Keenadu, a backdoor found in Android firmware, appears to have been introduced via a malicious static library linked to libandroid_runtime.so during firmware builds and, in other cases, pushed through OTA updates; it acts as a multistage loader enabling remote control, search hijacking, monetized app installs, and stealthy ad interactions. Extensive DNS and WHOIS analysis uncovered 29 primary IoCs (five subdomains, 20 domains, four IPs), dozens of associated email- and IP-connected domains, and additional weaponized IPs—highlighting infrastructure tied to istaticfiles[.]com. #Keenadu #istaticfiles
Keypoints
- Keenadu is a multistage firmware backdoor linked to a malicious static library connected with libandroid_runtime.so and has been found across multiple Android brands, with some infections delivered via OTA updates.
- The malware provides operators full remote control and includes payloads that hijack search engines, monetize new app installs, and interact stealthily with ad elements.
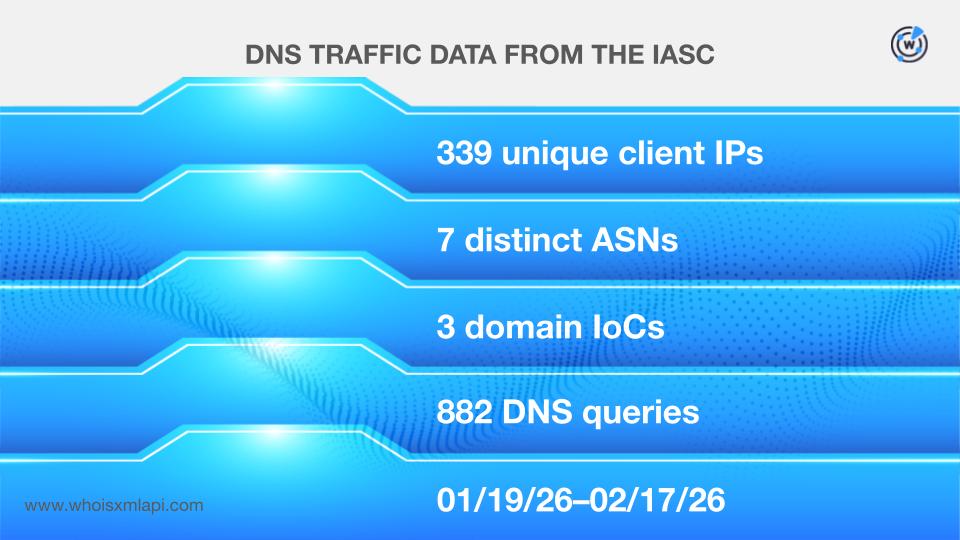
- Researchers extracted 29 primary network IoCs (five subdomains, 20 domains, four IPs) and observed 339 unique client IPs contacting three IoC domains and 61 potential victim IPs contacting two IoC IPs.
- Three domain IoCs were registered with malicious intent from inception, and several domains first resolved to IPs as recently as 2023 while others date back much further, indicating mixed aging tactics by attackers.
- WHOIS and reverse WHOIS analysis produced 80 email‑connected domains (12 already weaponized) and 52 IP‑connected domains, while DNS lookups revealed eight additional IP addresses (four weaponized).
- A public sample of additional artifacts is available for download from the researchers’ website; the report cautions that some flagged entities may later be reclassified and recommends supplementary investigation.
MITRE Techniques
Indicators of Compromise
- [Domain ] IoC domains identified in DNS/WHOIS analysis – gvvt1[.]com, playstations[.]click, and other 18 domains
- [Subdomain ] Five subdomain IoCs flagged as malware (hosted on legitimate cloud servers and on istaticfiles[.]com) – istaticfiles[.]com (host of multiple IoC subdomains) and three cloud-hosted subdomains, and 4 more subdomains
- [IP address ] Four IP IoCs observed with historical IP-to-domain resolutions – 110[.]34[.]191[.]81, 67[.]198[.]232[.]187, and 2 other IPs
- [Email-connected domains ] Email addresses recovered from WHOIS history led to 80 email-connected domains (12 weaponized) – fuhidd[.]com, huulog[.]com, and 78 other domains
- [Additional weaponized IPs ] Additional IPs discovered via DNS lookups, several already used in malicious campaigns – 104[.]21[.]87[.]166, 172[.]67[.]144[.]175, and 6 other IPs
- [Client/Victim IP addresses ] Network traffic samples showing affected endpoints – 339 unique client IP addresses (communicated with IoC domains), 61 potential victim IP addresses (communicated with IoC IPs)
Read more: https://circleid.com/posts/dns-analysis-of-the-keenadu-backdoor-network