Proofpoint monitored a cargo‑theft actor’s month‑long post‑compromise activity in a Deception.pro decoy environment, revealing installation of multiple remote management tools and operator-driven reconnaissance. The actor abused a third‑party signing‑as‑a‑service to re‑sign ScreenConnect installers and maintain stealthy persistence while targeting financial and transportation platforms for freight fraud and cargo theft. #ScreenConnect #signer.bulbcentral.com
Keypoints
- Proofpoint observed a threat actor maintaining access in a decoy environment for more than a month, allowing detailed visibility into post‑compromise operations and operator decision‑making.
- Initial access was achieved via a compromised load board and a malicious VBS payload delivered by email to carriers, which launched PowerShell and deployed remote access tooling.
- The actor installed multiple concurrent RMM solutions—four ScreenConnect instances, Pulseway, and SimpleHelp—to create redundancy and preserve access if one tool was detected or disabled.
- A previously undocumented signing‑as‑a‑service workflow was used to re‑sign ScreenConnect installers and binaries with a fraudulent but valid Authenticode certificate, bypassing revocations and suppressing security warnings.
- At least 13 PowerShell scripts automated reconnaissance to enumerate users, extract browser history and locked browser databases, and search for banking, accounting, fleet payment, and fuel card access.
- Operator actions included manual browser access to PayPal, execution of a cryptocurrency‑wallet‑stealer binary, and exfiltration of findings to attacker‑controlled Telegram bots to identify financially valuable victims.
MITRE Techniques
- [T1566 ] Phishing – Delivery of a malicious payload via email to targeted carriers; ‘delivered a malicious payload via email to transportation carriers inquiring about fraudulent advertised loads.’
- [T1059 ] Command and Scripting Interpreter – Use of VBS and PowerShell to download, execute, and chain payloads; ‘Downloaded and executed a PowerShell script’ and reference to the initial Visual Basic Script (VBS) payload.
- [T1021 ] Remote Services – Installation and use of remote access/RMM tools for interactive access and persistence (ScreenConnect, Pulseway, SimpleHelp); ‘Installed the ScreenConnect remote access tool’ and ‘Pulseway Remote Monitoring and Management (RMM) SimpleHelp RMM.’
- [T1553.002 ] Code Signing – Abuse of a third‑party signing‑as‑a‑service to re‑sign installers and evade trust controls; ‘re‑signed ScreenConnect installers and components with a valid—but fraudulent—code‑signing certificate.’
- [T1053 ] Scheduled Task/Job – Use of delayed SYSTEM scheduled tasks to evade proxy controls and maintain persistence; ‘creating delayed SYSTEM scheduled tasks to evade proxy controls.’
- [T1005 ] Data from Local System – Copying and exfiltration of browser artifacts and locked browser databases for credential/financial discovery; ‘Copy locked browser databases to temporary locations’ and ‘Extract browsing history from Chrome, Edge, Firefox, and Chromium‑based variants.’
- [T1041 ] Exfiltration Over C2 Channel – Transmission of reconnaissance results and search hits to attacker infrastructure and Telegram bots; ‘exfiltrate positive findings to attacker‑controlled Telegram bots’ and sending summaries to Telegram for operator review.
- [T1082 ] System Information Discovery – Enumeration of installed antivirus software, local user accounts, and endpoint telemetry to assess financial value; ‘enumerated installed antivirus software and checked for the presence of high‑value financial, tax, accounting, and cryptocurrency applications.’
Indicators of Compromise
- [SHA256 ] Malicious payloads and tooling – 1f89a432471ec2efe58df788c576007d6782bbdf5b572a5fbf5da40df536c9f5 (VBS payload), f4977bfeae2a957add1aaf01804d2de2a5a5f9f1338f719db661ac4f53528747 (ScreenConnect), and 7 more hashes
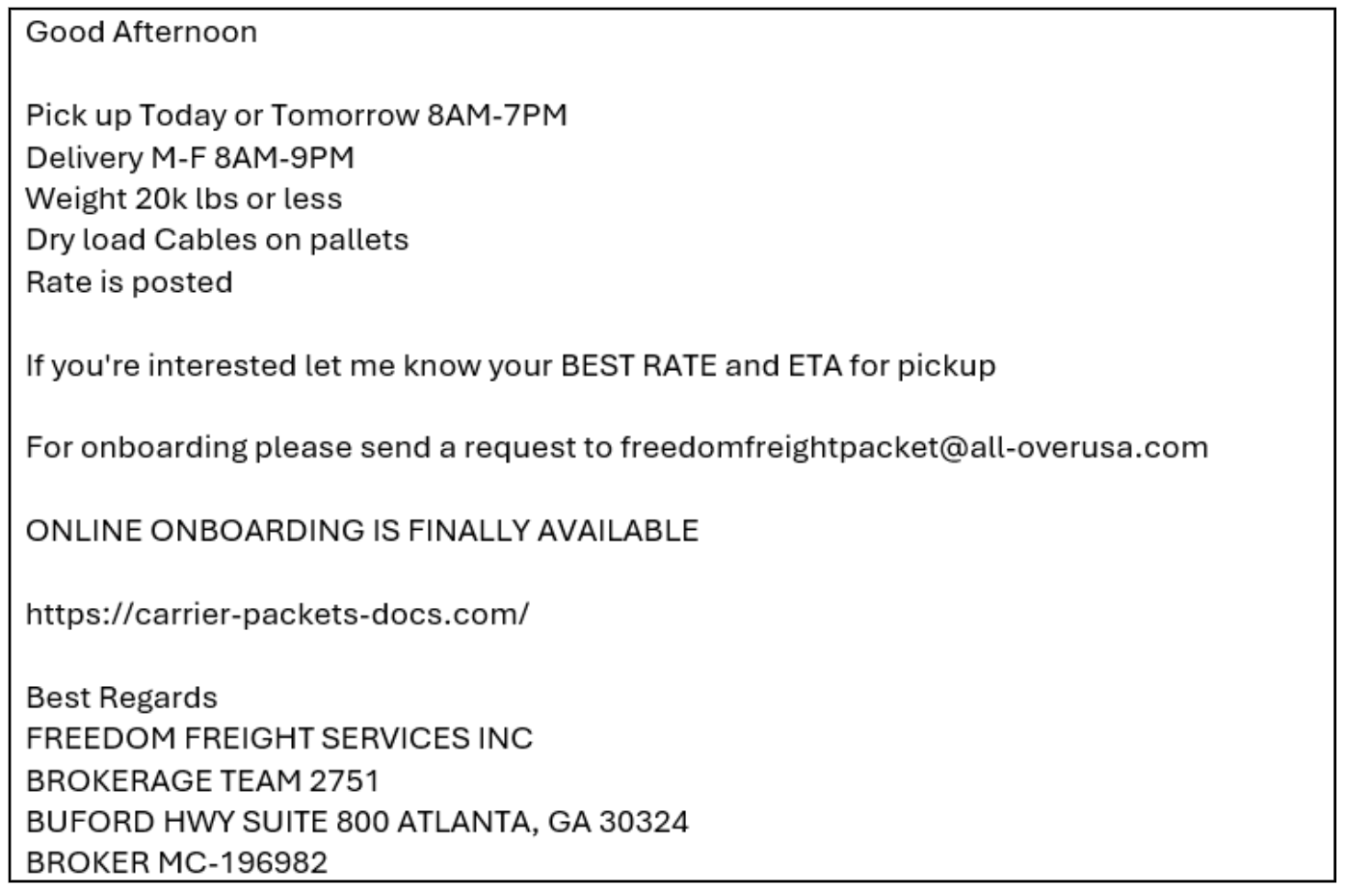
- [URL ] Staging and payload hosts – hxxps://carrier-packets-docs[.]com/FREEDOM_FREIGHT_SERVICES_CARRIERS_ONBOARDING.vbs (VBS staging), hxxps://qto12q[.]top/pdf.ps1 (PowerShell staging)
- [Domain/Hostname ] C2 and signing infrastructure – screlay.amtechcomputers[.]net (ScreenConnect C2), signer.bulbcentral[.]com (external signing service); services-sc-files.s3.us-east-2.amazonaws[.]com (signed MSI hosting)
- [IP address ] Actor infrastructure – 147.45.218[.]0 (observed related to SimpleHelp C2)
- [Certificate ] Fraudulent code‑signing certificate used to sign installers – SignerName: STEPHEN WHANG, CPA, INC.; Thumbprint: D45D60B20006BC3A39AE1761CB5F5F5B067B4EE5; ValidFrom 12/23/2025 ValidTo 12/24/2026 (used to evade revocation and suppress security warnings)