A refined, highly automated campaign by likely former Black Basta affiliates combines mass email bombing with Microsoft Teams help-desk impersonation to gain remote access to senior leaders within minutes, often using RMM tools like Supremo and Quick Assist. Defenders are advised to implement out-of-band verification for remote-access requests, tighten RMM allow-listing, and run targeted simulations for executives. #BlackBasta #Supremo
Keypoints
- Former Black Basta affiliates are likely running a unified, evolving campaign that uses automated email bombing followed by Teams-based help-desk impersonation to gain rapid initial access.
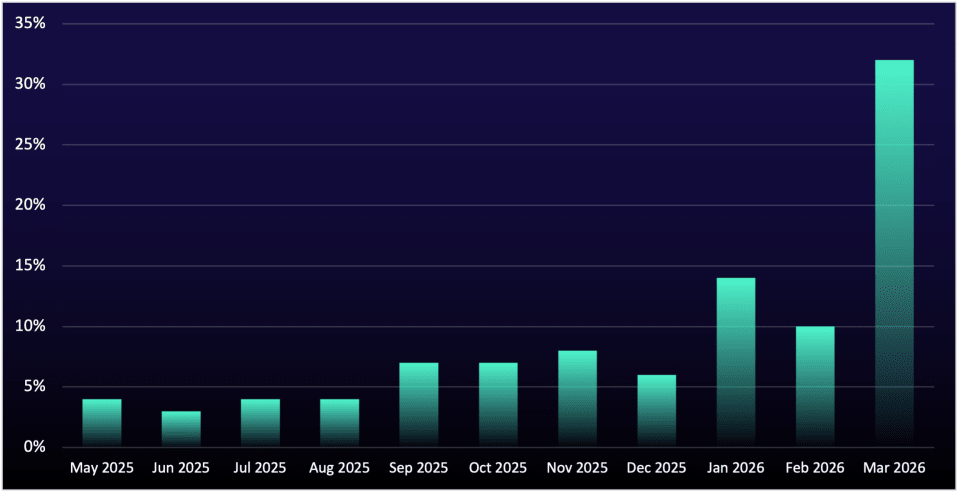
- 77% of observed incidents from March 1–April 1, 2026 targeted senior-level employees, up from 59% earlier in 2026, indicating focused targeting on high-privilege users.
- Manufacturing and Professional, Scientific, and Technical Services (PSTS) each accounted for 26% of incidents, mirroring Black Basta’s historical sector preferences.
- Attackers compress the multi-step social engineering timeline into minutes, with some intrusions moving from chat engagement to script execution in as little as 12 minutes.
- Supremo Remote Desktop and Quick Assist are primary RMM tools abused to convert social engineering into hands-on access and script execution (e.g., MailAccountWizard.jar) for pre-ransomware staging.
- Defensive recommendations include multi-channel out-of-band verification for help-desk requests, strict RMM application allow-listing, and targeted executive-level simulation training.
MITRE Techniques
- [T1566 ] Phishing – Attackers used mass email bombing and Microsoft Teams impersonation to initiate contact and create urgency (‘…email bombing…Microsoft Teams-based help desk impersonation…’).
- [T1021 ] Remote Services – Threat actors abused remote-assistance tools to gain interactive access to hosts, using both Supremo and native Quick Assist (‘…Supremo Remote Desktop…Quick Assist…’).
- [T1059 ] Command and Scripting Interpreter – Once connected via RMM, attackers executed malicious scripts named to resemble legitimate utilities (e.g., ‘MailAccountWizard.jar’) to conduct pre-ransomware staging (‘…execute malicious scripts often named to resemble common email tools, such as MailAccountWizard.jar.’).
- [T1078 ] Valid Accounts – Operators leveraged disposable onmicrosoft[.]com tenant accounts and impersonation identities to appear as legitimate help-desk personnel (‘…Disposable onmicrosoft[.]com tenant accounts, easily created and rotated to avoid blocklisting’).
Indicators of Compromise
- [Email Address ] help-desk impersonation and phishing outreach – helpdesk[at]dpf.edu[.]lk, networksupport[at]techguard359.onmicrosoft[.]com, and other onmicrosoft tenant addresses.
- [IP Address ] threat actor-linked source IPs used to initiate contact – 84.42.94[.]127, 84.42.92[.]225 (and 2 more IPs observed: 84.42.92[.]111, 84.42.92[.]176).
- [Domain ] impersonation and hosting of help-desk identities – griffinintl[.]net (helpdesk[at]griffinintl[.]net), groupbiocare[.]com (h.tachouche[at]groupbiocare[.]com).
- [Office 365 Tenant ID ] disposable tenant identifiers used for onmicrosoft accounts – f51f2e98-9365-4666-9be8-5b39063c6692, 2ad507a0-38a0-4574-baae-0ccc19c7e051.
- [Filename ] malicious script names used during RMM sessions – MailAccountWizard.jar (used to mimic legitimate email tools during pre-ransomware staging).