shortcut (LNK) file that runs an embedded PowerShell command to search for the parent ZIP, then carve an MSI or TAR file from the ZIP’).
- [T1078 ] Valid Accounts – Use of compromised government and diplomatic mailboxes to send phishing and delivery emails (‘using both attacker-controlled freemail accounts and compromised government and diplomatic mailboxes to send links to malicious archives’).
- [T1218 ] Signed Binary Proxy Execution – Abuse of legitimate signed Microsoft MSBuild executable to run malicious C# project files that download and launch payload components (‘the downloaded archives contained a legitimate Microsoft MSBuild executable renamed as a lure filename, alongside a malicious C# project (CSPROJ) file’).
- [T1574.001 ] DLL Side-Loading – Delivery of DLL sideloading triads (signed executable + malicious DLL + encrypted payload) to load the custom PlugX backdoor (‘deliver a signed executable, malicious DLL, and encrypted payload triad that ultimately loaded PlugX into memory’).
- [T1059.001 ] PowerShell – Embedded PowerShell in LNK files used to extract and execute carved MSI/TAR stages from ZIP archives (‘runs an embedded PowerShell command to search for the parent ZIP, then carve an MSI or TAR file from the ZIP’).
- [T1027 ] Obfuscated Files or Information – Multiple obfuscation and anti-analysis techniques in loaders and payloads, including API hashing, junk code, and control-flow flattening (‘the loader and payload code and data are obfuscated using techniques such as API hashing, junk code, and control-flow flattening’).
- [T1071.001 ] Application Layer Protocol: Web Protocols – PlugX C2 communicated over HTTP using an RC4-encrypted binary protocol (‘The client initiates communication to the C&C server by sending an HTTP GET request. The server responds with application/octet-stream data that serves as the RC4 encryption key’).
- [T1547.001 ] Registry Run Keys/Startup Folder – Persistence via Run registry key to execute sideloading binary on startup (‘the DLL sideloading triad is copied to the directory C:UsersPublicCanon and a Run registry key Canon is created to run CNMNSST.exe upon startup’).
Indicators of Compromise
- [Domain ] C2, web-bug, and delivery domains observed in TA416 campaigns – ombut[.]com, speedifynews[.]com, and many others (dozens of re-registered former legitimate domains used July 2025–Mar 2026).
- [URL ] Fake Cloudflare Turnstile challenge and OAuth redirect URLs used to gate or redirect to malicious archives – hxxps://mydownload.z29.web.core.windows[.]net/nv2199_update_on_situation_of_cambodia-thailand_border.html, hxxps://login.microsoftonline[.]com/common/oauth2/v2.0/authorize?client_id=607bb911-0f5a-4186-9d48-ecff8e094280 (silent redirect to payload).
- [Hostname ] Microsoft Azure Blob Storage hostnames used to host delivery pages and archives – mydownload.z29.web.core.windows[.]net, gooledives.z48.web.core.windows[.]net (actor-hosted delivery landing pages and fake Turnstile pages).
- [Email Address ] TA416-controlled or abused sender addresses used for phishing – emmeline.voss@gmail[.]com, office2000005@gmail[.]com (freemail and compromised government/diplomatic senders used in campaigns).
- [SHA256 ] File hashes for malicious components and lure artifacts – 4ed76fa68ef9e1a7705a849d47b3d9dcdf969e332bd5bcb68138579c288a16d3 (cnmpaui.exe), b6d866054dedf7a882dd1fa405a066de1278e35acf639b3a0e850a637d27c4bc (CNCLID.dll), and many more hashes listed in indicators.
- [File Name ] Lure and malware filenames observed in archives and deployments – Meeting invitation.pdf (decoy), CNCLID.dll (malicious loader), and signed executables such as cnmpaui.exe used for DLL sideloading.
- [GUID ] Microsoft Entra third-party application client IDs used to trigger silent OAuth redirects – 607bb911-0f5a-4186-9d48-ecff8e094280, 7d980c52-31e5-4554-9e20-b89c4617102f (client IDs embedded in authorization URLs observed Dec 2025–Mar 2026).