A Rhadamanthys infostealer campaign was distributed via malicious Ren’Py game bundles hosted on MediaFire, where a launcher and crafted Ren’Py scripts load a malicious package that ultimately injects Rhadamanthys into a .NET process. The campaign leverages Ren’Py’s python-packages import mechanism, uses encoded .key configuration files and decompressed helper executables to run…
Category: Threat Research
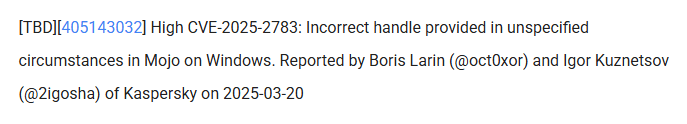
Kaspersky discovered Operation ForumTroll, a targeted espionage campaign that used personalized short-lived phishing links to deliver a Chrome sandbox escape zero-day (CVE-2025-2783) and deploy loaders and spyware including LeetAgent and the commercial Dante spyware. The campaign targeted Russian institutions and used techniques like WebGPU-based validation, COM hijacking persistence, and Fastly-hosted C2s. #CVE-2025-2783 #LeetAgent #Dante

TigerJack is a threat actor who published at least 11 malicious VS Code extensions across multiple publisher accounts that steal C++ source code, mine cryptocurrency, and provide a remote backdoor for full system control; two extensions alone—”C++ Playground” and “HTTP Format”—infected over 17,000 developers before removal from Microsoft’s marketplace but remain active on OpenVSX. The operation uses deceptive, fully functional tools, staged clean releases, coordinated republication, and centralized command-and-control endpoints to persist and scale its campaign. #TigerJack #C++Playground #HTTPFormat #ab498.pythonanywhere.com #CoinIMP
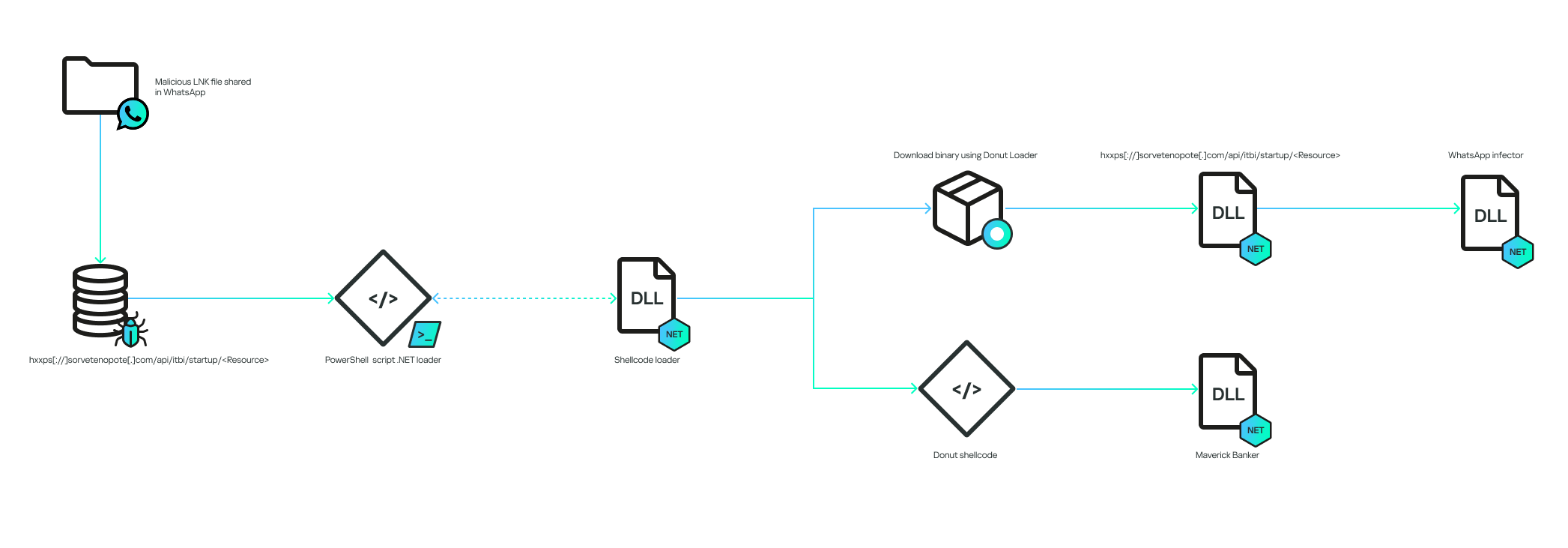
A Brazil-focused campaign spread a new banking trojan named Maverick via WhatsApp by delivering ZIPs containing a malicious LNK that launches a fully fileless infection chain ultimately loading in-memory .NET payloads and Donut shellcode. The campaign uses WPPConnect to hijack WhatsApp accounts for propagation, a C2 that validates user-agent and custom API keys, and shares code overlaps with the Coyote banker. #Maverick #Coyote

Qilin (formerly Agenda) continues high-volume leak-site activity in 2025, posting more than 40 victim cases per month and heavily targeting the manufacturing sector followed by professional and scientific services and wholesale trade. Artifacts show credential theft and exfiltration using tools like Mimikatz, SharpDecryptPwd, and the open-source Cyberduck, and dual encryptor deployments…
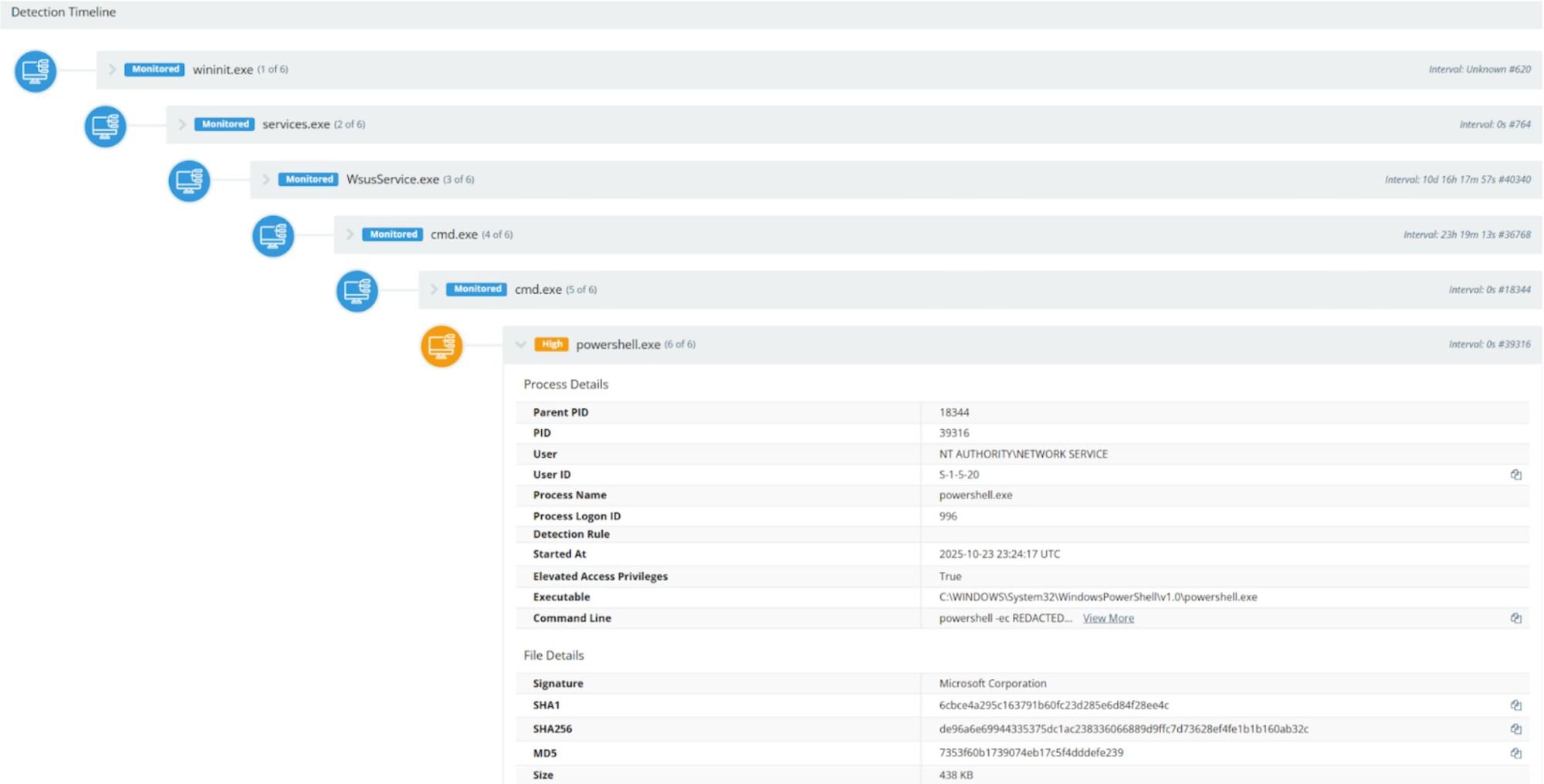
Microsoft released an out‑of‑band updates on October 23 for an unauthenticated deserialization remote code execution vulnerability in Windows Server Update Services (CVE-2025-59287) that has been exploited against publicly exposed WSUS instances on ports 8530/8531. Huntress observed attackers sending crafted POST requests to WSUS web services, spawning cmd.exe and powershell.exe via wsusservice.exe and w3wp.exe, decoding a base64 PowerShell payload that enumerated hosts and exfiltrated data to a remote webhook. #CVE-2025-59287 #WSUS

GhostGrab is a modular Android malware family that combines covert Monero mining with extensive banking credential theft, SMS interception (including OTPs), and device fingerprinting to enable financial fraud and resource monetization. The campaign uses Firebase for C2 and data exfiltration and leverages domains such as kychelp[.]live and uasecurity[.]org to deliver droppers and payloads. #GhostGrab #kychelp.live #uasecurity.org #Monero
AzureHound is an open-source data collection tool used to enumerate Microsoft Entra ID and Azure resources via Microsoft Graph and Azure REST APIs, and while intended for defensive testing, threat actors have misused it for cloud discovery and privilege escalation mapping. Recent activity links its misuse to actors such as Curious…
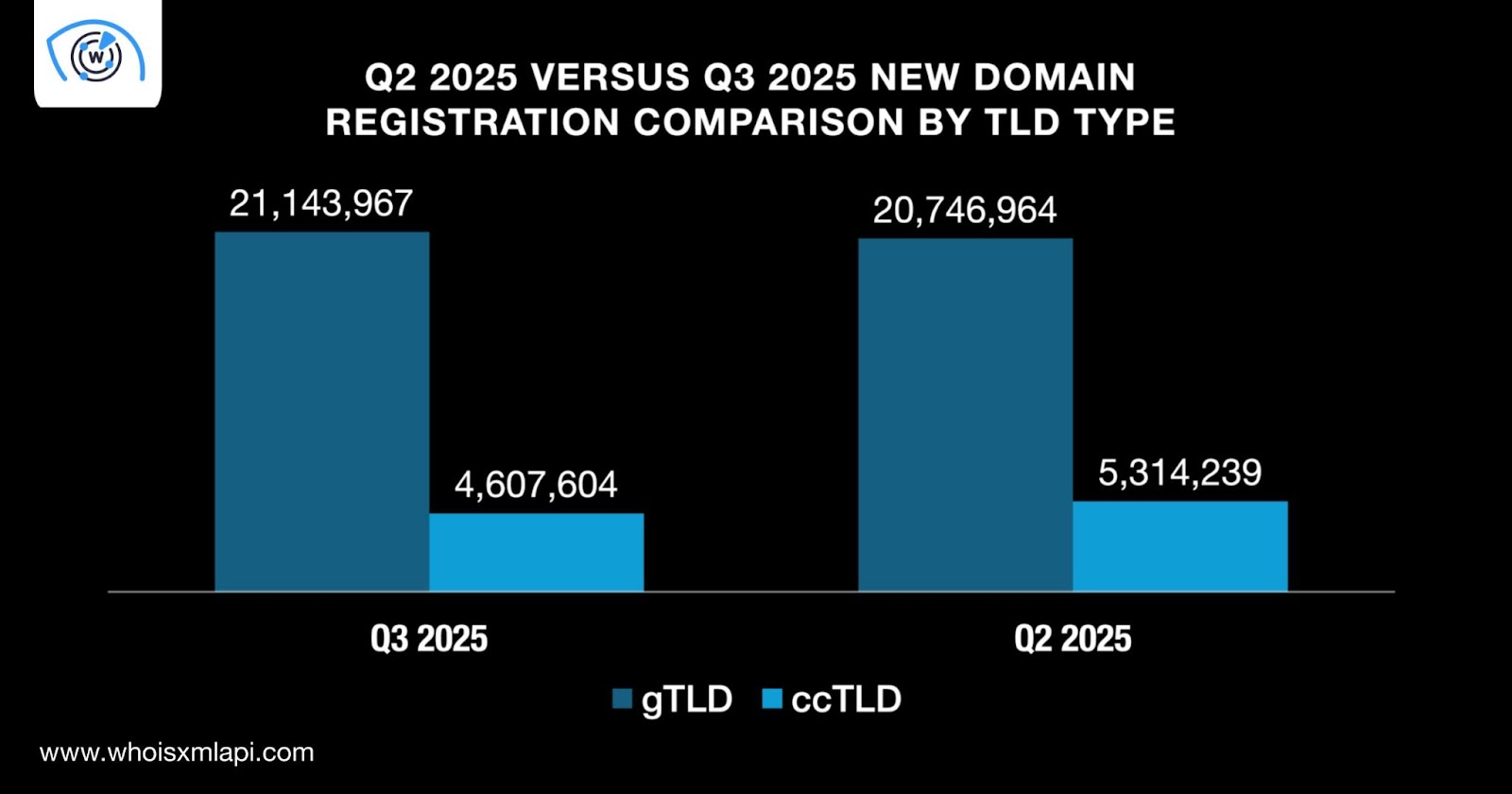
WhoisXML API’s Global Domain Activity Report: Q3 2025 analyzed 25.7+ million newly registered domains and found a 1.2% quarter-over-quarter decrease, while identifying 3.2+ million domains tagged as indicators of compromise and extensive MX/NS resolution data. The report highlights dominant TLDs and registrars (.com, .cn, GoDaddy, Namecheap) and unusual ccTLD activity such as the .cc volume-to-population incongruence. #GoDaddy #Namecheap
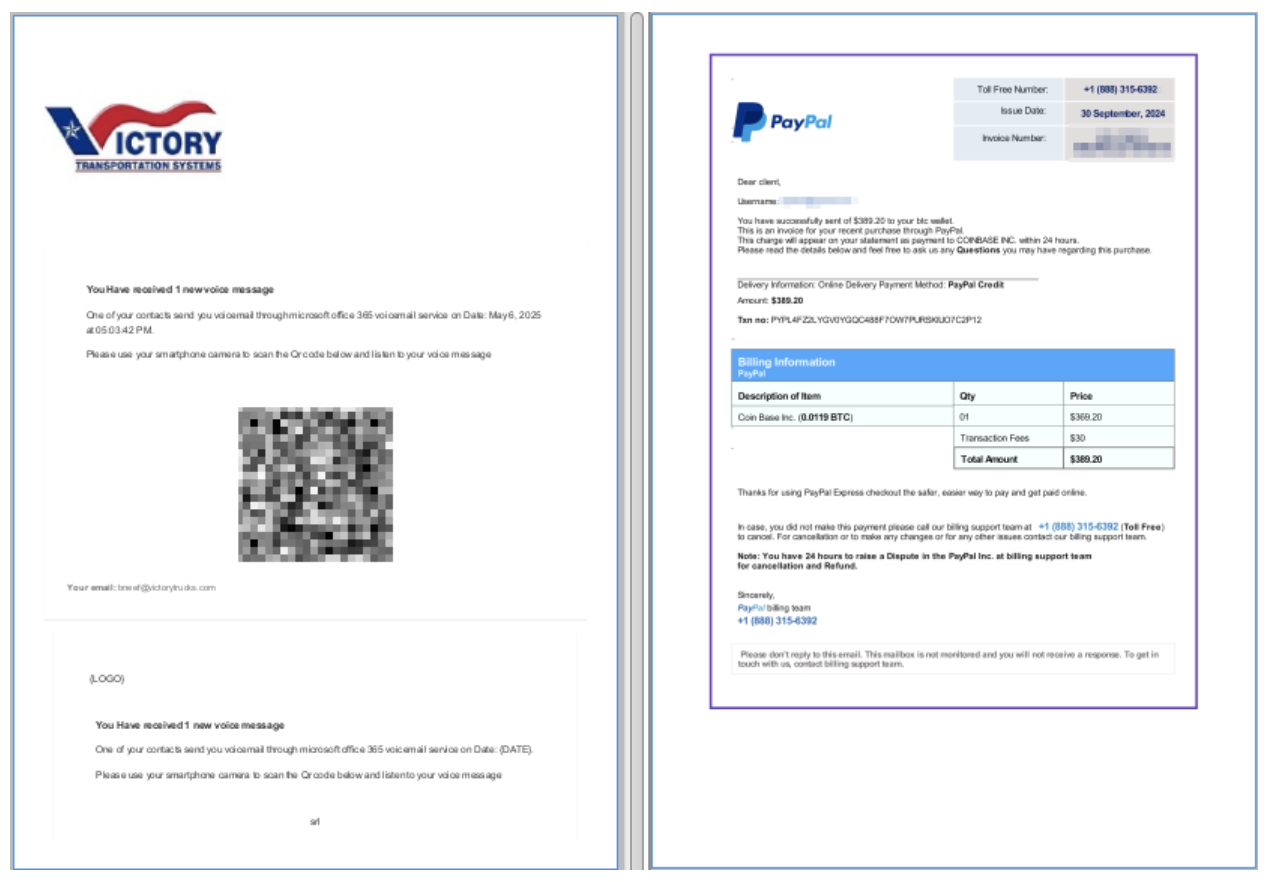
Proofpoint released an open-source tool called PDF Object Hashing to create detection rules that fingerprint PDFs by their internal object structure, enabling detection and clustering even when PDFs are obfuscated, encrypted, or have changing lure content. The technique has been used internally to track multiple threat actors including UAC-0050 and UNK_ArmyDrive…
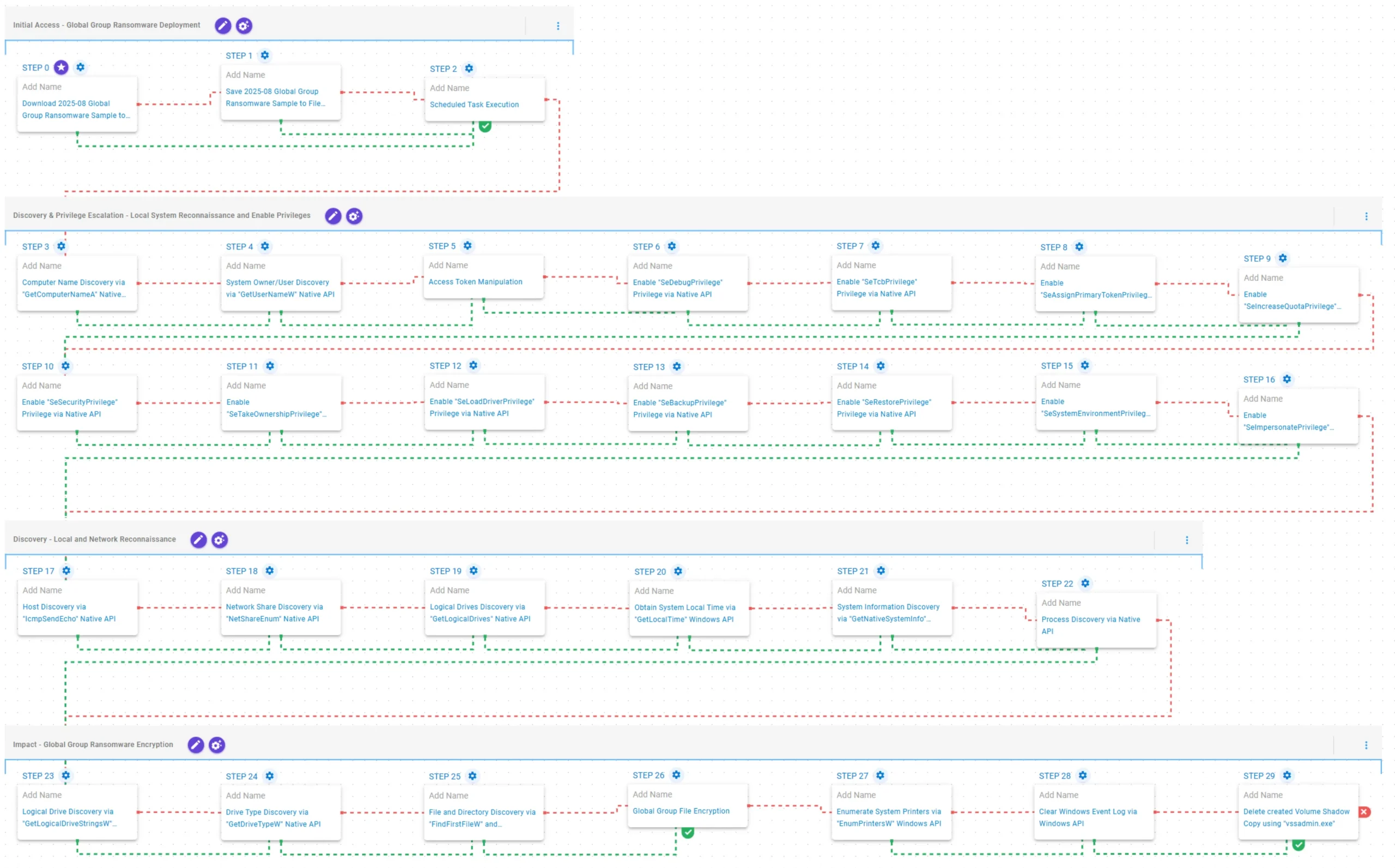
Global Group is a Ransomware-as-a-Service (RaaS) operation that surfaced in June 2025, offering cross-platform Go-based payloads, affiliate-friendly features (including AI-assisted extortion), and reuse of code and infrastructure linked to Mamona and BlackLock. AttackIQ published an emulation/attack graph to help organizations validate detection and prevention controls against Global Group behaviors. #GlobalGroup #Mamona…
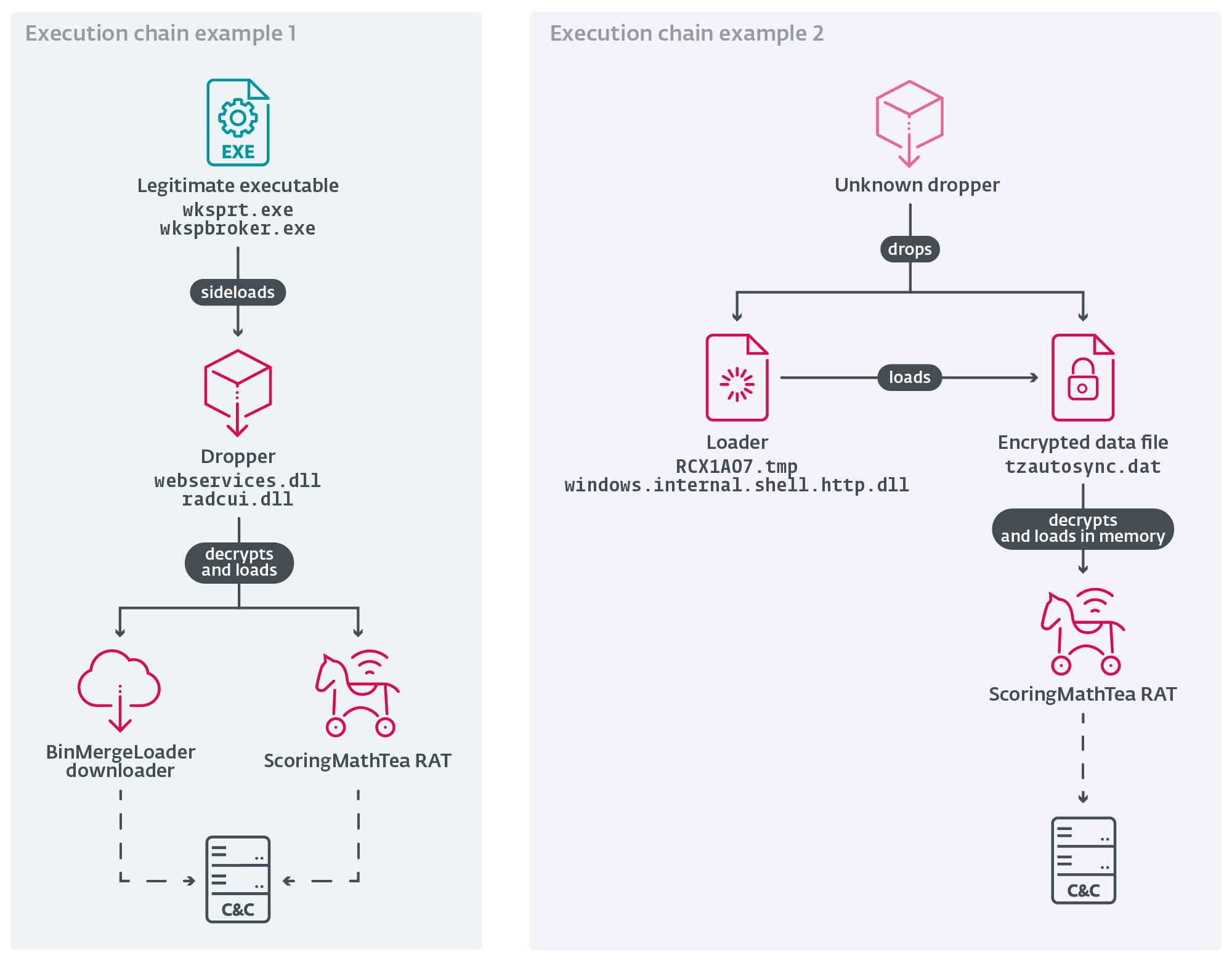
ESET observed a new wave of Operation DreamJob attributed to Lazarus targeting European defense and UAV-related companies using trojanized open-source projects and the ScoringMathTea RAT to steal proprietary information and manufacturing know-how. The campaign used DLL side-loading, reflective loading, and compromised WordPress sites for C2 infrastructure, suggesting a link to North Korea’s effort to scale up its drone program. #ScoringMathTea #Lazarus
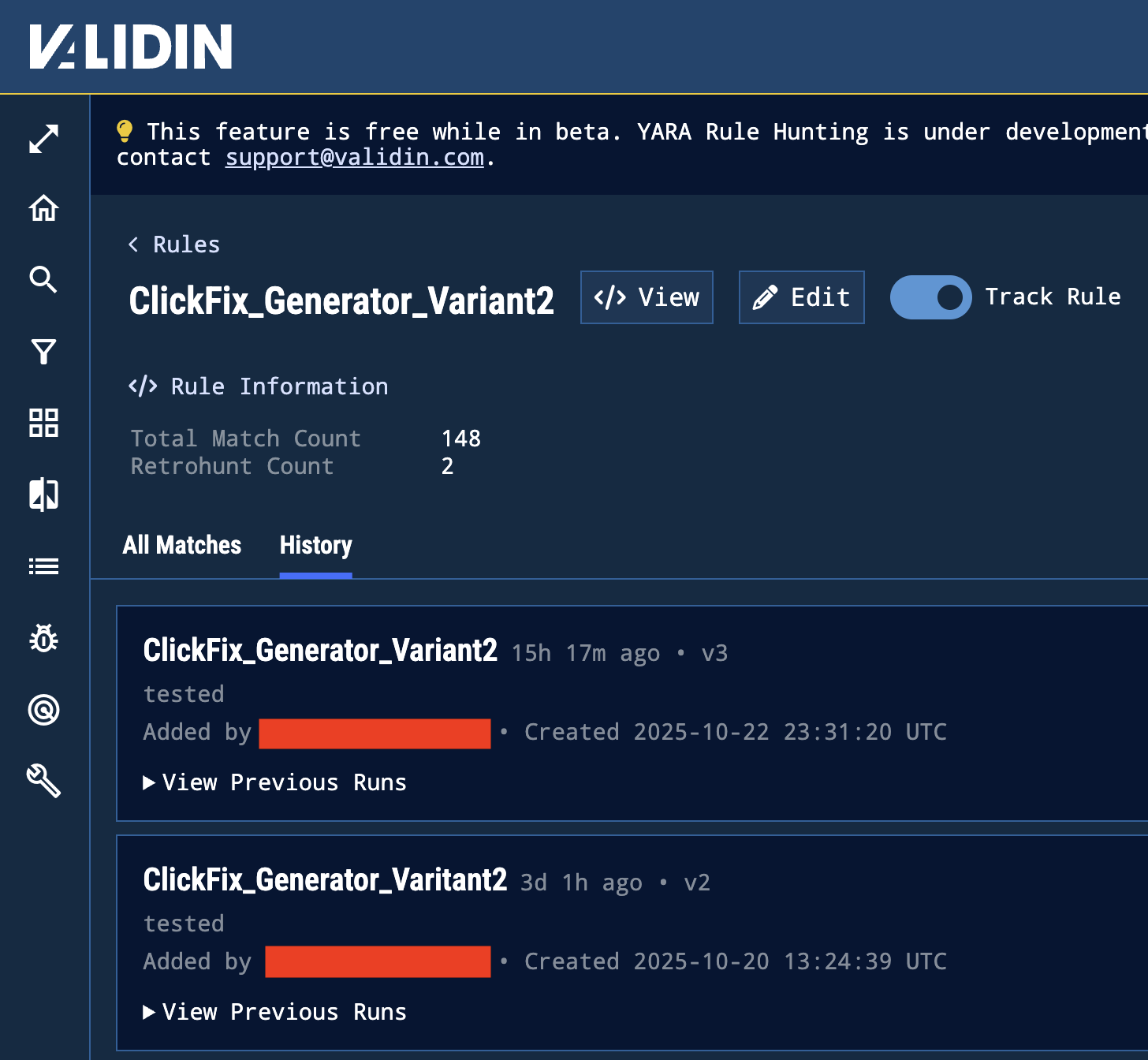
Validin has extended its YARA-X integration to run YARA rules continuously on live host response data, enabling timestamped, contextual detections across a dataset of over 850 million daily host responses. New features include a YARA playground, rule versioning, Projects for collaborative investigations, and demonstrated detections of ClickFix-related HTML and JavaScript injections. #ClickFix #IUAM
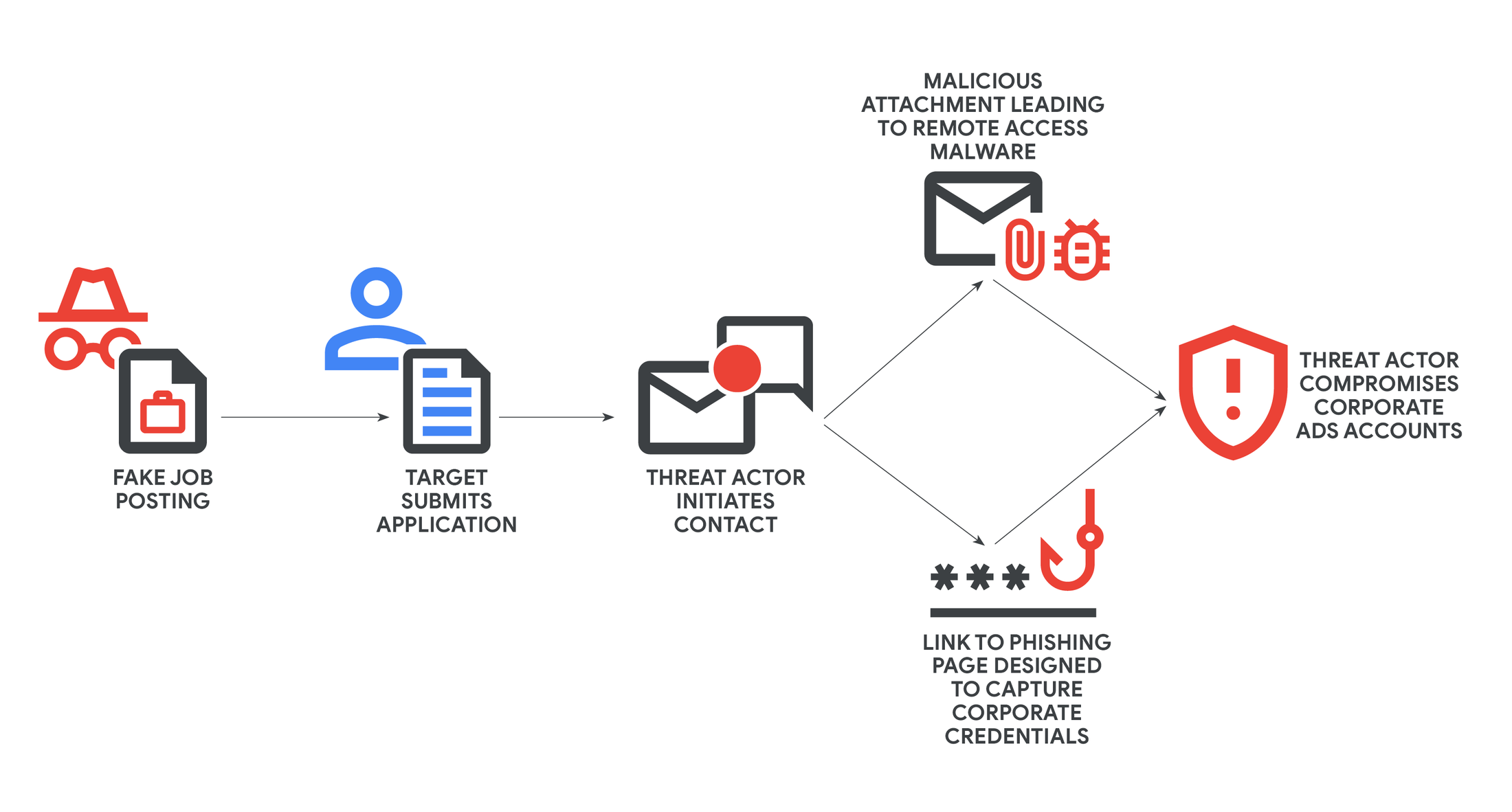
GTIG tracked a Vietnam-based cluster UNC6229 that uses fake job postings on legitimate platforms and abused CRM/SaaS services to socially engineer digital advertising workers into downloading RATs or entering credentials on phishing pages to steal corporate ad/social accounts. The campaign leverages personalized follow-ups, password-protected attachments, and convincing phishing kits (including MFA-capable pages) to monetize access by selling ad inventory or compromised accounts. #UNC6229 #staffvirtual.website

This article describes tools and a process to query the Azure WireServer from a compromised VM to retrieve and decrypt VM extension “Protected Settings” without directly reading local encrypted files. It provides PowerShell and Bash scripts (MicroBurst) that request goal state, fetch extension configs and certificate bundles, decrypt them using generated transport certificates, and extract sensitive settings for assessment and pivoting. #WireServer #Get-AzureVMExtensionSettingsWireServer
