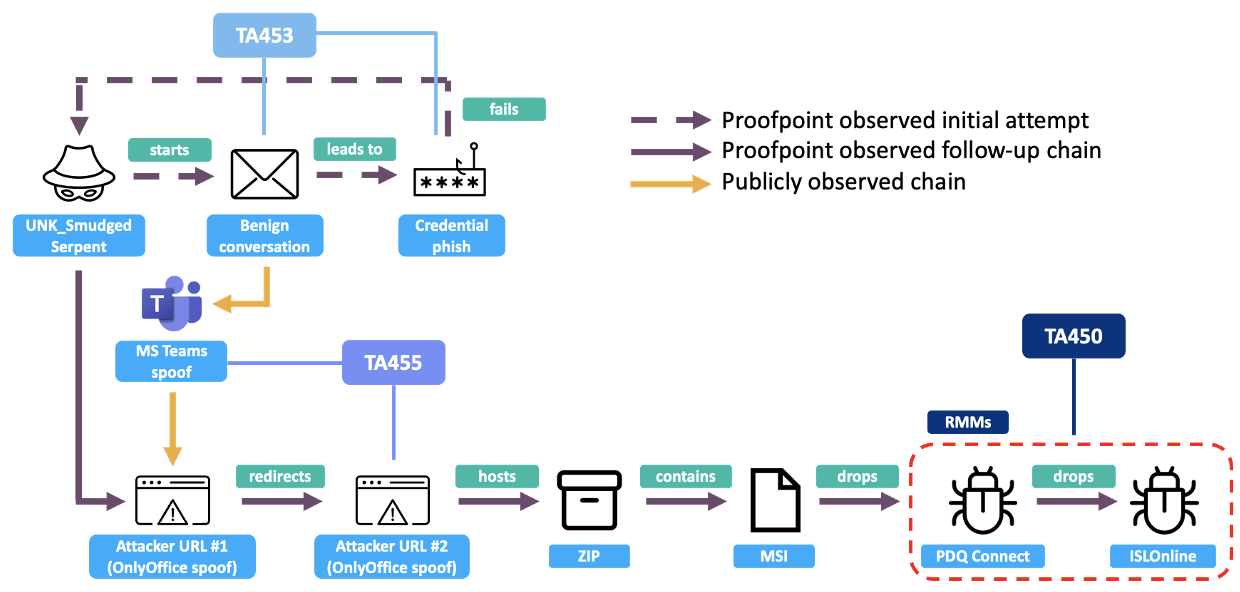
Proofpoint tracked a previously unidentified threat cluster dubbed UNK_SmudgedSerpent that targeted academics and foreign policy experts between June and August 2025 using benign conversation lures, credential harvesting pages, OnlyOffice and Teams spoofs, and RMM tool deployment. Observed TTPs and infrastructure overlapped with Iranian-aligned groups TA453, TA455, and TA450, but attribution remains low confidence. #UNK_SmudgedSerpent #TA455
Keypoints
- UNK_SmudgedSerpent conducted targeted phishing of policy experts and think-tank members from June–August 2025 using benign conversation starters impersonating known experts.
- Initial lures spoofed Brookings’ Suzanne Maloney (misspelled) and later personas including Patrick Clawson to solicit collaboration on Iran-related topics.
- Delivery used OnlyOffice and health-themed domains (thebesthomehealth[.]com, mosaichealthsolutions[.]com, healthcrescent[.]com, ebixcareers[.]com) that redirected to credential harvesting pages and hosted archives.
- The infection chain delivered a ZIP containing an MSI that installed RMM software (PDQConnect) and operators later installed ISL Online RMM, indicating hands-on-keyboard activity.
- TTPs and infrastructure overlap with TA453 (benign conversation lures), TA455 (health-themed domains, OnlyOffice hosting, MiniJunk/MiniBike artifacts), and TA450 (use of RMM tools), preventing high-confidence attribution.
- Infrastructure analysis found OnlyOffice-hosted files including a loader (Interview time.msi) and a package (Hiring Portal.zip) that sideloaded DLLs, including a DLL matching TA455’s MiniJunk backdoor family.
- Proofpoint released ET rules and numerous domains associated with UNK_SmudgedSerpent and TA455 to detect observed phishing, OnlyOffice usage, and PDQ/ RMM network activity.
MITRE Techniques
- [T1566] Phishing – Initial engagement used targeted spearphishing via email with benign conversation starters impersonating experts (“impersonated Suzanne Maloney … using a Gmail address and misspelled version of her name, ‘Suzzane Maloney’”).
- [T1598] Phishing: Spearphishing Link – Emails contained OnlyOffice or Teams-looking links that redirected to credential harvesting pages (“thebesthomehealth[.]com … redirected to … mosaichealthsolutions[.]com that displayed a Microsoft 365 login page. The URL hosted a customized credential harvesting page with the user’s information pre-loaded.”).
- [T1071] Application Layer Protocol – Use of web redirects and OnlyOffice hosting to deliver malicious archives and credential harvesters (“OnlyOffice URL … hosted two PDFs, an Excel document, and a ZIP archive.”).
- [T1531] Account Discovery / Credential Harvesting – Customized Microsoft 365 login pages pre-loaded with user information to harvest credentials (“displayed a Microsoft 365 login page. The URL hosted a customized credential harvesting page with the user’s information pre-loaded.”).
- [T1218] Signed Binary Proxy Execution (Sideloading) – Hiring Portal.zip contained an executable that sideloaded userenv.dll and xmllite.exe to load malicious DLLs (“the legitimate EXE sideloads userenv.dll and through another legitimate EXE, sideloads xmllite.exe. userenv.dll is a TA455 custom backdoor termed MiniJunk”).
- [T1047] Windows Management Instrumentation / [T1210] Exploitation of Remote Services (abuse of legitimate RMM tools) – Deployment and abuse of PDQConnect and ISL Online RMM to maintain access and perform hands-on-keyboard activity (“ZIP archive loaded an MSI file, which launched the PDQConnect Remote Monitoring & Management (RMM) software … attackers leveraged PDQConnect to install additional RMM software, ISL Online.”).
- [T1078] Valid Accounts – Use of freemail accounts and attacker-owned domains to send follow-up emails and continue engagement within the same email thread (“freemail (Outlook, Gmail) … attacker-owned domains … suzzanemaloney68@gmail[.]com … patrickclawson51@gmail[.]com”).
Indicators of Compromise
- [Email addresses] phishing sender addresses used to impersonate experts – suzzanemaloney@gmail[.]com, suzannemaloney68@gmail[.]com (June 2025)
- [Email addresses] additional spoofed senders – patrickclawson51@gmail[.]com, patrick.clawson51@outlook[.]com (June–August 2025)
- [Domains] UNK_SmudgedSerpent delivery and hosting domains – thebesthomehealth[.]com, mosaichealthsolutions[.]com (April–June 2025)
- [Domains] related infrastructure and OnlyOffice hosting tied to campaigns – healthcrescent[.]com, ebixcareers[.]com (May–July 2025)
- [URLs] OnlyOffice and delivery links – hxxps://suzzanemaloney2506090953.onlyoffice[.]com/s.-k6vjflsdagdsfgh (June 2025); interview.ebixcareers[.]com/teams/join-online-room-homv-patm-elro (OnlyOffice payload link)
- [File hashes: MSI/EXE/DLL/SHA256] payload and artifact hashes – 85858880ee7659cc1152b6a126bc20b9b4fb1b46dddea5af2d65d48d58cd058 (MSI), cac018dccdf6ce4bef19ab71e3e737724aed104bc824332a5213c878b065ff50 (EXE), and DLLs 7b5fb8202bff90398ab007579713f66430778249e43b46f35df6c3ded628f129, 129a40e38ef075c7d33d8517b268eb023093c765a32e406b58f39fab6cc6a040 (September 2025)
- [Files] archive and decoy artifacts – Hiring Portal.zip (contained sideloading DLLs and EXE), Interview time.msi (installer that launched PDQConnect RMM)