Check Point Research demonstrated that cloud-based static analysis with ChatGPT (using exported IDA data) combined with occasional MCP-assisted runtime checks can drastically accelerate reverse engineering of heavily obfuscated XLoader 8.0, enabling rapid recovery of keys, decrypted functions, strings, and C2 domains. The workflow reduced many manual steps (triage, deobfuscation, scripting, validation) from days to hours while still requiring targeted human adjustments for scattered key derivation and sample-specific quirks. #XLoader #RC4 #ChatGPT
Category: Threat Research
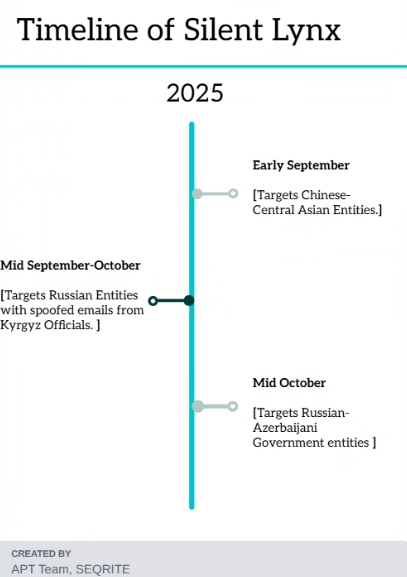
Silent Lynx conducted spear-phishing campaigns using malicious RAR archives and LNK shortcuts to deploy multiple implants (PowerShell reverse shells, C++ Laplas, C++/TLS variants, .NET SilentSweeper) targeting diplomatic and infrastructure-related entities in Central Asia, Russia, Azerbaijan, and China. Infrastructure includes GitHub-hosted Base64 blobs, C2s at 206.189.11.142 and Russian hosts, and use of tunneling tools like Ligolo-ng. #SilentLynx #SilentSweeper

SentinelLABS researchers detail the rise of LLM-enabled malware that embeds Large Language Model capabilities into malicious payloads, producing code at runtime and evading traditional static detection. Their retrohunt found thousands of samples and unique API keys, and they propose hunting for hardcoded provider API keys and prompt structures as effective detection techniques. #PromptLock #LameHug
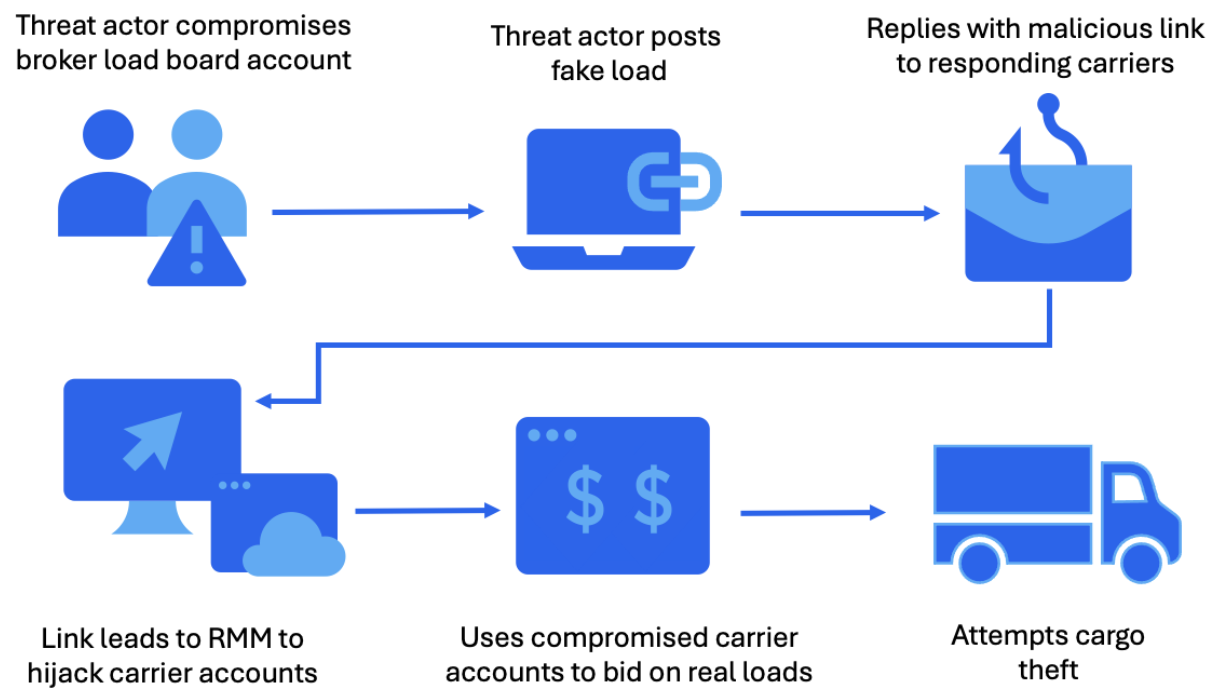
Proofpoint researchers observed a cluster of cybercriminals compromising trucking and freight companies to deliver remote monitoring and management (RMM) tools and remotely access systems to fraudulently bid on and steal cargo. The campaigns used compromised load board accounts, email thread hijacking, and direct email targeting, leveraging RMMs such as ScreenConnect, SimpleHelp,…

Midnight is a new ransomware strain derived from Babuk that uses ChaCha20 for file encryption and RSA to protect the ChaCha20 key, while employing intermittent encryption and file-extension/appended-content behaviors. Weaknesses in Midnight’s cryptographic implementation enabled researchers to produce a working decryptor and provide recovery guidance. #Midnight #Babuk

Check Point Research discovered multiple vulnerabilities in Windows GDI related to EMF+ metafile processing that could allow out-of-bounds reads/writes and information disclosure, and reported them to Microsoft, which issued fixes in the May, July, and August 2025 Patch Tuesday updates. #CVE-2025-30388 #CVE-2025-53766 #CVE-2025-47984

Datadog observed a rise in supply-chain and developer-tooling attacks in Q3 2025, including widespread npm account compromises via phishing and a self-replicating npm worm (Shai-Hulud) that exfiltrated GitHub tokens and propagated across packages. The report also highlights malicious VS Code extensions, AI-assisted malware (e.g., LameHug) using external LLM APIs, and persistent risks from long-lived cloud credentials and fraudulent deepfake job profiles. #Shai-Hulud #S1ngularity
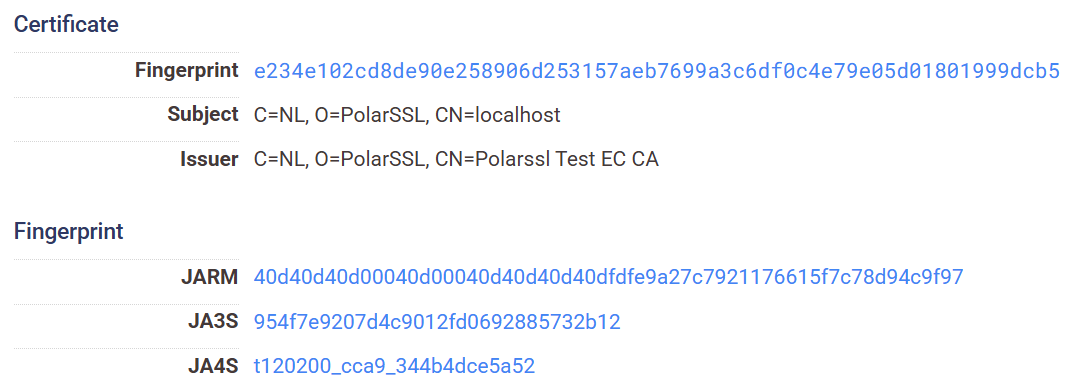
XLab discovered RPX_Client, a previously undocumented PolarEdge relay component that onboards compromised IoT/edge devices into a proxy pool and enables remote command execution, linked to download infrastructure at 111.119.223.196 and corroborated by homology with known PolarEdge samples. The investigation identified 140 RPX_Server VPS nodes (port 55555) and over 25,000 infected devices across 40 countries, revealing an ORB network used for long-term stealth and traffic obfuscation. #PolarEdge #RPX_Client

In October 2025, CRIL discovered a multi-stage backdoor campaign using a weaponized ZIP masquerading as a Belarusian military PDF that used nested archives, LNK-triggered PowerShell, scheduled tasks, and a Tor hidden-service with obfs4 to provide anonymous SSH/RDP/SFTP/SMB access. The TTPs and infrastructure show similarities to the December 2024 Army+ campaign attributed to Sandworm (UAC-0125/APT44), including pre-generated RSA keys and OpenSSH for Windows deployment. #Sandworm #obfs4
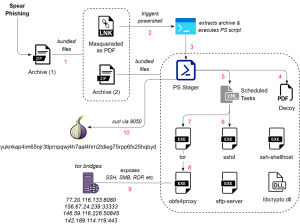
SEQRITE Labs identified a campaign called SkyCloak targeting Russian and Belarusian military personnel that uses spearphishing LNKs to execute PowerShell stages which deploy OpenSSH and Tor (with obfs4 bridges) to expose local services via onion addresses. The chain uses scheduled tasks for persistence, bundles legitimate OpenSSH/OpenSSL binaries for a stealthy SSH/SFTP server, and registers victims to yuknkap4im65njr3tlprnpqwj4h7aal4hrn2tdieg75rpp6fx25hqbyd.onion. #SkyCloak #yuknkap4im65njr3tlprnpqwj4h7aal4hrn2tdieg75rpp6fx25hqbyd.onion

Adversaries used stolen AWS credentials to run large-scale credential testing and cloud reconnaissance via an infrastructure named TruffleNet, leveraging TruffleHog and automated AWS API calls to identify valid accounts and probe SES sending capabilities. Compromised accounts were then used to create verified email identities and conduct Business Email Compromise campaigns, including a $50,000 W-9 invoice scam that used domains like cfp-impactaction[.]com. #TruffleNet #TruffleHog #cfp-impactaction[.]com
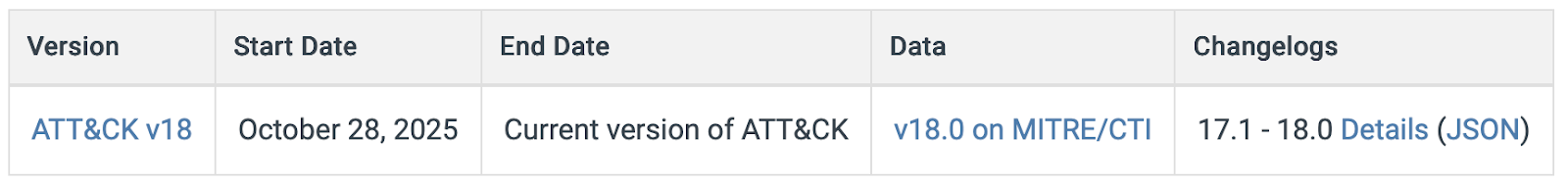
MITRE ATT&CK v18.0 replaces legacy Detections and Data Sources with a behavior-driven two-tier model of Detection Strategies and Analytics, improving telemetry mapping and cross-tactic correlation to better reflect real-world adversary behavior. The release adds 12 new techniques across Enterprise, Mobile, and ICS and signals future tactic reorganization and expanded coverage while vendors like Picus Security map tests and detections to the new model. #DET0525 #AN0850

A series of coordinated supply chain attacks (s1ngularity, Qix compromise, and Shai-Hulud) abused GitHub Actions and long-lived tokens to publish malicious npm packages and exfiltrate secrets, exposing thousands of repositories and leaking over 2,000 unique secrets. The incidents highlight phishing, unrotated credentials, and CI/CD workflow weaknesses as root causes and prompted mitigations like token rotation, GitHub hardening, and tools such as GuardDog and Supply-Chain Firewall. #s1ngularity #Shai-Hulud

Threat Labs discovered two DPRK-linked campaigns: Kimsuky deployed a multi-stage chain ending in an obfuscated HttpTroy HTTP-based backdoor, while Lazarus used new Comebacker variants to deliver an upgraded BLINDINGCAN RAT with enhanced cryptography. Both campaigns use layered obfuscation, dynamic API resolution, and stealthy persistence mechanisms like scheduled tasks and services. #HttpTroy #BLINDINGCAN
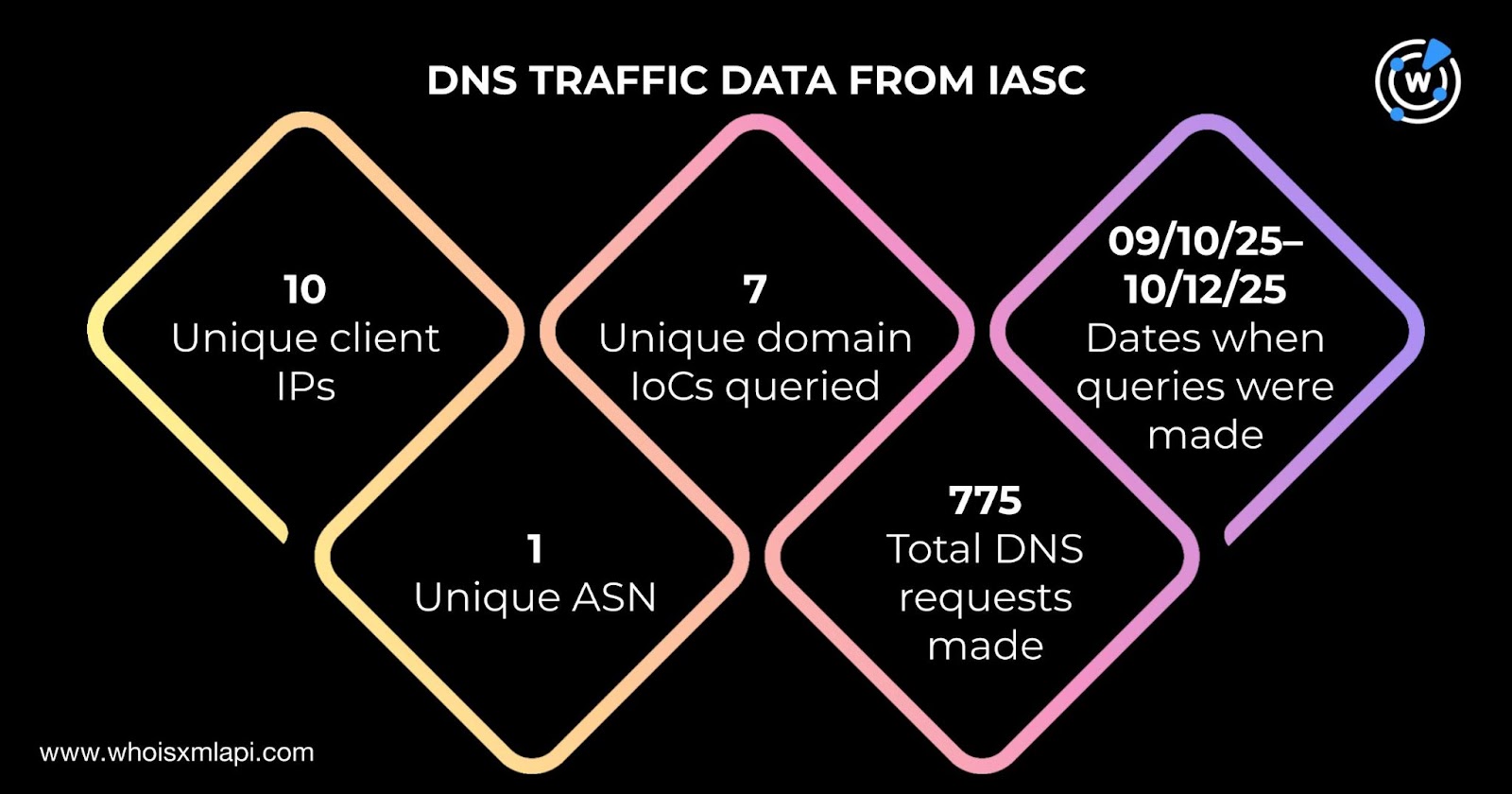
Threat actors used malicious SVG image attachments in phishing emails to gain remote control of victims’ devices, collect sensitive information, and deliver additional malware, with FortiGuard Labs identifying 26 IoCs (25 domains and one IP). Investigations revealed domain registration and resolution patterns, connections to multiple IPs and email-linked domains, and early detection indicators from threat feeds and WHOIS/DNS data. #ms-team-ping2[.]com #109.176.207.110
