A compromised Joomla site contained a heavily obfuscated PHP loader injected at the top of index.php that contacted remote C2 domains to retrieve instructions and dynamically inject spam, redirects, or fake SEO content. The attacker used two-character string concatenation and a remote-loading design to avoid detection while exfiltrating server environment data via $_SERVER, with cdn[.]erpsaz[.]com and cdn[.]saholerp[.]com acting as active C2s and lashowroom[.]com present as a decoded but unused decoy. #Joomla #cdnErpsazCom
Keypoints
- Heavily obfuscated PHP code was injected at the top of the Joomla index.php file and functioned as a remote loader rather than storing spam locally.
- The loader contacts attacker-controlled C2 domains, sends server environment details, and receives instructions that determine whether to redirect visitors, print raw payloads, or serve fake SEO content.
- String obfuscation avoided single base64 blobs by assembling the base64 payload from two-character chunks and using a 27-entry lookup table (mpjy) to reconstruct strings at runtime.
- Three domains appear in the payload: cdn[.]erpsaz[.]com (primary C2), cdn[.]saholerp[.]com (fallback C2), and lashowroom[.]com (decoded into the table but never used, acting as a decoy).
- The cloaking engine selectively serves content: redirects real users, serves keyword-stuffed HTML or XML sitemaps to crawlers, and can inject arbitrary product links—allowing dynamic control without modifying local files.
- Remediation required removing the injected code from index.php, resetting admin credentials, conducting a full file integrity check, updating Joomla/extensions, using a WAF, enforcing strong passwords/2FA, and restricting file permissions.
MITRE Techniques
- [T1071 ] Application Layer Protocol – The loader uses HTTP to communicate with attacker-controlled C2 servers and retrieve instructions (‘http://cdn[.]erpsaz[.]com/admin.php’).
- [T1105 ] Ingress Tool Transfer – The script acts as a remote loader that fetches remote content/payloads from C2 infrastructure to determine site behavior (‘the script acts as a remote loader. It contacts an external server, sends information about the infected website, and waits for instructions’).
- [T1027 ] Obfuscated Files or Information – The malware splits base64 and other strings into two-character concatenations and assembles them at runtime to evade signature-based scanners (‘the strings are not stored as single base64 blobs… the code is broken into two-character strings that reassemble and execute perfectly at runtime’).
- [T1041 ] Exfiltration Over C2 Channel – The attacker- controlled endpoint receives encoded server environment data collected from $_SERVER, enabling fingerprinting and targeted responses (‘The script collects server environment data using the $_SERVER variable and encodes it before sending it to the attacker’).
- [T1190 ] Exploit Public-Facing Application – The compromise aligns with attacks exploiting outdated Joomla instances and known vulnerabilities to gain initial access (‘The majority of compromises we see exploit known, patched vulnerabilities in outdated installations’).
- [T1505 ] Server Software Component – Web Shell/Backdoor – Malicious code persistent in index.php provides remote control and a backdoor for dynamic content manipulation (‘malicious code injected at the top of the Joomla index.php file’ / ‘A backdoor like this one is almost always sitting quietly at the very top of that file’).
Indicators of Compromise
- [Domains ] attacker C2 and decoy domains embedded in the payload – cdn[.]erpsaz[.]com (primary C2), cdn[.]saholerp[.]com (fallback C2), and lashowroom[.]com (decoded but unused decoy).
- [URLs ] C2 endpoints and request paths observed in the code – http://cdn[.]erpsaz[.]com/admin.php, http://cdn[.]saholerp[.]com/admin.php.
- [File names ] infected or referenced server files – index.php (Joomla core file with injected obfuscated PHP at the top), admin.php (C2 script path referenced by the loader).
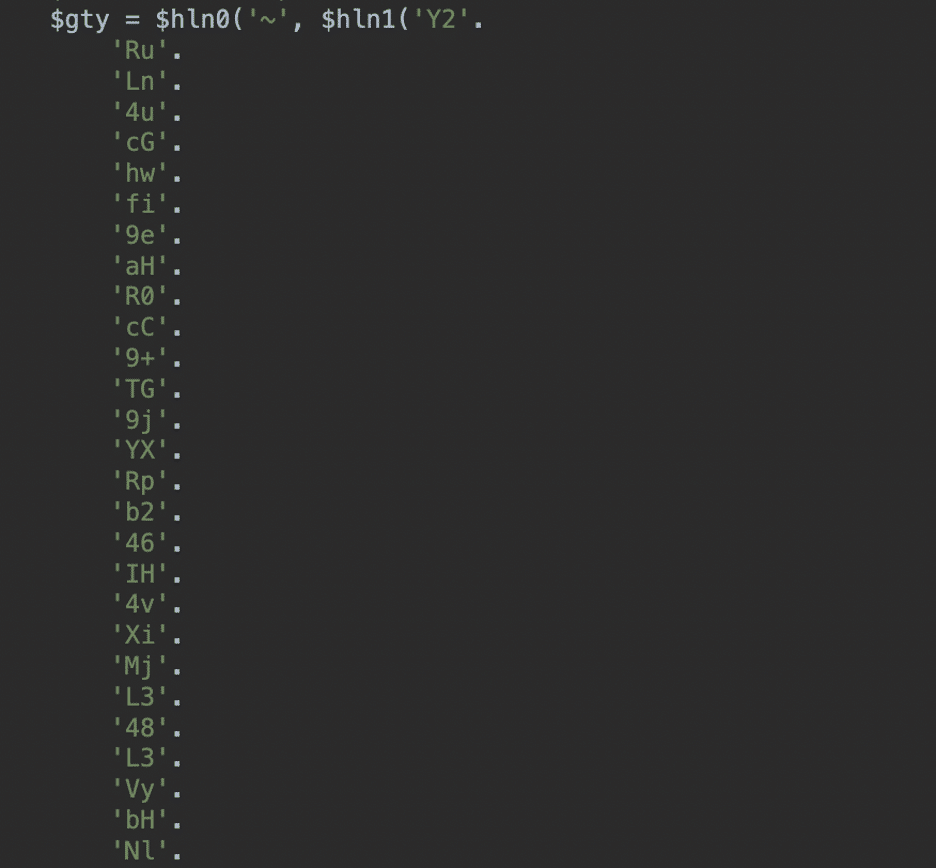
- [Code patterns ] obfuscated PHP and string assembly patterns – two-character concatenated base64 string table and mpjy() lookup usage (e.g., base64 assembled from 2-character chunks and split on ‘~’).
- [Injected content ] dynamically served fake content and spam indicators – unrelated product links appearing on site pages and fake XML sitemap content containing ” served to crawlers.