Microsoft DART discovered a novel backdoor named SesameOp that abuses the OpenAI Assistants API as a covert command-and-control (C2) channel to fetch encrypted commands and post execution results. The implant uses .NET AppDomainManager injection, Eazfuscator.NET obfuscation, layered encryption and compression, and creates persistence via a loader Netapi64.dll and OpenAIAgent.Netapi64 to enable long-term espionage; #SesameOp #OpenAIAgent.Netapi64
Keypoints
- SesameOp is a backdoor discovered in July 2025 that leverages the OpenAI Assistants API as a relay/storage mechanism for C2 communications instead of traditional infrastructure.
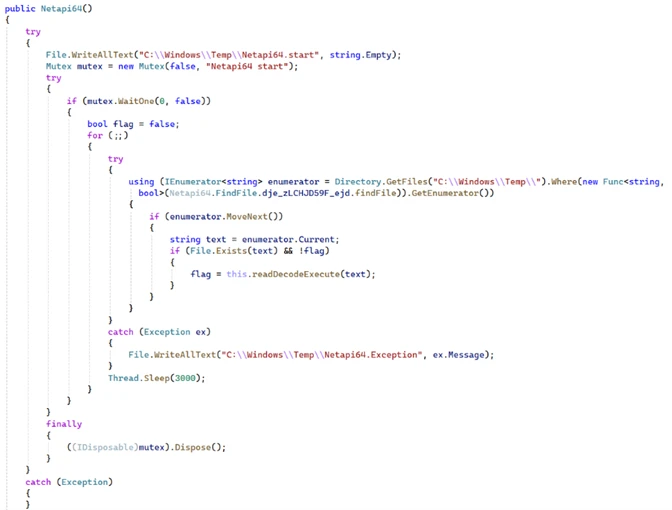
- The infection chain uses a loader (Netapi64.dll) and a .NET backdoor (OpenAIAgent.Netapi64) with heavy Eazfuscator.NET obfuscation and persistence via .NET AppDomainManager injection.
- The backdoor reads configuration from the executable resource (OpenAI API key, dictionary key name, proxy), creates mutexes and marker files, and may use a proxy for outbound connections to api.openai.com.
- Command retrieval and result exfiltration use OpenAI concepts: vector stores, Assistants, threads and messages; descriptions indicate action type (SLEEP, Payload, Result) and thread/message IDs drive retrieval and response.
- Payloads are protected via a hybrid cryptography scheme: a 32-byte AES session key encrypted with an embedded RSA private/public key pair, AES encryption, Base64 encoding, and GZIP compression before posting to OpenAI.
- Execution uses a dynamically loaded embedded .NET module and a Microsoft JScript VsaEngine to Eval.JScriptEvaluate payloads, enabling flexible remote code execution within the victim environment.
- Microsoft and OpenAI collaborated to disable an API key/account used by the actor; mitigations include firewall/proxy controls, Defender for Endpoint protections (block mode, tamper protection, PUA blocking), and hunting for connections to api.openai.com.
MITRE Techniques
- [T1574.002] Hijack Execution Flow: .NET AppDomainManager injection – The loader uses “.NET AppDomainManager injection” to load Netapi64.dll into host executables (“Netapi64.dll is loaded at runtime into the host executable via .NET AppDomainManager injection”).
- [T1027] Obfuscated Files or Information – Eazfuscator.NET obfuscation of .NET DLL to hinder analysis (“The DLL is heavily obfuscated using Eazfuscator.NET”).
- [T1105] Ingress Tool Transfer – Loader retrieves and XOR-decodes embedded .Netapi64 payload from Temp folder and runs it (“The loader then XOR-decodes the file and runs it”).
- [T1562.001] Impair Defenses: Disable or Modify Tools – Use of compromised Visual Studio utilities with malicious libraries to bypass normal defenses (threat leveraged “multiple Microsoft Visual Studio utilities that had been compromised with malicious libraries”).
- [T1573] Encrypted Channel – Layered encryption and compression for command and result data (uses “both symmetric and asymmetric” encryption plus compression to protect command data and exfiltrated results).
- [T1102] Web Service: Use of legitimate web services for C2 – Abuse of OpenAI Assistants API as C2 channel to fetch commands and post results (“uses the OpenAI Assistants API as a storage or relay mechanism to fetch commands… it sends the results back to OpenAI as a message”).
- [T1059.007] Command and Scripting Interpreter: JScript – Execution of payload via Microsoft JScript VsaEngine and Eval.JScriptEvaluate (“The Frameworks method initializes a Microsoft JScript VsaEngine… the value is then executed using Eval.JScriptEvaluate”).
- [T1486] Data Encrypted for Impact (exfiltration protection) – Results compressed, AES-encrypted with generated 32-byte key, and the AES key encrypted with embedded RSA key before being posted (“The result is first compressed with GZIP, then encrypted using AES… The AES key itself is encrypted using a hardcoded RSA public key”).
Indicators of Compromise
- [File name] Loader and marker files – Netapi64.dll (loader), OpenAIAgent.Netapi64 (backdoor), C:WindowsTempNetapi64.start (marker file).
- [Mutex] Running instance markers – mutex names “OpenAI APIS” and mutex created by Netapi64.dll to ensure single instance.
- [API endpoints / Domains] C2 service endpoints – connections to api.openai.com (e.g., https://api.openai.com) observed as C2 channel.
- [Configuration values] Embedded resource fields – OpenAIAgent.token (OpenAI API key placeholder), OpenAIAgent.aaazzz (dictionary key name), OpenAIAgent.proxy (proxy address) found in .NET resource TextFile1.
- [Obfuscation/tooling] Obfuscator indicator – presence of Eazfuscator.NET metadata in .NET binaries suggests obfuscation.
- [Cryptographic artifacts] Encrypted payload patterns – Base64-encoded AES-encrypted payloads and RSA-encrypted AES keys posted as message content (examples described as “32-byte AES key… Base64-encoded” and “encrypted key and processed result joined together”).