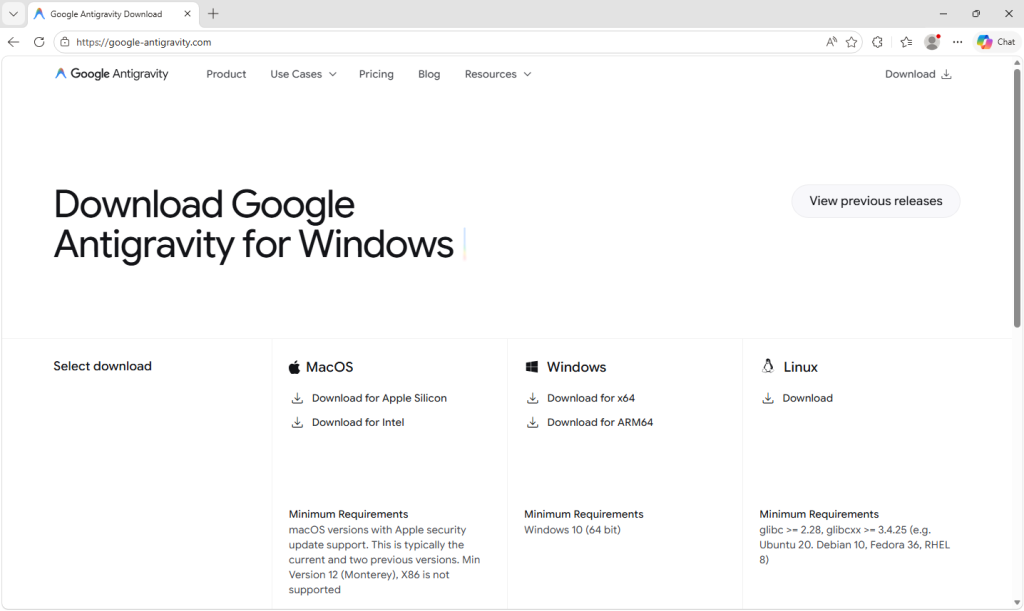
A trojanized Antigravity installer downloaded from a typosquat domain (google-antigravity[.]com) ran a single malicious MSI custom-action that dropped PowerShell downloader scripts which checked in to opus-dsn[.]com and could fetch follow-on payloads. When activated, the follow-on payloads disabled Defender/AMSI, staged an encrypted .NET stealer via a fake MicrosoftEdgeUpdate.png delivered from captr.b-cdn[.]net, persisted via a scheduled task, and exfiltrated browser credentials, session cookies, tokens, crypto wallets, and other sensitive data. #GoogleAntigravity #opus-dsn
Keypoints
- The attacker repackaged the legitimate Antigravity installer (Antigravity_v1.22.2.0.exe) and added a single malicious MSI custom-action named wefasgsdfg that runs a PowerShell script during install.
- The installer drops two PowerShell files (scr*.ps1 and pss*.ps1); the attacker-added script opens an HTTPS connection to opus-dsn[.]com to download and execute further code (a downloader cradle).
- If the operator authorizes escalation, the follow-on script disables Defender and AMSI (via Add-MpPreference and writing AmsiEnable=0), collects and RSA-encrypts a machine profile, and sends it to the operator for targeting decisions.
- Persistence is achieved by downloading an AES-encrypted payload disguised as secret.png to C:ProgramDataMicrosoftEdgeUpdate.png and registering a near-legitimate scheduled task (MicrosoftEdgeUpdateTaskMachineCore…) that runs a headless conhost.exe to decrypt and reflectively load the .NET assembly in memory.
- The in-memory .NET stealer exfiltrates browser logins, cookies, autofill data, Discord/Telegram/Steam tokens, FTP credentials, and crypto wallet files; it also contains clipboard hijacking, keylogging, and hidden-desktop capabilities for account takeover and fraud.
- Response guidance: search logs for opus-dsn[.]com, captr.b-cdn[.]net, google-antigravity[.]com, or 89[.]124[.]96[.]27; sign out everywhere and change email-first passwords; rotate keys and move crypto from a clean device; wipe and reinstall Windows and notify IT if corporate.
MITRE Techniques
- [T1059.001 ] PowerShell – Attacker used PowerShell scripts as the installer custom-action and downloader cradle to fetch and run follow-on code (‘two PowerShell files … scr5020.ps1 and pss5032.ps1’ and ‘open an HTTPS connection to https://opus-dsn[.]com/login/, download whatever code the server sends back, and run it.’)
- [T1071.001 ] Application Layer Protocol: Web Protocols – Command-and-control and payload retrieval occurred over HTTPS to opus-dsn[.]com and 89[.]124[.]96[.]27 (‘a single TCP connection on port 443 to 89[.]124[.]96[.]27 with a quiet HTTPS GET to /login/’)
- [T1105 ] Ingress Tool Transfer – The operation downloaded staged payload files (secret.png, GGn.xml) from a CDN host and saved them to disk for later use (‘downloads a file called secret.png from https://captr.b-cdn[.]net/secret.png … and saves it to C:ProgramDataMicrosoftEdgeUpdate.png’)
- [T1562.001 ] Impair Defenses: Disable or Modify Tools – The follow-on script modifies Defender exclusions and disables AMSI to prevent detection (‘calls Add-MpPreference … to exclude %ProgramData% and %APPDATA% … and writes AmsiEnable=0 into HKLMSoftwarePoliciesMicrosoftWindows ScriptSettings’)
- [T1053.005 ] Scheduled Task/Job – Persistence is achieved by creating a scheduled task named to resemble Microsoft Edge update that runs at logon to load the payload (‘registered with the name MicrosoftEdgeUpdateTaskMachineCore{JBNEN-NQVNZJ-KJAN323-111} … set to fire at every logon’)
- [T1055 ] Process Injection – The encrypted payload is decrypted in memory and reflectively loaded into a running process (conhost.exe -> hidden PowerShell), avoiding on-disk executables (‘conhost.exe –headless launching a hidden PowerShell, which decrypts the fake PNG in memory and reflectively loads the resulting .NET assembly into its own address space’)
- [T1555.003 ] Credentials from Web Browsers – The stealer specifically extracts saved logins, cookies, and autofills from Chromium- and Firefox-based browsers (‘it scans browsers … collecting data labeled Logins, Cookies, Autofills’)
- [T1056 ] Input Capture – The payload includes capabilities to capture keystrokes and hijack the clipboard to steal typed secrets or swap cryptocurrency addresses (‘imports Windows APIs used for clipboard hijacking and keystroke logging’)
- [T1113 ] Screen Capture – The malware contains building blocks for creating a hidden desktop and capturing or controlling it, enabling stealthy account access (‘creating a second, invisible Windows desktop that the attacker can capture and potentially control’)
- [T1027 ] Obfuscated Files or Information – The operation uses obfuscation and encryption (dynamic filenames, backtick splitting, AES with PBKDF2) to hide actions and payloads (‘the cmdlet name split by a backtick … key and IV both derived via PBKDF2 with 10,000 iterations from a hardcoded passphrase’)
Indicators of Compromise
- [SHA-256 ] malicious installer – 61aca585687ec21a182342a40de3eaa12d3fc0d92577456cae0df37c3ed28e99 (Antigravity_v1.22.2.0.exe)
- [Domain ] typosquat and C2/CDN – google-antigravity[.]com (typosquat distribution), opus-dsn[.]com (C2/check-in), and other domain captr.b-cdn[.]net (payload CDN)
- [IP Address ] C2 server – 89[.]124[.]96[.]27 (observed single TCP connection on port 443 for the downloader cradle)
- [File Name ] dropped/staged files – Antigravity_v1.22.2.0.exe (trojanized installer), secret.png (AES-encrypted .NET payload staged to C:ProgramData), and GGn.xml (second in-memory payload)
- [File Path ] installation and persistence locations – C:Program Files (x86)Google LLCAntigravity (legitimate-looking install), C:ProgramDataMicrosoftEdgeUpdate.png (encrypted payload)