October saw rapid evolution of phishing and ransomware campaigns that increasingly abused legitimate cloud services (Figma, ClickUp, Salesforce, Azure Blob Storage) and layered CAPTCHAs and redirects to evade detection, with new toolsets like TyKit and LockBit 5.0 expanding impact to Microsoft 365 accounts, ESXi, and Linux systems. #TyKit #LockBit5 #Figma #ClickUp #satoshicommands
Keypoints
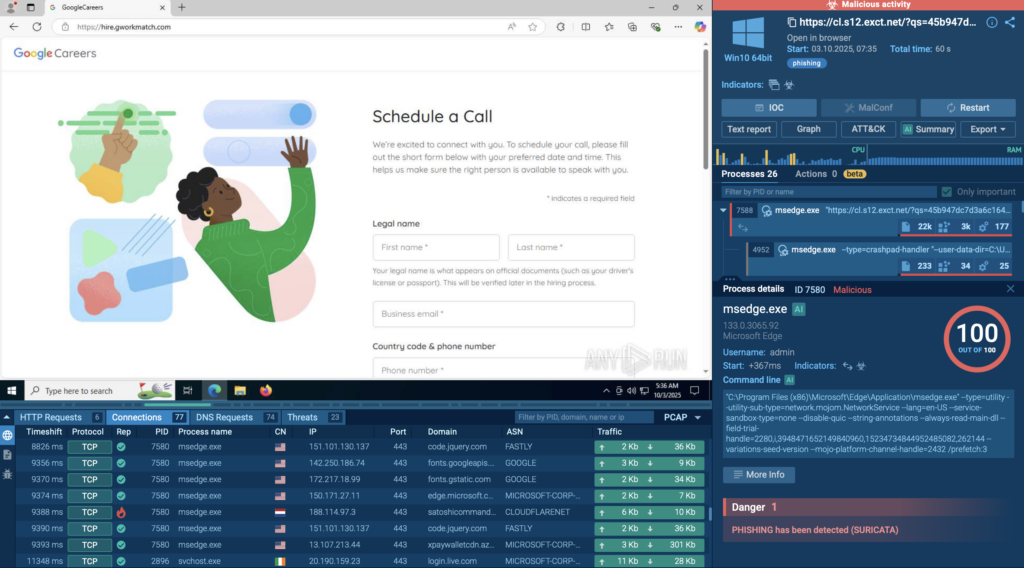
- Phishing campaigns used legitimate platforms (Google Careers lookalike, Salesforce redirects, Cloudflare Turnstile) to harvest corporate credentials and exfiltrate them to C2 domains such as satoshicommands[.]com.
- Attackers abused Figma public prototypes to host Microsoft-themed phishing pages, with major actors like Storm-1747 and Mamba leveraging figma.com to bypass URL reputation checks.
- LockBit 5.0 introduced ESXi and Linux encryptors alongside enhanced obfuscation and anti-analysis techniques, enabling large-scale disruption of virtualized infrastructure and data centers.
- ClickUp was used as a redirector in multi-step phishing chains that hop through Microsoft microdomains and Azure Blob Storage to deliver credential-harvesting pages.
- TyKit (Tykit) is a reusable phishing kit that hides JavaScript inside SVG files to perform staged redirects, CAPTCHA checks, and POST-based exfiltration of Microsoft 365 credentials.
- ANY.RUN’s Interactive Sandbox revealed full execution chains and behavioral indicators (redirect flows, POST endpoints, anti-debugging) that static tools miss, enabling SOCs to build behavior-based detections.
- Recommendations include inspecting SVGs in sandboxes, enforcing phishing-resistant MFA (FIDO2), restricting ESXi access, maintaining offline backups, and combining endpoint/network telemetry for behavior-based monitoring.
MITRE Techniques
- [T1192] Spearphishing Link – Phishing emails containing links to legitimate-hosted pages (e.g., Figma, ClickUp) that lead to credential-harvesting pages (“Phishing email invites the victim to view a ‘shared document.’”).
- [T1566.002] Phishing: Link – Use of cloud-hosted redirect chains and public prototypes to deliver credential stealing pages (“Figma prototype hosts a fake collaboration page within the figma.com domain.”).
- [T1193] Spearphishing Attachment – Malicious SVG files containing obfuscated JavaScript used by TyKit to rebuild payloads and trigger redirects (“SVG delivery → Obfuscated JS rebuilds payload and triggers redirect (eval, atob, charCodeAt patterns).”).
- [T1204.002] User Execution: Malicious Link – Victims interact with legitimate-looking links and buttons (Cloudflare Turnstile/CAPTCHA widgets) that proceed the phishing flow (“Embedded link triggers a fake CAPTCHA or Cloudflare Turnstile widget.”).
- [T1071.001] Application Layer Protocol: Web Protocols – Credential exfiltration via HTTP POSTs to attacker-controlled collectors and C2 endpoints (“/api/login sends {key, redierct, token, server, email, password}”).
- [T1490] Inhibit System Recovery – LockBit 5.0 behavior includes deleting shadow copies and wiping disks to prevent recovery (“performs cleanup actions like deleting shadow copies, stopping critical services, and clearing event logs.”).
- [T1486] Data Encrypted for Impact – LockBit 5.0 encryptors for Windows, Linux, and ESXi that encrypt drives and hypervisor datastores to cause outages (“dedicated encryptor for hypervisors capable of disabling multiple virtual machines at once.”).
- [T1027] Obfuscated Files or Information – LockBit 5.0 and TyKit use obfuscation and anti-analysis techniques to evade detection (“stronger obfuscation, flexible configuration files, and enhanced anti-analysis techniques”; “staged C2 checks, basic anti-debugging”).
Indicators of Compromise
- [IP Address] Google-like phishing C2/hosts – 188[.]114[.]97[.]3, 104[.]21[.]62[.]195
- [Domain] Credential exfiltration C2 and phishing domains – satoshicommands[.]com, hire[.]gworkmatch[.]com
- [Domain] Figma/Microsoft-related hosting or redirect domains – figma.com (abused prototypes), dataartnepal[.]com
- [Hash] Malicious file hashes (SVGs) – 9a4c7dcf25e95906…3c4bb2c, and 2 more hashes (ECD3C8…2CC8, A7184B…1892)
- [URL/Endpoint] Microsoft Forms / ClickUp redirect examples – https[:]//forms[.]office[.]com/e/YtRCbHDk14; doc[.]clickup[.]com redirects
- [Domain Pattern] TyKit-related domains and patterns – segy[.]zip / segy[.]xyz / segy[.]cc (segy* family), ^loginmicr(o|0)s.*?.([a-z]+)?d+.cc$
- [Storage Host] Azure Blob Storage hosting used for final pages – microlambda[.]blob[.]core[.]windows[.]net (example), and *.blob.core.windows.net patterns
- [HTTP Requests] Exfiltration endpoints and request patterns – POST /api/validate, POST /api/login, POST /x.php, GET /?s=
Read more: https://any.run/cybersecurity-blog/cybersecurity-blog/cyber-attacks-october-2025/