Silent Lynx conducted spear-phishing campaigns using malicious RAR archives and LNK shortcuts to deploy multiple implants (PowerShell reverse shells, C++ Laplas, C++/TLS variants, .NET SilentSweeper) targeting diplomatic and infrastructure-related entities in Central Asia, Russia, Azerbaijan, and China. Infrastructure includes GitHub-hosted Base64 blobs, C2s at 206.189.11.142 and Russian hosts, and use of tunneling tools like Ligolo-ng. #SilentLynx #SilentSweeper
Keypoints
- Silent Lynx used spear-phishing with malicious RAR archives and LNK shortcuts to deliver loaders and stagers aimed at diplomatic targets involved in summits (Dushanbe, Astana) and infrastructure projects.
- Multiple implant types were observed: PowerShell Base64 reverse shells, C++ loaders (Silent Loader), C++ Laplas (TCP and TLS variants), and .NET implant SilentSweeper that extracts and runs embedded PowerShell.
- Final-stage payloads frequently downloaded Base64-encoded PowerShell from a GitHub repo (GoBuster777) and connected back to C2 (notably 206.189.11.142:443); Ligolo-ng was used for tunneling/proxying.
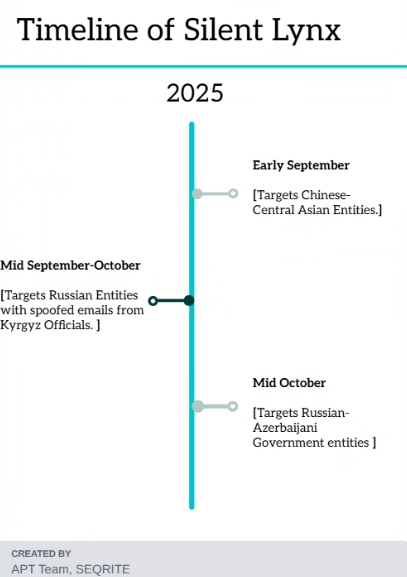
- Campaigns targeted government think-tanks, diplomats, mining, and transport & communications sectors across Tajikistan, Azerbaijan, Russia, China, and other Central-Asian nations.
- Hunting pivots included LNK metadata (Desktop path with user GoBus), GitHub-hosted blobs, and multiple malicious archives (RAR/ZIP) that revealed further campaigns and infrastructure.
- Attribution to Silent Lynx is based on repeated TTPs: Base64-encoded scripts, similar loader code, reuse of tunneling tools, and consistent victimology focused on Central Asia and related diplomatic events.
- IOCs include many file hashes, domains (updates-check-microsoft[.]ddns[.]net, catalog-update-update-microsoft[.]serveftp[.]com), and IPs (206.189.11.142, 62.113.66.137, 62.113.66.7, 37.18.27.27) used for C2 and hosting.
MITRE Techniques
- [T1566.001 ] Spearphishing Attachment – Malicious RAR archives sent as spear-phishing attachments to deliver LNK and executable stagers (“malicious RAR archive known as План развитие стратегического сотрудничества.pdf.rar”).
- [T1204.001 ] User Execution: Malicious Link – LNK shortcuts executed by victims to launch PowerShell and download remote scripts (“the RAR file contained a malicious LNK … abuse the powershell.exe binary to download and execute a malicious PowerShell file”).
- [T1204.002 ] User Execution: Malicious File – Victims executed delivered malicious executables and scripts (silent_loader.exe, laplas.exe, SilentSweeper .NET executable) that spawn processes to run payloads (“silent_loader.exe … passes the command line as an argument to CreateProcessW API”).
- [T1106 ] Native API (CreateProcess / CreateProcessW) – Loaders used CreateProcessW/CreateProcess to launch PowerShell or cmd.exe from decoded strings (“passed as a parameter to CreateProcess API”; “CreateProcessW API”).
- [T1053.005 ] Scheduled Task/Job: Windows Task Scheduler – Attackers created a scheduled task named WindowsUpdate to achieve persistence, running downloaded scripts every six minutes (“creates a scheduled task called WindowsUpdate … /sc minute /mo 6”).
- [T1059.001 ] PowerShell – PowerShell scripts and Base64-encoded blobs used to implement reverse shells and payload execution (“Base64 encoded malicious blob executed via powershell … downloads two helper scripts … WindowsUpdateService.ps1”).
- [T1027 ] Obfuscated Files or Information – Use of Base64-encoded blobs and encoded script payloads to hide final-stage behavior (“usage of Base64 encoded malicious blob executed via powershell”; “contains an encoded blob, which further upon decoding … resembles the exact final-stager reverse-shell”).
- [T1036 ] Masquerading – Filenames and task names mimicked legitimate items (Plan for the Development of Strategic Cooperation PDF, WindowsUpdate task) to blend with legitimate content (“Plan … .pdf.rar”; “scheduled task called WindowsUpdate”).
- [T1071 ] Application Layer Protocol (HTTPS / Web protocols) – Downloading payloads from GitHub and hosting domains over HTTP/HTTPS to stage components (“PowerShell file from a GitHub Repository known as GoBuster777”; C2 and hosting URLs listed).
- [T1095 ] Non-Application Layer Protocol (raw TCP / custom C2) – Custom TCP-based reverse shells connected directly to C2 ports (Laplas TCP reverse shell to port 443) (“quick TCP-based reverse shell that connects to 206.189.11.142:443”; “./laplas.exe “).
- [T1071 / T109 ] Tunneling / Proxy (use of Ligolo-ng) – Use of Ligolo-ng for tunnelled connectivity and proxying to reach internal networks and relay command and control (“threat actor also deployed the open-source tunneler Ligolo-ng alongside the PowerShell-based reverse shell”).
- [T1041 / T1071 ] Exfiltration over C2 channel / Application layer – Use of established C2 channels (reverse shells and tunneled sessions) to send command outputs and potentially exfiltrate data (“reads text commands … executes them … writes the output back over the same connection”; exfiltration over C2 mentioned).
Indicators of Compromise
- [File Hash ] Malicious archives & payloads – ef627bad8…8374 (RAR Plan_for_the_Development_of_Strategic_Cooperation.pdf.rar), 5b58133d…4639 (China-Central Asia SummitProject.rar).
- [File Hash ] LNK and script artifacts – 72a36e1d…48c7b (LNK file), b58f672e…1f92 (LNK file), ae51aef2…0bcfd (PowerShell file qw.ps1 embedded in SilentSweeper).
- [File Hash ] Executables (loaders/implants) – 262f9c63…da45 (EXE Laplas/silent_loader), 123901fa…0ba9 (EXE implant), 2c8efe6e…118dd (.NET executable SilentSweeper).
- [Domain/Host ] Hosting and distribution – updates-check-microsoft[.]ddns[.]net (malicious hosting masquerading as update service), catalog-update-update-microsoft[.]serveftp[.]com (malicious hosting for scripts).
- [IP Address ] Command-and-control and hosts – 206.189.11[.]142 (C2 hosting GitHub-linked PowerShell reverse shell), 62[.]113[.]66[.]137 and 62[.]113[.]66[.]7 (Russian-hosted infrastructure), 37[.]18[.]27[.]27 (Russian-hosted infrastructure).
- [File Names ] Delivered artifacts and scheduled task – План развитие стратегического сотрудничества.pdf.rar (malicious RAR decoy), China-Central Asia SummitProject.rar (malicious RAR), WindowsUpdateService.ps1 and WindowsUpdateService.vbs (dropped helper scripts), scheduled task WindowsUpdate.
Read more: https://www.seqrite.com/blog/operation-peek-a-baku-silent-lynx-apt-dushanbe-espionage/