Cloudflare and Microsoft disrupted RaccoonO365, a Phishing‑as‑a‑Service operation that enabled criminals to steal over 5,000 credentials and collected an estimated $100,000 in cryptocurrency. The takedown revealed hundreds of related domains, many newly registered in 2025, and IoCs including cryptocurrency addresses, 77 domains, 21 subdomains, and numerous IP addresses discovered through WHOIS and DNS analysis. #RaccoonO365 #Cloudflare
Keypoints
- Cloudflare and Microsoft coordinated to disrupt RaccoonO365, a Phishing‑as‑a‑Service (PhaaS) that enabled widespread credential theft affecting over 5,000 users.
- Cybercriminal customers paid about $100,000 in cryptocurrency to use RaccoonO365 since the service became available last year.
- Cloudflare’s brief listed many IoCs: three cryptocurrency addresses, 77 domain names, and 21 subdomains; hundreds of related domains have been taken down.
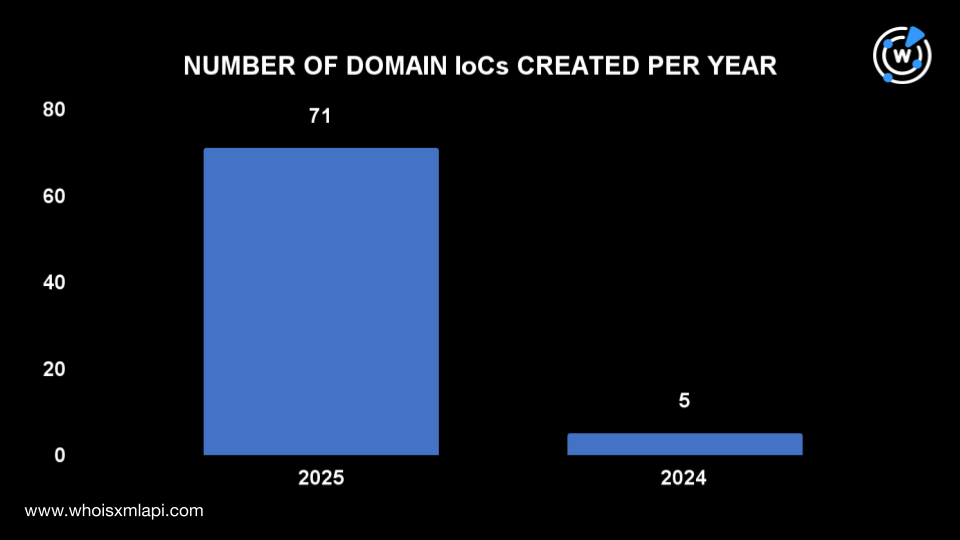
- Analysis of the 77 domain IoCs found 76 current WHOIS records, with 71 domains created in 2025, indicating a heavy reliance on newly registered domains (NRDs).
- Top registrars for the domain IoCs included Name SRS AB (32), Gransy (11), Namecheap (6), MarkMonitor (6), and NameSilo (6); registrant countries were dominated by Sweden (32) and the U.S. (19).
- DNS history for 65 of the domains showed 1,461 domain-to-IP resolutions; some domains had earlier resolutions predating current WHOIS creation, indicating reuse of dropped domains.
- A subgroup of 10 domains containing “o365” were flagged in First Watch’s feed and were predicted to turn malicious 10–355 days before Cloudflare’s 10 September 2025 report.
MITRE Techniques
- [T1584] Compromise Infrastructure – Use of extensive domain registrations and subdomains to host phishing sites and infrastructure (“…hundreds of domains related to Raccoono365 had already been taken down…”).
- [T1588] Obtain Capabilities – Phishing‑as‑a‑Service model enabled nontechnical criminals to obtain phishing capabilities (“…makes phishing easier, as cybercriminals use it to create fake emails and launch phishing websites…”).
- [T1598] Phishing – Deployment of fake emails and phishing websites to steal credentials (“…create fake emails and launch phishing websites…to steal more than 5,000 user credentials worldwide.”).
- [T1086] PowerShell (detection/related scripting) – (If present in artifacts) indicated by downloadable additional artifacts and investigative emphasis on artifacts for detection (“A sample of the additional artifacts obtained from our analysis is available for download from our website.”).
Indicators of Compromise
- [Domains] RaccoonO365 related domains – examples: o365microsoftsecurecloud[.]com, filesoo365cloudocxs[.]com (and 75 more domain IoCs total).
- [Subdomains] Phishing subdomains used for credential collection – example patterns: fileso365clloudoccs[.]com (part of the 21 subdomains reported).
- [IP Addresses] Historical domain-to-IP resolutions tied to IoCs – examples: 163 IPs found from Jan–Aug 2025 (159 flagged as malicious), and four non-flagged IPs.
- [Email addresses] WHOIS-connected emails used across related domains – example: 17 public emails discovered historically, 8 emails linked to 121 email-connected domains.
- [Cryptocurrency addresses] Payment destinations for the PhaaS – example: three cryptocurrency addresses listed in Cloudflare’s brief (specific addresses available in the original report).
Read more: https://circleid.com/posts/chasing-after-racoono365-iocs-using-dns-and-domain-intelligence