Researchers discovered a campaign using a previously observed DLL loader to deliver Needle Stealer, a modular Golang infostealer that harvests browser data, wallets, and other sensitive files and can deploy malicious browser extensions. The malware was distributed via a fake AI trading site (tradingclaw[.]pro) and communicates with C2 servers via HTTP API endpoints to exfiltrate data and receive instructions #NeedleStealer #TradingClaw
Keypoints
- Needle is a modular Golang infostealer with core capabilities (form grabbing, clipboard hijacking, screenshots) and modules targeting desktop and browser cryptocurrency wallets.
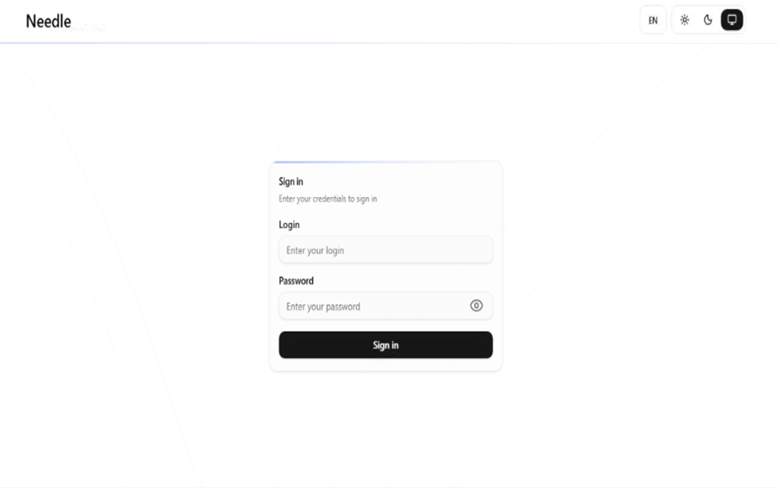
- Attackers used a fake TradingClaw website (tradingclaw[.]pro) as the lure, selectively showing malicious content or redirecting to a benign-looking studypages[.]com to evade detection.
- The initial infection chain uses DLL hijacking (iviewers.dll) to load a second-stage DLL that injects Needle into RegAsm.exe via process hollowing.
- Needle can drop and install malicious browser extensions (packed as hidden ZIPs like base.zip/meta.zip) that intercept browsing activity, inject scripts, perform redirects, and replace downloads.
- The malware and extensions communicate with C2 API endpoints (e.g., /upload, /extension, /scripts) and support backup domains to maintain connectivity.
- Detected IOCs include specific file hashes, malicious domains (tradingclaw[.]pro, chrocustumapp[.]com, coretest[.]digital, etc.) and multiple C2 IP addresses; defenders are advised to check EDR logs, browser extension folders, and move crypto funds from affected machines.
MITRE Techniques
- [T1574.001 ] DLL Search Order Hijacking – The campaign “relies on a technique called DLL hijacking.” (‘the attack relies on a technique called DLL hijacking.’)
- [T1055.012 ] Process Hollowing – The loader “injects the Needle Stealer into a legitimate Windows process (RegAsm.exe) using a technique known as process hollowing.” (‘injects the Needle Stealer into a legitimate Windows process (RegAsm.exe) using a technique known as process hollowing.’)
- [T1056 ] Input Capture – Needle Core implements “form grabbing (capturing data you enter into websites) and clipboard hijacking” to capture user input and clipboard contents. (‘form grabbing (capturing data you enter into websites) and clipboard hijacking’)
- [T1113 ] Screen Capture – The stealer can “Take screenshots of the infected system” to capture visual data from the victim’s desktop. (‘Take screenshots of the infected system’)
- [T1555.003 ] Credentials from Web Browsers – The malware “Steal[s] browser data, including history, cookies, and saved information” to harvest stored credentials and session data. (‘Steal browser data, including history, cookies, and saved information’)
- [T1176 ] Browser Extensions – The threat “has the ability to install malicious browser extensions” that provide extensive browser control and data theft. (‘its ability to install malicious browser extensions.’)
- [T1059.007 ] JavaScript – The extensions and stealer “inject scripts directly into web pages, enabling further data theft or manipulation.” (‘inject scripts directly into web pages, enabling further data theft or manipulation.’)
- [T1041 ] Exfiltration Over Command and Control Channel – Stolen data is sent back to attackers via an API endpoint (“/upload—sends stolen data back to the attackers”). (‘/upload—sends stolen data back to the attackers’)
- [T1071.001 ] Application Layer Protocol: Web Protocols – The malware and extensions use HTTP-based API endpoints (e.g., /extension, /scripts, /backup-domains/active) to communicate with C2 servers. (‘/backup-domains/active—retrieves backup servers …’, ‘/extension—receives instructions …’, ‘/scripts—downloads malicious code …’)
Indicators of Compromise
- [File Hashes ] Needle-related binaries – 95dcac62fc15e99d112d812f7687292e34de0e8e0a39e4f12082f726fa1b50ed, 0d10a6472facabf7d7a8cfd2492fc990b890754c3d90888ef9fe5b2d2cca41c0
- [Domains ] Malicious distribution and C2 – tradingclaw[.]pro (fake site), coretest[.]digital (C2 panel), and 4 more domains including chrocustumapp[.]com, chrocustomreversal[.]com, google-services[.]cc, reisen[.]work
- [IP Addresses ] C2 infrastructure – 178[.]16[.]55[.]234, 185[.]11[.]61[.]149, and 5 more IPs associated with C2 panels (e.g., 37[.]221[.]66[.]27, 2[.]56[.]179[.]16)
- [File Names ] Loader and extension artifacts – iviewers.dll (DLL loader), base.zip/meta.zip (embedded extension archives), popup.js/content.js/background.js (dropped extension files)
- [File Paths ] Extension installation location – malicious extensions dropped to %LOCALAPPDATA%PackagesExtensions (contains popup.js, content.js, background.js)