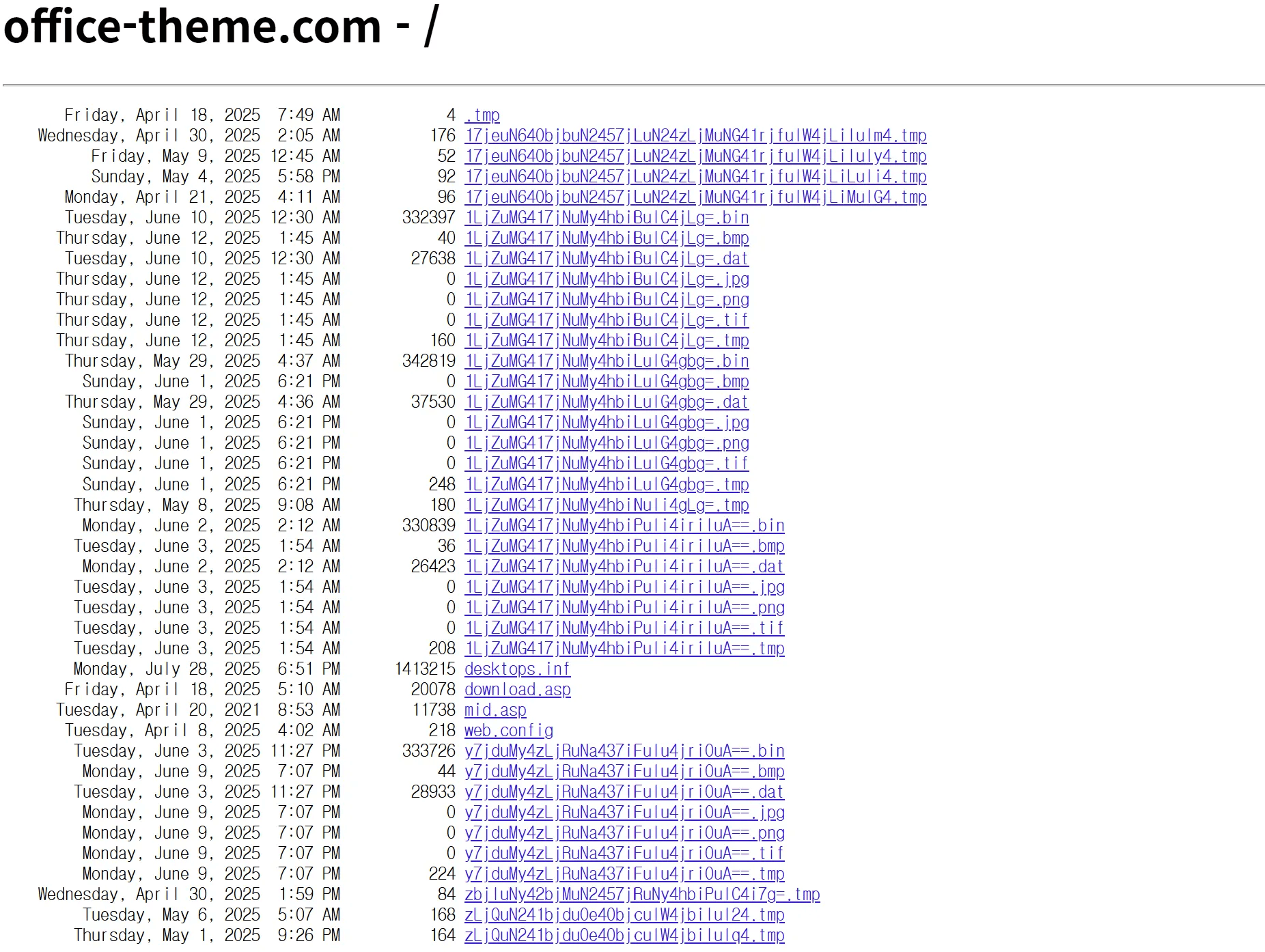
A multi-stage campaign uses malicious Word documents hosted on an open directory at office-theme[.]com to deliver a loader chain that ultimately executes the Comebacker payload in memory, targeting aerospace and defense-related organizations. The malware chain includes VBA droppers, a ChaCha20-decrypted USOPrivate.dll loader, and HTTPS AES-128-CBC C2 communications to hxxps://hiremployee[.]com. #Comebacker #USOPrivate.dll
Category: Threat Research

CRIL uncovered a widespread phishing campaign using self-contained HTML attachments that render fake Adobe-style login UIs and exfiltrate harvested credentials directly to attacker-controlled Telegram bots via the Bot API. The campaign reuses templates across multiple brands (Adobe, FedEx, WeTransfer, etc.), employs obfuscation and anti-analysis measures, and targets organizations primarily in Central and Eastern Europe. #Telegram #Adobe

Acronis TRU and VirusTotal collaborated to hunt and analyze three campaigns—FileFix (a ClickFix variant using clipboard-based web payload delivery), SideWinder (document-based attacks exploiting CVE-2017-0199 and CVE-2017-11882), and Shadow Vector (judicial-themed malicious SVGs targeting Colombia)—by combining Livehunt, Retrohunt, VT Diff, and metadata filtering to map infection chains and infrastructure. The investigations produced YARA/livehunt rules, IOC pivots (e.g., decoy RTF hash and multiple SVG hashes), and practical VT hunting techniques for detecting web-based and document-based threats. #FileFix #SideWinder
.png)
A race in osanalyticshelperd’s crash-report creation allowed an attacker to combine sandbox-extension abuse, XPC message manipulation, and a non-atomic rename to place files (including a sudoers entry) as root on macOS, enabling local privilege escalation (CVE-2025-24277) and potential sandbox escape. The issue was fixed by restricting the XPC call with the entitlement com.apple.private.osanalytics.write-logs.allow. #osanalyticshelperd #CVE-2025-24277
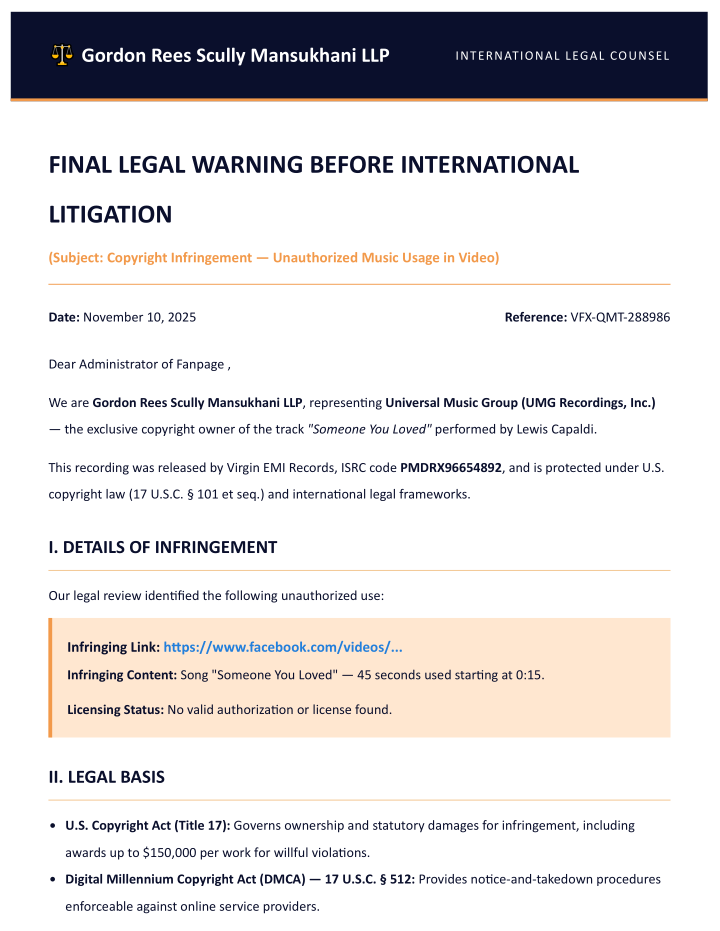
Italian CERT-AGID warned of a phishing campaign impersonating legal notices from Universal Music Group to trick victims into clicking a PDF attachment and submitting Facebook credentials. The attack uses a fake reCAPTCHA and a realistic-looking but fraudulent Facebook login popup to harvest credentials and send them to an attacker C2 server. #UniversalMusicGroup #Facebook

Hybrid Analysis identified a new two-stage Windows malware family — LeakyInjector and LeakyStealer — that injects a ChaCha20-encrypted stealer into explorer.exe, establishes persistence as an Edge update component, and exfiltrates crypto wallet data and browser history to a hard-coded C2. Both components were signed with a valid EV certificate and beacon to everstead[.]group and 45[.]151[.]62[.]120 while implementing a polymorphic engine and backdoor commands for downloading/executing files and running Windows commands. #LeakyInjector #LeakyStealer

As of October 1, 2025, 78% of Kubernetes hosts in Datadog’s dataset run mainstream supported versions (1.31+), 19% run extended support versions (1.28–1.30), and 3% run unsupported versions (earlier than 1.28). The introduction of LTS offerings by major cloud providers (EKS, GKE, AKS) has helped reduce unsupported clusters compared with 2022, though a long tail of very old versions remains. #EKS #GKE #AKS

Threat intelligence gathers and contextualizes external data about who might attack, their motives, and relevant indicators, while threat hunting proactively searches internal environments for hidden or ongoing intrusions that defenses missed. Together they form a feedback loop that improves detection, prioritization, and response by enriching hunts with intelligence and feeding findings back into intelligence programs. #RecordedFuture

Mandiant discovered UNC6485 exploiting an unauthenticated access vulnerability (CVE-2025-12480) in Gladinet Triofox that allowed attackers to bypass authentication, create an admin account, and achieve code execution by abusing the built-in anti‑virus feature. The actor used that access to deploy a Zoho UEMS installer, install remote access tools (Zoho Assist, AnyDesk), and establish an SSH reverse tunnel for RDP access. #CVE-2025-12480 #UNC6485 #Triofox

A large-scale malspam campaign is using GLS-branded emails with an attached XHTML that decodes obfuscated JavaScript to redirect victims to a Netlify-hosted phishing site that uses the ClickFix social-engineering technique to trick users into pasting and running terminal commands. Analysis of a downloaded binary found a SETTINGS resource matching Remcos RAT configuration, indicating likely Remcos-based remote access and data-stealing activity. #Remcos
A new KONNI-linked campaign abused Google’s Find Hub to remotely wipe Android devices after compromising Google accounts and used KakaoTalk to distribute MSI-based malware disguised as “stress-relief” programs. The campaign targeted South Korea, impersonated counselors and other trusted contacts, and relied on AutoIt-based RAT loaders and multi-stage C2 infrastructure. #KONNI #FindHub
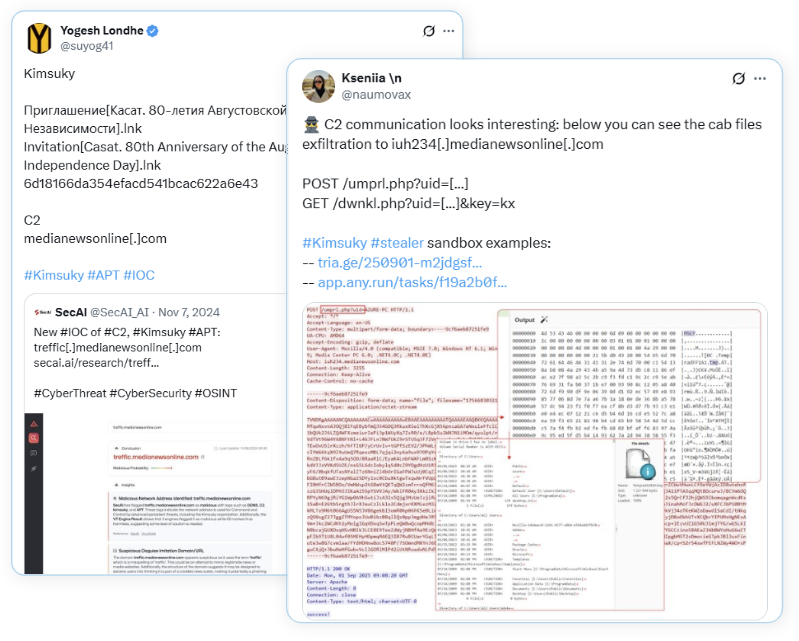
Kimsuky used a small initial JavaScript (Themes.js) to download additional JavaScript stages from iuh234.medianewsonline[.]com, collect system/process/file information, package results into .cab files via certutil, and exfiltrate them via POST requests. The intrusion established persistence by writing Themes.js to %APPDATA%MicrosoftWindowsThemes and creating a scheduled task “Windows Theme Manager”; #Kimsuky #iuh234.medianewsonline

Online casino SEO spam has surged since 2021, with attackers increasingly compromising WordPress sites to inject cloaked casino pages and backlinks, often targeting regions with strict gambling laws like Indonesia. The observed infection used layered redundancies—database-stored payloads, .dat files, theme/plugin modifications, and reinfection code—to persist and evade detection. #SlotGacor #browsec.xyz
On November 5, 2025, multiple high-profile YouTube creators reported receiving fake DMCA takedown notices that linked to malicious downloads, prompting researchers to analyze the campaign and disclose numerous related domains and IPs. Public analysis identified phishing domains (e.g., dmca-security[.]com, ms-team-ping4[.]com), rotating infrastructure with distinctive host banners and certificates, and additional related domains discovered via DNS and host-response pivots. #dmca-security #ms-team-ping4
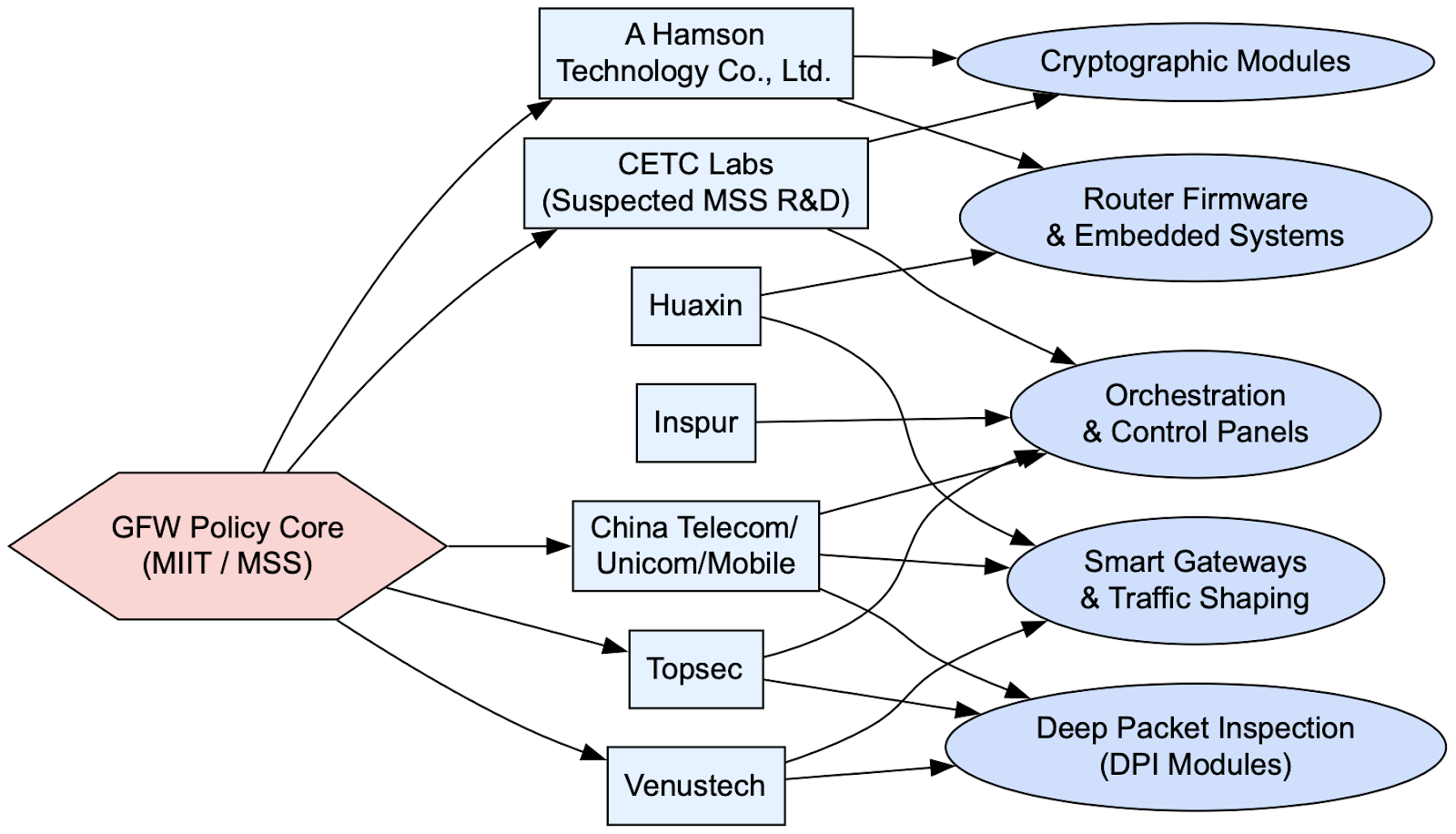
The leaked 500GB Great Firewall dataset details a modular, nationwide DPI and orchestration ecosystem—centered on a Traffic Secure Gateway (TSG) platform, MAAT, Gohangout, Redis telemetry, JA3 and SNI fingerprinting, and vendor-supplied DPI hardware—used to detect, predict, and disrupt circumvention tools like Psiphon, V2Ray, and Shadowsocks while integrating telemetry into broader surveillance and social-credit systems. The files reveal centralized command queues, regional enforcement nodes, sinkholing/BGP hijacks, protocol-deviation quarantine and active probing, and evidence of misclassification/false positives affecting cloud providers and legitimate services. #Psiphon #V2Ray #Shadowsocks