The GlassWorm campaign has expanded on Open VSX with a new cluster of 73 impersonation extensions that were initially published as benign “sleeper” packages and later updated to deliver malware through normal extension update and dependency mechanisms. Socket is tracking confirmed malicious activations and many high-confidence sleeper extensions that use cloned listings, transitive delivery, GitHub-hosted VSIX payloads, native binaries, and obfuscated JavaScript to evade detection. #GlassWorm #OpenVSX
Keypoints
- Socket is tracking a new cluster of 73 impersonation extensions on Open VSX that were published by newly created GitHub accounts with minimal repositories (one empty repo named with an eight-character string).
- At least six of the tracked extensions have already been activated to deliver malware, while the remainder are classified as high-confidence sleepers or suspicious extensions pending further updates.
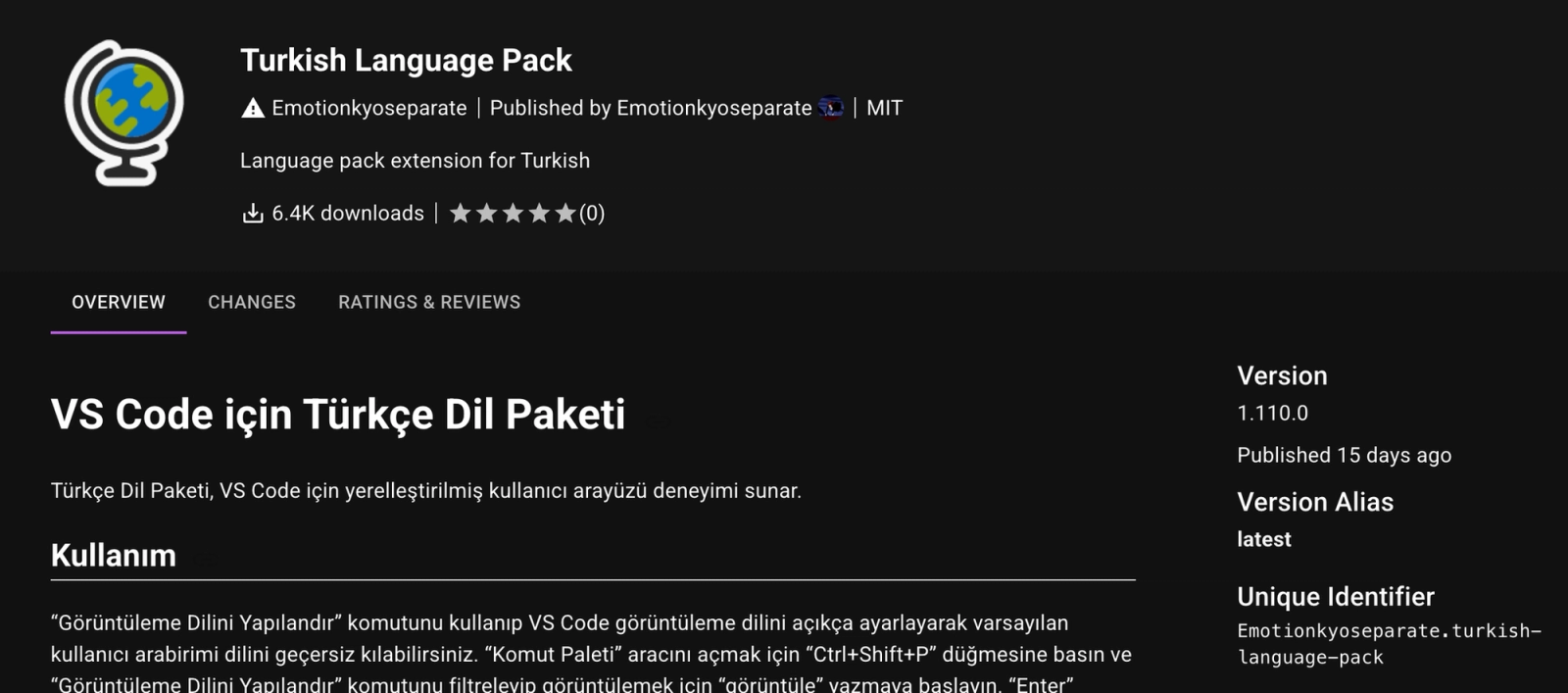
- Attackers are using cloned listings that mimic legitimate extensions (e.g., Emotionkyoseparate.turkish-language-pack mimicking MS-CEINTL.vscode-language-pack-tr) to socially engineer installs and build credibility prior to weaponization.
- Delivery techniques include transitive delivery via extensionPack/extensionDependencies, updates that retrieve VSIX payloads from GitHub, previously observed Solana transaction memos as dead-drops, bundled native installer binaries, and obfuscated JavaScript loaders.
- Many extensions act as thin loaders where core malicious logic runs outside the visible source: platform-specific .node binaries embed GitHub release URLs and invoke installer logic, while other variants use heavily obfuscated JS to decode and fetch payloads at runtime.
- Socket has marked the tracked extensions on its GlassWorm v2 page and continues analysis as new updates appear, warning users and protecting tracked listings while investigation proceeds.
MITRE Techniques
- [T1195 ] Supply Chain Compromise – Threat actors publish impostor or “sleeper” extensions to a software marketplace and later weaponize them via updates or dependencies; (‘A sleeper extension or package is a threat actor-controlled imposter that is published before it is weaponized.’)
- [T1583 ] Acquire Infrastructure – Adversaries create and use newly created GitHub accounts and repositories to host payloads and masquerade as publishers; (‘published by newly created GitHub accounts with only one or two public repositories. In each case, one repository is empty and named with an eight-character string.’)
- [T1105 ] Ingress Tool Transfer – Extensions retrieve additional payloads (VSIX files) from external hosting such as GitHub releases and download them during activation or updates; (‘sleeper extensions that activate via updates and retrieve payloads from external sources, including VSIX packages hosted on GitHub.’)
- [T1059 ] Command and Scripting Interpreter – Extensions resolve CLI paths for multiple editors and execute installer commands (e.g., –install-extension) to install downloaded payloads across IDEs; (‘installs the downloaded extension using commands such as –install-extension.’)
- [T1574 ] Hijack Execution Flow – Malicious behavior is executed from platform-specific native modules (.node binaries) loaded at activation time so the JavaScript source does not show core logic; (‘the activation code simply loads a platform-specific native module and invokes an install() function … The core logic is implemented in the bundled .node binary’)
- [T1027 ] Obfuscated Files or Information – Adversaries use heavily obfuscated JavaScript that decodes at runtime to retrieve and execute payloads, hiding the delivery logic from static inspection; (‘the activation code contains heavily obfuscated code that decodes at runtime to retrieve a .vsix payload from a GitHub release.’)
Indicators of Compromise
- [SHA256 ] Native and VSIX payload hashes – native installer binary: 1b62b7c2ed7cc296ce821f977ef7b22bae59ef1dcdb9a34ae19467ee39bcf1684ebfe8f66ca7e9751060b3301b5e8838d6017593cdae748541de83bfa28183bd, downloaded VSIX payload: 97c275e3406ad6576529f41604ad138c5bdc4297d195bf61b049e14f6b30adfd
- [Domain/Hosting ] GitHub repositories used to host payloads – github[.]com/SquadMagistrate10/wnxtgkih, github[.]com/francesca898/dqwffqw, and 1 more GitHub-hosted payload location
- [Extension Names (Confirmed Malicious) ] Extensions activated to deliver malware – boulderzitunnel.vscode-buddies, cubedivervolt.html-code-validate, and 4 more confirmed malicious extension names
- [Extension Names (Sleepers/Suspicious) ] High-confidence sleeper or impersonation listings used in the campaign – emotionkyoseparate.turkish-language-pack, peldravix.rpgiv2, and 70 more impersonation/sleeper extensions tracked in this cluster
Read more: https://socket.dev/blog/73-open-vsx-sleeper-extensions-glassworm