Between late August and early September 2025, many IIS servers were compromised via ASP.NET viewstate exploitation using publicly exposed machine keys and a ready-made toolkit that installed a malicious IIS module named “HijackServer”, supplemented by a customized Hidden rootkit to conceal artifacts. The operation deployed C++, .NET and PHP variants of HijackServer to perform SEO fraud and provide unauthenticated remote command execution, using staging domains such as c.cseo99[.]com and f.fseo99[.]com. #HijackServer #Wingtb.sys
Keypoints
- Attackers exploited exposed ASP.NET machine keys to manipulate viewstate and achieve remote code execution on IIS servers.
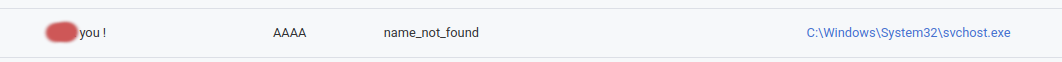
- Post-exploitation used “Potatoes” privilege escalation (EfsPotato, DeadPotato) to create hidden local admin accounts and deploy tooling.
- The toolkit (sys-tw-v1-6-1-clean-log.zip) included HijackServer IIS modules (x86.dll/x64.dll), a customized Hidden rootkit (Wingtb.sys), deployment GUI (HijackDriverManager.exe), and scripts (install.bat, lock.bat).
- HijackServer (C++/.NET) and a PHP variant provided SEO page generation, redirectors to cryptocurrency sites, file upload, and unauthenticated remote shell/command execution endpoints.
- Configuration and templates were fetched from staging servers (notably c.cseo99[.]com and f.fseo99[.]com) and stored under C:WindowsTemp_FAB234CD3-09434-8898D-BFFC-4E23123DF2C.
- Operators used a signed (expired-certificate) rootkit driver Wingtb.sys with a Chinese-localized usermode tool (WingtbCLI.exe) to hide files, registry keys, and processes and to delete Windows Event logs.
- At least 171 HijackServer instances were identified, affecting ~240 IPs and ~280 domains worldwide, indicating opportunistic mass compromise; overlap with activity tracked as Larva-25003 was noted but not conclusively attributed.
MITRE Techniques
- [T1559] Inter-Process Communication – Attackers used ASP.NET viewstate deserialization to execute code on IIS servers by leveraging exposed machine keys (“…the attackers first exploited the ASP .NET viewstate to achieve remote code execution…”).
- [T1203] Exploitation for Client Execution – Exploited deserialization of viewstate and known machine keys to run ASP payloads on targeted servers (“…exploit ASP .NET viewstate deserialization to remotely execute code if they know the associated cryptographic secrets.”).
- [T1068] Exploitation for Privilege Escalation – Used “Potatoes” techniques (EfsPotato and DeadPotato) to escalate privileges and create a hidden local administrator account (“…then leveraged privileges escalation techniques known as “Potatoes” (EfsPotato and DeadPotato) to create an additional “hidden” local administrator (admin$).”).
- [T1105] Ingress Tool Transfer – Deployed a ZIP archive (sys-tw-v1-6-1-clean-log.zip) containing modules, drivers and tools to the compromised hosts (“…the attackers relied on pre-packaged tools and scripts… initially deployed … as a ZIP archive”).
- [T1210] Exploitation of Trusted Relationship – Used a signed kernel driver (Wingtb.sys) signed with an older certificate to load a rootkit on Windows systems (“…The driver is signed with an expired code-signing certificate … may still be loaded on Windows systems…”).
- [T1547] Boot or Logon Autostart Execution – Installed a kernel driver and associated service to persist and hide artifacts (“…Hidden.inf defines the corresponding service name as “Wingtb”… lock.bat loads the driver and hides files and registry keys”).
- [T1566] Phishing (malicious use of web content) – Generated SEO HTML pages and redirects to boost visibility of dubious cryptocurrency sites, abusing search engine crawlers (“…generate SEO HTML pages to answer HTTP requests that come from Google… links to redirection URL paths … lead to questionable cryptocurrency-related websites.”).
- [T1106] Native API – Malicious IIS modules hook HTTP processing stages (GL_PRE_BEGIN_REQUEST, RQ_BEGIN_REQUEST, RQ_SEND_RESPONSE) to manipulate responses and implement C2 (“…hooks all HTTP requests … at the very first stage … uses the content of HTTP requests … as a command and control (C2) channel.”).
- [T1059] Command and Scripting Interpreter – Provided unauthenticated remote command execution via HTTP endpoints (/scjg) and upload form (/mywebdll) to execute Windows shell commands (“…file upload and Windows shell command execution capability … can be triggered without any sort of authentication when bypassing the form (/scjg URL path).”).
- [T1070] Indicator Removal on Host – Scripted deletion of Windows Event logs to cover tracks (“…the install process includes a noisy deletion of every single Windows Event log file… delete every Windows Event log file (for /f “tokens=*” %%1 in (‘wevtutil el’) do wevtutil cl “%%1″).”).
Indicators of Compromise
- [File Hash ] malicious IIS modules and toolkit – c1ca053e3c346513bac332b5740848ed9c496895201abc734f2de131ec1b9fb2 (HijackServer x64/caches.dll), 82b7f077021df9dc2cf1db802ed48e0dec8f6fa39a34e3f2ade2f0b63a1b5788 (HijackServer x86/scripts.dll).
- [File Hash ] rootkit and utilities – f9dd0b57a5c133ca0c4cab3cca1ac8debdc4a798b452167a1e5af78653af00c1 (Wingtb.sys), 913431f1d36ee843886bb052bfc89c0e5db903c673b5e6894c49aabc19f1e2fc (WingtbCLI.exe).
- [Domain ] staging/configuration servers – c.cseo99[.]com (configuration stager), f.fseo99[.]com (files stager); additional related: api.aseo99[.]com.
- [File Path ] deployed module locations – C:WindowsSystem32inetsrvscripts.dll, C:WindowsSystem32inetsrvcaches.dll (IIS modules); C:WindowsSystem32driversWingtb.sys (rootkit).
- [File Hash ] PHP/Apache variants – e3bfd9aca49726556f6279aad2ab54ca9c1f0df22bcad27aa7e1ba3234f8eaff (Apache HijackServer PHP module 1.2.5), 665234a6627269ba0b3816a6a29ede4fc72d36f34978f5ba1410e63d968d3d62 (PHP downloader).
- [Domains ] additional infrastructure and possible variants – c.cseo8[.]com, f.zseo8[.]com, api.xseo8[.]com, and others like lseo99[.]com and jseo99[.]com (likely related staging/reporting endpoints).
Read more: https://harfanglab.io/insidethelab/rudepanda-owns-iis-servers-like-2003/