On November 3, 2025, an attacker exploited an arithmetic precision (rounding) vulnerability in Balancer V2’s ComposableStablePool _upscaleArray function and used 65+ micro-swaps inside atomic batchSwap transactions to drain $128.64 million across six networks. The exploit contract leveraged Vault internal balances and a constructor-based attack to accumulate funds, later withdrawing them to a recipient address. #ComposableStablePool #BalancerV2 #FixedPoint.mulDown
Category: Threat Research
Gootloader, a JavaScript-based loader used by Storm-0494 to hand off access to Vanilla Tempest, has resurged with updated evasion including custom WOFF2 glyph-substitution fonts, XOR-encrypted ZIP payloads via compromised WordPress comment endpoints, and Startup-folder persistence enabling rapid reconnaissance and domain controller compromise. Post-intrusion, Vanilla Tempest commonly deploys Supper SOCKS5 backdoor (TextShell-obfuscated) and proceeds with AD enumeration, lateral movement (WinRM), privileged account creation, and ransomware deployment such as Rhysida and BlackCat. #Gootloader #Storm-0494 #Vanilla_Tempest #Supper_backdoor #Rhysida
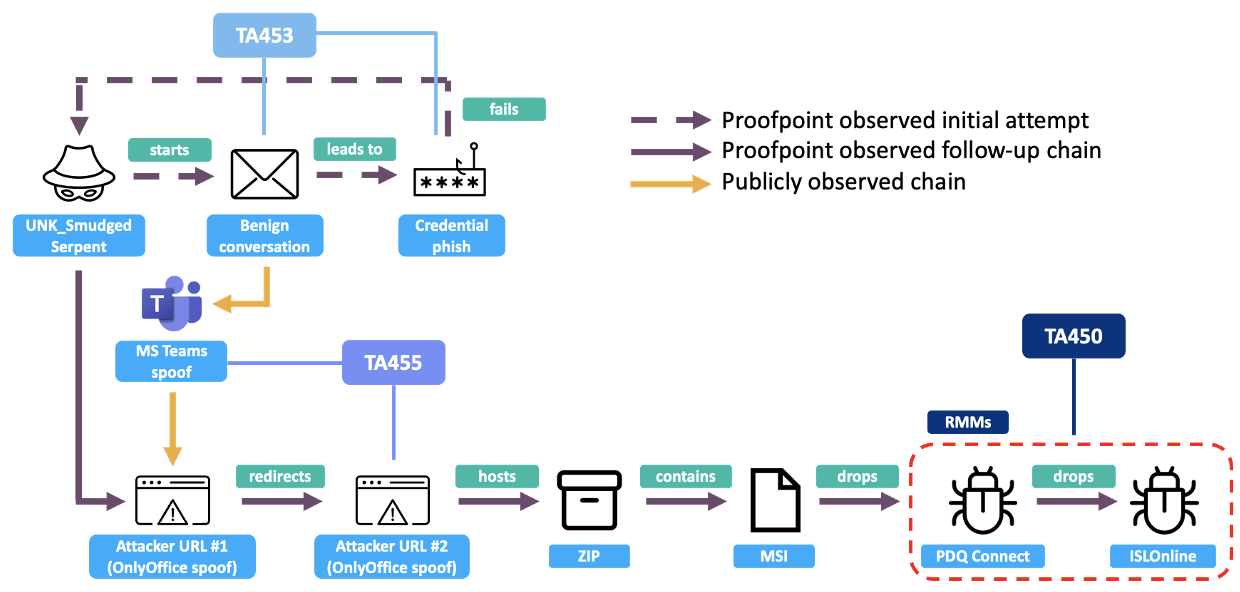
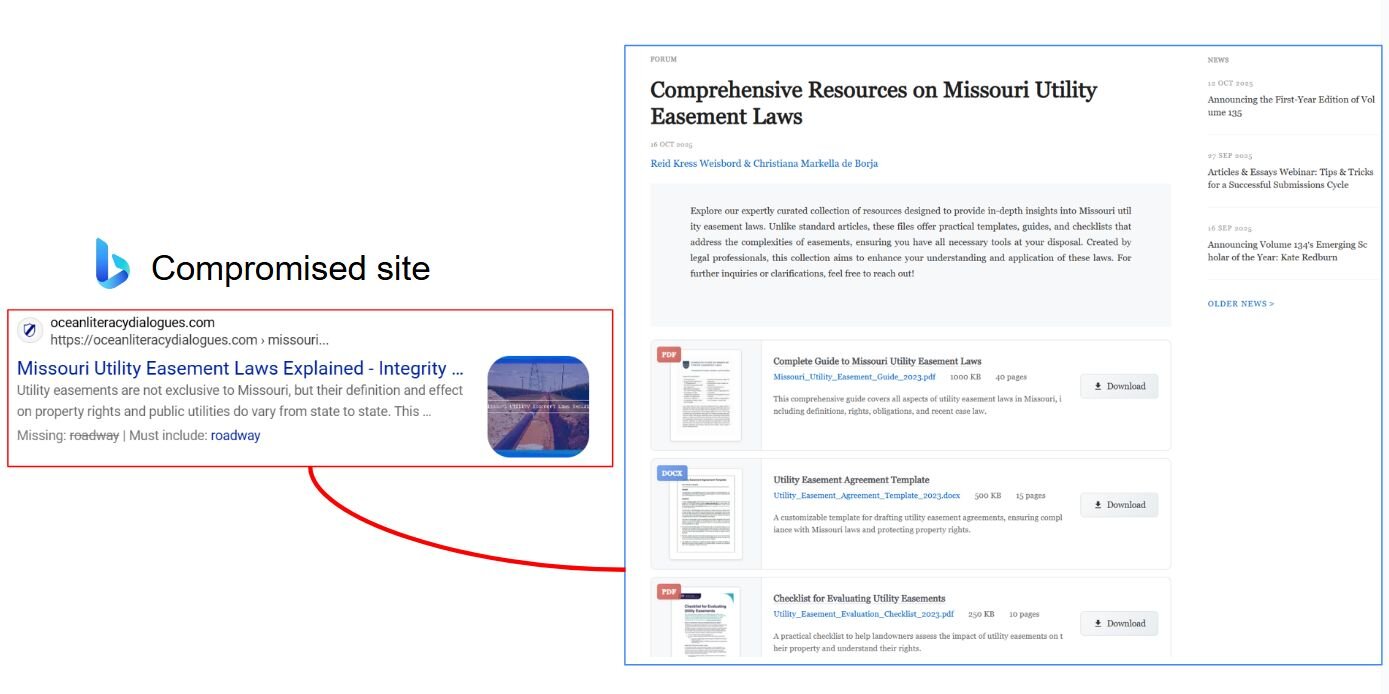
Proofpoint tracked a previously unidentified threat cluster dubbed UNK_SmudgedSerpent that targeted academics and foreign policy experts between June and August 2025 using benign conversation lures, credential harvesting pages, OnlyOffice and Teams spoofs, and RMM tool deployment. Observed TTPs and infrastructure overlapped with Iranian-aligned groups TA453, TA455, and TA450, but attribution remains…

In September 2025 a supply-chain attack on npm introduced an infostealer named Shai-Hulud into 500+ packages, using post-install scripts to harvest credentials, run TruffleHog, exfiltrate secrets to a webhook, and self-propagate by publishing infected package versions when it obtained publishing tokens. The incident highlighted CI/CD pipelines and stolen long-term tokens as primary vectors and showed how eBPF-based runtime sensors and execution-context detection (e.g., Datadog Workload Protection) can detect such behaviors at install time. #Shai-Hulud #TruffleHog
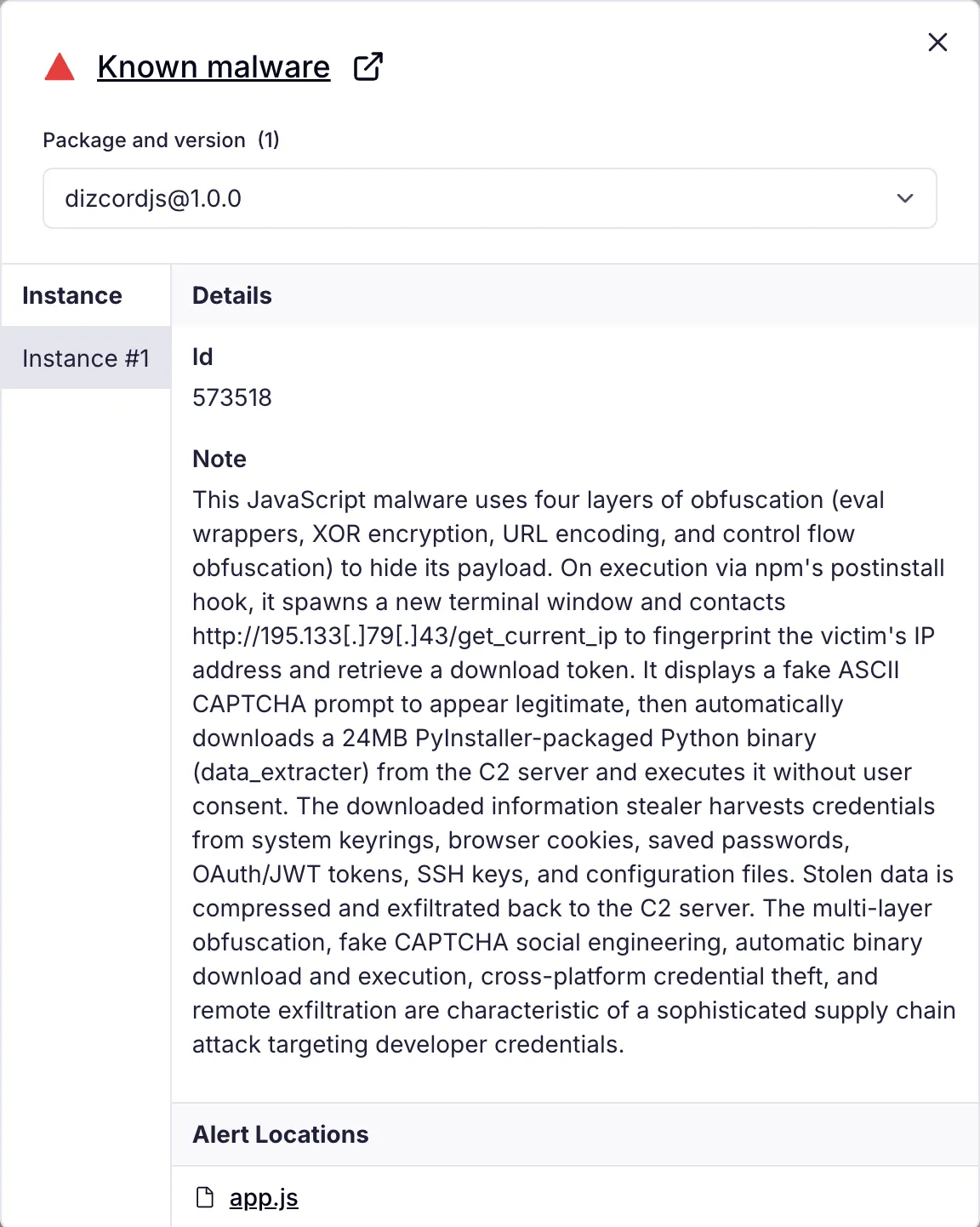
Socket’s Threat Research Team discovered 10 typosquatted npm packages that execute a multi-stage credential stealer via npm’s postinstall hook, using four layers of JavaScript obfuscation, a fake CAPTCHA prompt, IP fingerprinting, and a downloaded 24MB PyInstaller data_extracter binary to harvest credentials across Windows, Linux, and macOS. The campaign’s packages (published July 4, 2025) accumulated over 9,900 downloads, contact the npm registry was made for takedown, and the actor registered packages under the alias andrew_r1 (parvlhonor@gmx[.]com). #data_extracter #andrew_r1
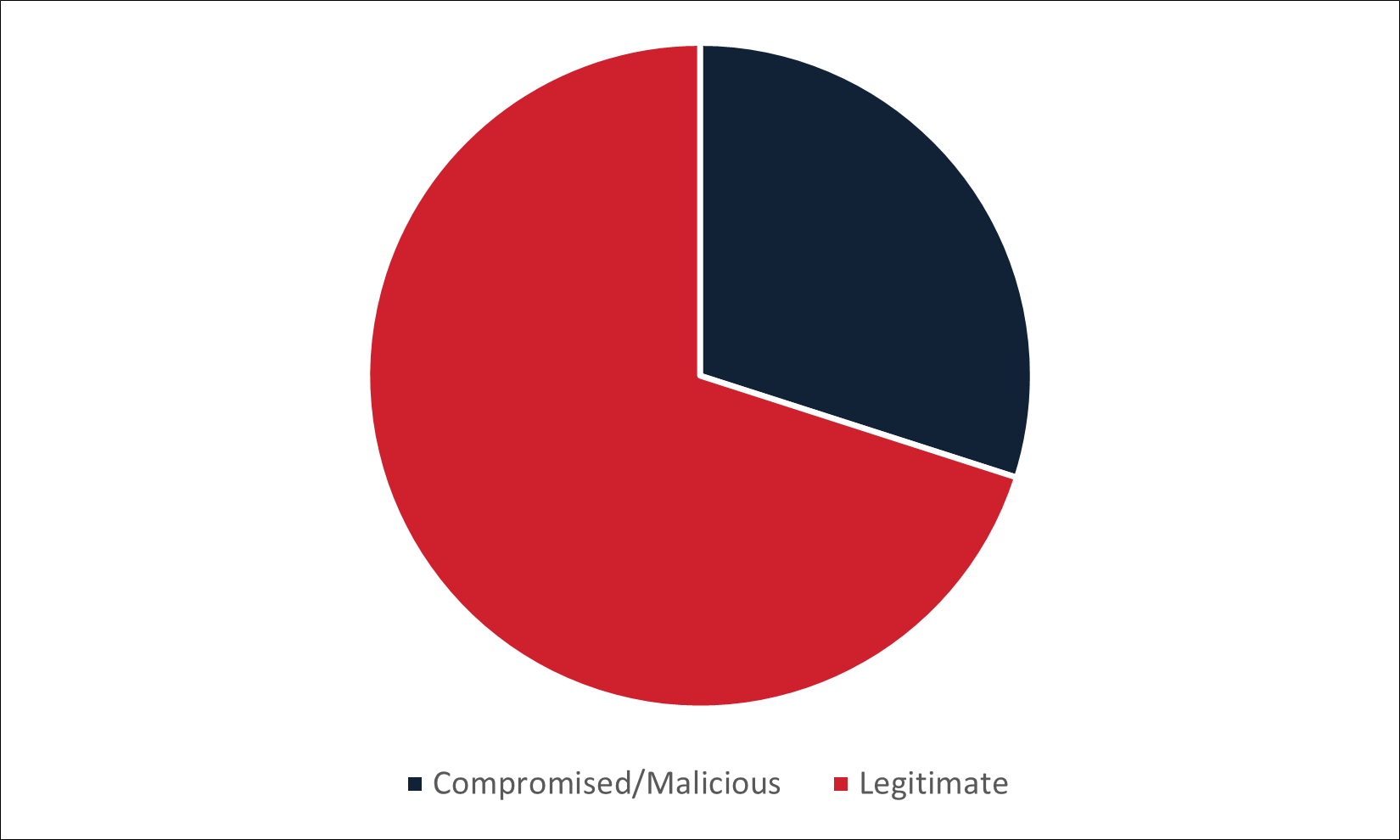
Cofense Intelligence analyzed infection URLs embedded in non-English phishing emails that bypassed secure email gateways, finding that legitimate cloud/file-hosting services (e.g., Google Drive, Dropbox, Amazon AWS) are commonly abused while some languages see more compromised or malicious domains. Malware families show strong language targeting: Remcos and Loda appear across several languages, KrBanker dominates Chinese campaigns, and many Portuguese-specific families (e.g., PeepingTile, Lampion) are almost exclusively delivered in Portuguese. #Remcos #KrBanker
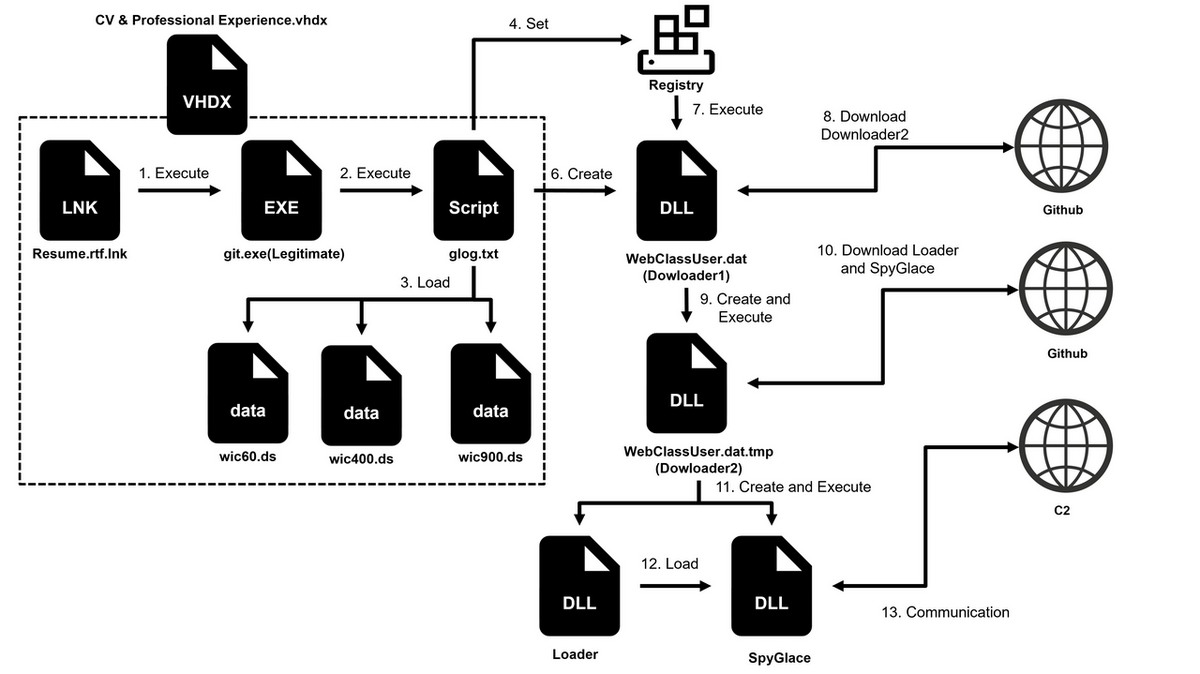
JPCERT/CC observed APT-C-60 spear-phishing attacks in Japan (June–August 2025) that use attached VHDX files containing LNKs which execute legitimate git (gcmd.exe) to run malicious scripts, leading to persistence via COM hijacking and deployment of Downloaders and SpyGlace. The campaign uses GitHub/statcounter for C2 and payload distribution, employs custom encoding (XOR+ADD, modified RC4, AES-128-CBC with known KEY/IV), and includes decoy resumes targeting recruitment staff. #APT-C-60 #SpyGlace #statcounter
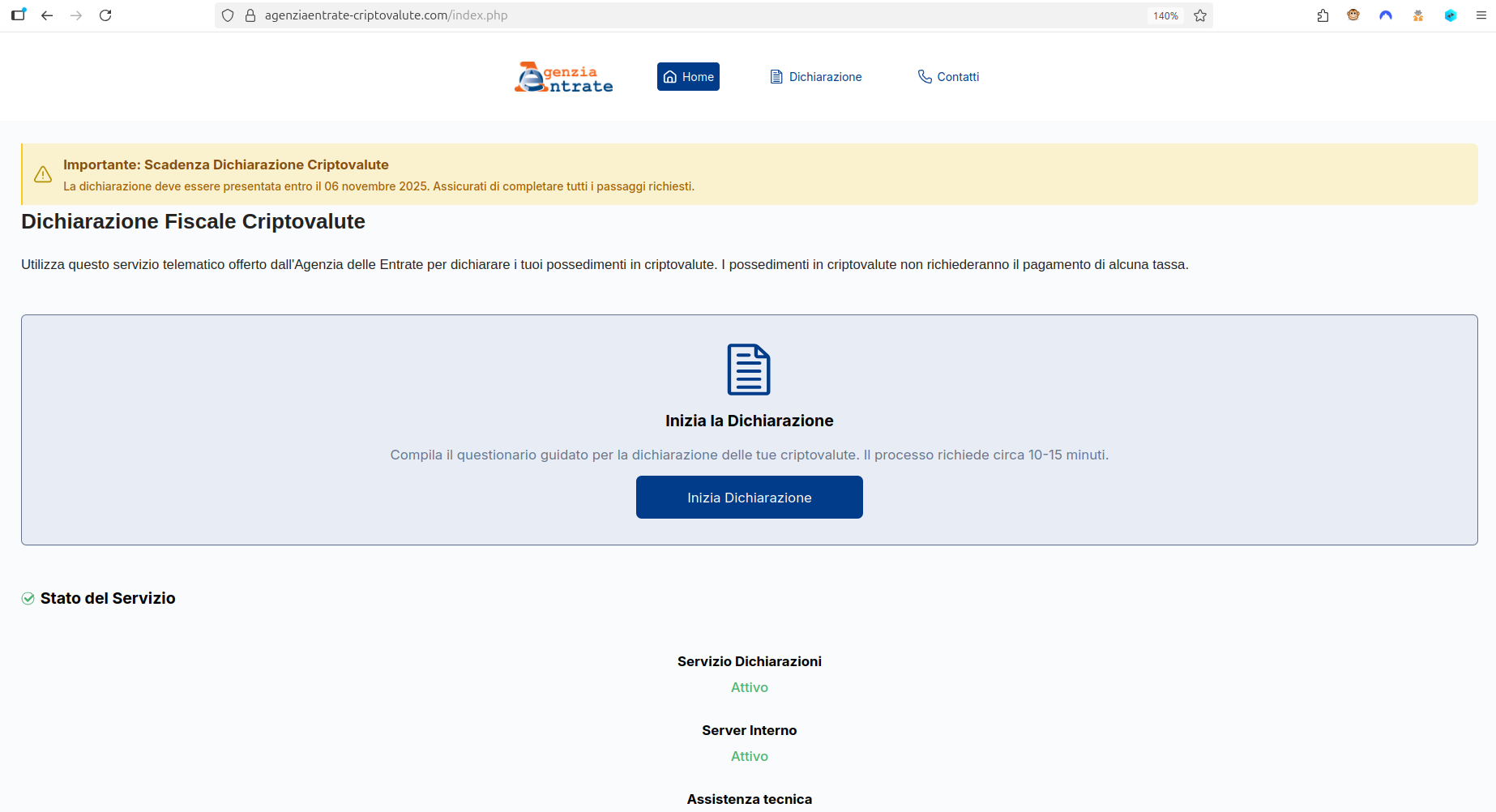
CERT-AGID identified a phishing campaign impersonating the Italian Revenue Agency to trick users into completing a fake "Cryptocurrency Tax Declaration," using institutional branding, fake FAQs, and GDPR references to appear legitimate. The scam collects personal and crypto wallet data and ultimately prompts victims to import or connect wallets (Solana/Ethereum) to steal access. #CERT-AGID #AgenziadelleEntrate

Ransomware threats are accelerating in volume, velocity, and sophistication—driven by RaaS, AI-enabled attacks, and identity-based intrusions—making traditional, signature-based detection insufficient. Organizations need timely, relevant, intelligence-driven data and integrated technologies (threat intelligence, ML/AI, behavioral analytics, automation) to detect and prevent ransomware early. #Ransomware-as-a-Service #RecordedFuture
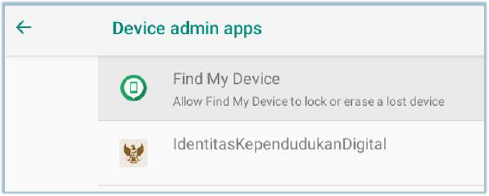
Cyfirma researchers uncovered Android banking Trojans that masquerade as trusted apps (news readers or digital ID apps) to quietly steal login credentials and cryptocurrency wallet data by using Accessibility Services, Device Administrator rights, and overlay screens. The malware checks for emulators, silences notifications, connects to a remote command center to exfiltrate…

Acronis TRU analyzed DragonForce, a Conti-derived RaaS active since 2023 that rebranded as a ransomware cartel, uses leaked Conti code and BYOVD attacks via vulnerable drivers (truesight.sys, rentdrv2.sys) to disable security products and terminate protected processes. The group’s affiliate model and partnerships with Scattered Spider (and overlaps with LAPSUS$ and ShinyHunters) have led to over 200 public victims and variants like Devman and Mamona/Global. #DragonForce #Conti #ScatteredSpider #truesight.sys #rentdrv2.sys
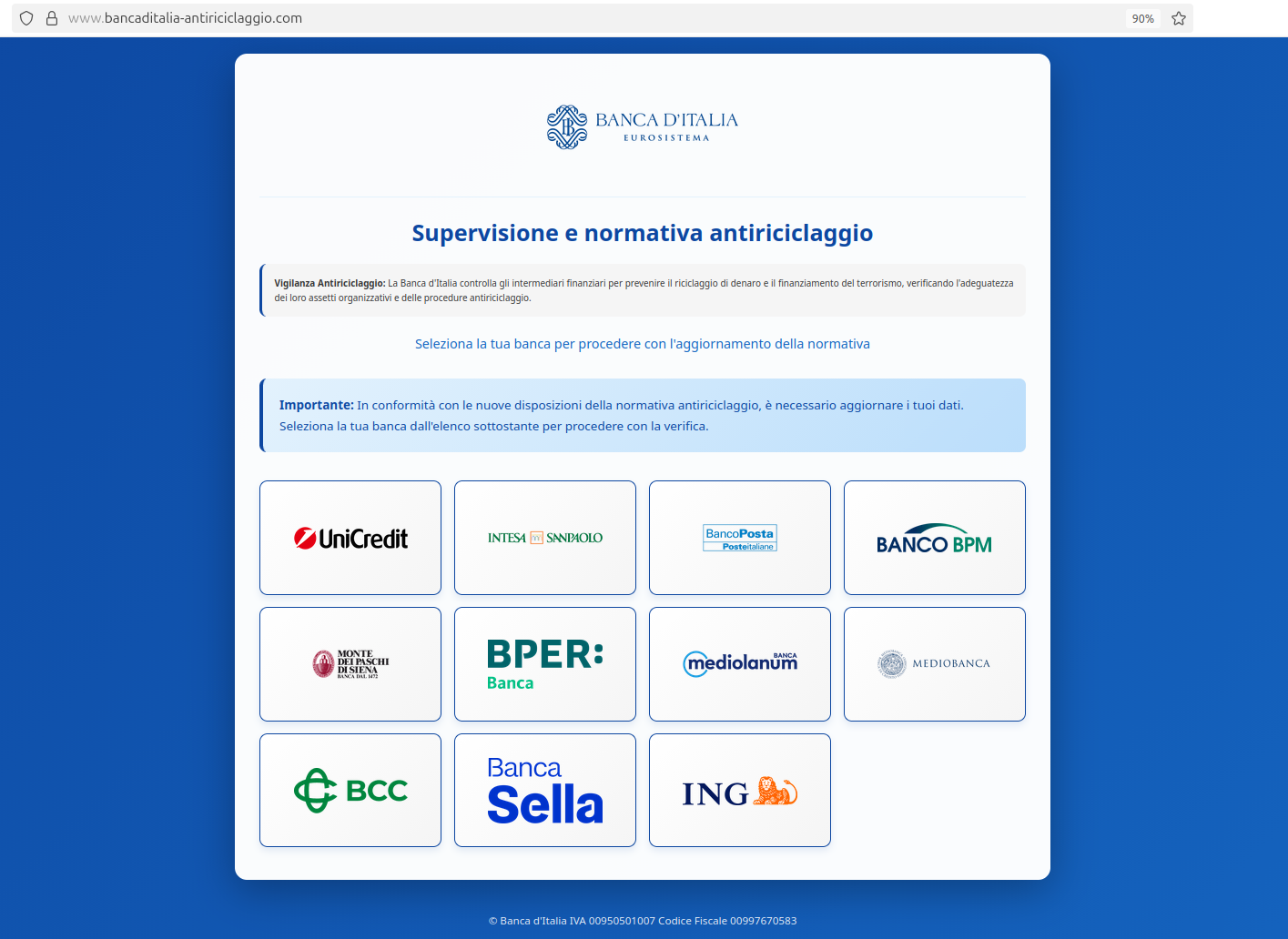
CERT-AGID reported a phishing campaign impersonating Banca d’Italia that uses a fraudulent website to harvest personal and banking information from Italian citizens by asking them to "update" data under the pretext of anti-money laundering rules. The malicious site prompts users to select their bank and enter credentials and OTPs; CERT-AGID notified Banca d’Italia’s security team and requested takedown of the domain. #Banca_dItalia #CERT-AGID

Researchers observed the Russian APT COLDRIVER rapidly replace LOSTKEYS with new malware families NOROBOT, YESROBOT, and MAYBEROBOT to target high-value individuals in NGOs, policy advisory roles, and dissidents. The group refined delivery (ClickFix CAPTCHA lure with iamnotarobot.dll executed via rundll32), rotated infrastructure, and shifted from Python-based to PowerShell-based backdoors to improve flexibility and evade detection. #COLDRIVER #NOROBOT
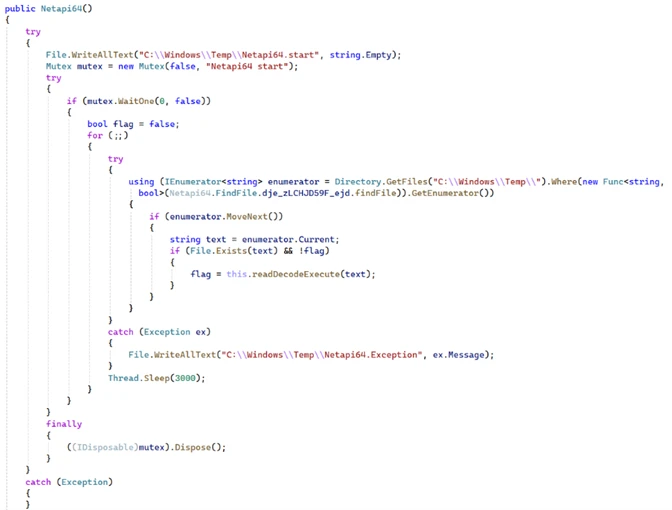
Microsoft DART discovered a novel backdoor named SesameOp that abuses the OpenAI Assistants API as a covert command-and-control (C2) channel to fetch encrypted commands and post execution results. The implant uses .NET AppDomainManager injection, Eazfuscator.NET obfuscation, layered encryption and compression, and creates persistence via a loader Netapi64.dll and OpenAIAgent.Netapi64 to enable long-term espionage; #SesameOp #OpenAIAgent.Netapi64

Check Point Research demonstrated that cloud-based static analysis with ChatGPT (using exported IDA data) combined with occasional MCP-assisted runtime checks can drastically accelerate reverse engineering of heavily obfuscated XLoader 8.0, enabling rapid recovery of keys, decrypted functions, strings, and C2 domains. The workflow reduced many manual steps (triage, deobfuscation, scripting, validation) from days to hours while still requiring targeted human adjustments for scattered key derivation and sample-specific quirks. #XLoader #RC4 #ChatGPT
