Arctic Wolf Labs discovered a Brazilian-origin Loader-as-a-Service called Caminho that uses LSB steganography to hide .NET loaders inside images hosted on legitimate platforms and delivers diverse payloads including REMCOS RAT, XWorm, and Katz Stealer. The multi-stage campaign uses spear-phishing with obfuscated JS/VBS and PowerShell stages, in-memory .NET loading and process injection, and persistence via scheduled tasks, with confirmed victims in Brazil, South Africa, Ukraine, and Poland. #Caminho #REMCOS #KatzStealer
Keypoints
- Caminho is a .NET loader (first observed March 2025) delivered via spear-phishing archives containing obfuscated JavaScript/VBScript that stage PowerShell payloads.
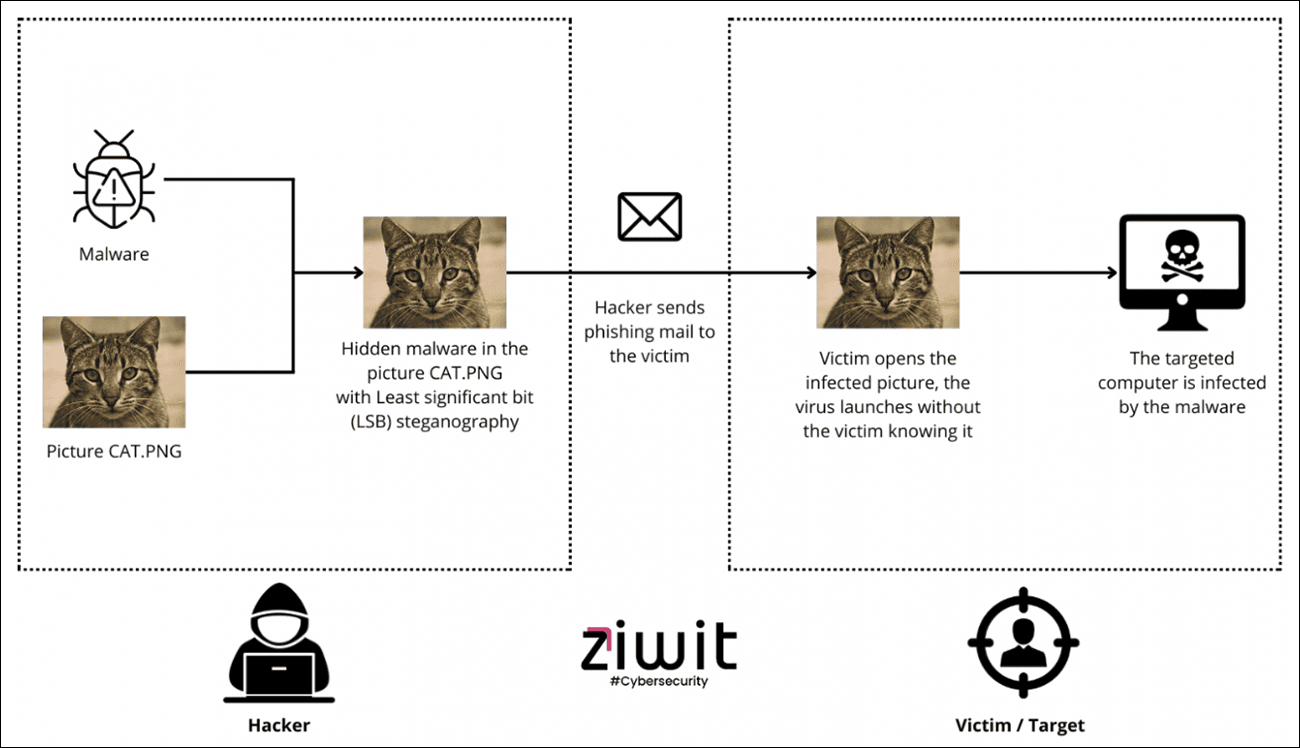
- Operators employ LSB steganography to conceal Base64-encoded .NET payloads inside JPG/PNG images hosted on archive.org and other file hosting services.
- The loader extracts the hidden .NET assembly in memory and injects final payloads into calc.exe/calc64.exe, avoiding disk writes and enabling fileless execution.
- Observed final payloads include REMCOS RAT, XWorm, and Katz Stealer, indicating a Loader-as-a-Service model used by multiple customers.
- Samples contain extensive Portuguese-language artifacts and operational timing consistent with Brazil, supporting high-confidence Brazilian origin attribution.
- Persistence is implemented via scheduled tasks running a JavaScript persistence script (panters.js) from C:UsersPublicDownloads executed every minute.
- Infrastructure mixes legitimate services (archive.org, paste.ee, pastefy.app, catbox.moe) and bulletproof hosting (AS214943 Railnet LLC) to stage scripts, images, and C2.
MITRE Techniques
- [T1566.001 ] Spear-phishing Attachment – Delivered RAR/ZIP archives containing JavaScript or VBS files as initial infection vectors: “RAR/ZIP archives containing JavaScript or VBS files delivered via email with business-themed lures (invoices, quotations, urgent requests).”
- [T1059.007 ] JavaScript – Multi-stage JavaScript used as initial droppers and to retrieve PowerShell: “Multi-stage JavaScript execution beginning with obfuscated .js files extracted from archives.”
- [T1059.001 ] PowerShell – PowerShell used to download images from archive.org and perform LSB extraction of a .NET assembly: “Intermediate stage uses PowerShell for steganographic extraction and .NET assembly loading.”
- [T1027 ] Obfuscated Files or Information – Heavy obfuscation of JavaScript, PowerShell, and .NET to evade analysis: “Heavy JavaScript obfuscation using variable randomization and string encoding.”
- [T1027.003 ] Steganography – LSB steganography hides a BMP/.NET payload inside JPG/PNG images hosted on archive.org: “LSB steganography conceals .NET payload within JPG/PNG image files hosted on archive.org.”
- [T1055 ] Process Injection – Loader injects final payload into calc.exe/calc64.exe to execute in-memory: “Injects final payload into calc.exe or calc64.exe address space.”
- [T1053.005 ] Scheduled Task/Job: Scheduled Task – Creates scheduled tasks (amandes/amandines) executing a JS persistence script every minute: “Creates task named “amandes” or “amandines” executing JavaScript from C:UsersPublicDownloads every minute on system start.”
- [T1140 ] Deobfuscate/Decode Files or Information – Uses Base64 and reversal to encode URLs/payloads which are decoded at runtime: “Base64 decoding of URLs, payloads, and embedded scripts throughout execution chain.”
- [T1497 ] Virtualization/Sandbox Evasion – Extensive VM, sandbox, and debugger detection to avoid analysis: “Detects VMware, VirtualBox, Hyper-V, Cuckoo, sandbox environments, debugging tools.”
- [T1036.005 ] Match Legitimate Name or Location – Masquerades payloads using legitimate-seeming filenames such as Microsoft.Win32.TaskScheduler.dll: “Uses filename “Microsoft.Win32.TaskScheduler.dll” for malicious payloads.”
- [T1071.001 ] Web Protocols – Uses HTTPS/HTTP to retrieve staging scripts and steganographic images from paste sites and archive.org: “Uses HTTPS for payload retrieval from paste sites and archive.org.”
- [T1102.001 ] Dead Drop Resolver – Uses paste.ee and pastefy.app as dead-drop resolvers for staging scripts: “Uses paste.ee and pastefy.app as staging for scripts and payloads.”
Indicators of Compromise
- [File Hash ] initial JavaScript droppers – 42761793d309a0e10b664de61fb25f8d915c65a86b4c5b6229c73d3992519fd5 (IMG-04072025.js), 134c29f52884adc5a3050e5c820229e060308e7377c7125805a6bfccd0859361 (378115664.js)
- [Steganographic Image Hash ] archive-hosted image – 89959ad7b1ac18bbd1e850f05ab0b5fce164596bce0f1f8aafb70ebd1bbcf900 (universe-1733359315202-8750.jpg)
- [Loader DLL Hash ] Caminho .NET loader – c2bce00f20b3ac515f3ed3fd0352d203ba192779d6b84dbc215c3eec3a3ff19c (Microsoft.Win32.TaskScheduler.dll masquerade)
- [Final Payload Hash ] REMCOS RAT – 003cd08d0e4e3e53b5c2dd7e0ea292059f88f827d0cb025adf478d1f8e005fbd; XWorm – c5208189f4851b8ff525bf3cd74767e89af4ef256b256ed1143f4c8f3a48b01f
- [Domains/URLs ] staging and C2 – http[:]//paste[.]ee/d/BfcImbCm/0, http[:]//paste[.]ee/d/2hfodTFT/0, https[:]//archive[.]org/download/universe-1733359315202-8750/universe-1733359315202-8750.jpg, cestfinidns[.]vip (C2)
- [IP / ASN ] C2 and script hosting – 66.63.187[.]166 (AS214943 Railnet LLC – REMCOS C2), 198.46.173[.]60 (script hosting)
- [File Path / Persistence ] scheduled task and script – C:UsersPublicDownloadspanters.js (panters.js SHA-256: a0e2b00951c6327788e3cc834a2d5294c2b7f94aad344ec132fe78b30cce18cc); Scheduled Task names: amandes, amandines