RedTiger is an open-source, Python-based infostealer (released 2024) that targets gamers by stealing Discord tokens and account data, browser-stored credentials and payment info, game accounts (e.g., Roblox), cryptocurrency wallets, screenshots, and webcam images. Stolen data is archived, uploaded to GoFile, and the download link is sent to attackers via Discord webhook; samples are PyInstaller binaries with some targeting French-speaking users. #RedTiger #GoFile
Category: Threat Research
Check Point Research uncovered a coordinated YouTube Ghost Network that uploaded over 3,000 malicious videos since 2021 to distribute infostealers (notably Lumma and Rhadamanthys) by abusing account roles, positive engagement, and platform features to build trust. The campaign shifted from Lumma to Rhadamanthys after Lumma disruption in 2025 and concentrated on “Game Hacks/Cheats” and “Software Cracks/Piracy” content, driving high view counts for targeted videos. #Lumma #Rhadamanthys
Trend Research reported that the Agenda (Qilin) ransomware group deployed a Linux-based ransomware binary on Windows hosts by abusing legitimate remote management and file-transfer tools (WinSCP and Splashtop), combined with BYOVD techniques and targeted theft of Veeam backup credentials. The campaign used fake Cloudflare R2-hosted CAPTCHA pages, SOCKS proxy backdoors, and…

Silent Push uses domain and DNS analytics, infrastructure-variance metrics, and module fingerprinting to attribute threat actors, detect Fast Flux activity, and identify soon-to-be-malicious infrastructure despite attackers abusing CDNs and cloud services. Jensen emphasizes proactive, data-driven defenses (IOFA feeds, Domain Search, ThreatCheck) and notes automation and modularization are reliable fingerprinting vectors. #SilentPush…

Chinese-linked attackers exploited the recently disclosed SharePoint “ToolShell” vulnerability (CVE-2025-53770) to breach multiple organisations across the Middle East, Africa, South America, Europe and the U.S., deploying loaders and backdoors including Zingdoor, KrustyLoader and ShadowPad. The campaign used DLL sideloading, legitimate binaries, PetitPotam credential theft, and living-off-the-land tools to establish stealthy persistence and credential theft for espionage. #ToolShell #Zingdoor #KrustyLoader
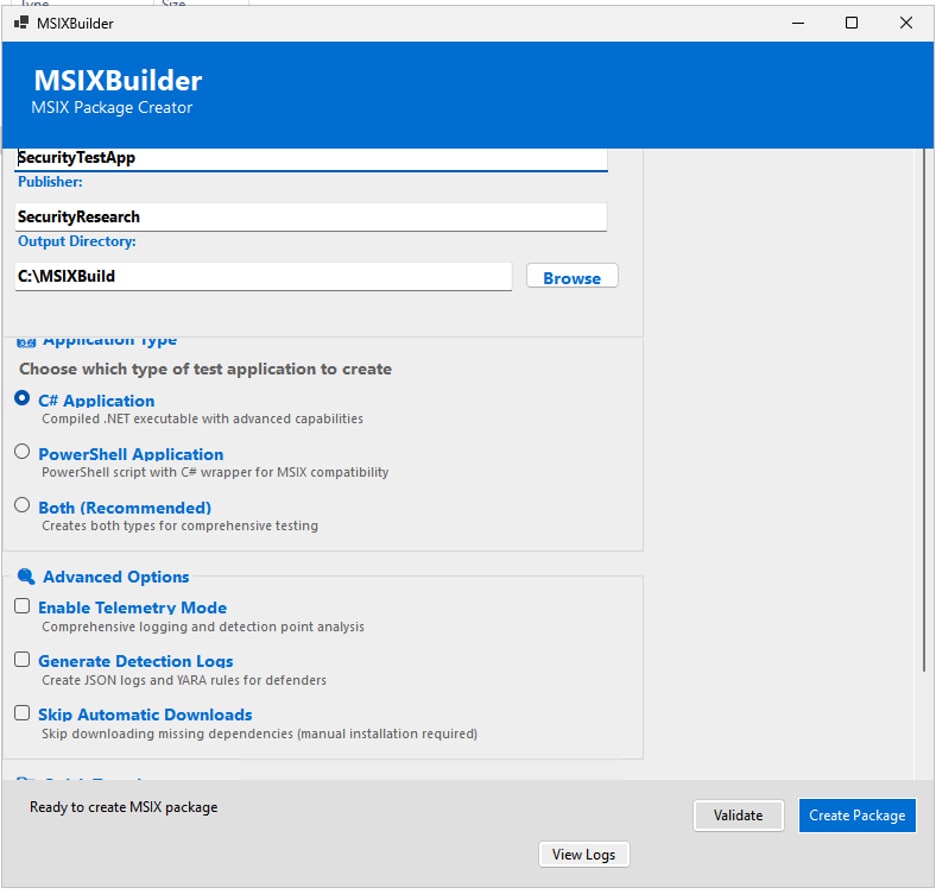
Attackers are weaponizing MSIX packages—using signed developer certificates, malvertising, SEO poisoning, and Loader-as-a-Service offerings—to deliver loaders and remote-access tools that bypass protections and run with elevated capabilities like runFullTrust and PowerShell execution. Defenders can use MSIXBuilder to safely generate realistic signed and unsigned MSIX test packages, validate AppXDeployment and AppXPackaging logging, and deploy the provided Splunk analytics to detect techniques used by groups like FIN7 and campaigns such as Storm-0569. #MSIXBuilder #FIN7
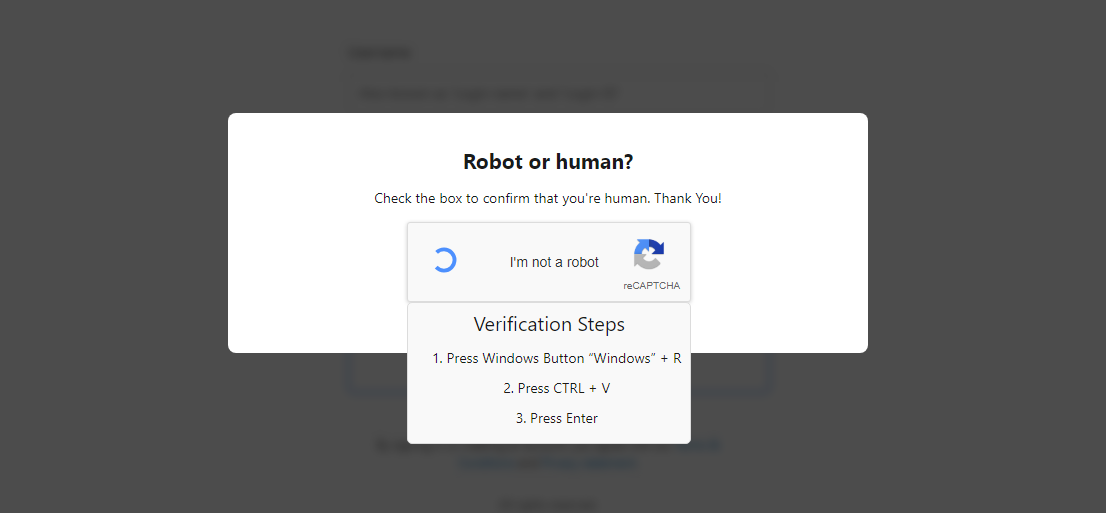
eSentire’s TRU investigated numerous 2025 incidents where threat actors abused legitimate NetSupport Manager RMM, primarily delivered via the ClickFix social engineering vector and executed through PowerShell/JSON, Run Prompt loaders, and MSI-based installers. The report clusters activity into three distinct actor groups (EVALUSION, FSHGDREE32/SGI, XMLCTL), provides IOCs and deobfuscation guidance, and includes detection tooling such as a Yara rule and an unpacking utility. #NetSupport #ClickFix

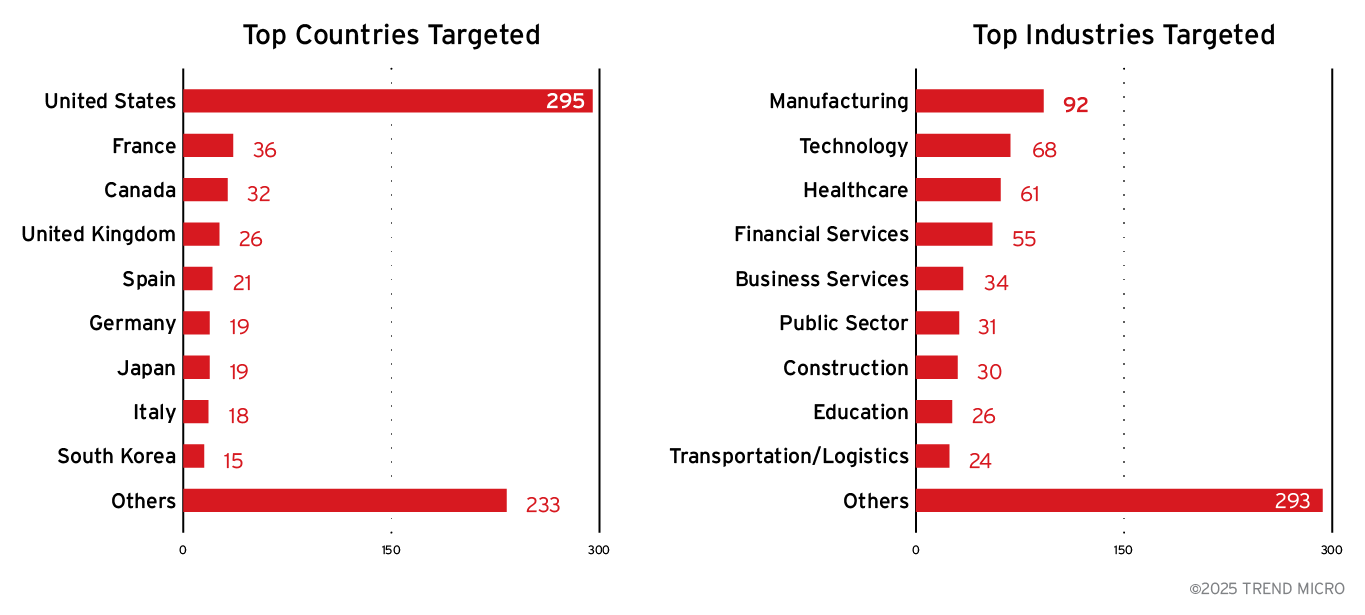
September 2025 saw a surge in ransomware activity led by the Qilin group, notably targeting asset management companies in Korea, alongside the appearance of several new ransomware groups. The AhnLab TIP/ATIP-derived statistics cover top affected countries, industries, top ransomware groups, and three-year detection trends. #Qilin #AhnLab…
Infoblox and UNODC-linked research uncovered Vault Viper (Baoying Group / BBIN), a large iGaming white-label operator distributing a custom “Universe Browser” that routes traffic through China and installs persistent background programs with functionality consistent with RATs and information stealers. The investigation ties Vault Viper to transnational organized crime networks including Suncity and convicted Triad leader Alvin Chau, and documents a vast DNS and C2 footprint used to support online gambling, fraud, and money laundering. #VaultViper #UniverseBrowser
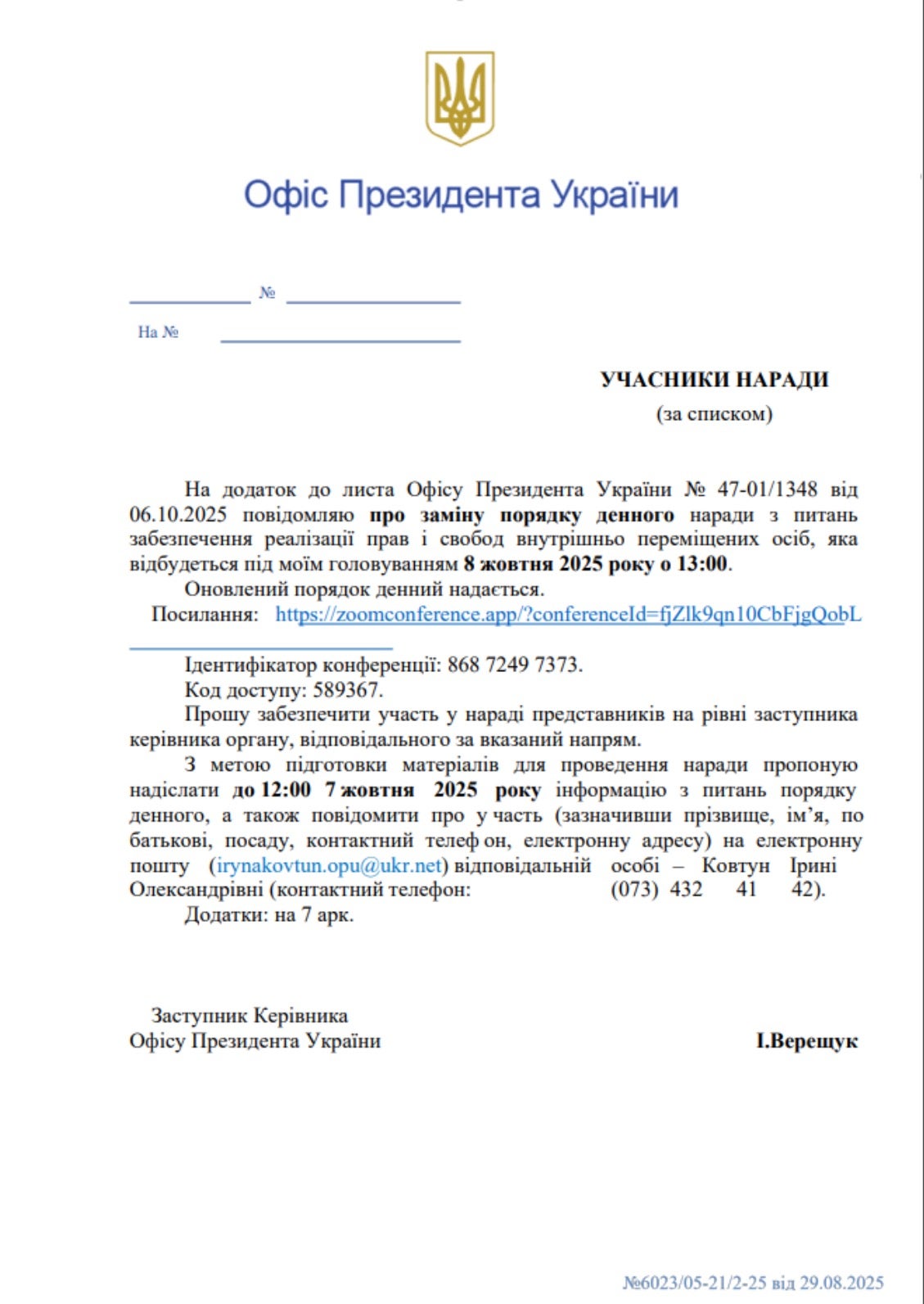
A coordinated spearphishing campaign called PhantomCaptcha targeted NGOs and Ukrainian regional administrations using weaponized PDFs that redirected victims to a fake Cloudflare captcha and coerced them into executing PowerShell loaders. The multi-stage attack delivered a WebSocket RAT and also pivoted to Android lures (princess.apk) hosted on related domains and infrastructure. #PhantomCaptcha #bsnowcommunications #princess.apk
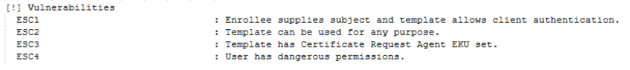
ADCS misconfigurations create a broad privilege-escalation attack surface allowing attackers to obtain certificates that can impersonate high-value domain accounts and potentially lead to full domain and hybrid cloud compromise. Notable tools like Certipy and Certify automate enumeration and exploitation of 16 identified ESC techniques, some of which (e.g., ESC15) exploit known CA vulnerabilities such as CVE-2024-49019. #Certipy #ESC15

TransparentTribe (APT36) conducted a phishing campaign in mid-2025 targeting Linux systems used by Indian government entities, delivering a Golang-based RAT dubbed DeskRAT via malicious .desktop files inside ZIP archives hosted on staging servers. The malware establishes WebSocket C2 communications, supports file collection and remote execution, and uses persistence methods tailored to Linux (systemd service, cron, autostart .desktop, and .bashrc), with decoy PDFs referencing Indian defense events. #DeskRAT #TransparentTribe

The report details multiple cyber incidents affecting financial institutions worldwide, including database leaks, large-scale ransomware attacks (notably by Qilin), and statistics on malware and leaked account credentials targeting the finance sector. It highlights supply-chain infection vectors, data sale attempts on cybercrime forums, and recommends stronger data integrity verification and response strategies….

A large, evolving smishing campaign attributed to the Smishing Triad has used hundreds of thousands of short-lived domains to impersonate toll services, postal carriers, banks, cryptocurrency platforms, healthcare, law enforcement and social media to harvest credentials and personal data. The campaign leverages decentralized infrastructure (many domains, U.S.-hosted IPs, Chinese nameservers and…
Lumma infostealer is distributed via MaaS and phishing sites disguised as pirated software to steal credentials, browser cookies, cryptocurrency wallets, and VPN/RDP account data for use in account takeover and fraud. Strengthening EDR with behavior-based detection and integrating threat intelligence are recommended defenses. #Lumma #MEGA
