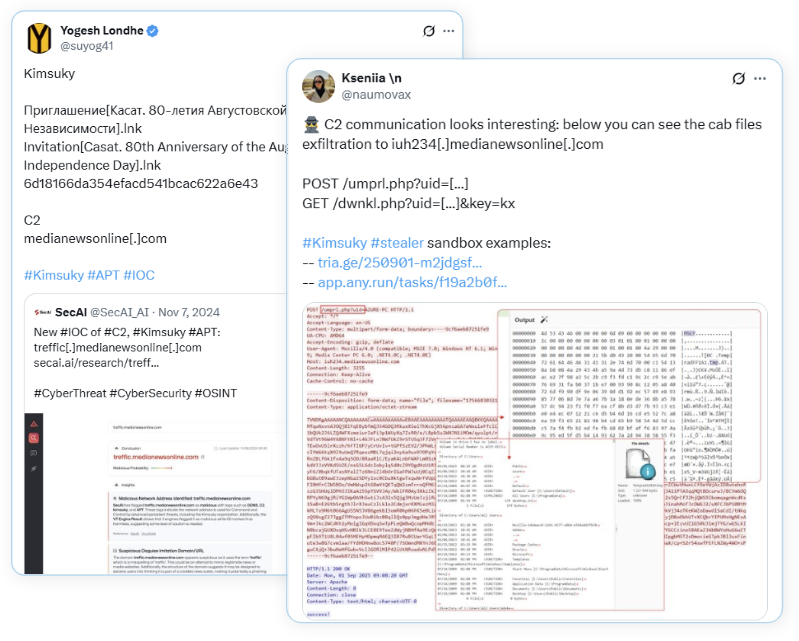
Kimsuky used a small initial JavaScript (Themes.js) to download additional JavaScript stages from iuh234.medianewsonline[.]com, collect system/process/file information, package results into .cab files via certutil, and exfiltrate them via POST requests. The intrusion established persistence by writing Themes.js to %APPDATA%MicrosoftWindowsThemes and creating a scheduled task “Windows Theme Manager”; #Kimsuky #iuh234.medianewsonline
Keypoints
- The initial drop is an unobfuscated JavaScript file named Themes.js that issues GET requests to iuh234[.]medianewsonline[.]com/dwnkl[.]php with uid (computer name) and a hardcoded key to retrieve further stages.
- The second-stage JavaScript collects system information, running processes, and directory listings under C:Users, writes results to temp files, packages them as .cab files, and uploads them via POST to /umprl.php?uid=.
- Exfiltration uses certutil (LOLBIN) to decode or create cabinet files and sends the cabinet content in POST request bodies to the adversary-controlled domain.
- The C2 responds to each upload with another JavaScript stage that executes additional functions, including code to establish persistence and drop a Word document (E-CARD.docx) via base64 payloads.
- Persistence is achieved by writing Themes.js to %APPDATA%MicrosoftWindowsThemesThemes.js and creating a scheduled task named “Windows Theme Manager” that runs wscript.exe every minute.
- The code modifies the HKCUConsoleCodePage registry value to 65001 (UTF-8) and removes temporary .tmp files after exfiltration, indicating attempts at encoding handling and cleanup (indicator removal).
- A Word document dropped by the campaign appears empty (likely a lure) and the initial delivery vector for Themes.js remains undetermined.
MITRE Techniques
- [T1059.007 ] Command and Scripting Interpreter: JavaScript – Used as the primary execution and orchestration language for initial and subsequent stages to download, execute, and run reconnaissance and exfiltration code. Quote: ‘The first file observed within this intrusion chain is a JavaScript file called Themes.js.’
- [T1053.003 ] Scheduled Task/Job: Scheduled Task – The decoded script writes Themes.js to disk and creates a scheduled task “Windows Theme Manager” that runs wscript.exe every minute to maintain persistence. Quote: ‘a scheduled task is created that runs every minute with the task name Windows Theme Manager’
- [T1112 ] Modify Registry – The malware modifies HKCUConsoleCodePage to 65001 to set UTF-8 encoding before executing or decoding payloads. Quote: ‘modify the HKCUConsoleCodePage registry by adding an entry with the value 65001.’
- [T1070.004 ] Indicator Removal: File Deletion – After exfiltration the script changes to %TEMP% and deletes .tmp files used to stage data. Quote: ‘changes the working directory to the %TEMP% directory and deletes any .tmp file within that directory.’
- [T1027.010 ] Obfuscated Files or Information: Command Obfuscation – The actor uses percent-encoded payloads and base64-encoded content embedded in JS to hide code and a Word document payload. Quote: ‘This function contains hardcoded data that is URI percent-encoded data.’
- [T1082 ] System Information Discovery – The second-stage script runs commands to collect system information (systeminfo) and uploads the output. Quote: ‘The first command executed collects system information’
- [T1083 ] File and Directory Discovery – The script lists files and attributes in C:Users, ordering by newest files first, to identify targets for exfiltration. Quote: ‘navigates to the C:Users directory and lists all the files and subdirectories within it by listing the newest files first.’
- [T1005 ] Data from Local System – Collected outputs (systeminfo, process list, directory listings) are staged for exfiltration. Quote: ‘the first request exfiltrates system information, while the second one contains details about all the processes running on the system’
- [T1074.001 ] Data Staged: Local Data Staging – Results are written to temporary files and turned into .cab files before upload. Quote: ‘All content to be exfiltrated is turned into a .cab (cabinet) file’
- [T1071.001 ] Application Layer Protocol: Web Protocols – Communication with C2 uses HTTP(S) GET and POST requests to medianewsonline subdomain endpoints for staging, commands, and exfiltration. Quote: ‘initiates a GET request to iuh234[.]medianewsonline[.]com’
- [T1105 ] Ingress Tool Transfer – Additional JavaScript stages and a Word document are delivered from the remote server to the victim during the interaction. Quote: ‘The server responds to the GET request with some more JavaScript code.’
Indicators of Compromise
- [Domain ] C2 and download/exfiltration endpoints – iuh234[.]medianewsonline[.]com/dwnkl[.]php, iuh234[.]medianewsonline[.]com/umprl[.]php
- [File Hash ] initial JavaScript sample SHA256 – 596cd0d30fe035e8be1dd9d78c1f71a8fc0e2c653d1318af26c51758339ca6bd
- [File Name ] dropped/persistent file – Themes.js written to %APPDATA%MicrosoftWindowsThemesThemes.js
- [Scheduled Task ] persistence – Task name “Windows Theme Manager” running wscript.exe every minute
- [Temporary File ] staged/document payload – L298306.tmp (used to hold base64 data decoded via certutil to E-CARD.docx)