Proofpoint researchers observed a cluster of cybercriminals compromising trucking and freight companies to deliver remote monitoring and management (RMM) tools and remotely access systems to fraudulently bid on and steal cargo. The campaigns used compromised load board accounts, email thread hijacking, and direct email targeting, leveraging RMMs such as ScreenConnect, SimpleHelp, PDQ Connect, Fleetdeck, N-able, and LogMeIn Resolve. #ScreenConnect #SimpleHelp
Keypoints
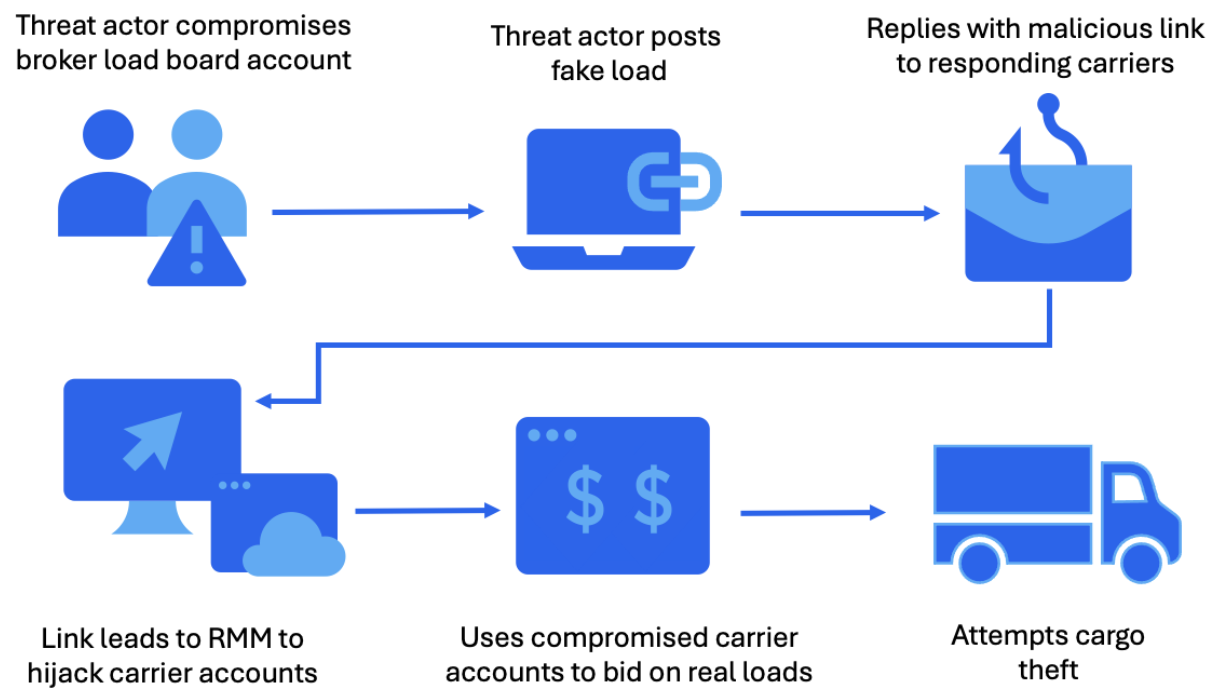
- Threat actors target surface transportation (trucking carriers and freight brokers) to enable physical cargo theft by compromising systems and bidding on real shipments.
- Actors deliver RMM and remote access tooling (ScreenConnect, SimpleHelp, PDQ Connect, Fleetdeck, N-able, LogMeIn Resolve) as first-stage payloads to gain persistent control.
- Three primary delivery tactics observed: compromising load board accounts with fake postings, hijacking existing email threads, and broad direct email campaigns.
- After initial access, actors perform reconnaissance and credential harvesting (e.g., WebBrowserPassView) to expand access and identify lucrative loads.
- Campaigns active since at least January–June 2025 with intensified activity observed through October 2025 and nearly two dozen campaigns since August 2025.
- Public reports and social-media posts corroborate compromises where attackers deleted bookings, blocked notifications, and rebooked loads under compromised carriers.
- Mitigations include restricting unapproved RMM installs, network/endpoint detections (Emerging Threats ruleset), blocking executable downloads from email, and user training.
MITRE Techniques
- [T1190] Exploit Public-Facing Application – Threat actors posted fraudulent freight listings on load boards and used resulting interactions to send malicious URLs leading to RMM installers (“the threat actor will compromise a broker load board account (a marketplace companies use to facilitate booking loads for trucks), post a fake load, and kick off the attack chain when a carrier responds”).
- [T1566.001] Phishing: Spearphishing Link – Emails contained URLs that led to .exe or .msi files which, when clicked, installed RMM tools (“emails contain URLs that lead to an executable (.exe) or an MSI (.msi) file… these files install an RMM tool”).
- [T1608] Stage Capabilities – Actors used payload staging domains to host and distribute RMM installers and landing pages impersonating legitimate brands (“create domains and landing pages that impersonate legitimate brands or generic transportation terms to further the believability”).
- [T1078] Valid Accounts – Actors leveraged compromised email accounts to inject malicious content into ongoing conversations (email thread hijacking) (“Using compromised email accounts, the threat actors inject malicious content and URLs into existing conversations”).
- [T1218] Signed Binary Proxy Execution (e.g., signed installers) – RMM installers were often legitimate, signed payloads distributed maliciously to evade detections (“installers are often signed, legitimate payloads distributed maliciously”).
- [T1083] File and Directory Discovery – After access, actors conducted system and network reconnaissance to identify opportunities and targets within environments (“once initial access is established, the threat actor conducts system and network reconnaissance”).
- [T1056.001] Input Capture: Keylogging/Browser Credential Theft – Actors deployed credential harvesting tools such as WebBrowserPassView to steal credentials (“deploys credential harvesting tools such as WebBrowserPassView”).
Indicators of Compromise
- [Domain ] Payload staging domains used to host RMM installers and landing pages – nextgen1[.]net, carrier-packets[.]net, and many others (e.g., carrierpacket[.]online, rateconfirm[.]net).
- [Domain ] ScreenConnect C2 domains observed – dwssa[.]top, ggdt35[.]anondns[.]net, officews101[.]com.
- [IP Address ] SimpleHelp C2 servers – 185[.]80[.]234[.]36, 147[.]45[.]218[.]66.
- [File Hash ] RMM/installer SHA256 hashes observed – cf0cee4a57aaf7…676ec (ScreenConnect), 559618e2ffbd3b…12765 (PDQ Connect), and 70983c62244c2…734631 (LogMeIn).
- [Emerging Threats Signature ] IDS/Network detection signatures for RMM activity – 2837962 (ScreenConnect – Establish Connection Attempt), 2049863 (simplehelp Remote Access Software Activity).