Privileged access is the primary pathway attackers use to achieve high-impact compromises, and protecting both human and non-human privileged identities across on-premises and cloud environments is essential. Mandiant recommends a defense-in-depth PAM strategy—tiering, least privilege, PAWs, MFA, secrets management, detection (high-fidelity session telemetry and anomaly analytics), and practiced response including coordinated credential rotation—to reduce dwell time and blast radius. #Mandiant #GoogleSecOps
Category: Threat Research

Agentic AI is emerging as a transformative layer in cybersecurity, enabling autonomous detection, decision-making, and action to drastically reduce response times and shift humans into oversight and strategy roles. The META region faces rising, AI-augmented threats and operational urgency, prompting industry discussions like Cyble’s webinar on Oct 29, 2025 to explore responsible adoption. #AgenticAI #Cyble

Digital risk management (DRM) expands protection beyond traditional network defenses to cover brand reputation, supply chains, cloud/SaaS assets, and third-party integrations using intelligence, automation, and continuous monitoring. Recorded Future combines threat, digital risk, and third-party intelligence to give enterprises unified visibility and automated response capabilities for faster detection and remediation. #RecordedFuture #BrandImpersonation

Beast ransomware, evolved from the Monster strain, began RaaS operations in February 2025 and has publicly disclosed 16 victims across multiple regions and industries while actively distributing via SMB scanning, phishing, and Vidar-assisted campaigns. The malware uses ChaCha20-based hybrid encryption, country-based execution filtering, persistence, shadow copy deletion, process/service termination, and a…
AI-powered web builders enable criminals to create convincing phishing and scam sites (VibeScams) from simple prompts or screenshots, dramatically lowering the technical barrier and accelerating brand impersonation across many platforms. Researchers blocked roughly 140,000 AI-generated malicious sites (about 580 per day) between early 2025 and August 2025, affecting users worldwide including the U.S., France, Brazil, Germany, and Japan. #VibeScams #Coinbase
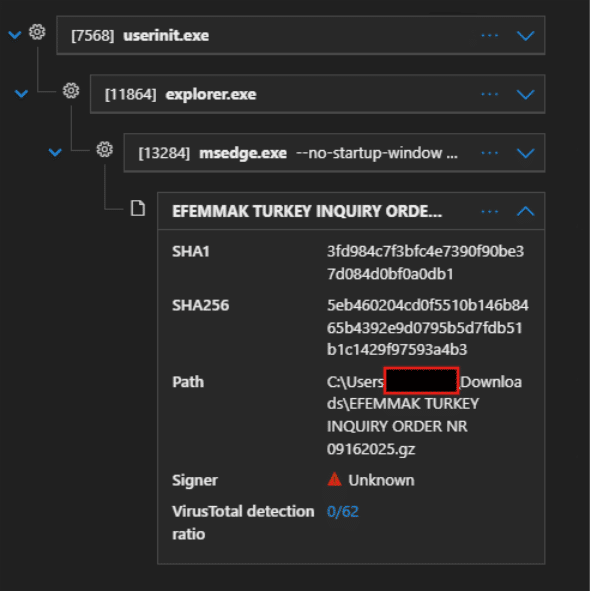
CyberProof observed a surge in a Remcos infostealer campaign in Sep–Oct 2025 that used malicious email attachments, obfuscated PowerShell, and process hollowing of msiexec into RMClient.exe to deploy Remcos and harvest browser-stored credentials. The operation used compromised or malicious domains (e.g., icebergtbilisi.ge) to host payloads and employed continuous download-and-execute loops to ensure delivery. #Remcos #icebergtbilisi.ge
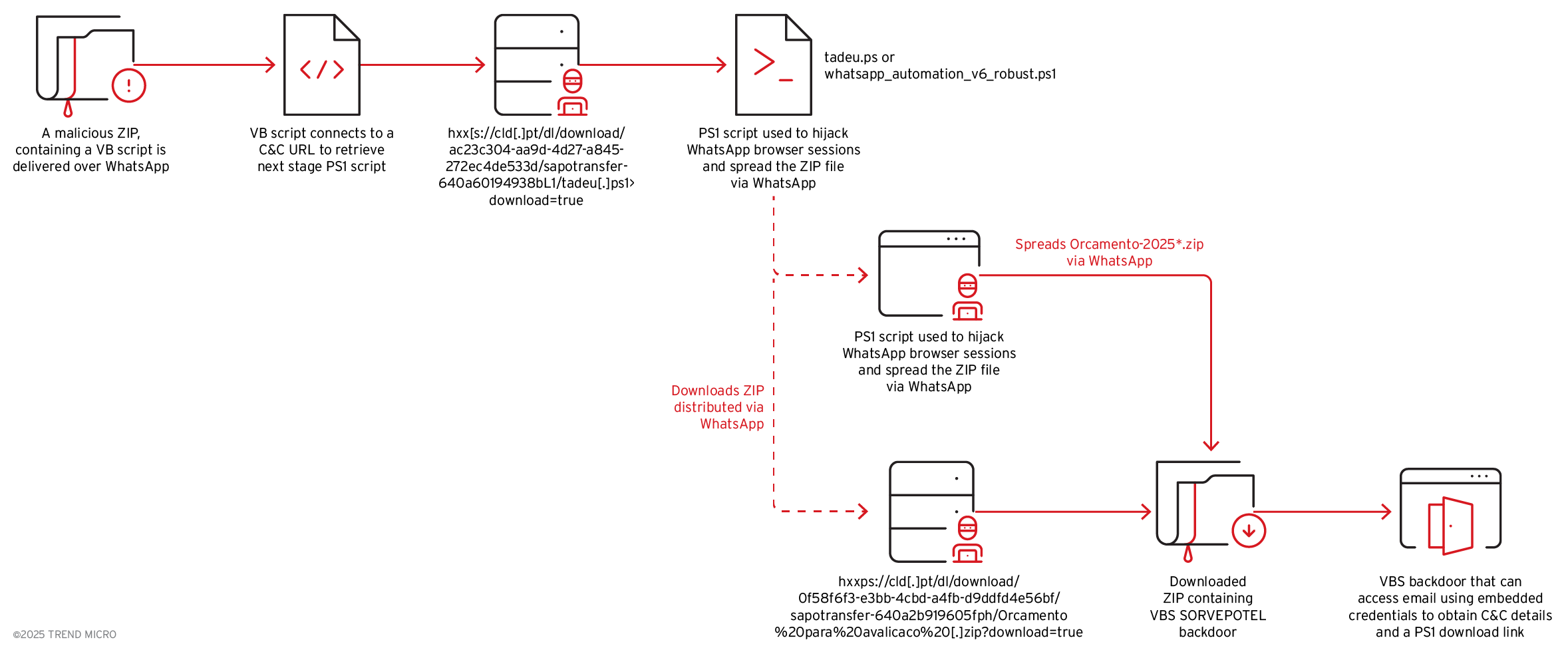
Trend Research uncovered an evolved Water Saci campaign that uses WhatsApp Web to deliver malicious ZIPs containing an obfuscated VBS downloader which launches a fileless PowerShell payload that hijacks browser sessions, harvests contacts, and self-propagates. The campaign pairs a dual-channel C2 infrastructure (email/IMAP to retrieve C2 URLs and aggressive HTTP polling)…

Trigona threat actors continue targeting exposed or weakly protected MS‑SQL servers, using BCP to store and export malware from databases and employing tools like AnyDesk, RDP, Teramind, Rust scanners, and various downloaders. ASEC observed reused Trigona infrastructure and provided IoCs including file hashes, URLs, and IPs for the 2024 campaign. #Trigona…
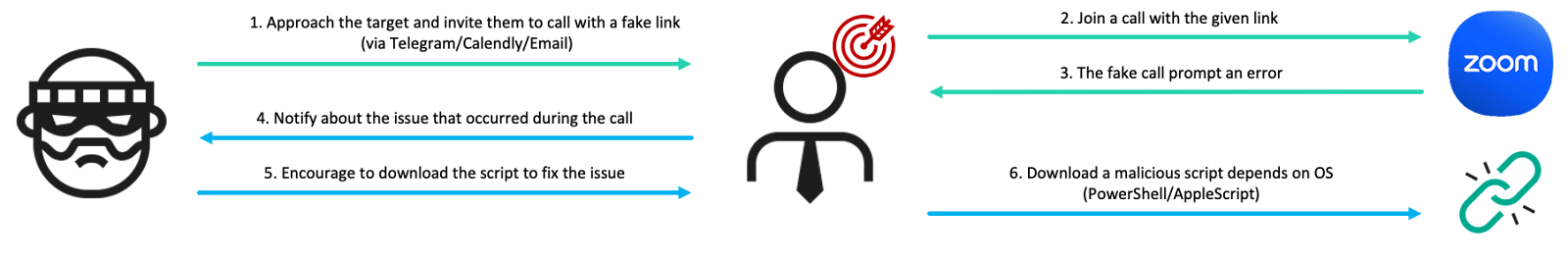
BlueNoroff’s SnatchCrypto operation runs two linked campaigns — GhostCall and GhostHire — that use sophisticated social engineering (fake Zoom/Teams calls and fake recruiter assessments) to deliver multi-stage malware chains targeting Web3/blockchain executives and developers. The actor reuses recordings of real victims, leverages Telegram and GitHub for delivery, and deploys modular implants like DownTroy, ZoomClutch/TeamsClutch, CosmicDoor, RooTroy, SneakMain, and SysPhon while employing AI to refine lures and tooling. #BlueNoroff #DownTroy

A critical unauthenticated RCE vulnerability in Windows Server Update Services (CVE-2025-59287) was actively exploited in the wild shortly after Microsoft released an emergency patch on Oct. 23, 2025, prompting CISA to add it to the KEV catalog. Unit 42 observed exploitation chains leveraging unsafe deserialization via GetCookie() and ReportingWebService endpoints, with…
APT-C-60 intensified operations against Japanese organizations in Q3 2025, deploying SpyGlace backdoor versions 3.1.12–3.1.14 with refined delivery (direct VHDX attachments), enhanced evasion, and sophisticated abuse of GitHub, StatCounter, and Git for stealthy payload distribution. #APT-C-60 #SpyGlace #GitHub #StatCounter

Atroposia is a modular remote access trojan (RAT) that provides hidden RDP, encrypted C2 channels, credential and cryptocurrency wallet theft, DNS hijacking, local vulnerability scanning, and multiple persistence/evasion mechanisms. It is marketed on underground forums alongside turnkey criminal toolkits like SpamGPT and MatrixPDF, lowering the skill required to run complex attacks….

Wiz uses its own platform to continuously secure its cloud environment and to support SOC 2 Type 2 compliance, covering 26% of required controls with the strongest overlap in the Security trust principle. The platform’s capabilities—Mika AI, Graph Search, Inventory, Compliance Frameworks, and reporting—streamline GRC workflows, automate evidence collection, and speed audits. #Wiz #MikaAI

Monitoring TOR exit node activity helps detect anonymized reconnaissance, C2 communications, and data exfiltration that leverage TOR to hide attackers’ origins, and organizations can ingest TOR node data into Elastic via an ingest pipeline, index template, and Elastic-Agent or Filebeat integration. The guide provides step-by-step configuration (API request, ingest pipeline, index template, and agent policy) to surface TOR node activity for detection and correlation with Threat Intel rules. #TOR #Onionoo

Ransomware has grown in scale and sophistication, with exploited vulnerabilities and AI-assisted campaigns driving more frequent and impactful incidents, making traditional reactive defenses insufficient. Proactive, entity-centric threat intelligence—powered by AI/ML, dark-web monitoring, and automated remediation—enables organizations to anticipate, prioritize, and prevent ransomware attacks. #LockBit #RecordedFuture
