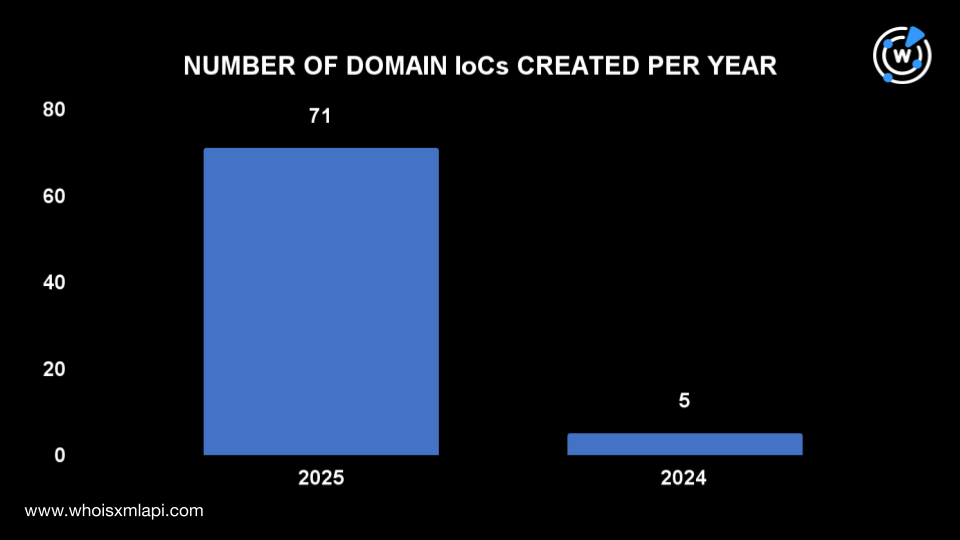
Cloudflare and Microsoft disrupted RaccoonO365, a Phishing‑as‑a‑Service operation that enabled criminals to steal over 5,000 credentials and collected an estimated $100,000 in cryptocurrency. The takedown revealed hundreds of related domains, many newly registered in 2025, and IoCs including cryptocurrency addresses, 77 domains, 21 subdomains, and numerous IP addresses discovered through WHOIS and DNS analysis. #RaccoonO365 #Cloudflare
Category: Threat Research
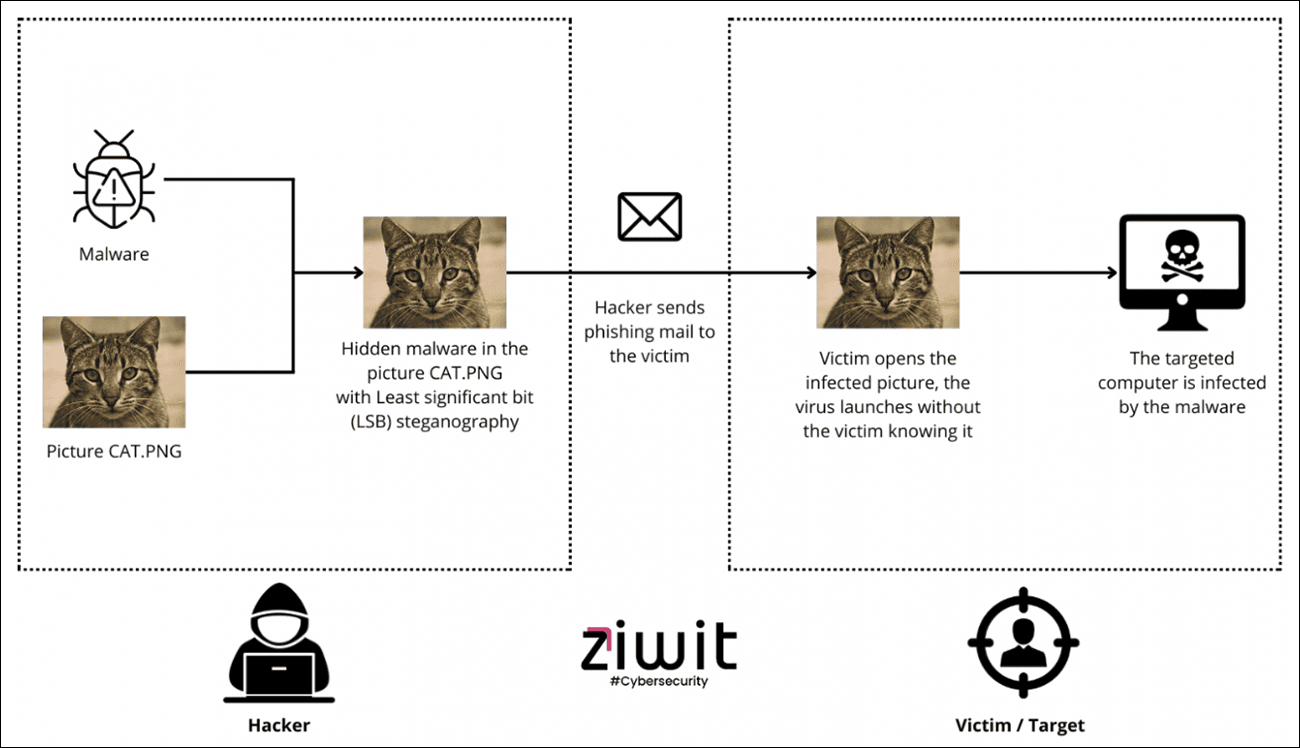
Arctic Wolf Labs discovered a Brazilian-origin Loader-as-a-Service called Caminho that uses LSB steganography to hide .NET loaders inside images hosted on legitimate platforms and delivers diverse payloads including REMCOS RAT, XWorm, and Katz Stealer. The multi-stage campaign uses spear-phishing with obfuscated JS/VBS and PowerShell stages, in-memory .NET loading and process injection,…
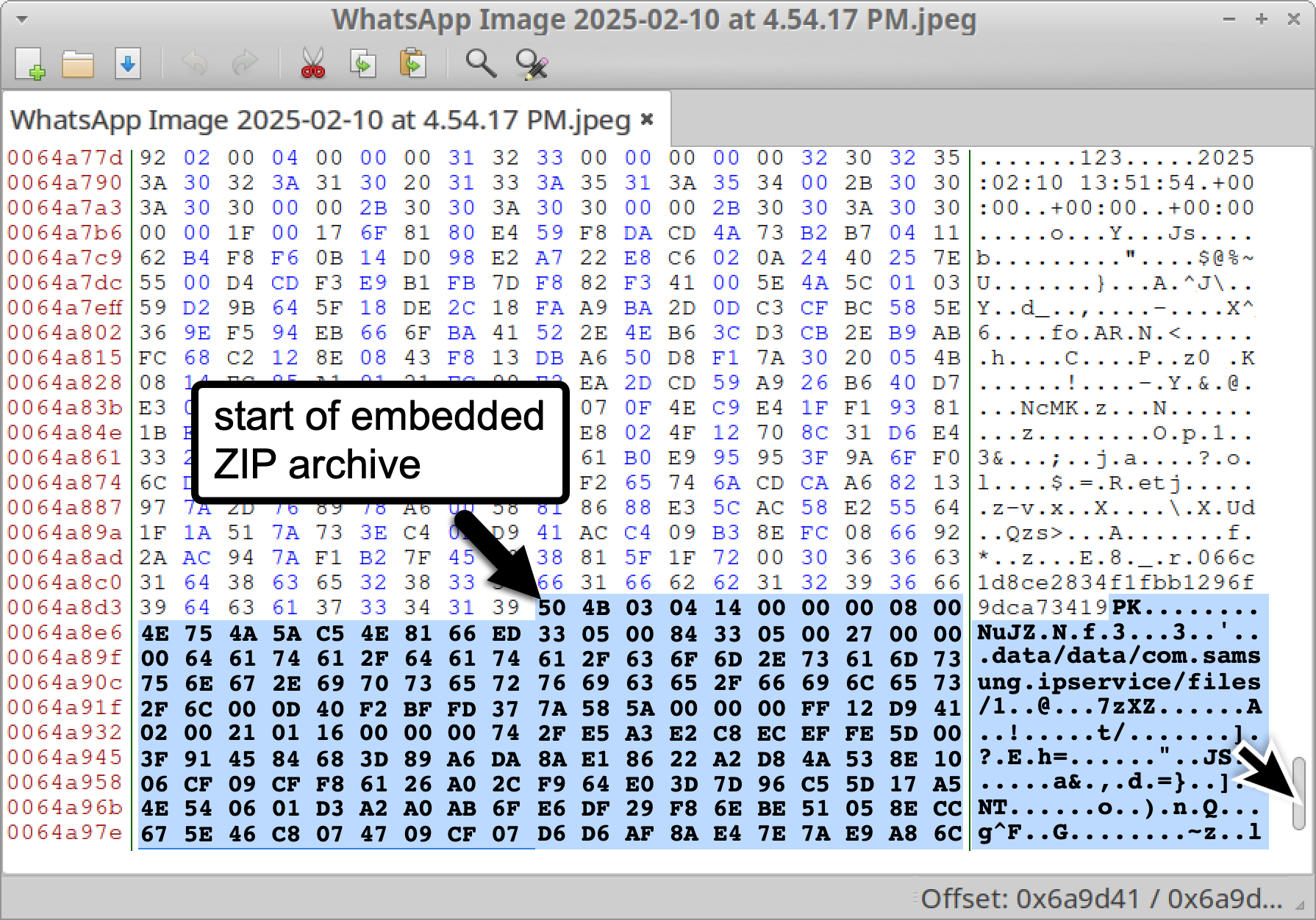
Unit 42 uncovered LANDFALL, a previously unknown Android spyware family targeting Samsung Galaxy devices that was delivered via malformed DNG image files exploiting a zero-day in Samsung’s image processing library (CVE-2025-21042) and active in mid-2024 through early 2025. The campaign used embedded shared object payloads and infrastructure consistent with commercial spyware…
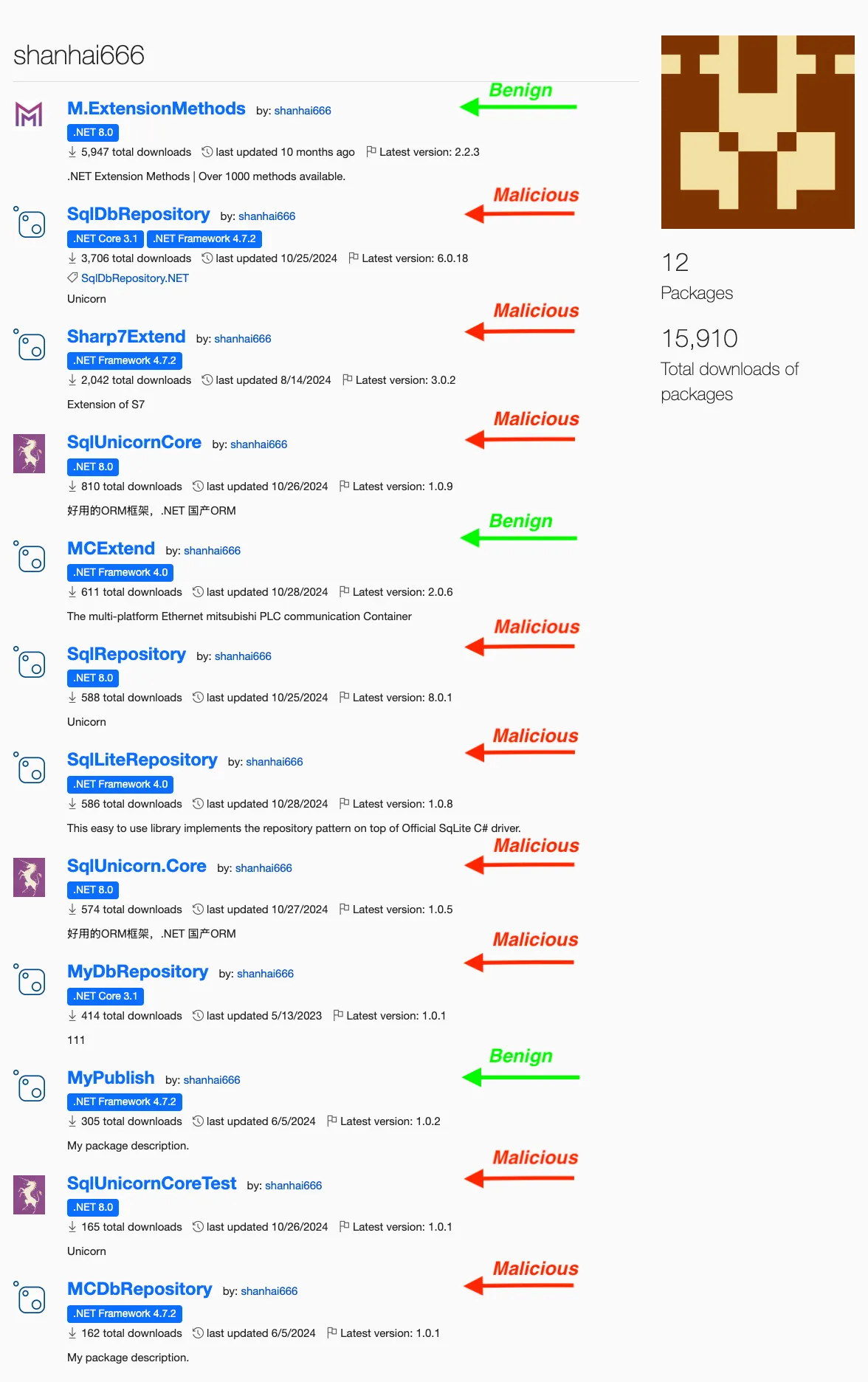
Socket discovered nine malicious NuGet packages published under the alias shanhai666 that inject time-delayed destructive payloads into database operations and target industrial PLCs, causing probabilistic process termination and silent write failures. The most dangerous package, Sharp7Extend, bundles legitimate Sharp7 code while implementing immediate random process kills and time-delayed 80% write failures against PLC operations, affecting safety-critical manufacturing systems. #Sharp7Extend #shanhai666

Tycoon 2FA is a Phishing-as-a-Service platform that uses an Adversary-in-the-Middle reverse proxy to capture credentials and session tokens from Microsoft 365 and Gmail logins, bypassing 2FA/MFA by relaying codes in real time. The kit uses obfuscated JavaScript, bot/debugger checks, hosted assets on services like Amazon S3, and dynamic templates to tailor attacks to organization-specific policies. #Tycoon2FA #Microsoft365 #Gmail

A malicious VS Code/Open VSX extension named SleepyDuck uses an Ethereum smart contract to store and update its C2 server address, enabling resilient remote access trojan functionality and sandbox evasion. The campaign reached thousands of downloads and parallels other malicious extensions that delivered crypto-mining payloads under deceptive publishers. #SleepyDuck #0xDAfb81732db454DA238e9cFC9A9Fe5fb8e34c465

A phishing campaign called “I Paid Twice” targeted hotel establishments by using compromised Booking.com accounts and ClickFix social engineering to deliver PowerShell commands that deploy PureRAT, enabling theft of booking-extranet credentials and subsequent customer-targeted banking phishing. The operation leveraged a redirection/TDS infrastructure, hundreds of malicious domains, and a cybercrime ecosystem selling Booking.com logs and services such as traffers and log checkers. #PureRAT #ClickFix

zLabs discovered “Fantasy Hub,” an Android Remote Access Trojan sold as Malware‑as‑a‑Service with documentation, builder bot, and instructions to create fake Google Play pages to deploy spyware and phishing windows targeting banks. The malware abuses default SMS handler privileges, uses a native dropper and WebRTC for live streaming, and has been observed targeting institutions including Alfa, PSB, Tbank, and Sber. #FantasyHub #Alfa #Sber
Three runc vulnerabilities disclosed on November 5, 2025 can allow container escapes by abusing maskedPaths, /dev/console mount races, and procfs write redirection, though no active exploits were identified at publication. Recommended mitigations include updating runc to fixed versions, enabling user namespaces, and using rootless containers. #CVE-2025-31133 #CVE-2025-52565

Datadog Security Research discovered 17 malicious npm packages (23 releases) that used postinstall scripts to download and execute a Vidar infostealer payload on Windows systems, attributed to threat cluster MUT-4831. The campaign abused freshly created npm accounts to publish SDK-like packages masquerading as benign libraries and used download URLs such as upload.bullethost.cloud to fetch encrypted ZIP archives containing bridle.exe. #Vidar #MUT-4831

DORA forces EU financial organizations to adopt proactive, testable ICT risk management, moving security “left of boom” to detect threats before they materialize using Indicators of Future Attack (IOFA)™. Silent Push maps its IOFA-centric platform to DORA’s five pillars to provide continuous monitoring, incident response support, resilience testing, third-party risk visibility,…

Chinese-linked APT actors used known exploitation scans and a multi-stage intrusion in April 2025 to establish persistent, stealthy access to a U.S. organization, employing DLL sideloading (vetysafe.exe -> sbamres.dll), legitimate binaries (msbuild.exe, Imjpuexc), scheduled tasks, a custom loader, and DCSync-like activity. #APT41 #Kelp #SpacePirates #Dcsync #DeedRAT

A MuddyWater phishing campaign used compromised mailboxes and macro-enabled Word documents to deliver a FakeUpdate loader that decrypts and injects Phoenix backdoor v4, establishing persistence and C2 communication. The operation also hosted a Chromium-based credential stealer and RMM tools on the same infrastructure, notably screenai[.]online, targeting government and regional entities in the Middle East and North Africa. #MuddyWater #Phoenix #FakeUpdate #screenai.online

Google Threat Intelligence Group (GTIG) reports that adversaries have progressed from using AI for productivity to deploying novel AI-enabled malware that dynamically alters behavior during execution, exemplified by families like PROMPTFLUX and PROMPTSTEAL. The report documents state-backed and criminal actors misusing Gemini and other LLMs across the attack lifecycle and details mitigations Google has taken, including disabling assets and strengthening model and classifier safeguards. #PROMPTFLUX #PROMPTSTEAL

Cephalus is a Go-based ransomware group active since mid-June 2025 that breaches organizations mainly by compromising RDP accounts lacking MFA, exfiltrates data, and performs targeted encryption using a custom ransomware that disables protections and deletes backups. The malware uses a single AES-CTR key protected by memory-locking and XOR masking, generates fake…